Post-Quantum Cryptography in Network Protocols
JUL 14, 2025 |
In today's digital age, securing data as it travels across networks is paramount. With the advent of quantum computers on the horizon, the traditional cryptographic protocols we rely on are at risk of being compromised. This is where Post-Quantum Cryptography (PQC) comes into play. PQC refers to cryptographic algorithms that are secure against the powerful computational capabilities of quantum computers. As we prepare for a future where quantum computing is mainstream, integrating PQC into network protocols is crucial to ensure long-term data security.
The Threat of Quantum Computing
Quantum computers, unlike classical computers, use quantum bits or qubits that can represent and store information in multiple states simultaneously. This characteristic allows quantum computers to perform complex computations at unprecedented speeds, posing a significant threat to current encryption methods such as RSA and ECC, which rely heavily on the difficulty of specific mathematical problems. Quantum algorithms, like Shor’s algorithm, can solve these problems exponentially faster than classical algorithms, rendering traditional cryptographic methods vulnerable.
Understanding Post-Quantum Cryptography
Post-Quantum Cryptography is designed to withstand the computational prowess of quantum systems. It involves developing new cryptographic algorithms based on mathematical problems that are believed to remain difficult for quantum computers to solve. Some of the promising techniques in PQC include lattice-based cryptography, hash-based cryptography, code-based cryptography, and multivariate polynomial cryptography. Each of these techniques offers a unique approach to enhancing security in the quantum era.
Integrating PQC in Network Protocols
The integration of PQC into network protocols is not merely a theoretical exercise but a practical necessity. Network protocols such as TLS (Transport Layer Security), which underpin secure communications over the internet, need to be adapted to incorporate PQC to ensure they remain secure in a quantum computing future.
1. Lattice-Based Cryptography in TLS: Lattice-based cryptography is currently one of the most promising candidates for PQC due to its strong security guarantees and efficiency. Protocols like TLS 1.3 can be augmented with lattice-based key exchange mechanisms to provide quantum-resistant security.
2. Hybrid Cryptographic Systems: As we transition to PQC, hybrid cryptographic systems, which combine classical and quantum-resistant algorithms, offer a pragmatic solution. This approach allows networks to benefit from the strengths of both systems while preparing for a fully quantum-resistant future.
3. Implementation Challenges: Integrating PQC into existing network protocols is not without challenges. Issues such as increased computational overhead, larger key sizes, and the need for backward compatibility with existing systems must be addressed. Researchers and engineers are actively working on optimizing these algorithms for practical deployment.
PQC Adoption and Standardization Efforts
The transition to PQC is a significant global effort, with organizations like the National Institute of Standards and Technology (NIST) leading the charge in standardizing post-quantum algorithms. NIST’s Post-Quantum Cryptography Standardization Project aims to evaluate and recommend quantum-resistant cryptographic algorithms for widespread adoption. The project is currently in its final stages, and once finalized, it will pave the way for the implementation of standardized PQC across various network protocols.
The Future of Network Security in a Quantum World
As quantum computing technology advances, the urgency to adopt PQC in network protocols becomes increasingly apparent. Organizations must begin assessing their cryptographic needs and plan for a transition to quantum-resistant algorithms. This involves not only updating protocols but also educating stakeholders about the implications of quantum computing on data security.
Ultimately, the integration of post-quantum cryptography into network protocols is a proactive step towards safeguarding digital communications in a future where quantum computing is a reality. By staying ahead of the curve, we can ensure that our data remains secure, no matter how powerful computers become.
From 5G NR to SDN and quantum-safe encryption, the digital communication landscape is evolving faster than ever. For R&D teams and IP professionals, tracking protocol shifts, understanding standards like 3GPP and IEEE 802, and monitoring the global patent race are now mission-critical.
