Encrypted vs. Unencrypted Logging: Security vs. Performance Impacts
JUL 17, 2025 |
In today's digital landscape, where data breaches and cyberattacks are commonplace, organizations must prioritize security measures to protect sensitive information. Logging is a critical component of system monitoring and troubleshooting, but it can also be a potential security risk if not handled properly. One of the key considerations when implementing logging solutions is whether to use encrypted or unencrypted logs. This article explores the security and performance impacts of encrypted versus unencrypted logging, helping you make an informed decision for your organization.
Security Implications
1. Confidentiality and Integrity
Encrypted logging provides a higher level of confidentiality and integrity for your logs. By encrypting log data, you ensure that even if unauthorized access occurs, the contents remain unreadable without the appropriate decryption key. This is particularly important for logs containing sensitive information such as user credentials, personal data, or proprietary business information. Unencrypted logs, on the other hand, are vulnerable to interception and tampering, posing significant security risks.
2. Compliance Requirements
Many industries are subject to regulatory compliance requirements that mandate the protection of sensitive data. Encryption of logs is often a crucial component of meeting these requirements. Regulations such as GDPR, HIPAA, and PCI-DSS emphasize the need to safeguard personal and financial information. Failure to comply with these regulations can result in hefty fines and damage to your organization's reputation. By implementing encrypted logging, you not only enhance security but also demonstrate a commitment to compliance.
3. Insider Threat Mitigation
Even within an organization, there can be risks from insiders with malicious intent or those who inadvertently compromise security. Encrypted logging minimizes the risk of insider threats by restricting access to log data. Only individuals with the appropriate cryptographic keys can decrypt and view the logs, reducing the potential for misuse or unauthorized access from within the organization.
Performance Impacts
1. Processing Overhead
One of the main trade-offs of encrypted logging is the additional processing overhead required for encryption and decryption. Encrypting log data increases CPU usage and can impact system performance, particularly in high-volume logging environments. Organizations need to consider this performance impact and assess whether their systems can handle the extra processing load without affecting overall system responsiveness.
