Secure Boot for Data Loggers: Preventing Firmware Compromise
JUL 17, 2025 |
In today's rapidly evolving technological landscape, data loggers play a crucial role in various industries, from environmental monitoring to industrial automation. These devices collect and store data over time, often in remote or challenging environments. However, as the reliance on these data loggers grows, so does the risk of firmware compromise by malicious actors. To mitigate this risk, the implementation of secure boot mechanisms is imperative. Secure boot is a security standard designed to ensure that a device boots only with firmware that is trusted by the manufacturer. This article delves into the significance of secure boot for data loggers and how it can prevent firmware compromise.
Understanding the Threat: Firmware Compromise
Firmware is the foundational software embedded in hardware devices, and its compromise can have dire consequences. Malicious firmware can manipulate data, disrupt operations, or serve as a gateway for further attacks. Data loggers, often deployed in critical environments, are particularly vulnerable due to their extensive use and sometimes unattended operation. A compromised data logger can lead to inaccurate data collection, unauthorized access, and even complete system failure. Thus, protecting the integrity of firmware in data loggers is essential for maintaining data accuracy and system reliability.
The Mechanics of Secure Boot
Secure boot works by establishing a chain of trust that begins with the hardware and continues through the boot process. This process involves several steps:
1. **Root of Trust**: The secure boot process starts with a hardware-based root of trust. This is a small, immutable piece of code embedded in the hardware that verifies the digital signature of the firmware before it's loaded.
2. **Validation of Firmware**: Each component in the boot process is validated before being executed. This validation ensures that only firmware that has been cryptographically signed by the manufacturer is allowed to run.
3. **Chain of Trust**: As each component is verified, it confirms the integrity of the next component. This creates a chain of trust that ensures no unauthorized code is executed during the startup process.
4. **Firmware Update Protection**: Secure boot also facilitates safe firmware updates. Updates are verified in the same manner as the initial firmware, preventing unauthorized or malicious updates.
Implementing Secure Boot in Data Loggers
To implement secure boot in data loggers, manufacturers need to integrate several key components:
- **Trusted Platform Module (TPM)**: A TPM is a dedicated microcontroller designed to secure hardware through integrated cryptographic keys. It plays a pivotal role in the cryptographic verification process of secure boot.
- **Firmware Signatures**: Firmware needs to be digitally signed using robust cryptographic methods. This ensures that only firmware from a trusted source can be executed.
- **Bootloader Security**: The bootloader, which is responsible for loading the operating system, must be secured. It should only load and execute verified firmware images.
- **Regular Audits and Updates**: Continuous security audits and regular firmware updates are necessary to address new vulnerabilities and ensure the ongoing integrity of the system.
Benefits of Secure Boot for Data Loggers
Implementing secure boot in data loggers offers several significant benefits:
- **Enhanced Security**: By preventing unauthorized firmware from being loaded, secure boot significantly reduces the risk of firmware compromise.
- **Data Integrity**: Secure boot ensures that data collected by the data logger is accurate and reliable, as it prevents tampering with the logging process.
- **System Stability**: Devices are protected from malicious code that could disrupt operations, ensuring continuous and stable system performance.
- **Regulatory Compliance**: Many industries require strict adherence to security standards. Secure boot helps in achieving compliance with these regulations.
Conclusion: A Necessary Security Measure
In conclusion, the implementation of secure boot in data loggers is a necessary measure to protect against firmware compromise. In an era where data is an invaluable asset, securing the devices that collect and manage this data is of paramount importance. By establishing a chain of trust and safeguarding the boot process, secure boot ensures that data loggers operate with integrity and reliability, ultimately safeguarding the interests of businesses and consumers alike. As technology continues to advance, secure boot will remain a critical component of a comprehensive cybersecurity strategy for data loggers.
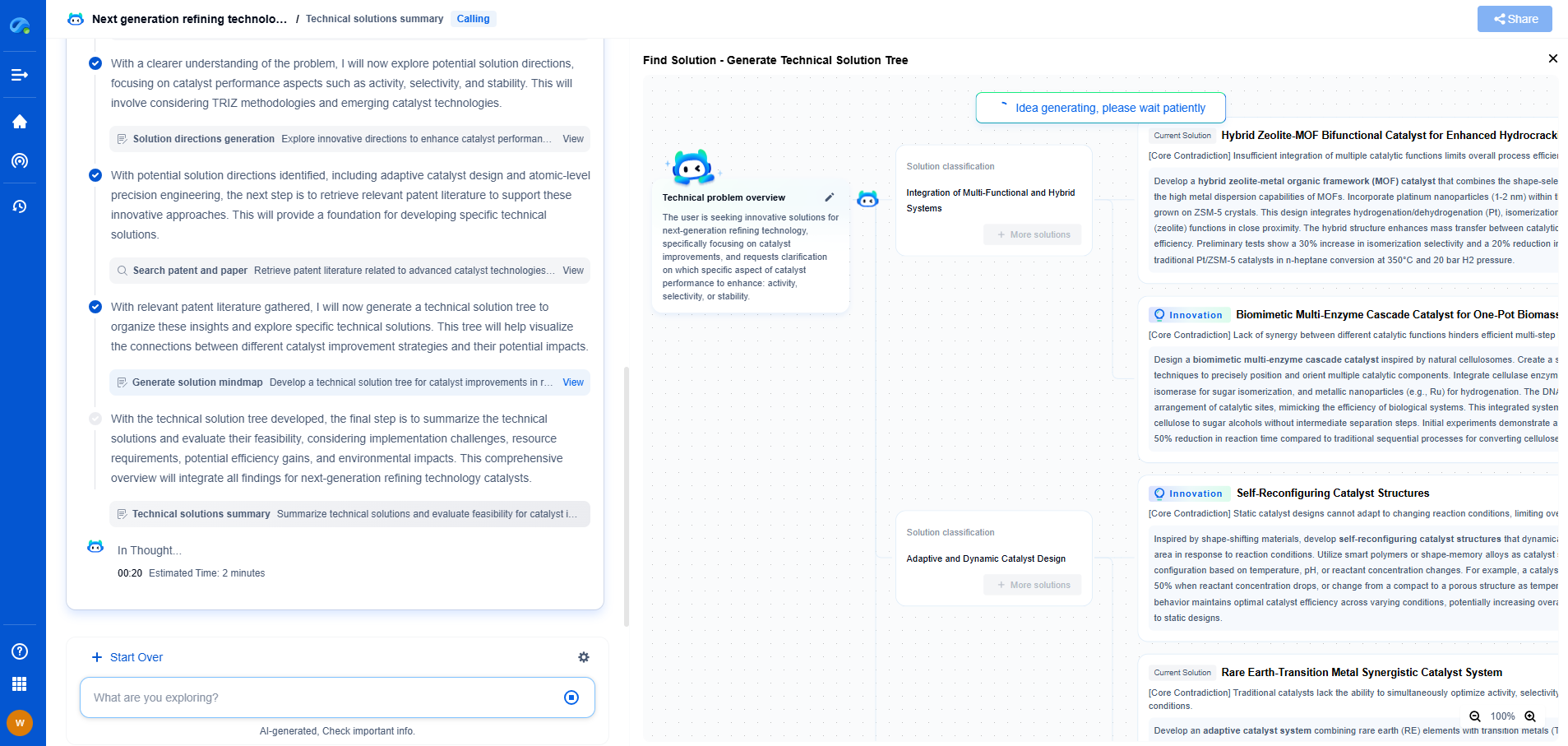
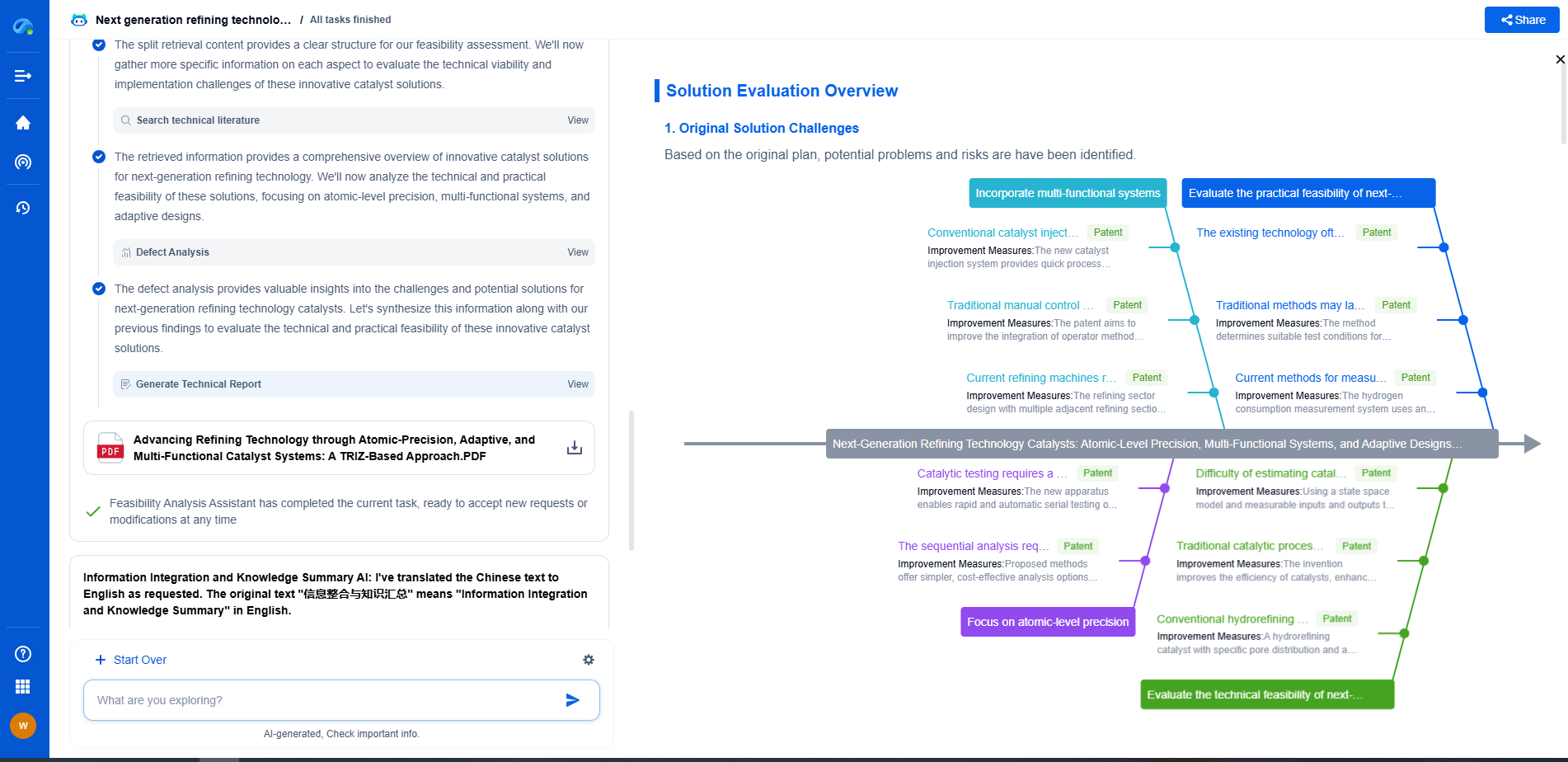
Whether you’re developing multifunctional DAQ platforms, programmable calibration benches, or integrated sensor measurement suites, the ability to track emerging patents, understand competitor strategies, and uncover untapped technology spaces is critical.
Patsnap Eureka, our intelligent AI assistant built for R&D professionals in high-tech sectors, empowers you with real-time expert-level analysis, technology roadmap exploration, and strategic mapping of core patents—all within a seamless, user-friendly interface.
🧪 Let Eureka be your digital research assistant—streamlining your technical search across disciplines and giving you the clarity to lead confidently. Experience it today.