How Certificate Authorities (CAs) Prevent Man-in-the-Middle Attacks
JUL 14, 2025 |
Man-in-the-Middle (MitM) attacks are a form of cyber threat where a malicious actor intercepts and possibly alters the communication between two parties without their knowledge. This type of attack can compromise sensitive data, such as login credentials or personal information. MitM attacks pose significant risks to online security because they exploit the trust users place in the security of their digital communications. Understanding how these attacks work and how they can be prevented is crucial in safeguarding information.
The Role of Certificate Authorities
Certificate Authorities (CAs) play a pivotal role in preventing MitM attacks by establishing a chain of trust in online communications. CAs are trusted entities that issue digital certificates to verify the authenticity of websites. These certificates confirm that the website's public key actually belongs to the entity it claims to represent. By using cryptographic techniques, CAs ensure that the data exchanged between users and websites remains confidential and tamper-proof.
How CAs Prevent Man-in-the-Middle Attacks
1. Authentication of Websites
One of the primary functions of a CA is to authenticate websites, ensuring users are communicating with legitimate entities. When a user visits a website, their browser checks the digital certificate provided by the site. This certificate contains information about the CA that issued it, the public key of the website, and the website's identity. If the certificate is verified against the CA's records, the connection proceeds; otherwise, the user is warned about potential security risks. This process prevents attackers from masquerading as legitimate sites to intercept user data.
2. Encryption of Data
CAs facilitate the encryption of data exchanged between a user's browser and a website through the use of public and private keys. Once a website is authenticated, data is encrypted with the website's public key, ensuring that only the intended recipient, possessing the corresponding private key, can decrypt it. This process ensures that even if data is intercepted during transmission, it cannot be deciphered by unauthorized parties.
3. Integrity of Communications