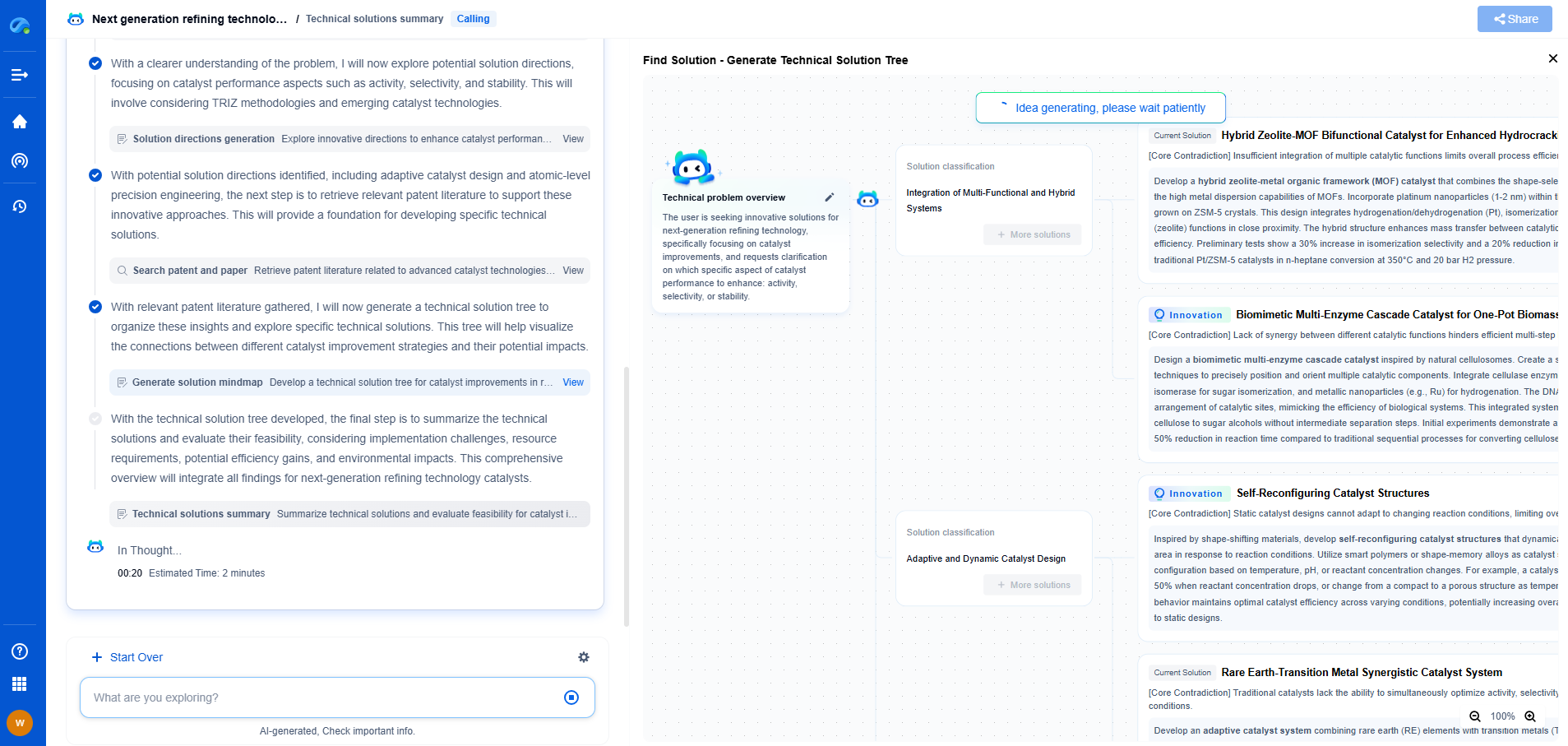
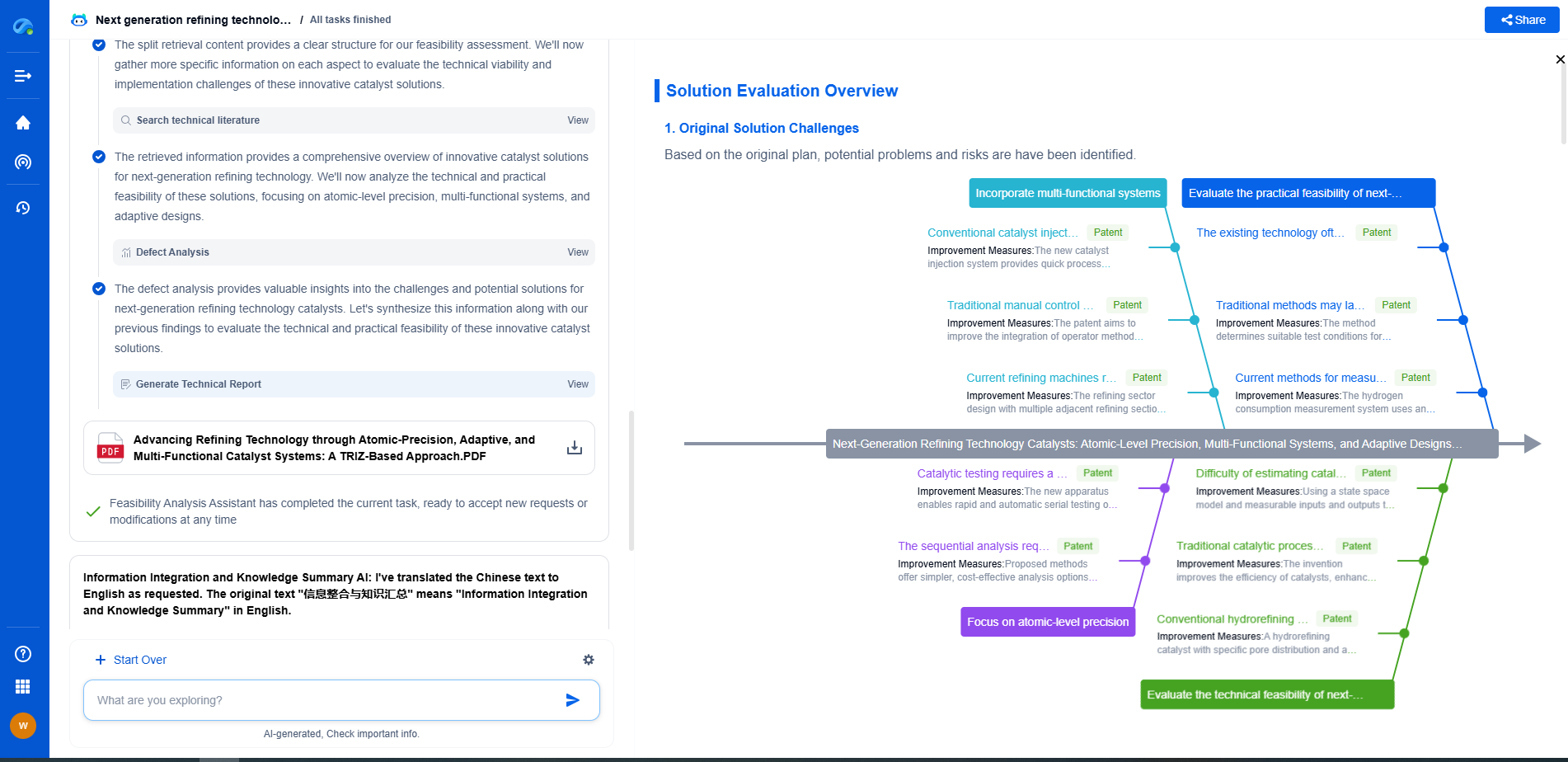
Patsnap Eureka, our intelligent AI assistant built for R&D professionals in high-tech sectors, empowers you with real-time expert-level analysis, technology roadmap exploration, and strategic mapping of core patents—all within a seamless, user-friendly interface.
📡 Experience Patsnap Eureka today and unlock next-gen insights into digital communication infrastructure, before your competitors do.