Comparing certificate chains in X.509 vs self-signed models
JUL 14, 2025 |
In the realm of digital security, certificate chains play a crucial role in establishing trust between parties. When digital certificates are used to authenticate identities, the validity of those certificates is verified through a certificate chain. This chain links a given certificate to a trusted root certificate authority (CA), thereby ensuring its authenticity. There are primarily two models when it comes to certificate chains: the X.509 model and the self-signed model. Each has its own unique characteristics and applications.
Understanding the X.509 Model
The X.509 model is a widely adopted standard for public key infrastructure (PKI). In this model, certificates are issued by trusted certificate authorities. These CAs are authoritative entities responsible for verifying the identity of the certificate requester and signing the certificate. The chain of trust in the X.509 model starts with a root CA, which is inherently trusted by systems and users. The root CA may issue certificates to intermediate CAs, which in turn can issue certificates to end-entities, such as websites or individuals.
Each certificate in this chain vouches for the authenticity of the certificate below it, eventually leading to the end-entity certificate. This hierarchical structure ensures that if the root CA is trusted, all certificates in the chain are also trusted. The use of multiple intermediate CAs allows for efficient management and scalability, as responsibilities can be delegated without compromising the integrity of the trust model.
Examining the Self-Signed Model
Contrary to the X.509 model, the self-signed model does not rely on external certificate authorities. In this model, the certificate issuer is also the certificate signer. The certificate is "self-signed," meaning that its authenticity is vouched for by the entity that created it. Self-signed certificates are usually employed in controlled environments where the trust relationship is established manually, such as internal networks or development environments.
While self-signed certificates provide a straightforward and cost-effective solution for establishing secure communications, they lack the inherent trust of the X.509 model. There is no third-party validation, and users must manually trust the certificate by adding it to their list of trusted certificates. This can be a security risk if users are not diligent about verifying the legitimacy of the self-signed certificate.
Comparing Security Implications
The security implications of each model are significant. The X.509 model is generally considered more secure for public-facing applications due to its reliance on trusted third-party verification. Since the root CAs are trusted by default, and they are subject to rigorous security standards and audits, users can be confident in the authenticity of certificates issued under this model.
On the other hand, self-signed certificates may be vulnerable to man-in-the-middle attacks or other security threats if not properly managed. Since trust is established manually, any oversight can lead to potential compromises. In environments where security is paramount, relying solely on self-signed certificates without additional safeguards is not advisable.
Use Cases and Suitability
X.509 certificates are best suited for scenarios where wide-scale trust and interoperability are needed. They are commonly used in e-commerce, online banking, and any application where secure communication over the internet is essential. The global recognition of CA-backed certificates ensures seamless interactions across different systems and organizations.
Self-signed certificates, however, are suitable for scenarios where control is entirely within the scope of the issuing organization. They are ideal for internal applications, testing, and development environments where the overhead and cost of acquiring CA-signed certificates are unnecessary.
Conclusion
Both the X.509 and self-signed models serve important roles in digital security. The choice between them largely depends on the context and requirements of the application in question. While the X.509 model provides a robust framework for establishing trust among disparate parties, the self-signed model offers flexibility and simplicity for controlled environments. Understanding the strengths and limitations of each model is essential for making informed decisions about certificate management and security.
