Developing Scalable Access Control Solutions for Enterprises
FEB 27, 20269 MIN READ
Generate Your Research Report Instantly with AI Agent
PatSnap Eureka helps you evaluate technical feasibility & market potential.
Enterprise Access Control Technology Background and Objectives
Enterprise access control has evolved from simple password-based authentication systems in the 1960s to sophisticated multi-layered security frameworks that govern digital resource access across complex organizational structures. The foundational concepts emerged from mainframe computing environments where centralized control was paramount, gradually expanding to accommodate distributed computing, cloud infrastructure, and mobile workforce requirements.
The technological landscape has witnessed significant paradigm shifts, transitioning from discretionary access control models to mandatory and role-based approaches. Modern enterprises now grapple with hybrid environments spanning on-premises infrastructure, multiple cloud platforms, and edge computing resources, necessitating unified access governance that maintains security while enabling operational agility.
Contemporary access control challenges stem from the exponential growth of digital identities, applications, and data repositories within enterprise ecosystems. Organizations typically manage thousands of user accounts, hundreds of applications, and complex permission matrices that traditional systems struggle to handle efficiently. The proliferation of remote work, third-party integrations, and regulatory compliance requirements has further amplified the complexity of access management.
The primary objective of scalable access control solutions centers on establishing dynamic, policy-driven frameworks capable of managing millions of access decisions per second while maintaining sub-millisecond response times. These systems must seamlessly integrate with existing enterprise infrastructure, support zero-trust security models, and provide granular visibility into access patterns and potential security threats.
Strategic goals encompass the development of adaptive authentication mechanisms that leverage behavioral analytics, contextual risk assessment, and machine learning algorithms to make intelligent access decisions. The solutions must demonstrate horizontal scalability to accommodate organizational growth, support federated identity management across business partnerships, and ensure compliance with evolving regulatory frameworks such as GDPR, SOX, and industry-specific mandates.
Future-oriented objectives include the implementation of autonomous access governance systems that can automatically provision, modify, and revoke permissions based on organizational changes, project requirements, and risk profiles. These solutions aim to reduce administrative overhead by up to 80% while enhancing security posture through continuous monitoring and real-time threat response capabilities.
The technological landscape has witnessed significant paradigm shifts, transitioning from discretionary access control models to mandatory and role-based approaches. Modern enterprises now grapple with hybrid environments spanning on-premises infrastructure, multiple cloud platforms, and edge computing resources, necessitating unified access governance that maintains security while enabling operational agility.
Contemporary access control challenges stem from the exponential growth of digital identities, applications, and data repositories within enterprise ecosystems. Organizations typically manage thousands of user accounts, hundreds of applications, and complex permission matrices that traditional systems struggle to handle efficiently. The proliferation of remote work, third-party integrations, and regulatory compliance requirements has further amplified the complexity of access management.
The primary objective of scalable access control solutions centers on establishing dynamic, policy-driven frameworks capable of managing millions of access decisions per second while maintaining sub-millisecond response times. These systems must seamlessly integrate with existing enterprise infrastructure, support zero-trust security models, and provide granular visibility into access patterns and potential security threats.
Strategic goals encompass the development of adaptive authentication mechanisms that leverage behavioral analytics, contextual risk assessment, and machine learning algorithms to make intelligent access decisions. The solutions must demonstrate horizontal scalability to accommodate organizational growth, support federated identity management across business partnerships, and ensure compliance with evolving regulatory frameworks such as GDPR, SOX, and industry-specific mandates.
Future-oriented objectives include the implementation of autonomous access governance systems that can automatically provision, modify, and revoke permissions based on organizational changes, project requirements, and risk profiles. These solutions aim to reduce administrative overhead by up to 80% while enhancing security posture through continuous monitoring and real-time threat response capabilities.
Market Demand Analysis for Scalable Enterprise Access Solutions
The enterprise access control market is experiencing unprecedented growth driven by the accelerating digital transformation initiatives across industries. Organizations are rapidly adopting cloud-first strategies, implementing hybrid work models, and expanding their digital ecosystems, creating complex security challenges that traditional access control systems cannot adequately address. This transformation has fundamentally altered how businesses approach identity and access management, shifting from perimeter-based security models to zero-trust architectures.
Remote work adoption has become a permanent fixture in modern business operations, significantly amplifying the demand for scalable access solutions. Organizations now require systems capable of securely managing access for distributed workforces while maintaining seamless user experiences. The proliferation of mobile devices, cloud applications, and third-party integrations has created an exponential increase in access points that need continuous monitoring and control.
Regulatory compliance requirements are intensifying across multiple sectors, particularly in healthcare, financial services, and government organizations. Frameworks such as GDPR, HIPAA, SOX, and emerging data protection regulations mandate sophisticated access controls with comprehensive audit trails and real-time monitoring capabilities. These compliance demands are driving organizations to seek solutions that can demonstrate granular access governance and provide detailed reporting mechanisms.
