Evaluating packet integrity over UDP vs TCP connections
JUL 14, 2025 |
When it comes to networking, ensuring the integrity of data packets is crucial for reliable communication. Two of the most commonly used transport protocols in the TCP/IP suite are TCP (Transmission Control Protocol) and UDP (User Datagram Protocol). Both facilitate data transmission across networks but handle packet integrity differently. Understanding how each protocol operates can help determine the best use case for maintaining the integrity of data packets. In this article, we will delve into the mechanisms of packet integrity for both UDP and TCP connections, exploring their strengths and weaknesses.
Understanding Packet Integrity
Packet integrity refers to the assurance that data sent from a source reaches its destination unaltered. This is vital for applications where data accuracy is paramount, such as in financial transactions, medical records, or video conferencing. Two critical factors in ensuring packet integrity are error detection and data consistency. While both UDP and TCP are used to send data over the internet, they implement these factors in distinct ways.
UDP and Packet Integrity
UDP is a connectionless protocol known for its simplicity and low overhead. Since UDP does not establish a dedicated end-to-end connection before data transfer, it sends packets, called datagrams, without verifying their arrival at the destination. There is no inherent mechanism in UDP to guarantee packet integrity. If a packet is lost, arrives out of order, or is duplicated, the protocol does not attempt to correct the error. This makes UDP ideal for scenarios where speed is prioritized over reliability, such as live streaming, online gaming, and voice over IP (VoIP), where some data loss is acceptable, and retransmitting lost packets could cause undesirable delays.
However, UDP does include a checksum field, which offers some level of error detection. The checksum is an optional feature that allows the receiver to verify that the data has not been corrupted during transmission. If an error is detected, the packet is simply discarded. While the checksum aids in maintaining some degree of packet integrity, it does not provide a foolproof solution, as no error correction is involved.
TCP and Packet Integrity
In contrast, TCP is a connection-oriented protocol that actively manages packet integrity. It establishes a reliable connection between the sender and receiver through a process known as a three-way handshake. This handshake sets up a session, allowing TCP to provide comprehensive error checking and correction.
TCP achieves packet integrity through several mechanisms. Firstly, it employs sequence numbers to ensure data is received in the correct order. If packets arrive out of sequence, TCP reorders them before passing the data to the application layer. Secondly, TCP uses acknowledgments (ACKs) to confirm the receipt of packets. If an ACK is not received within a certain timeframe, TCP assumes packet loss and retransmits the missing data.
Furthermore, TCP utilizes checksums similar to UDP but with additional error correction capabilities through retransmission strategies. TCP’s flow control and congestion control mechanisms also contribute to maintaining integrity by regulating the rate of data transmission based on network capacity, preventing packet loss due to congestion.
Comparing UDP and TCP for Packet Integrity
When evaluating packet integrity, TCP is superior to UDP due to its built-in mechanisms for error detection, correction, and reliable data delivery. TCP’s ability to retransmit lost packets and reorder out-of-sequence data makes it the preferred choice for applications where data reliability is crucial, such as file transfers, emails, and web browsing.
However, the robustness of TCP comes at the cost of increased latency and bandwidth usage due to its extensive error-checking and retransmission processes. In scenarios where speed is prioritized, and some data loss is tolerable, UDP becomes an attractive option despite its limited integrity features.
Choosing the Right Protocol
The choice between UDP and TCP for ensuring packet integrity largely depends on the specific requirements of your application. If your application demands high data accuracy and reliability, TCP is the evident choice, offering comprehensive solutions to maintain packet integrity. On the other hand, if your application can tolerate some degree of data loss and prioritizes rapid transmission, UDP might be more suitable.
Conclusion
While both UDP and TCP serve essential roles in networking, understanding their fundamental differences in handling packet integrity is crucial for making informed decisions. TCP offers a robust solution for maintaining data integrity through its reliable connection-oriented approach, while UDP, with its simpler, faster, but less reliable connectionless nature, finds its place in applications where speed is paramount. By examining the needs of your specific application, you can effectively choose the protocol that best balances speed and integrity.
