Embedded Security: TrustZone and Secure Boot for Tamper-Resistant Field Units
JUL 17, 2025 |
In an increasingly connected world, the security of embedded systems is more crucial than ever. These systems, often deployed in field units, operate in environments where they might be subjected to unauthorized access or tampering. Ensuring the integrity and security of these systems is vital to protect sensitive data and maintain operational reliability. Two significant technologies in the realm of embedded security are TrustZone and Secure Boot. These technologies provide robust solutions for creating tamper-resistant field units, offering a layered approach to security that is vital in today's threat landscape.
Understanding TrustZone Technology
TrustZone technology, developed by ARM, provides a framework that enables secure and non-secure states within a single processor. By creating isolated environments, TrustZone ensures that sensitive operations and data are protected from potentially malicious code running in the non-secure domain.
TrustZone works by implementing a "world" separation at the hardware level. This separation extends to the software stack, including the operating system and applications. By doing so, TrustZone creates a Trusted Execution Environment (TEE) where sensitive operations can be executed without interference. The non-secure world, meanwhile, operates independently, ensuring that even if it’s compromised, the secure world remains unaffected.
Applications of TrustZone in Field Units
In field units, TrustZone can be employed to safeguard critical data and processes. For instance, it can secure cryptographic operations, ensuring that encryption keys remain protected. It can also be used to store sensitive user data, such as credentials or configuration settings, in a manner that unauthorized entities cannot access.
Furthermore, TrustZone's ability to isolate secure and non-secure operations allows developers to implement more flexible security policies. They can choose which operations need to run in the secure world, providing a tailored security approach that meets specific application requirements. This flexibility is crucial in field units, which may operate under varying conditions and threat levels.
The Role of Secure Boot in Embedded Security
Secure Boot is another critical technology in the realm of embedded security. It ensures that a device boots using only software that is trusted by the device manufacturer. This is achieved by verifying the digital signature of the bootloader and subsequent software components during the boot process.
Secure Boot works by maintaining a chain of trust from the initial bootloader to the operating system and applications. Each component in the boot sequence is cryptographically signed, and its integrity is verified before execution. If any component is tampered with or fails verification, the boot process is halted, preventing compromised software from running.
Implementing Secure Boot in Field Units
For field units, Secure Boot provides a robust mechanism to prevent unauthorized software from being executed. This is particularly important in environments where physical access to the device is possible, as attackers might attempt to replace or alter the software to gain control or access sensitive data.
By implementing Secure Boot, manufacturers can ensure that only approved software versions are executed, reducing the risk of malware infiltration and unauthorized modifications. This approach not only protects the device itself but also maintains the integrity of the data and operations it supports.
Achieving Tamper Resistance Through TrustZone and Secure Boot
Combining TrustZone and Secure Boot provides a comprehensive security strategy for field units. TrustZone offers runtime protection by isolating sensitive operations, while Secure Boot ensures that the software stack is verified and trusted from the moment the device is powered on.
This dual-layered approach makes it significantly harder for attackers to compromise the system. Even if they manage to gain access to the device, Secure Boot protects the boot process, and TrustZone safeguards critical operations and data.
Conclusion
Incorporating TrustZone and Secure Boot into the design of field units delivers a robust security framework that addresses both software integrity and operational security. These technologies work hand in hand to create tamper-resistant systems capable of withstanding various attack vectors. As embedded systems continue to play a pivotal role in critical applications, employing such security measures is not just advisable but essential to ensure trust and reliability in the field.