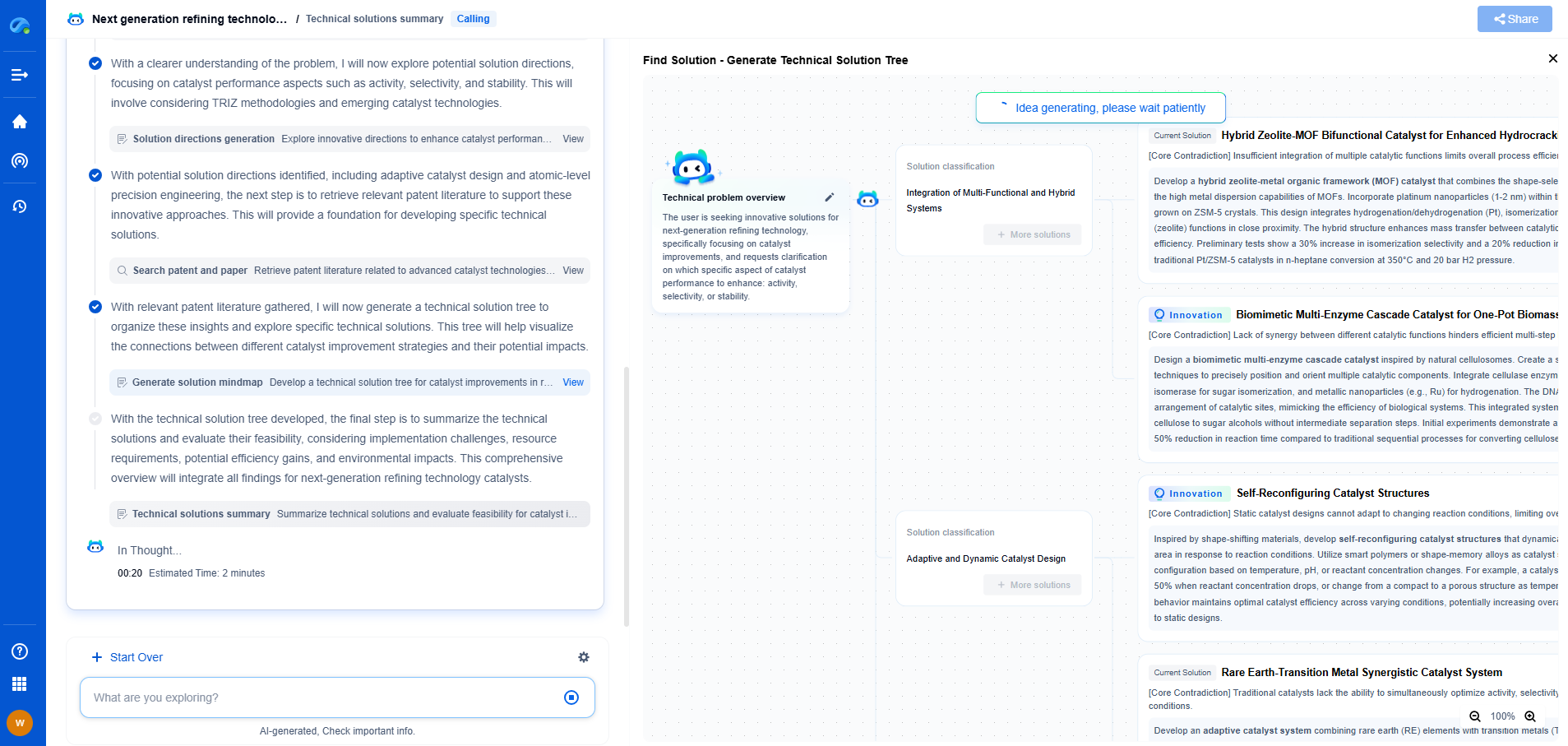
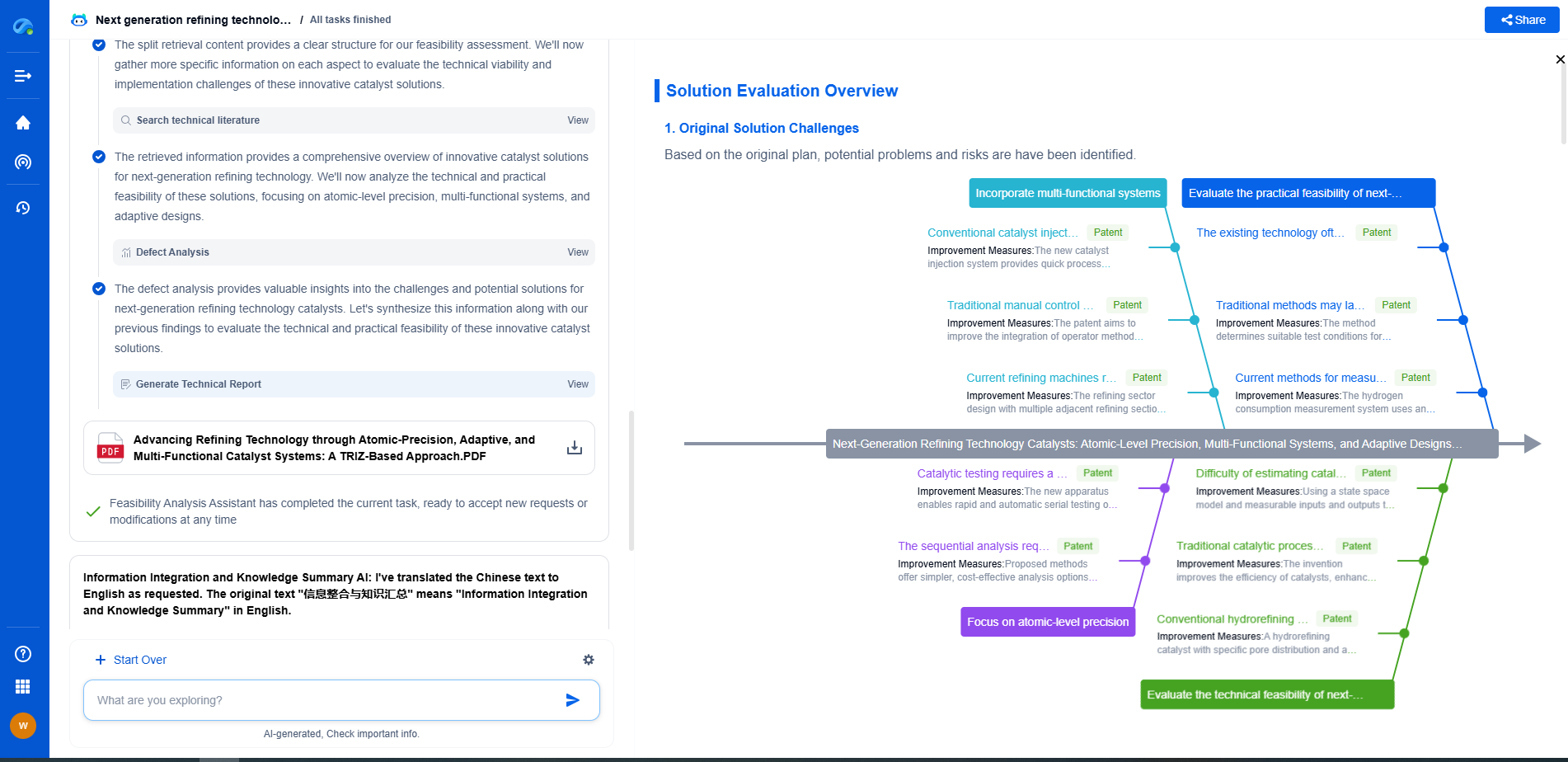
From 5G NR to SDN and quantum-safe encryption, the digital communication landscape is evolving faster than ever. For R&D teams and IP professionals, tracking protocol shifts, understanding standards like 3GPP and IEEE 802, and monitoring the global patent race are now mission-critical.
Patsnap Eureka, our intelligent AI assistant built for R&D professionals in high-tech sectors, empowers you with real-time expert-level analysis, technology roadmap exploration, and strategic mapping of core patents—all within a seamless, user-friendly interface.
📡 Experience Patsnap Eureka today and unlock next-gen insights into digital communication infrastructure, before your competitors do.