Small program login verification method and device based on face recognition, equipment and storage medium
A face recognition, login verification technology, applied in secure communication devices, character and pattern recognition, user identity/authority verification, etc. problems, to achieve the effect of improving accuracy and security, increasing security, and improving recognition accuracy
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Example Embodiment
[0027] Example 1
[0028] In this embodiment, the company account of the logistics enterprise applet is used by many people, which is not conducive to information security and fund security. At the same time, when a problem occurs, the responsible person cannot be traced, which is inconvenient for the management of the logistics enterprise.
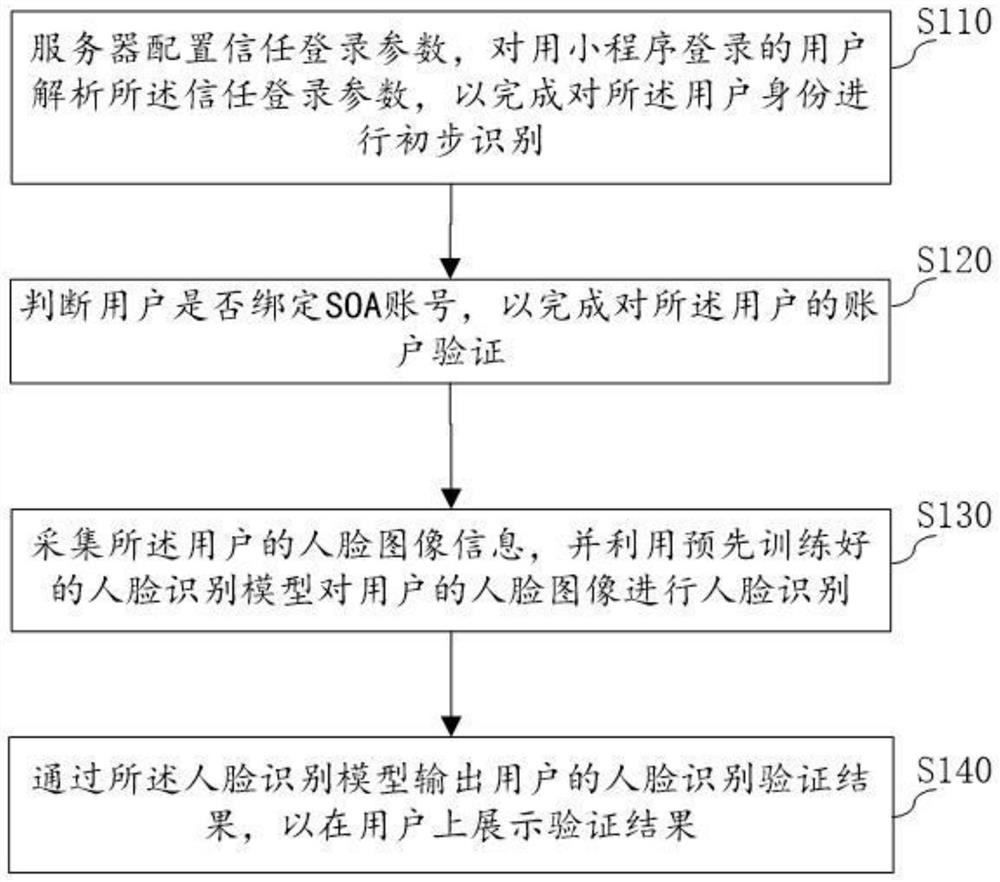
[0029] Specifically, as figure 1 As shown, the flowchart of the first example of the face recognition-based applet login verification method. It includes the following steps:
[0030] S110: The server configures the trusted login parameters, and parses the trusted login parameters for users who log in with the applet, so as to complete the preliminary identification of the user identity;
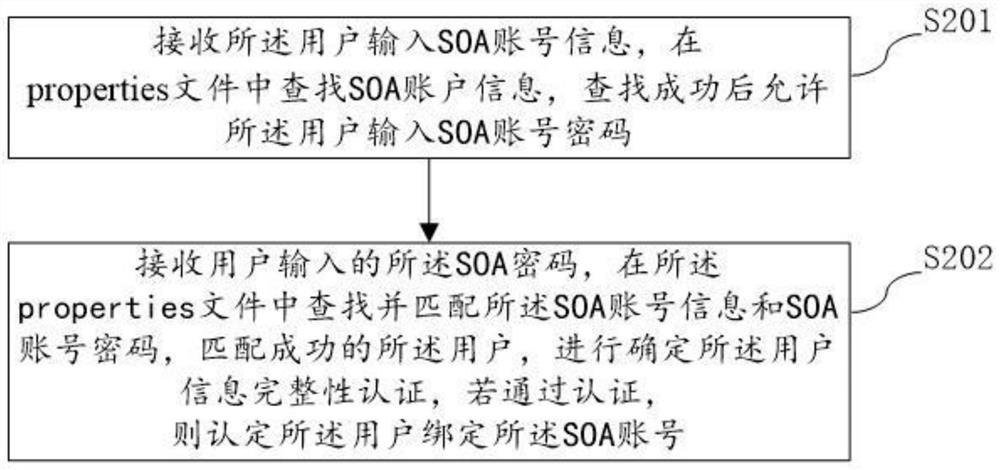
[0031] S120: determine whether the user is bound to the SOA account, to complete the account verification to the user;
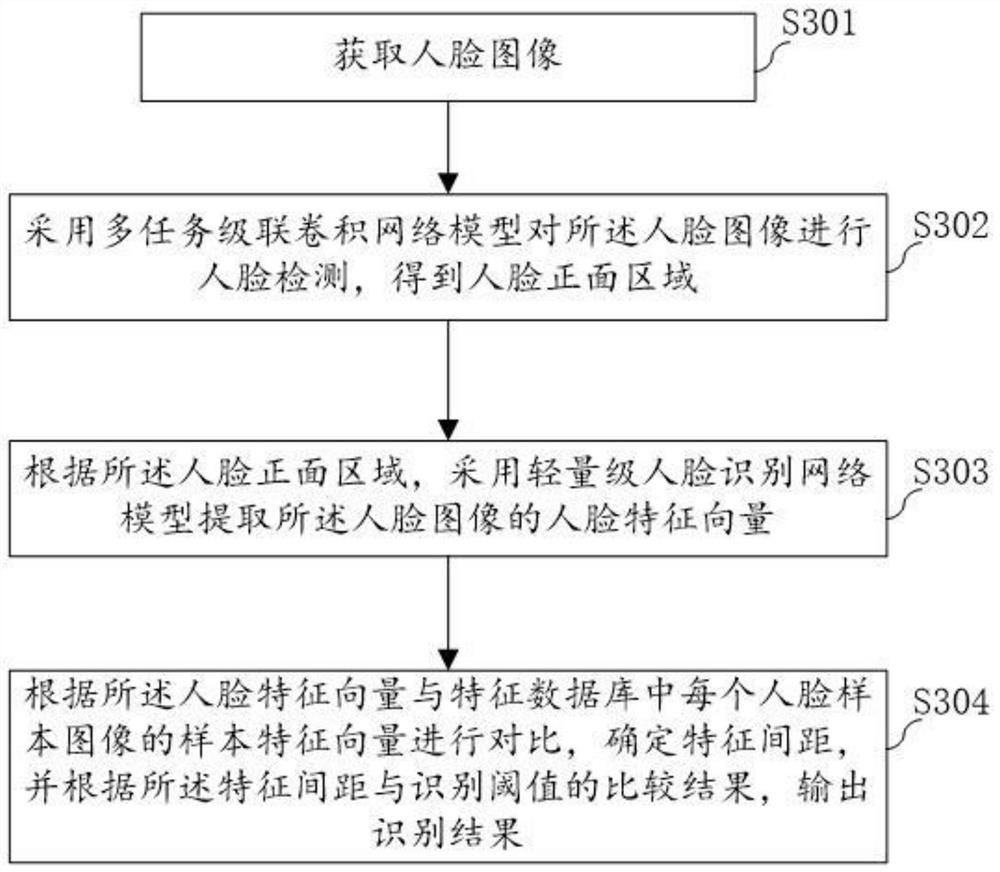
[0032] S130: collect the user's face image information, and utilize the pre-trained face recognition model to carry out face reco...
Example Embodiment
[0095] Embodiment 2
[0096] Compared with the first embodiment, the server can use the secondary identity authentication to complete the preliminary identity recognition (see Figure 4 ).
[0097] S401: The server generates a two-dimensional code of the applet, and displays it to the user;