CAs also help maintain the integrity of communications by providing digital signatures. These signatures ensure that any data sent between a user and a website has not been altered during transmission. If a MitM attacker attempts to modify the data, the digital signature verification process will fail, alerting the user to the tampering attempt.
Challenges and Limitations of CAs
While CAs provide essential security services, they are not without their challenges. The trustworthiness of a CA is paramount, and any compromise of a CA can lead to significant vulnerabilities. There have been instances where CAs have issued fraudulent certificates, allowing attackers to impersonate legitimate websites. As a result, maintaining strict security protocols and regular audits is critical for CAs to ensure ongoing trust.
Additionally, the complexity of the certificate ecosystem can be a challenge, with numerous CAs and a variety of certificate types. Users and organizations must remain vigilant, ensuring they are utilizing valid and up-to-date certificates to protect against MitM attacks.
Conclusion: The Continued Importance of CAs
In the ever-evolving landscape of cyber threats, Certificate Authorities remain a cornerstone of online security. By authenticating websites, encrypting data, and ensuring communication integrity, CAs provide critical defenses against Man-in-the-Middle attacks. As technology advances, the role of CAs will continue to be essential in protecting users and maintaining trust in digital communications. It is imperative for both users and organizations to understand the vital functions CAs perform and to support efforts that enhance their security and reliability.
From 5G NR to SDN and quantum-safe encryption, the digital communication landscape is evolving faster than ever. For R&D teams and IP professionals, tracking protocol shifts, understanding standards like 3GPP and IEEE 802, and monitoring the global patent race are now mission-critical.
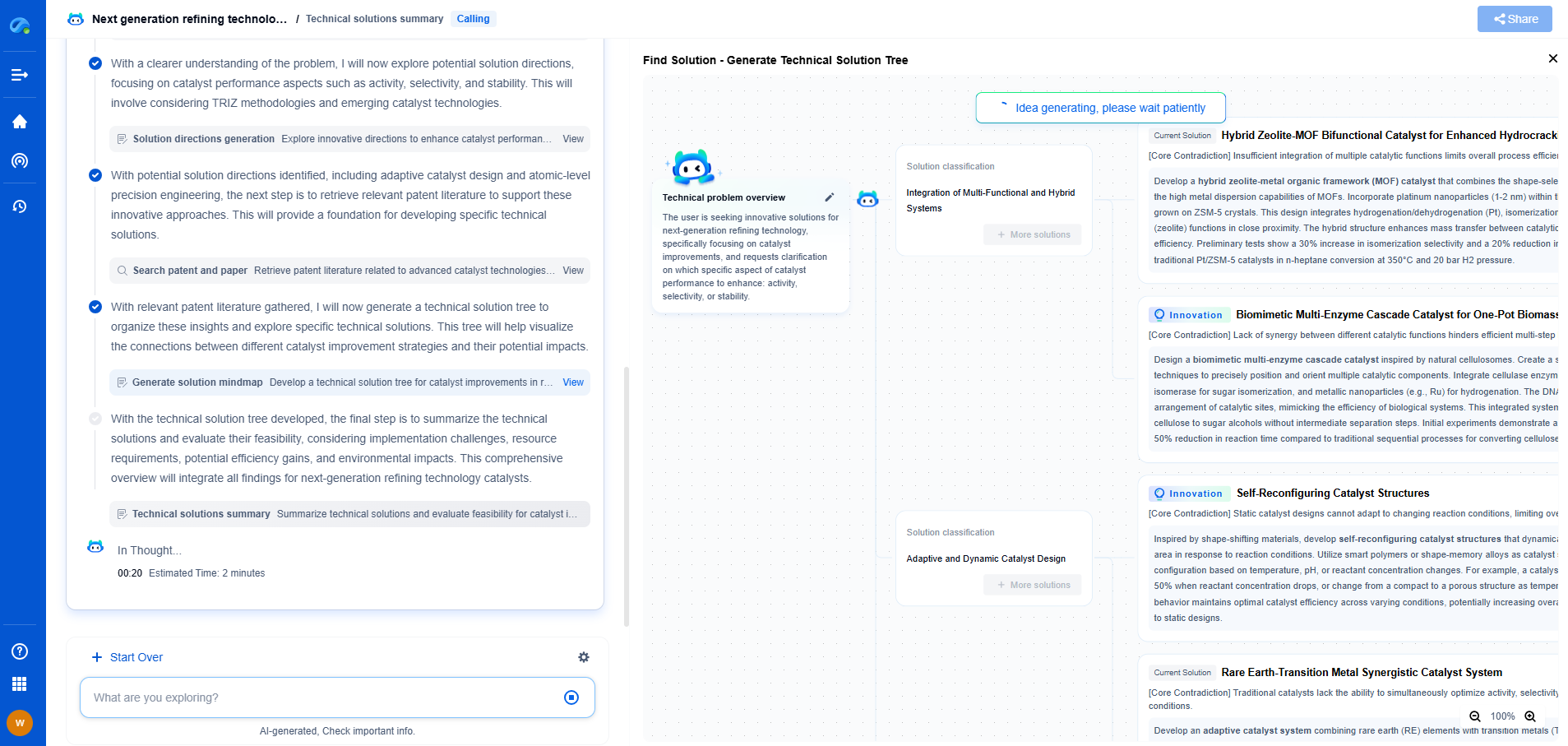
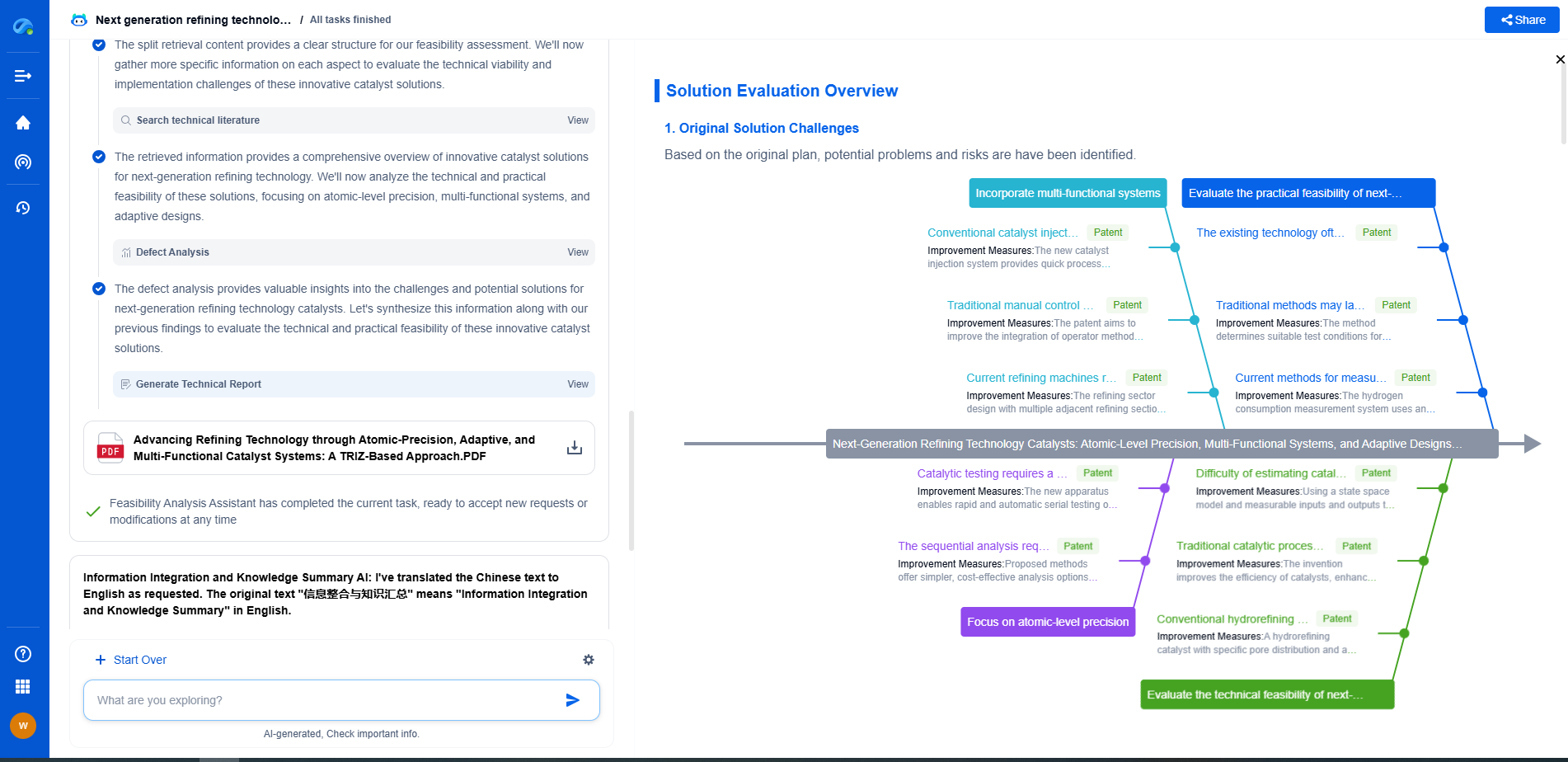
Patsnap Eureka, our intelligent AI assistant built for R&D professionals in high-tech sectors, empowers you with real-time expert-level analysis, technology roadmap exploration, and strategic mapping of core patents—all within a seamless, user-friendly interface.
📡 Experience Patsnap Eureka today and unlock next-gen insights into digital communication infrastructure, before your competitors do.