2. Storage Considerations
Encryption can also impact storage requirements. Encrypted logs are typically larger in size compared to their unencrypted counterparts due to the added cryptographic metadata. This increased storage requirement can result in higher costs for data storage solutions. Organizations must evaluate their storage capacity and budget to accommodate the larger encrypted log files.
3. Latency Issues
Another consideration is the potential for increased latency when accessing and processing encrypted logs. The decryption process adds an additional step when retrieving log information for analysis or troubleshooting. While this latency is often negligible in most cases, organizations with time-sensitive applications or those requiring real-time log analysis should carefully evaluate the impact of encryption on their operations.
Conclusion
The decision between encrypted and unencrypted logging involves weighing the trade-offs between security and performance. Encrypted logging offers enhanced security by protecting log data from unauthorized access and ensuring compliance with regulatory requirements. However, it introduces additional processing overhead, storage considerations, and potential latency issues. Organizations must carefully assess their specific needs, risk tolerance, and resource capabilities to determine the most appropriate logging strategy. Balancing security and performance is crucial to maintaining a robust and efficient logging system that safeguards sensitive information while supporting operational needs.
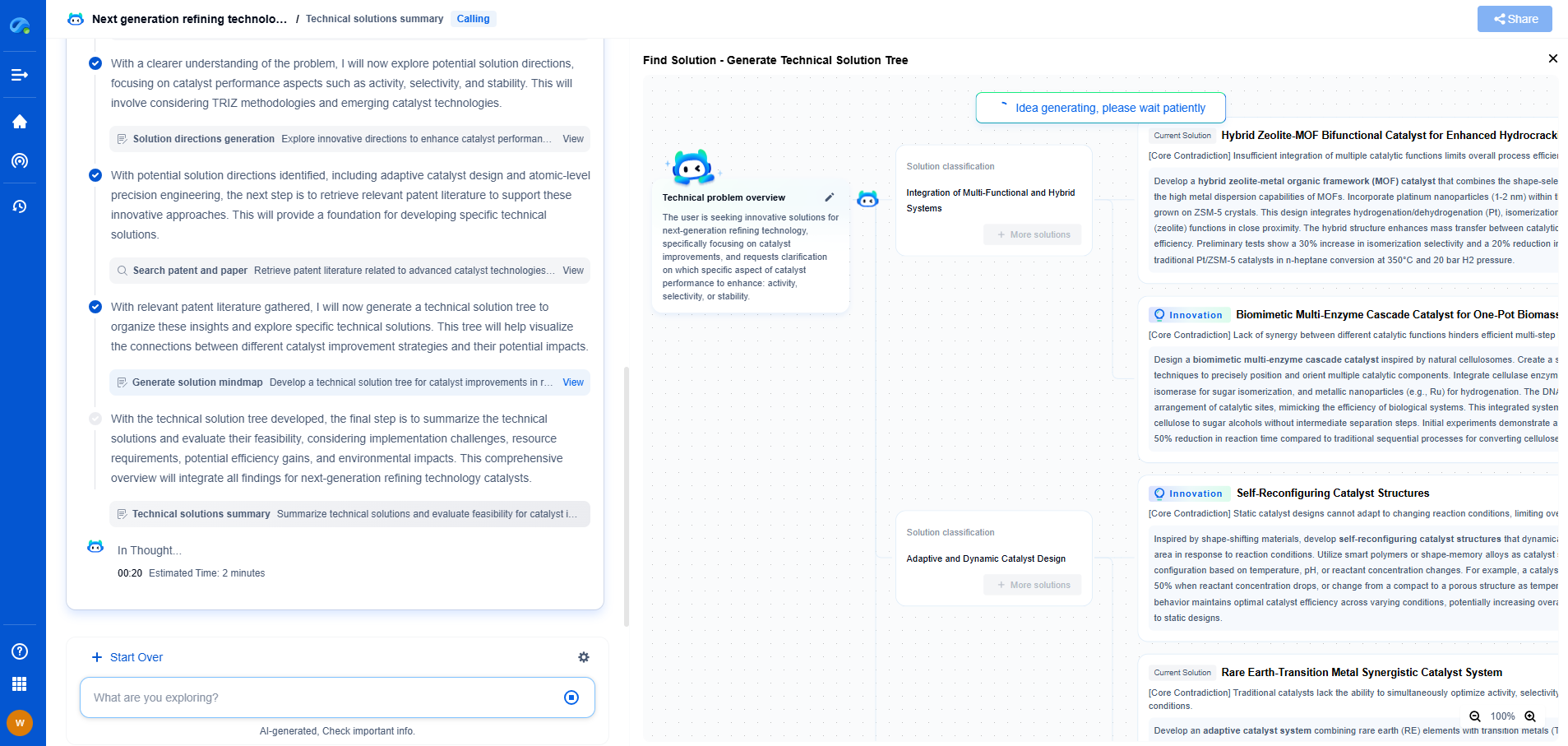
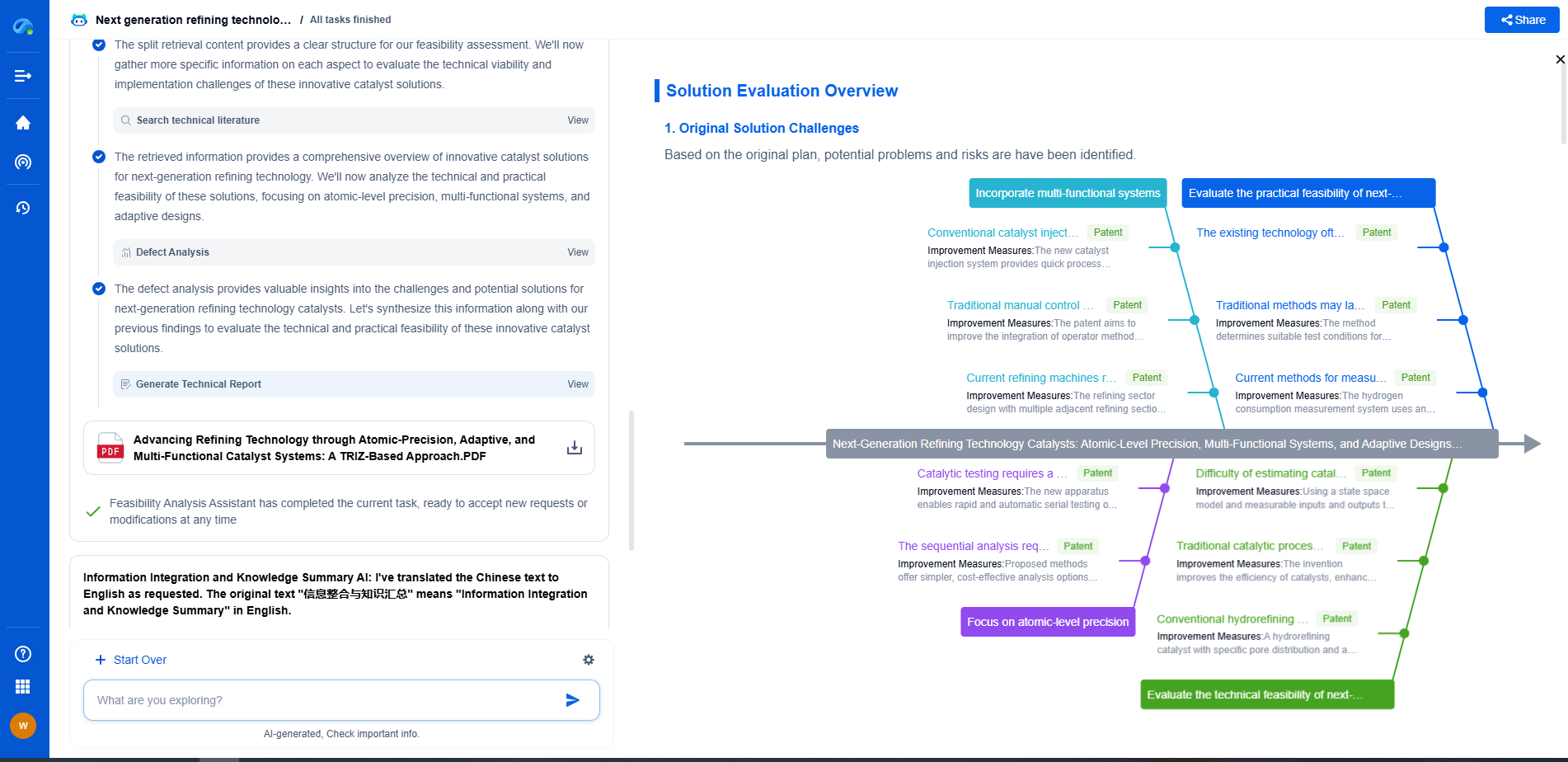
Whether you’re developing multifunctional DAQ platforms, programmable calibration benches, or integrated sensor measurement suites, the ability to track emerging patents, understand competitor strategies, and uncover untapped technology spaces is critical.
Patsnap Eureka, our intelligent AI assistant built for R&D professionals in high-tech sectors, empowers you with real-time expert-level analysis, technology roadmap exploration, and strategic mapping of core patents—all within a seamless, user-friendly interface.
🧪 Let Eureka be your digital research assistant—streamlining your technical search across disciplines and giving you the clarity to lead confidently. Experience it today.