The cybersecurity threat landscape continues to evolve with increasingly sophisticated attack vectors targeting identity and access vulnerabilities. High-profile data breaches attributed to compromised credentials and privilege escalation have elevated access control from an IT concern to a board-level priority. Organizations are recognizing that traditional username-password authentication is insufficient for protecting critical assets and sensitive data.
Market demand is particularly strong among mid-to-large enterprises operating in highly regulated industries or those with complex organizational structures. Technology companies, healthcare systems, financial institutions, and government agencies represent the primary demand drivers, seeking solutions that can scale across thousands of users while maintaining security integrity. These organizations require adaptive access controls that can respond to changing business needs without compromising security posture.
The emergence of artificial intelligence and machine learning technologies is creating new expectations for intelligent access management. Organizations are seeking solutions that can provide behavioral analytics, anomaly detection, and automated risk assessment capabilities. This demand for intelligent automation reflects the growing recognition that manual access management processes cannot scale effectively in modern enterprise environments.
Remote work adoption has become a permanent fixture in modern business operations, significantly amplifying the demand for scalable access solutions. Organizations now require systems capable of securely managing access for distributed workforces while maintaining seamless user experiences. The proliferation of mobile devices, cloud applications, and third-party integrations has created an exponential increase in access points that need continuous monitoring and control.
Regulatory compliance requirements are intensifying across multiple sectors, particularly in healthcare, financial services, and government organizations. Frameworks such as GDPR, HIPAA, SOX, and emerging data protection regulations mandate sophisticated access controls with comprehensive audit trails and real-time monitoring capabilities. These compliance demands are driving organizations to seek solutions that can demonstrate granular access governance and provide detailed reporting mechanisms.
The cybersecurity threat landscape continues to evolve with increasingly sophisticated attack vectors targeting identity and access vulnerabilities. High-profile data breaches attributed to compromised credentials and privilege escalation have elevated access control from an IT concern to a board-level priority. Organizations are recognizing that traditional username-password authentication is insufficient for protecting critical assets and sensitive data.
Market demand is particularly strong among mid-to-large enterprises operating in highly regulated industries or those with complex organizational structures. Technology companies, healthcare systems, financial institutions, and government agencies represent the primary demand drivers, seeking solutions that can scale across thousands of users while maintaining security integrity. These organizations require adaptive access controls that can respond to changing business needs without compromising security posture.
The emergence of artificial intelligence and machine learning technologies is creating new expectations for intelligent access management. Organizations are seeking solutions that can provide behavioral analytics, anomaly detection, and automated risk assessment capabilities. This demand for intelligent automation reflects the growing recognition that manual access management processes cannot scale effectively in modern enterprise environments.
Current State and Challenges in Enterprise Access Control Systems
Enterprise access control systems have evolved significantly over the past decade, transitioning from traditional perimeter-based security models to more sophisticated, identity-centric approaches. Currently, most organizations employ a hybrid architecture combining on-premises Active Directory systems with cloud-based identity providers such as Azure AD, Okta, and AWS IAM. This evolution reflects the fundamental shift toward distributed workforces and multi-cloud environments that characterize modern enterprise operations.
The predominant access control frameworks in use today include Role-Based Access Control (RBAC), Attribute-Based Access Control (ABAC), and emerging Zero Trust architectures. RBAC remains the most widely implemented model due to its simplicity and compatibility with existing infrastructure, while ABAC is gaining traction for its granular policy capabilities. Zero Trust principles are increasingly being adopted as organizations recognize the limitations of traditional network perimeter security.
Despite technological advances, enterprises face significant scalability challenges when managing access control across diverse environments. Legacy systems often lack the flexibility to integrate seamlessly with modern cloud services, creating security gaps and administrative overhead. The proliferation of Software-as-a-Service applications has exponentially increased the number of access points requiring management, straining traditional provisioning and deprovisioning processes.
Identity sprawl represents another critical challenge, with employees typically maintaining multiple digital identities across various systems and platforms. This fragmentation complicates user lifecycle management and increases the risk of orphaned accounts remaining active after employee departures. Organizations struggle to maintain consistent access policies across heterogeneous environments while ensuring compliance with regulatory requirements such as SOX, GDPR, and industry-specific mandates.
Performance bottlenecks emerge as enterprises scale their access control infrastructure to support thousands or tens of thousands of users. Authentication latency and policy evaluation delays can significantly impact user productivity, particularly in geographically distributed organizations. The complexity of managing fine-grained permissions across multiple resource types and locations often leads to over-privileged access as administrators opt for broader permissions to avoid operational friction.