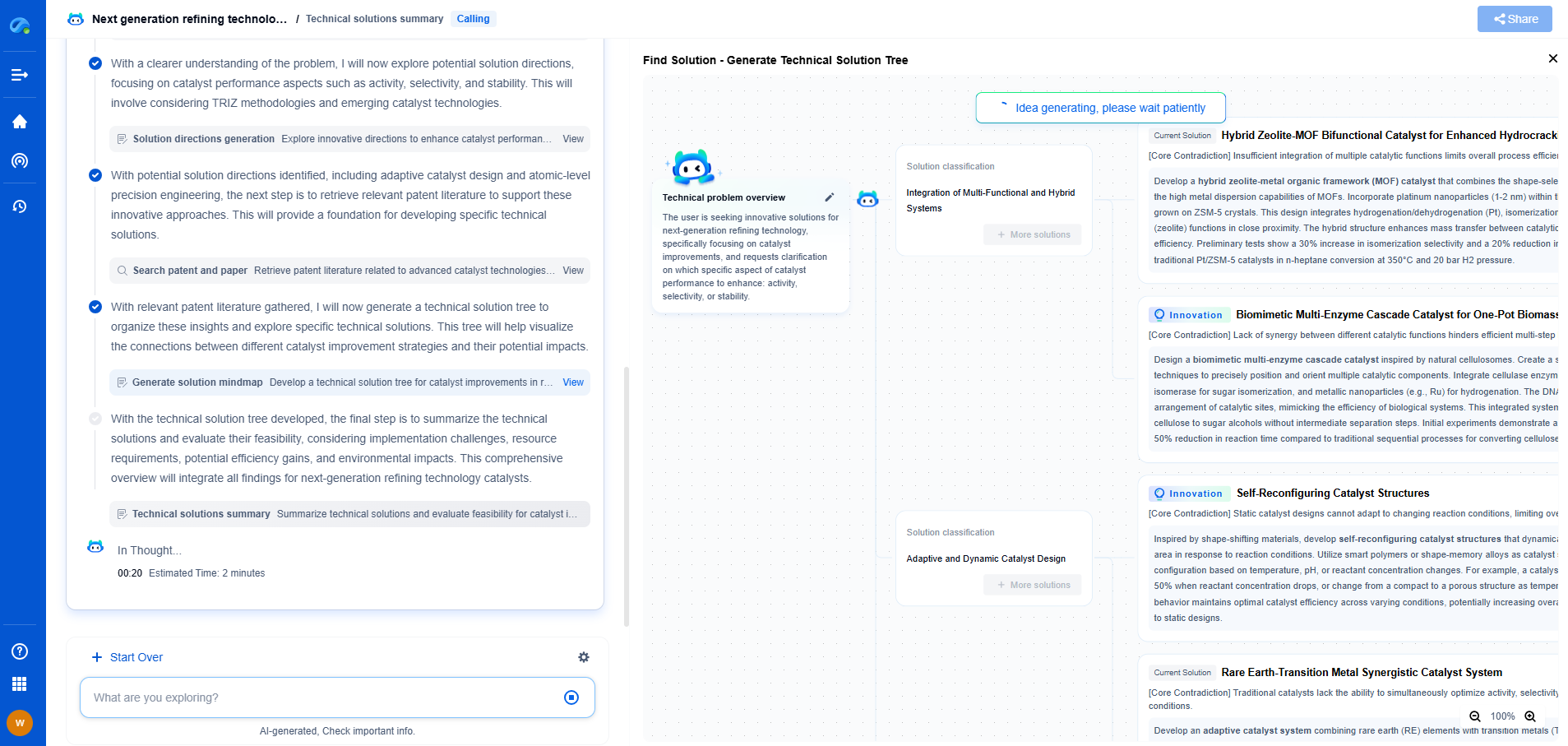
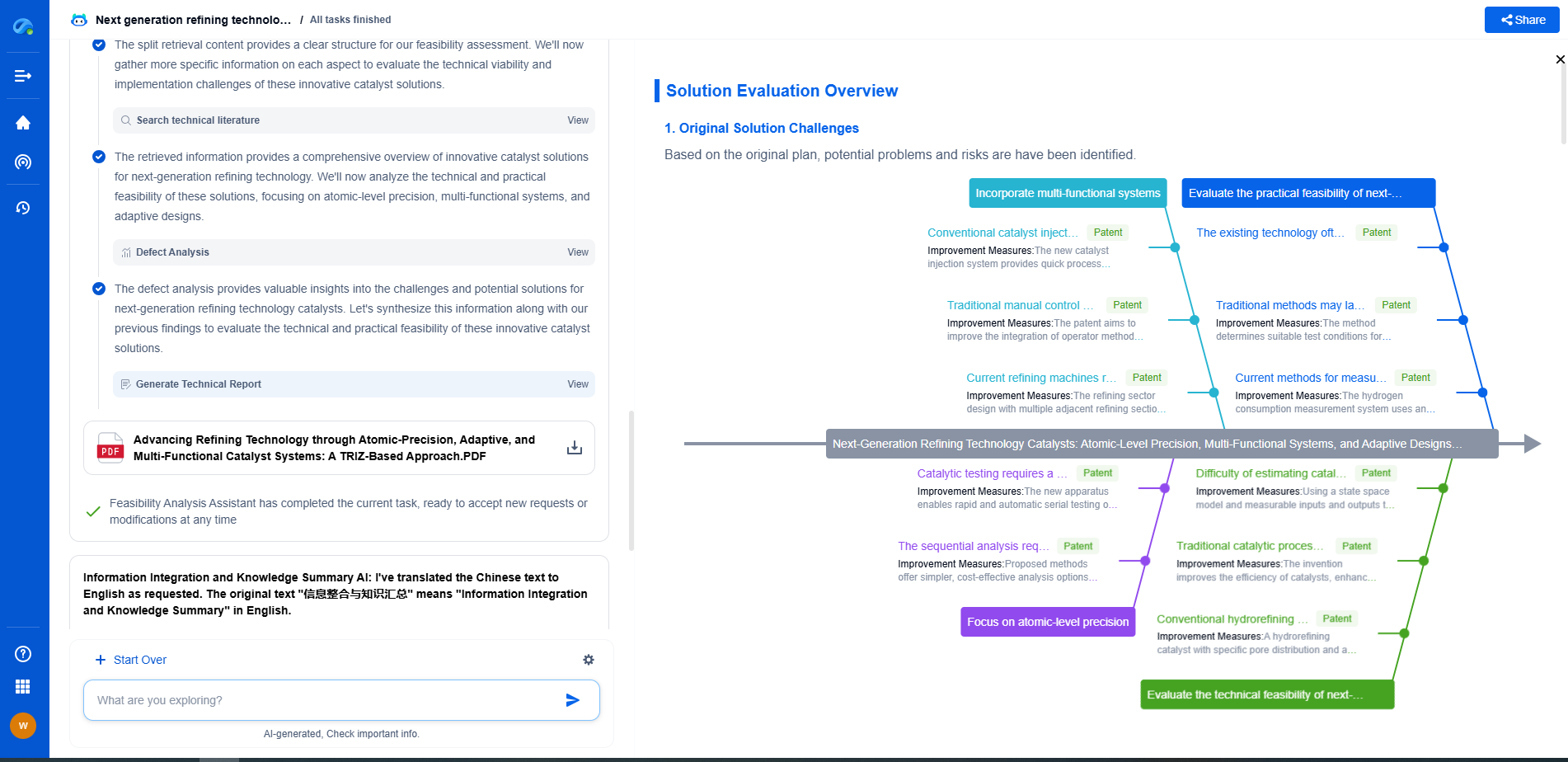
From 5G NR to SDN and quantum-safe encryption, the digital communication landscape is evolving faster than ever. For R&D teams and IP professionals, tracking protocol shifts, understanding standards like 3GPP and IEEE 802, and monitoring the global patent race are now mission-critical.
Patsnap Eureka, our intelligent AI assistant built for R&D professionals in high-tech sectors, empowers you with real-time expert-level analysis, technology roadmap exploration, and strategic mapping of core patents—all within a seamless, user-friendly interface.
📡 Experience Patsnap Eureka today and unlock next-gen insights into digital communication infrastructure, before your competitors do.