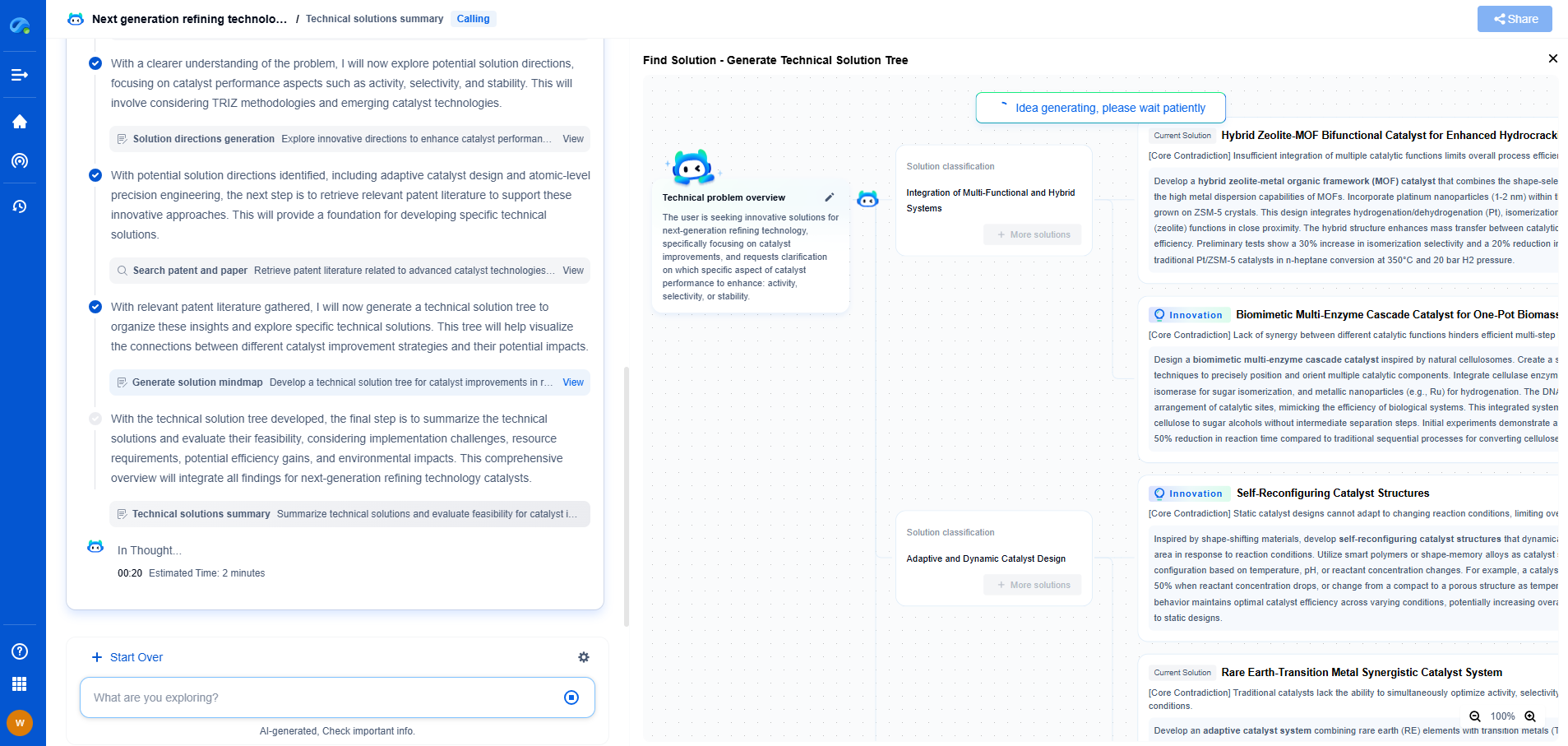
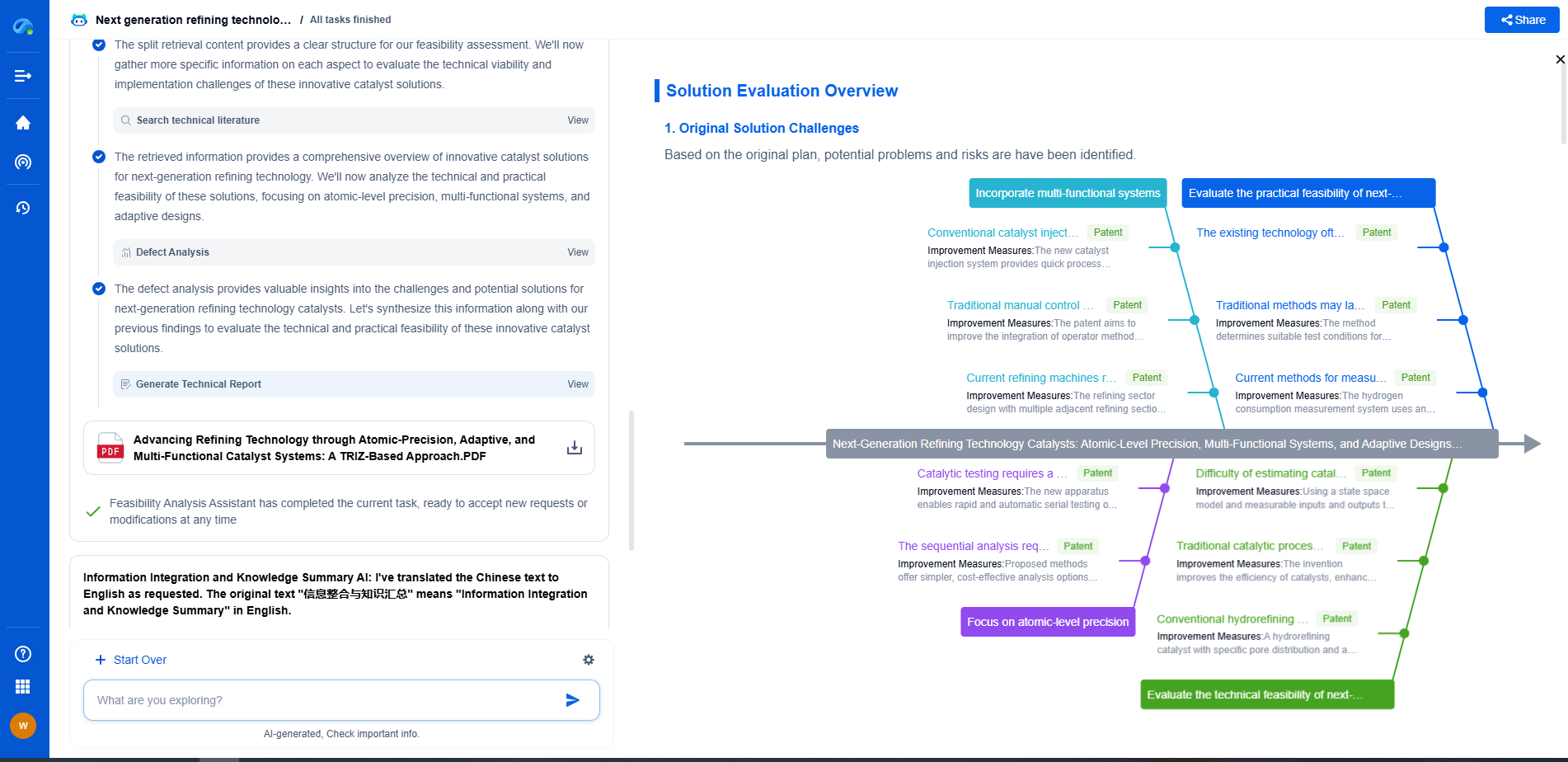
Whether you’re developing multifunctional DAQ platforms, programmable calibration benches, or integrated sensor measurement suites, the ability to track emerging patents, understand competitor strategies, and uncover untapped technology spaces is critical.
Patsnap Eureka, our intelligent AI assistant built for R&D professionals in high-tech sectors, empowers you with real-time expert-level analysis, technology roadmap exploration, and strategic mapping of core patents—all within a seamless, user-friendly interface.
🧪 Let Eureka be your digital research assistant—streamlining your technical search across disciplines and giving you the clarity to lead confidently. Experience it today.