Advanced Quantum Multicast Configurations for Data Security
MAR 17, 202610 MIN READ
Generate Your Research Report Instantly with AI Agent
PatSnap Eureka helps you evaluate technical feasibility & market potential.
Quantum Multicast Background and Security Objectives
Quantum multicast represents a revolutionary paradigm in secure communications, leveraging the fundamental principles of quantum mechanics to enable simultaneous distribution of information to multiple recipients while maintaining unprecedented security guarantees. This technology emerged from the convergence of quantum information theory and classical multicast networking, addressing the growing demand for secure group communications in an increasingly interconnected digital landscape.
The evolution of quantum multicast began with the foundational work in quantum key distribution (QKD) in the 1980s, which demonstrated the theoretical possibility of unconditionally secure point-to-point communications. As quantum technologies matured through the 1990s and 2000s, researchers recognized the potential to extend these security principles to one-to-many communication scenarios, leading to the development of quantum multicast protocols that could distribute quantum states or classical information secured by quantum principles to multiple parties simultaneously.
The core technological foundation rests on quantum entanglement, quantum superposition, and the no-cloning theorem, which collectively ensure that any unauthorized interception or eavesdropping attempts can be detected with mathematical certainty. Unlike classical multicast systems that rely on computational complexity for security, quantum multicast derives its security from the laws of physics themselves, making it theoretically immune to advances in computational power, including potential threats from quantum computers.
Current quantum multicast configurations aim to achieve several critical security objectives that address fundamental vulnerabilities in classical communication systems. The primary objective involves establishing unconditional security guarantees for group communications, ensuring that distributed information remains confidential even against adversaries with unlimited computational resources. This represents a significant advancement over traditional cryptographic approaches that depend on mathematical assumptions about computational difficulty.
Information-theoretic security stands as another fundamental objective, providing provable security bounds that do not rely on unproven mathematical conjectures. This approach ensures that security guarantees remain valid regardless of future technological developments or mathematical breakthroughs that might compromise classical encryption methods.
The technology also targets scalable secure multicast distribution, enabling efficient quantum-secured communications across networks of varying sizes while maintaining security properties. This involves developing protocols that can handle dynamic group membership, network topology changes, and varying quality of service requirements without compromising the underlying security guarantees.
Detection and mitigation of sophisticated attacks represent additional critical objectives, particularly addressing advanced persistent threats and coordinated attacks that might exploit vulnerabilities in classical multicast systems. Quantum multicast configurations incorporate intrinsic tamper-detection mechanisms that can identify unauthorized access attempts in real-time, providing immediate alerts when security breaches are attempted.
The evolution of quantum multicast began with the foundational work in quantum key distribution (QKD) in the 1980s, which demonstrated the theoretical possibility of unconditionally secure point-to-point communications. As quantum technologies matured through the 1990s and 2000s, researchers recognized the potential to extend these security principles to one-to-many communication scenarios, leading to the development of quantum multicast protocols that could distribute quantum states or classical information secured by quantum principles to multiple parties simultaneously.
The core technological foundation rests on quantum entanglement, quantum superposition, and the no-cloning theorem, which collectively ensure that any unauthorized interception or eavesdropping attempts can be detected with mathematical certainty. Unlike classical multicast systems that rely on computational complexity for security, quantum multicast derives its security from the laws of physics themselves, making it theoretically immune to advances in computational power, including potential threats from quantum computers.
Current quantum multicast configurations aim to achieve several critical security objectives that address fundamental vulnerabilities in classical communication systems. The primary objective involves establishing unconditional security guarantees for group communications, ensuring that distributed information remains confidential even against adversaries with unlimited computational resources. This represents a significant advancement over traditional cryptographic approaches that depend on mathematical assumptions about computational difficulty.
Information-theoretic security stands as another fundamental objective, providing provable security bounds that do not rely on unproven mathematical conjectures. This approach ensures that security guarantees remain valid regardless of future technological developments or mathematical breakthroughs that might compromise classical encryption methods.
The technology also targets scalable secure multicast distribution, enabling efficient quantum-secured communications across networks of varying sizes while maintaining security properties. This involves developing protocols that can handle dynamic group membership, network topology changes, and varying quality of service requirements without compromising the underlying security guarantees.
Detection and mitigation of sophisticated attacks represent additional critical objectives, particularly addressing advanced persistent threats and coordinated attacks that might exploit vulnerabilities in classical multicast systems. Quantum multicast configurations incorporate intrinsic tamper-detection mechanisms that can identify unauthorized access attempts in real-time, providing immediate alerts when security breaches are attempted.
Market Demand for Quantum-Secured Multicast Communications
The global telecommunications landscape is experiencing unprecedented demand for quantum-secured multicast communications, driven by escalating cybersecurity threats and the proliferation of sensitive data transmission across multiple endpoints simultaneously. Organizations across various sectors are recognizing the critical need for quantum-enhanced security protocols that can protect multicast data streams from both classical and quantum-based attacks.
Financial services institutions represent one of the most significant market segments driving this demand. High-frequency trading platforms, real-time market data distribution, and secure inter-branch communications require multicast capabilities with quantum-level security assurances. The sector's stringent regulatory requirements and zero-tolerance approach to data breaches create substantial market pull for advanced quantum multicast solutions.
Government and defense agencies constitute another primary demand driver, requiring secure distribution of classified information across multiple military installations and intelligence networks. The emergence of quantum computing threats to traditional encryption methods has accelerated procurement initiatives for quantum-secured communication infrastructure, particularly for multicast scenarios involving command and control systems.
The healthcare industry presents growing market opportunities as telemedicine and distributed medical research expand. Secure multicast transmission of patient data, medical imaging, and research findings across hospital networks and research institutions demands quantum-level protection to ensure HIPAA compliance and patient privacy. The COVID-19 pandemic has further accelerated digital transformation in healthcare, intensifying security requirements.
Enterprise cloud computing and content delivery networks are experiencing surging demand for quantum-secured multicast capabilities. As organizations migrate to hybrid and multi-cloud architectures, the need to securely distribute data across geographically dispersed data centers has become paramount. Video streaming services and digital media companies also require robust multicast security to protect premium content distribution.
The Internet of Things ecosystem presents an emerging but rapidly expanding market segment. Smart city infrastructures, industrial IoT networks, and autonomous vehicle communications increasingly rely on secure multicast protocols to distribute control signals and sensor data across vast networks of connected devices.
Market growth is further accelerated by increasing awareness of quantum computing's potential to compromise existing cryptographic methods. Organizations are proactively investing in quantum-resistant communication technologies to future-proof their infrastructure against emerging quantum threats, creating substantial market momentum for advanced quantum multicast configurations.
Financial services institutions represent one of the most significant market segments driving this demand. High-frequency trading platforms, real-time market data distribution, and secure inter-branch communications require multicast capabilities with quantum-level security assurances. The sector's stringent regulatory requirements and zero-tolerance approach to data breaches create substantial market pull for advanced quantum multicast solutions.
Government and defense agencies constitute another primary demand driver, requiring secure distribution of classified information across multiple military installations and intelligence networks. The emergence of quantum computing threats to traditional encryption methods has accelerated procurement initiatives for quantum-secured communication infrastructure, particularly for multicast scenarios involving command and control systems.
The healthcare industry presents growing market opportunities as telemedicine and distributed medical research expand. Secure multicast transmission of patient data, medical imaging, and research findings across hospital networks and research institutions demands quantum-level protection to ensure HIPAA compliance and patient privacy. The COVID-19 pandemic has further accelerated digital transformation in healthcare, intensifying security requirements.
Enterprise cloud computing and content delivery networks are experiencing surging demand for quantum-secured multicast capabilities. As organizations migrate to hybrid and multi-cloud architectures, the need to securely distribute data across geographically dispersed data centers has become paramount. Video streaming services and digital media companies also require robust multicast security to protect premium content distribution.
The Internet of Things ecosystem presents an emerging but rapidly expanding market segment. Smart city infrastructures, industrial IoT networks, and autonomous vehicle communications increasingly rely on secure multicast protocols to distribute control signals and sensor data across vast networks of connected devices.
Market growth is further accelerated by increasing awareness of quantum computing's potential to compromise existing cryptographic methods. Organizations are proactively investing in quantum-resistant communication technologies to future-proof their infrastructure against emerging quantum threats, creating substantial market momentum for advanced quantum multicast configurations.
Current State and Challenges of Quantum Multicast Systems
Quantum multicast systems represent a cutting-edge convergence of quantum communication principles and multicast networking architectures, designed to enable secure simultaneous data transmission to multiple recipients. Current implementations primarily leverage quantum key distribution (QKD) protocols integrated with classical multicast frameworks, creating hybrid systems that attempt to preserve quantum security properties across multiple communication channels.
The technological landscape is dominated by point-to-point quantum communication solutions, with multicast configurations remaining largely experimental. Existing quantum multicast prototypes utilize quantum entanglement distribution networks and quantum secret sharing protocols to establish secure group communications. These systems typically employ photonic quantum states transmitted through fiber optic networks or free-space optical channels, with quantum repeaters and amplifiers facilitating signal propagation across extended distances.
Several fundamental challenges significantly constrain the practical deployment of quantum multicast systems. Quantum decoherence poses the most critical limitation, as quantum states deteriorate rapidly when transmitted over long distances or through noisy channels. The no-cloning theorem prevents direct replication of quantum states, necessitating complex workarounds for multicast distribution. Scalability issues emerge when attempting to expand beyond small group configurations, as quantum error rates increase exponentially with network size and complexity.
Infrastructure requirements present substantial barriers to widespread adoption. Quantum multicast systems demand specialized hardware including single-photon sources, quantum detectors, and cryogenic cooling systems. The integration of quantum components with existing classical network infrastructure remains technically challenging and economically prohibitive for most organizations. Current systems exhibit limited transmission ranges, typically restricted to metropolitan area networks due to photon loss and quantum state degradation.
Synchronization and timing coordination across multiple quantum channels introduce additional complexity layers. Maintaining quantum coherence while ensuring simultaneous delivery to multiple recipients requires precise temporal control mechanisms that current technology struggles to achieve reliably. Authentication and verification processes for quantum multicast communications remain underdeveloped, creating potential security vulnerabilities despite the inherent quantum cryptographic advantages.
The geographical distribution of quantum multicast research and development is concentrated primarily in advanced research institutions across North America, Europe, and East Asia. Limited commercial implementations exist, with most progress confined to laboratory environments and small-scale proof-of-concept demonstrations, highlighting the significant gap between theoretical potential and practical deployment capabilities.
The technological landscape is dominated by point-to-point quantum communication solutions, with multicast configurations remaining largely experimental. Existing quantum multicast prototypes utilize quantum entanglement distribution networks and quantum secret sharing protocols to establish secure group communications. These systems typically employ photonic quantum states transmitted through fiber optic networks or free-space optical channels, with quantum repeaters and amplifiers facilitating signal propagation across extended distances.
Several fundamental challenges significantly constrain the practical deployment of quantum multicast systems. Quantum decoherence poses the most critical limitation, as quantum states deteriorate rapidly when transmitted over long distances or through noisy channels. The no-cloning theorem prevents direct replication of quantum states, necessitating complex workarounds for multicast distribution. Scalability issues emerge when attempting to expand beyond small group configurations, as quantum error rates increase exponentially with network size and complexity.
Infrastructure requirements present substantial barriers to widespread adoption. Quantum multicast systems demand specialized hardware including single-photon sources, quantum detectors, and cryogenic cooling systems. The integration of quantum components with existing classical network infrastructure remains technically challenging and economically prohibitive for most organizations. Current systems exhibit limited transmission ranges, typically restricted to metropolitan area networks due to photon loss and quantum state degradation.
Synchronization and timing coordination across multiple quantum channels introduce additional complexity layers. Maintaining quantum coherence while ensuring simultaneous delivery to multiple recipients requires precise temporal control mechanisms that current technology struggles to achieve reliably. Authentication and verification processes for quantum multicast communications remain underdeveloped, creating potential security vulnerabilities despite the inherent quantum cryptographic advantages.
The geographical distribution of quantum multicast research and development is concentrated primarily in advanced research institutions across North America, Europe, and East Asia. Limited commercial implementations exist, with most progress confined to laboratory environments and small-scale proof-of-concept demonstrations, highlighting the significant gap between theoretical potential and practical deployment capabilities.
Existing Quantum Multicast Configuration Solutions
01 Quantum key distribution for multicast security
Quantum key distribution (QKD) protocols can be applied to multicast communication scenarios to establish secure encryption keys among multiple parties. This approach leverages quantum mechanical properties to detect eavesdropping attempts and ensure information-theoretic security for group communications. The quantum states are distributed to multiple receivers simultaneously, enabling secure multicast transmissions resistant to computational attacks.- Quantum key distribution for multicast security: Quantum key distribution (QKD) protocols can be applied to multicast communication scenarios to establish secure encryption keys among multiple parties. This approach leverages quantum mechanical properties to detect eavesdropping attempts and ensure the confidentiality of multicast data transmissions. The quantum keys generated through entanglement or prepare-and-measure schemes provide information-theoretic security for group communications.
- Quantum-resistant cryptographic algorithms for multicast: Post-quantum cryptographic algorithms can be integrated into multicast configurations to protect against attacks from quantum computers. These algorithms include lattice-based, code-based, and hash-based cryptographic schemes that remain secure even when quantum computing capabilities advance. Implementation of quantum-resistant encryption ensures long-term security of multicast data streams.
- Quantum entanglement-based multicast authentication: Quantum entanglement can be utilized to create authentication mechanisms for multicast group members. This technique ensures that only authorized participants can access multicast data by verifying quantum states shared among legitimate users. The non-clonability of quantum states provides robust protection against impersonation and unauthorized access in multicast networks.
- Hybrid quantum-classical multicast encryption: Combining quantum and classical cryptographic techniques creates a hybrid approach for securing multicast communications. This method uses quantum channels for key distribution while employing classical encryption algorithms for actual data transmission. The hybrid architecture balances security requirements with practical implementation constraints in multicast network environments.
- Quantum secure multicast routing protocols: Specialized routing protocols can be designed to incorporate quantum security features into multicast network configurations. These protocols manage the distribution of quantum-secured keys across multicast trees and ensure secure path establishment for group communications. Integration of quantum security at the routing layer provides end-to-end protection for multicast data flows.
02 Quantum entanglement-based multicast protocols
Entanglement-based quantum communication protocols enable secure multicast by distributing entangled quantum states among multiple nodes. These protocols utilize quantum correlations to establish shared secret information across the multicast group. The entanglement properties provide inherent security guarantees and enable detection of unauthorized access attempts during the multicast transmission process.Expand Specific Solutions03 Hybrid quantum-classical multicast architectures
Hybrid systems combine quantum communication channels with classical network infrastructure to enable practical quantum-secured multicast. These architectures use quantum channels for key distribution or authentication while leveraging existing classical networks for data transmission. The integration allows scalable deployment of quantum security features in multicast scenarios without requiring complete quantum network infrastructure.Expand Specific Solutions04 Quantum authentication for multicast group management
Quantum authentication mechanisms provide secure identity verification and access control for multicast group members. These techniques use quantum states or quantum-derived credentials to authenticate participants before allowing them to join multicast sessions. The quantum properties ensure that authentication credentials cannot be cloned or forged, preventing unauthorized access to secure multicast communications.Expand Specific Solutions05 Quantum random number generation for multicast encryption
Quantum random number generators provide truly random keys and initialization vectors for encrypting multicast data streams. These generators exploit quantum phenomena to produce unpredictable random numbers that enhance the security of multicast encryption schemes. The quantum-generated randomness eliminates vulnerabilities associated with pseudo-random number generators in conventional multicast security implementations.Expand Specific Solutions
Key Players in Quantum Communication and Multicast Industry
The advanced quantum multicast configurations for data security field represents an emerging technology sector at the intersection of quantum computing and secure communications, currently in its early development stage with significant growth potential. The market remains relatively nascent but shows promising expansion as organizations increasingly recognize quantum threats to traditional cryptographic systems. Technology maturity varies considerably across market participants, with established telecommunications giants like Huawei Technologies, ZTE Corp., Nokia Solutions & Networks, and Ericsson leveraging their extensive networking infrastructure expertise to develop quantum-enhanced security solutions. Specialized quantum security companies such as QuantumCTek, ID Quantique, and Qusecure demonstrate advanced technical capabilities in quantum key distribution and post-quantum cryptography implementations. Technology leaders including Google LLC contribute fundamental quantum computing research, while networking specialists like Cisco Technology, Arista Networks, and New H3C Technologies integrate quantum security features into existing infrastructure platforms, creating a competitive landscape characterized by both innovation-driven startups and established industry players pursuing quantum-safe communication architectures.
Huawei Technologies Co., Ltd.
Technical Solution: Huawei has developed quantum-enhanced multicast security solutions that combine traditional network protocols with quantum cryptographic techniques. Their system implements quantum random number generators for enhanced encryption key generation and utilizes quantum-safe algorithms to protect against future quantum computing threats. The technology features adaptive quantum channel allocation and supports hierarchical quantum key management for large-scale multicast scenarios. Huawei's approach integrates seamlessly with existing 5G infrastructure and provides end-to-end quantum security for mission-critical communications in telecommunications networks.
Strengths: Strong telecommunications infrastructure expertise and comprehensive quantum security portfolio. Weaknesses: Geopolitical restrictions limiting global market access and regulatory compliance challenges.
Google LLC
Technical Solution: Google has developed advanced quantum networking protocols that leverage quantum entanglement for secure multicast communications. Their approach utilizes quantum key distribution (QKD) integrated with classical network infrastructure to enable simultaneous secure data transmission to multiple recipients. The system employs quantum error correction codes and implements sophisticated quantum channel multiplexing techniques to maintain data integrity across distributed quantum networks. Google's quantum multicast solution incorporates machine learning algorithms to optimize routing paths and dynamically adjust quantum states based on network conditions and security requirements.
Strengths: Leading quantum computing research capabilities and robust cloud infrastructure integration. Weaknesses: Limited commercial deployment and high implementation costs for enterprise adoption.
Core Innovations in Advanced Quantum Multicast Protocols
System, apparatus and method for efficient multicast key distribution
PatentWO2012160137A2
Innovation
- The method involves an orthogonal decomposition of a vector space to efficiently distribute and manage cryptographic keys, allowing for secure and rapid key renewal by assigning random vectors to users and using scalar products for decryption, enabling secure multicast communications in dynamic groups.
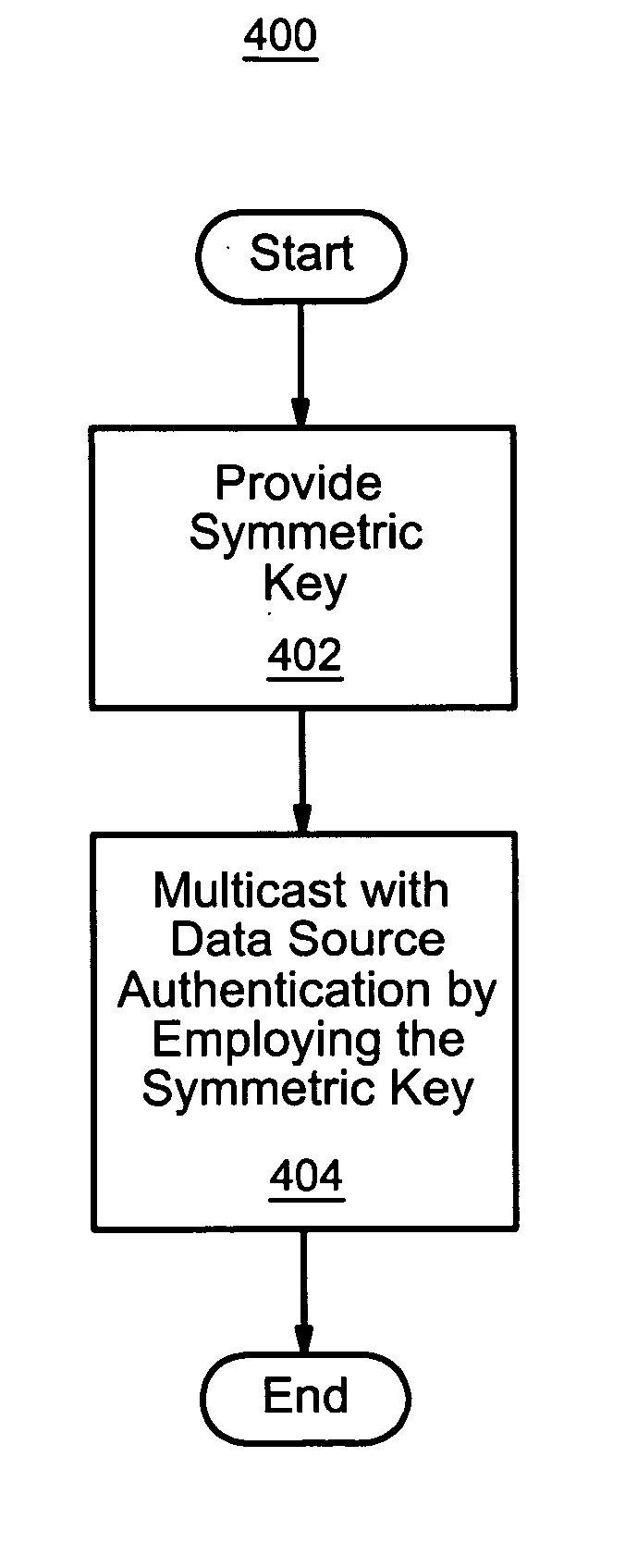
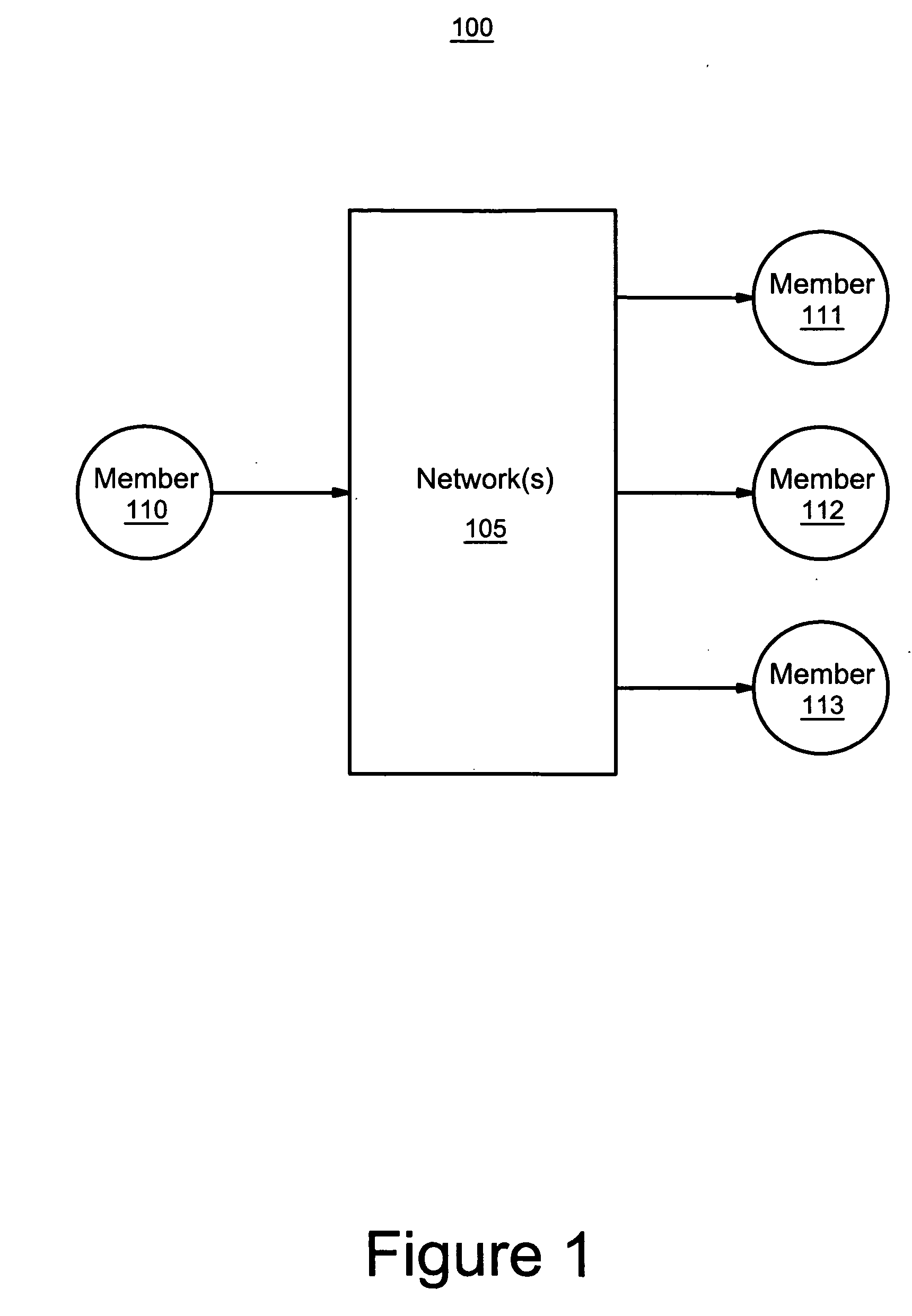
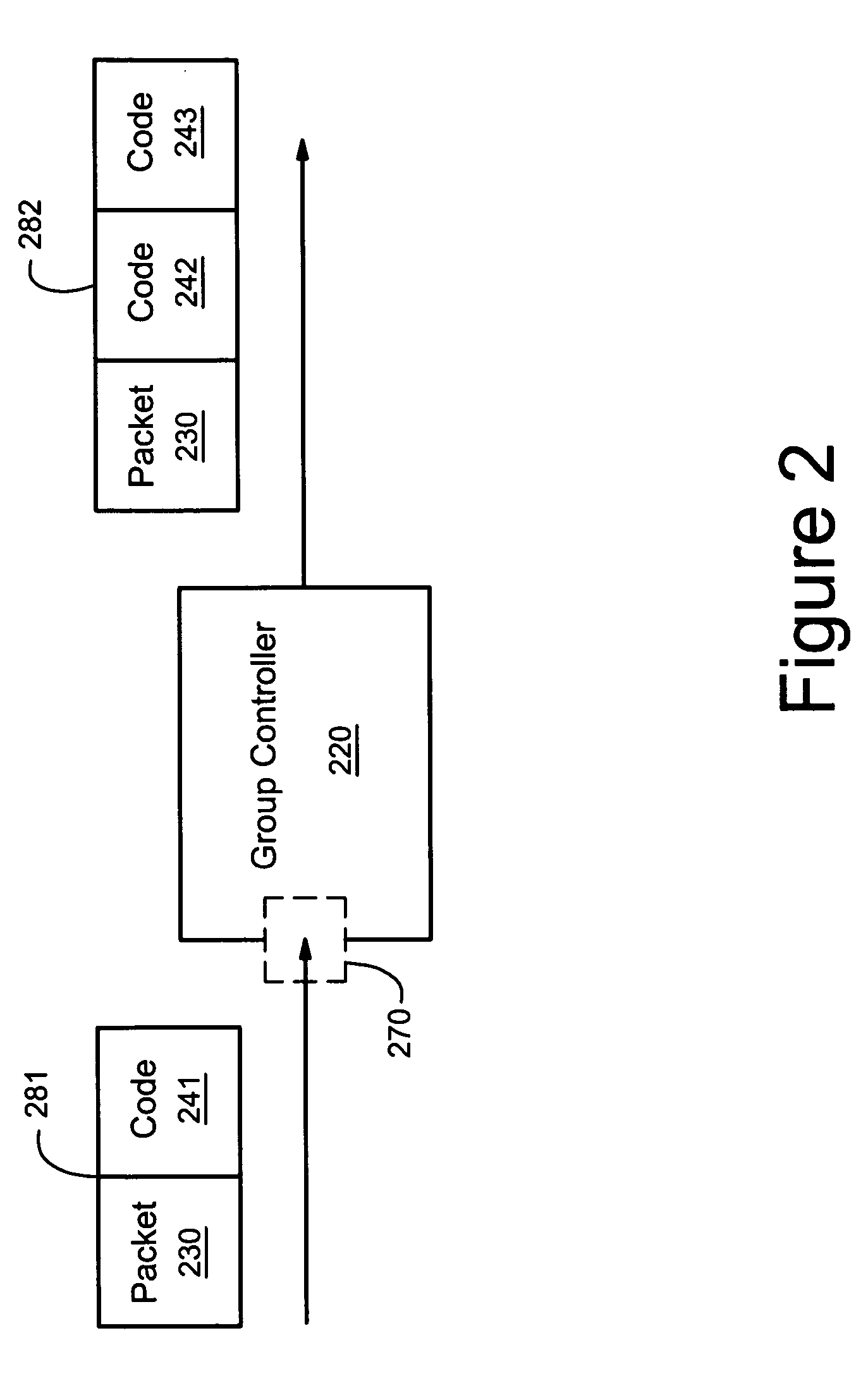
Apparatus and method for data source authentication for multicast security
PatentInactiveUS20050129236A1
Innovation
- Implementing data source authentication through the use of symmetric keys, where packets are unicast to a group controller with a message authentication code (MAC) and then multicast to the group, with each receiving member having a separate MAC generated using their unique symmetric key, ensuring only authorized members can decrypt and receive the packet.
Quantum Technology Regulatory and Standards Framework
The regulatory landscape for quantum multicast technologies is rapidly evolving as governments and international organizations recognize the transformative potential and security implications of quantum communications. Current regulatory frameworks primarily focus on export controls, national security considerations, and research funding guidelines, with limited specific provisions for quantum multicast implementations.
The United States leads regulatory development through the National Quantum Initiative Act and NIST's quantum standards efforts. The European Union has established the Quantum Flagship program alongside emerging data protection regulations that address quantum-resistant cryptography. China has implemented comprehensive quantum technology regulations emphasizing both development promotion and security oversight. These regional approaches create a complex patchwork of compliance requirements for quantum multicast deployments.
International standardization efforts are coordinated through ITU-T Study Group 17 and ISO/IEC JTC 1/SC 27, which are developing quantum key distribution standards applicable to multicast scenarios. The IEEE 802.11 working groups are exploring quantum-enhanced wireless standards, while ETSI has published preliminary specifications for quantum cryptographic protocols. However, specific standards for quantum multicast configurations remain in early development stages.
Critical regulatory gaps exist in areas including cross-border quantum data transmission, liability frameworks for quantum security failures, and certification processes for quantum multicast equipment. Privacy regulations like GDPR require updates to address quantum computing's impact on current encryption methods, particularly in multicast environments where multiple parties access shared quantum-secured channels.
Compliance challenges emerge from the intersection of quantum physics principles with traditional telecommunications regulations. Current frameworks struggle to address quantum entanglement distribution, measurement-based security verification, and the probabilistic nature of quantum protocols in multicast scenarios.
Future regulatory development will likely focus on establishing quantum-specific certification authorities, defining quantum security levels for different applications, and creating international cooperation frameworks for quantum network governance. Harmonization efforts between major regulatory jurisdictions will be essential for enabling global quantum multicast infrastructure deployment while maintaining appropriate security controls and technological sovereignty considerations.
The United States leads regulatory development through the National Quantum Initiative Act and NIST's quantum standards efforts. The European Union has established the Quantum Flagship program alongside emerging data protection regulations that address quantum-resistant cryptography. China has implemented comprehensive quantum technology regulations emphasizing both development promotion and security oversight. These regional approaches create a complex patchwork of compliance requirements for quantum multicast deployments.
International standardization efforts are coordinated through ITU-T Study Group 17 and ISO/IEC JTC 1/SC 27, which are developing quantum key distribution standards applicable to multicast scenarios. The IEEE 802.11 working groups are exploring quantum-enhanced wireless standards, while ETSI has published preliminary specifications for quantum cryptographic protocols. However, specific standards for quantum multicast configurations remain in early development stages.
Critical regulatory gaps exist in areas including cross-border quantum data transmission, liability frameworks for quantum security failures, and certification processes for quantum multicast equipment. Privacy regulations like GDPR require updates to address quantum computing's impact on current encryption methods, particularly in multicast environments where multiple parties access shared quantum-secured channels.
Compliance challenges emerge from the intersection of quantum physics principles with traditional telecommunications regulations. Current frameworks struggle to address quantum entanglement distribution, measurement-based security verification, and the probabilistic nature of quantum protocols in multicast scenarios.
Future regulatory development will likely focus on establishing quantum-specific certification authorities, defining quantum security levels for different applications, and creating international cooperation frameworks for quantum network governance. Harmonization efforts between major regulatory jurisdictions will be essential for enabling global quantum multicast infrastructure deployment while maintaining appropriate security controls and technological sovereignty considerations.
Quantum Cryptography Implementation Risk Assessment
The implementation of advanced quantum multicast configurations for data security introduces several critical risk factors that organizations must carefully evaluate before deployment. These risks span technical, operational, and strategic dimensions, each requiring comprehensive assessment and mitigation strategies.
Technical implementation risks represent the most immediate concerns for quantum cryptography deployment. Quantum key distribution systems are highly sensitive to environmental factors, including temperature fluctuations, electromagnetic interference, and physical vibrations. These sensitivities can lead to increased quantum bit error rates, potentially compromising the security guarantees that quantum cryptography promises to deliver. Additionally, the integration of quantum systems with existing classical network infrastructure presents compatibility challenges that may introduce unexpected vulnerabilities.
Hardware reliability poses another significant risk category, particularly given the current maturity level of quantum technologies. Quantum devices often require specialized maintenance protocols and have limited operational lifespans compared to classical networking equipment. The failure of quantum components can result in complete communication breakdowns, as fallback mechanisms may not maintain the same security levels. This reliability concern is amplified in multicast scenarios where multiple endpoints depend on synchronized quantum states.
Scalability limitations present substantial operational risks for organizations planning large-scale deployments. Current quantum multicast implementations face constraints in terms of the number of simultaneous participants, transmission distances, and data throughput rates. These limitations may force organizations to compromise between security coverage and operational efficiency, potentially creating security gaps in their communication networks.
Human factor risks emerge from the specialized knowledge required to operate and maintain quantum cryptographic systems. The shortage of qualified personnel capable of managing these complex systems increases the likelihood of configuration errors, improper maintenance procedures, and inadequate incident response. Training existing staff requires significant time and resource investments, while recruiting quantum-skilled professionals remains challenging in the current market.
Economic risks encompass both direct implementation costs and potential opportunity costs. The high capital expenditure required for quantum infrastructure deployment may not yield immediate returns, particularly given the evolving nature of the technology. Organizations face the risk of technological obsolescence as quantum standards continue to develop, potentially requiring costly system upgrades or replacements within shorter timeframes than traditional IT investments.
Regulatory and compliance risks add another layer of complexity, as quantum cryptography standards are still emerging across different jurisdictions. Organizations operating in multiple regions may encounter conflicting requirements or face uncertainty regarding future regulatory changes. The lack of established certification processes for quantum systems complicates compliance verification and audit procedures.
Technical implementation risks represent the most immediate concerns for quantum cryptography deployment. Quantum key distribution systems are highly sensitive to environmental factors, including temperature fluctuations, electromagnetic interference, and physical vibrations. These sensitivities can lead to increased quantum bit error rates, potentially compromising the security guarantees that quantum cryptography promises to deliver. Additionally, the integration of quantum systems with existing classical network infrastructure presents compatibility challenges that may introduce unexpected vulnerabilities.
Hardware reliability poses another significant risk category, particularly given the current maturity level of quantum technologies. Quantum devices often require specialized maintenance protocols and have limited operational lifespans compared to classical networking equipment. The failure of quantum components can result in complete communication breakdowns, as fallback mechanisms may not maintain the same security levels. This reliability concern is amplified in multicast scenarios where multiple endpoints depend on synchronized quantum states.
Scalability limitations present substantial operational risks for organizations planning large-scale deployments. Current quantum multicast implementations face constraints in terms of the number of simultaneous participants, transmission distances, and data throughput rates. These limitations may force organizations to compromise between security coverage and operational efficiency, potentially creating security gaps in their communication networks.
Human factor risks emerge from the specialized knowledge required to operate and maintain quantum cryptographic systems. The shortage of qualified personnel capable of managing these complex systems increases the likelihood of configuration errors, improper maintenance procedures, and inadequate incident response. Training existing staff requires significant time and resource investments, while recruiting quantum-skilled professionals remains challenging in the current market.
Economic risks encompass both direct implementation costs and potential opportunity costs. The high capital expenditure required for quantum infrastructure deployment may not yield immediate returns, particularly given the evolving nature of the technology. Organizations face the risk of technological obsolescence as quantum standards continue to develop, potentially requiring costly system upgrades or replacements within shorter timeframes than traditional IT investments.
Regulatory and compliance risks add another layer of complexity, as quantum cryptography standards are still emerging across different jurisdictions. Organizations operating in multiple regions may encounter conflicting requirements or face uncertainty regarding future regulatory changes. The lack of established certification processes for quantum systems complicates compliance verification and audit procedures.
Unlock deeper insights with PatSnap Eureka Quick Research — get a full tech report to explore trends and direct your research. Try now!
Generate Your Research Report Instantly with AI Agent
Supercharge your innovation with PatSnap Eureka AI Agent Platform!