Emerging technologies such as artificial intelligence and machine learning are beginning to address some of these challenges through adaptive authentication and automated policy recommendations. However, implementation complexity and the need for specialized expertise limit widespread adoption. The integration of biometric authentication and behavioral analytics shows promise for enhancing security while maintaining user experience, though privacy concerns and regulatory compliance requirements present additional considerations for enterprise deployment.
The predominant access control frameworks in use today include Role-Based Access Control (RBAC), Attribute-Based Access Control (ABAC), and emerging Zero Trust architectures. RBAC remains the most widely implemented model due to its simplicity and compatibility with existing infrastructure, while ABAC is gaining traction for its granular policy capabilities. Zero Trust principles are increasingly being adopted as organizations recognize the limitations of traditional network perimeter security.
Despite technological advances, enterprises face significant scalability challenges when managing access control across diverse environments. Legacy systems often lack the flexibility to integrate seamlessly with modern cloud services, creating security gaps and administrative overhead. The proliferation of Software-as-a-Service applications has exponentially increased the number of access points requiring management, straining traditional provisioning and deprovisioning processes.
Identity sprawl represents another critical challenge, with employees typically maintaining multiple digital identities across various systems and platforms. This fragmentation complicates user lifecycle management and increases the risk of orphaned accounts remaining active after employee departures. Organizations struggle to maintain consistent access policies across heterogeneous environments while ensuring compliance with regulatory requirements such as SOX, GDPR, and industry-specific mandates.
Performance bottlenecks emerge as enterprises scale their access control infrastructure to support thousands or tens of thousands of users. Authentication latency and policy evaluation delays can significantly impact user productivity, particularly in geographically distributed organizations. The complexity of managing fine-grained permissions across multiple resource types and locations often leads to over-privileged access as administrators opt for broader permissions to avoid operational friction.
Emerging technologies such as artificial intelligence and machine learning are beginning to address some of these challenges through adaptive authentication and automated policy recommendations. However, implementation complexity and the need for specialized expertise limit widespread adoption. The integration of biometric authentication and behavioral analytics shows promise for enhancing security while maintaining user experience, though privacy concerns and regulatory compliance requirements present additional considerations for enterprise deployment.
Current Scalable Access Control Technical Solutions
01 Distributed access control architecture
Implementing distributed access control systems that can scale horizontally by distributing authentication and authorization processes across multiple nodes or servers. This approach allows the system to handle increased loads by adding more processing units, improving overall system performance and reliability. The architecture typically includes load balancing mechanisms and redundant components to ensure continuous operation even as the system scales.- Distributed access control architecture: Implementing distributed access control systems that can scale horizontally by distributing authentication and authorization processes across multiple nodes or servers. This approach allows the system to handle increased loads by adding more processing units, enabling better performance as the number of users and access requests grows. The architecture typically includes load balancing mechanisms and redundant components to ensure high availability and fault tolerance.
- Role-based and attribute-based access control mechanisms: Utilizing flexible access control models that can efficiently manage permissions for large numbers of users and resources. These mechanisms allow for hierarchical organization of access rights and dynamic policy evaluation, reducing administrative overhead while maintaining security. The scalable design enables organizations to manage complex permission structures across growing user bases and expanding resource portfolios without performance degradation.
- Cloud-based access control services: Leveraging cloud infrastructure to provide scalable access control solutions that can automatically adjust resources based on demand. These services utilize elastic computing resources and distributed databases to handle varying loads efficiently. The cloud-based approach enables organizations to scale their access control systems without significant upfront infrastructure investments, supporting both small deployments and enterprise-level implementations with millions of users.
- Caching and optimization techniques: Implementing intelligent caching strategies and optimization algorithms to reduce latency and improve throughput in access control systems. These techniques include caching frequently accessed permissions, pre-computing authorization decisions, and using efficient data structures for rapid policy evaluation. The optimization methods enable systems to handle high-volume access requests while maintaining low response times, crucial for scalability in large-scale deployments.
- Federated identity and single sign-on integration: Adopting federated identity management and single sign-on solutions that enable scalable access control across multiple systems and domains. These approaches allow users to authenticate once and access multiple resources, reducing authentication overhead and improving user experience. The federated architecture supports scalability by distributing authentication responsibilities and enabling seamless integration with external identity providers, facilitating growth across organizational boundaries.
02 Cloud-based access control management
Utilizing cloud infrastructure to provide scalable access control solutions that can dynamically adjust resources based on demand. This approach leverages virtualization and elastic computing resources to accommodate varying numbers of users, devices, and access points without requiring significant hardware investments. The system can automatically scale up or down based on real-time usage patterns and requirements.Expand Specific Solutions03 Hierarchical access control frameworks
Designing multi-tiered access control systems that organize permissions and authentication in hierarchical structures, enabling efficient management of large-scale deployments. This framework allows for delegation of administrative tasks and localized control while maintaining centralized oversight. The hierarchical approach reduces processing overhead and improves response times by distributing decision-making across different levels of the organization.Expand Specific Solutions04 Caching and optimization mechanisms
Implementing intelligent caching strategies and optimization techniques to reduce latency and improve system responsiveness in large-scale access control deployments. These mechanisms store frequently accessed credentials, permissions, and authentication tokens locally or in distributed caches, minimizing the need for repeated database queries. The optimization includes efficient data structures and algorithms that can handle high-volume access requests with minimal computational overhead.Expand Specific Solutions05 Modular and extensible system design
Creating access control solutions with modular architectures that support easy integration of additional components and features as system requirements grow. This design approach uses standardized interfaces and protocols that allow seamless addition of new authentication methods, access points, and security features without disrupting existing operations. The extensible framework ensures long-term scalability by accommodating future technological advances and changing security requirements.Expand Specific Solutions
Major Players in Enterprise Access Control Market
The enterprise access control solutions market is experiencing rapid growth driven by increasing cybersecurity threats and regulatory compliance requirements. The industry is in a mature expansion phase with significant market opportunities, as organizations transition from traditional perimeter-based security to zero-trust architectures. Technology maturity varies considerably across players, with established giants like Oracle, IBM, Microsoft, and SAP offering comprehensive enterprise-grade platforms, while cloud leaders Amazon and specialized vendors like Citrix and SailPoint provide innovative cloud-native solutions. Emerging players such as Oleria Corp. are introducing AI-driven identity security capabilities, and traditional hardware companies like ASSA ABLOY are expanding into digital access management. The competitive landscape spans from infrastructure providers (Huawei, HPE, Dell) to pure-play security specialists, indicating a fragmented but rapidly consolidating market with increasing emphasis on AI-powered automation and unified identity governance platforms.
Oracle International Corp.
Technical Solution: Oracle delivers enterprise access control through Oracle Identity Cloud Service (IDCS) and Oracle Access Management solutions. Their platform provides comprehensive identity governance, featuring automated user lifecycle management, access certification campaigns, and segregation of duties controls. Oracle's approach emphasizes risk-based authentication and adaptive access policies, supporting both on-premises and cloud deployments. The solution includes advanced analytics for access risk assessment and compliance reporting, with built-in connectors for hundreds of enterprise applications. Oracle's architecture supports high-availability deployments and can scale to support millions of identities across global enterprises.
Strengths: Strong enterprise governance capabilities, comprehensive compliance features, robust on-premises integration. Weaknesses: Higher cost of ownership, complex implementation process, limited modern API capabilities compared to cloud-native solutions.
International Business Machines Corp.
Technical Solution: IBM provides scalable access control through IBM Security Verify and IBM Security Access Manager solutions. Their approach combines AI-powered risk assessment with traditional access control mechanisms, offering context-aware authentication and authorization. IBM's platform supports federated identity management, API security, and mobile access management, with particular strength in hybrid cloud environments. The solution includes advanced threat detection capabilities and integrates with IBM's broader security ecosystem. IBM emphasizes zero-trust principles with continuous verification and adaptive policies based on user behavior analytics and machine learning algorithms.
Strengths: Strong AI integration for risk assessment, excellent hybrid cloud support, comprehensive threat intelligence integration. Weaknesses: Complex architecture requiring specialized expertise, higher implementation costs, slower innovation pace compared to cloud-native competitors.
Core Technologies in Scalable Access Control Systems
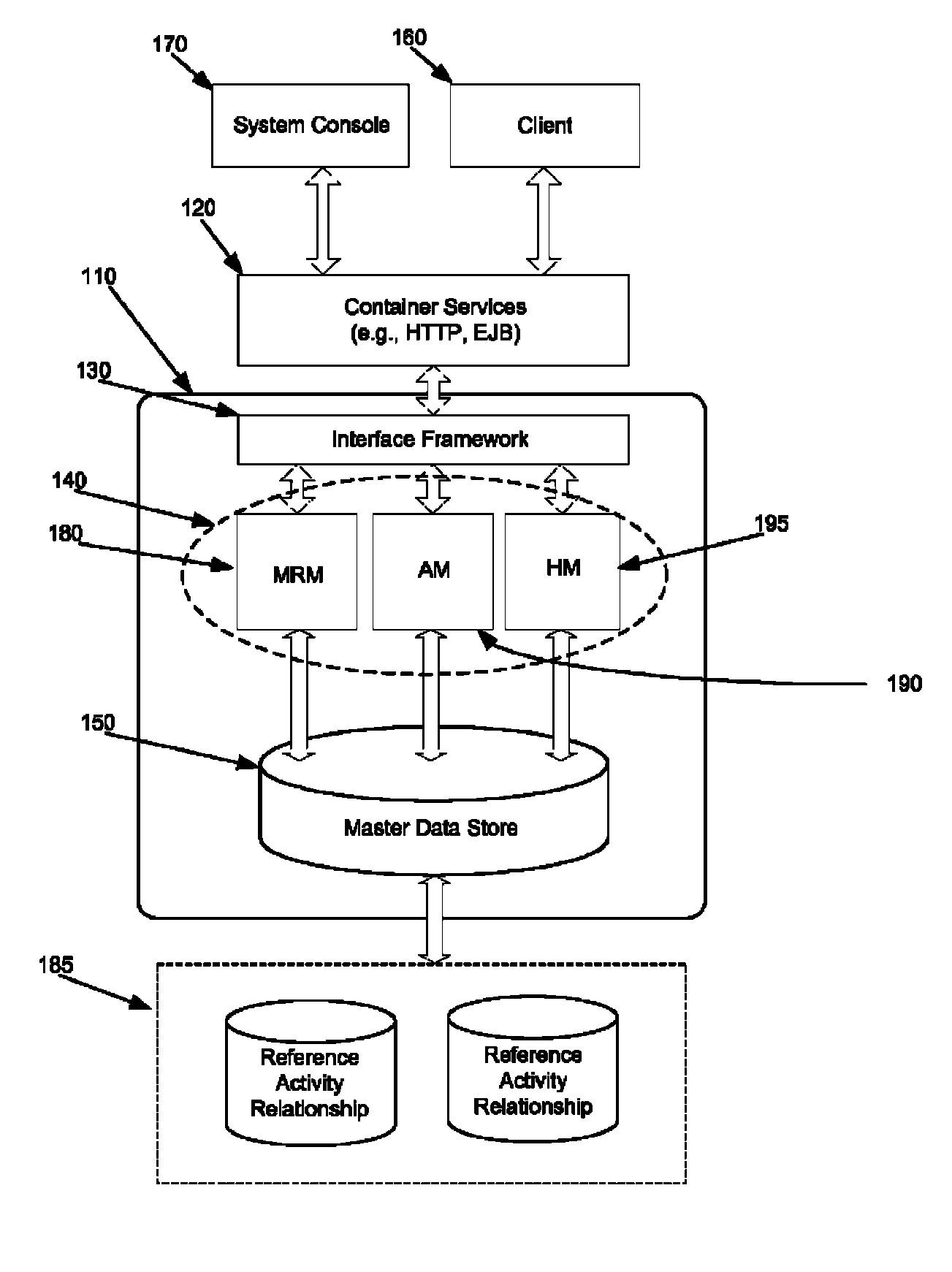
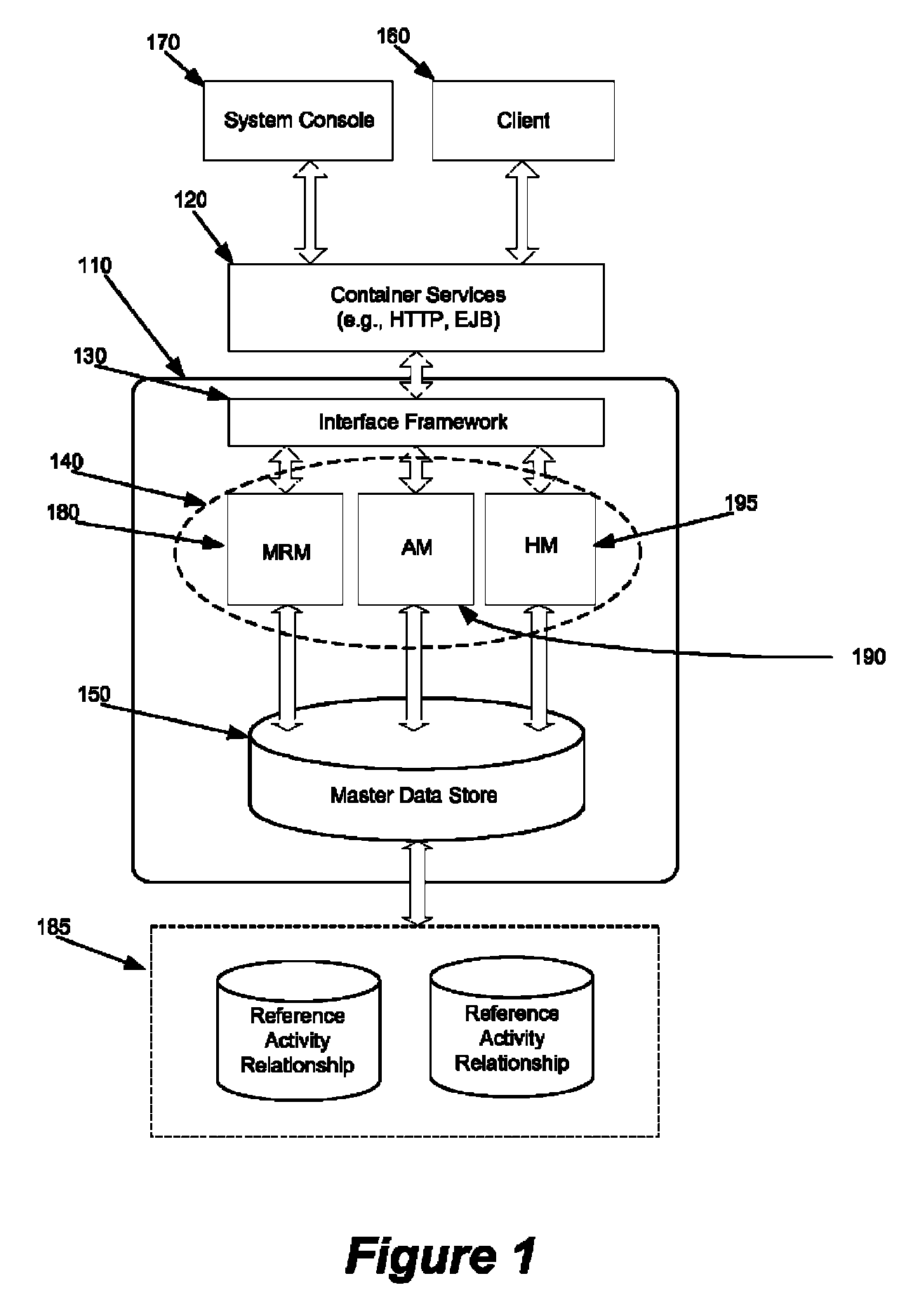
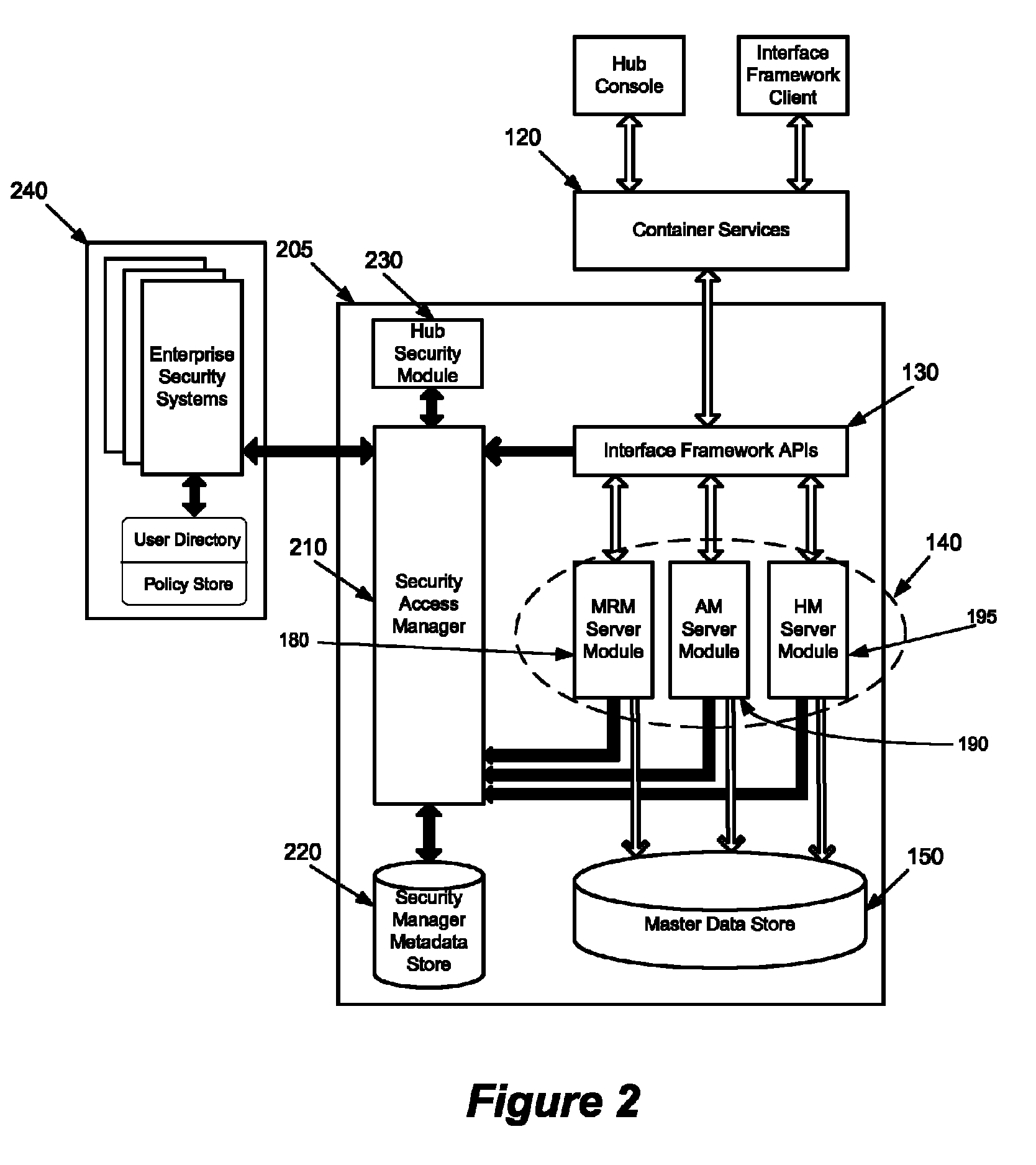
System and method for flexible security access management in an enterprise
PatentActiveUS8224873B1
Innovation
- A security access manager (SAM) that integrates with multiple security systems, providing configurable management modules for authentication, authorization, and role mapping, allowing for distributed security access control and the ability to scale by adding or removing security systems, while leveraging different security models such as role-based and policy-based access.
Systems and methods for secure, scalable zero trust security processing
PatentPendingUS20240333772A1
Innovation
- The implementation of a system that uses endpoint agents, endpoint management systems, and access nodes to perform scalable zero trust network access control, integrating UTM, threat, and malware scans, and generating device records based on security postures to manage network access.
Compliance and Security Standards for Enterprise Access
Enterprise access control solutions must operate within a complex framework of compliance and security standards that vary across industries, geographical regions, and organizational requirements. The regulatory landscape encompasses multiple layers of requirements, from international frameworks like ISO 27001 and NIST Cybersecurity Framework to industry-specific mandates such as HIPAA for healthcare, PCI DSS for payment processing, and SOX for financial reporting. These standards establish baseline security controls that access management systems must implement and maintain throughout their operational lifecycle.
Data protection regulations represent a critical compliance dimension for enterprise access control systems. The General Data Protection Regulation (GDPR) in Europe and similar privacy laws worldwide impose strict requirements on how organizations collect, process, and protect personal data. Access control solutions must incorporate privacy-by-design principles, ensuring that data access is limited to authorized personnel with legitimate business purposes. This includes implementing granular permission structures, maintaining detailed audit trails, and providing mechanisms for data subject rights such as access requests and deletion requirements.
Industry-specific compliance frameworks add additional layers of complexity to access control implementations. Financial services organizations must adhere to regulations like Basel III and MiFID II, which mandate strict segregation of duties and real-time monitoring of privileged access. Healthcare entities face HIPAA requirements that demand role-based access controls aligned with minimum necessary standards for protected health information. Government contractors must comply with frameworks such as NIST 800-171 and CMMC, which specify detailed technical safeguards for controlled unclassified information.
Security certification standards provide structured approaches for implementing and validating access control measures. ISO 27001 establishes comprehensive information security management requirements, including access control policies, user access management, and system access controls. The NIST Cybersecurity Framework offers a risk-based approach to cybersecurity that emphasizes identity management and access control as core protective functions. These frameworks require organizations to implement continuous monitoring, regular assessments, and documented procedures for access provisioning and deprovisioning.
Emerging regulatory trends are reshaping compliance requirements for enterprise access control solutions. Zero-trust security models are becoming regulatory expectations rather than optional enhancements, with frameworks increasingly emphasizing continuous verification and least-privilege access principles. Cross-border data transfer regulations are creating new challenges for multinational organizations, requiring access control systems to enforce data residency requirements and implement appropriate safeguards for international data flows.
Data protection regulations represent a critical compliance dimension for enterprise access control systems. The General Data Protection Regulation (GDPR) in Europe and similar privacy laws worldwide impose strict requirements on how organizations collect, process, and protect personal data. Access control solutions must incorporate privacy-by-design principles, ensuring that data access is limited to authorized personnel with legitimate business purposes. This includes implementing granular permission structures, maintaining detailed audit trails, and providing mechanisms for data subject rights such as access requests and deletion requirements.
Industry-specific compliance frameworks add additional layers of complexity to access control implementations. Financial services organizations must adhere to regulations like Basel III and MiFID II, which mandate strict segregation of duties and real-time monitoring of privileged access. Healthcare entities face HIPAA requirements that demand role-based access controls aligned with minimum necessary standards for protected health information. Government contractors must comply with frameworks such as NIST 800-171 and CMMC, which specify detailed technical safeguards for controlled unclassified information.
Security certification standards provide structured approaches for implementing and validating access control measures. ISO 27001 establishes comprehensive information security management requirements, including access control policies, user access management, and system access controls. The NIST Cybersecurity Framework offers a risk-based approach to cybersecurity that emphasizes identity management and access control as core protective functions. These frameworks require organizations to implement continuous monitoring, regular assessments, and documented procedures for access provisioning and deprovisioning.
Emerging regulatory trends are reshaping compliance requirements for enterprise access control solutions. Zero-trust security models are becoming regulatory expectations rather than optional enhancements, with frameworks increasingly emphasizing continuous verification and least-privilege access principles. Cross-border data transfer regulations are creating new challenges for multinational organizations, requiring access control systems to enforce data residency requirements and implement appropriate safeguards for international data flows.
Zero Trust Architecture Implementation Strategies
Zero Trust Architecture represents a paradigm shift from traditional perimeter-based security models to a comprehensive "never trust, always verify" approach. This implementation strategy fundamentally transforms how enterprises approach access control by eliminating implicit trust assumptions and continuously validating every transaction and access request regardless of location or user credentials.
The foundational principle of Zero Trust implementation begins with identity verification as the new security perimeter. Organizations must establish robust identity and access management systems that authenticate and authorize users, devices, and applications before granting any network access. This approach requires implementing multi-factor authentication, continuous identity verification, and dynamic risk assessment mechanisms that evaluate user behavior patterns and contextual factors in real-time.
Network segmentation forms another critical component of Zero Trust implementation strategies. Enterprises must adopt micro-segmentation techniques that create granular security zones, limiting lateral movement within networks. This involves deploying software-defined perimeters and implementing least-privilege access principles where users and systems receive only the minimum permissions necessary to perform their designated functions.
Device trust and endpoint security constitute essential elements of comprehensive Zero Trust deployment. Organizations need to implement device registration, compliance monitoring, and continuous health assessment protocols. This includes deploying endpoint detection and response solutions, ensuring device encryption, and maintaining updated security patches across all connected devices within the enterprise ecosystem.
Data protection and classification strategies require careful integration within Zero Trust frameworks. Enterprises must implement data loss prevention mechanisms, encryption protocols, and access controls that follow data throughout its lifecycle. This involves establishing clear data governance policies and implementing technologies that can identify, classify, and protect sensitive information regardless of its location or access method.
Monitoring and analytics capabilities provide the intelligence foundation for effective Zero Trust implementation. Organizations need to deploy comprehensive logging, behavioral analytics, and threat detection systems that can identify anomalous activities and potential security breaches. These systems must provide real-time visibility into user activities, network traffic, and system behaviors to enable rapid response to security incidents.
The implementation process requires phased deployment approaches that minimize operational disruption while gradually expanding Zero Trust principles across enterprise infrastructure. Organizations typically begin with high-value assets and critical applications before extending coverage to broader network segments and user populations.
The foundational principle of Zero Trust implementation begins with identity verification as the new security perimeter. Organizations must establish robust identity and access management systems that authenticate and authorize users, devices, and applications before granting any network access. This approach requires implementing multi-factor authentication, continuous identity verification, and dynamic risk assessment mechanisms that evaluate user behavior patterns and contextual factors in real-time.
Network segmentation forms another critical component of Zero Trust implementation strategies. Enterprises must adopt micro-segmentation techniques that create granular security zones, limiting lateral movement within networks. This involves deploying software-defined perimeters and implementing least-privilege access principles where users and systems receive only the minimum permissions necessary to perform their designated functions.
Device trust and endpoint security constitute essential elements of comprehensive Zero Trust deployment. Organizations need to implement device registration, compliance monitoring, and continuous health assessment protocols. This includes deploying endpoint detection and response solutions, ensuring device encryption, and maintaining updated security patches across all connected devices within the enterprise ecosystem.
Data protection and classification strategies require careful integration within Zero Trust frameworks. Enterprises must implement data loss prevention mechanisms, encryption protocols, and access controls that follow data throughout its lifecycle. This involves establishing clear data governance policies and implementing technologies that can identify, classify, and protect sensitive information regardless of its location or access method.
Monitoring and analytics capabilities provide the intelligence foundation for effective Zero Trust implementation. Organizations need to deploy comprehensive logging, behavioral analytics, and threat detection systems that can identify anomalous activities and potential security breaches. These systems must provide real-time visibility into user activities, network traffic, and system behaviors to enable rapid response to security incidents.
The implementation process requires phased deployment approaches that minimize operational disruption while gradually expanding Zero Trust principles across enterprise infrastructure. Organizations typically begin with high-value assets and critical applications before extending coverage to broader network segments and user populations.
Unlock deeper insights with PatSnap Eureka Quick Research — get a full tech report to explore trends and direct your research. Try now!
Generate Your Research Report Instantly with AI Agent
Supercharge your innovation with PatSnap Eureka AI Agent Platform!