[0098] The server generates a two-dimensional code for the user to scan to open the applet, wherein, the coding method for generating the two-dimensional code can use Data Matrix, Maxi Code, Aztec, QR Code, Vericode, PDF417, Ultracode, Code49, Code 16K, etc. . The user sends a login request to the server through the applet.
[0099] S402: Receive the first login request sent by the user through the applet;
[0100] Specifically, the user can send the user name to the server; after receiving the user name, the server generates a string of random numbers and responds the random numbers to the user.
[0101] S403: Generate a random number according to the username of the user, further s...
Example Embodiment
[0119] Embodiment 3
[0120] like Figure 5 As shown, based on the same concept, the present invention also provides a small program login verification device 500 based on face recognition. The face recognition-based applet login verification device 500 includes: a preliminary identification processing module 501 for configuring trust The login parameters are used to preliminarily identify the identity of the user logged in with the applet; the SOA account verification module 502 is used to determine whether the user is bound with an SOA account, so as to complete the account verification of the user; the face recognition module 503 is used for In collecting the face image information of the user, and using the pre-trained face recognition model to perform face recognition on the face image of the user; the verification result display module 504 is used for outputting through the face recognition model. The face recognition verification result of the user to display the verif...
PUM
 Login to view more
Login to view more Abstract
Description
Claims
Application Information
 Login to view more
Login to view more - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap