Enhancing Network Security with Advanced Optical Switching
APR 11, 20269 MIN READ
Generate Your Research Report Instantly with AI Agent
Patsnap Eureka helps you evaluate technical feasibility & market potential.
Optical Switching Network Security Background and Objectives
The evolution of network infrastructure has fundamentally transformed how organizations manage and secure their digital communications. Traditional electronic switching systems, while effective for decades, now face unprecedented challenges in meeting the demands of modern high-speed, high-capacity networks. The exponential growth in data traffic, driven by cloud computing, IoT devices, and real-time applications, has exposed critical limitations in conventional network architectures, particularly regarding security vulnerabilities and performance bottlenecks.
Optical switching technology represents a paradigm shift in network infrastructure, offering the potential to address these fundamental challenges through photonic signal processing. Unlike electronic switches that convert optical signals to electrical form for processing, optical switches maintain signals in their native photonic state, enabling faster processing speeds and reduced latency. This technological approach has gained significant momentum as organizations seek solutions that can simultaneously enhance network performance and security posture.
The convergence of optical switching with advanced security mechanisms has emerged as a critical research area, driven by the increasing sophistication of cyber threats and the need for real-time threat detection and mitigation. Traditional network security approaches often introduce additional latency and processing overhead, creating tension between security requirements and performance objectives. Optical switching presents unique opportunities to integrate security functions directly into the network fabric without compromising speed or efficiency.
The primary objective of enhancing network security through advanced optical switching is to develop integrated solutions that provide robust protection against evolving cyber threats while maintaining the high-speed, low-latency characteristics essential for modern applications. This involves creating optical switching architectures that can perform real-time traffic analysis, implement dynamic security policies, and respond to threats at the speed of light.
Key technical objectives include developing optical switching systems capable of deep packet inspection without electronic conversion, implementing quantum-resistant security protocols within optical networks, and creating adaptive switching mechanisms that can isolate compromised network segments instantaneously. Additionally, the integration of machine learning algorithms with optical switching hardware aims to enable predictive threat detection and automated response capabilities.
The strategic goal extends beyond mere performance improvements to establish a new security paradigm where protection mechanisms are inherently embedded within the network infrastructure rather than applied as external layers. This approach promises to deliver unprecedented levels of security while enabling the ultra-low latency and high bandwidth requirements of next-generation applications.
Optical switching technology represents a paradigm shift in network infrastructure, offering the potential to address these fundamental challenges through photonic signal processing. Unlike electronic switches that convert optical signals to electrical form for processing, optical switches maintain signals in their native photonic state, enabling faster processing speeds and reduced latency. This technological approach has gained significant momentum as organizations seek solutions that can simultaneously enhance network performance and security posture.
The convergence of optical switching with advanced security mechanisms has emerged as a critical research area, driven by the increasing sophistication of cyber threats and the need for real-time threat detection and mitigation. Traditional network security approaches often introduce additional latency and processing overhead, creating tension between security requirements and performance objectives. Optical switching presents unique opportunities to integrate security functions directly into the network fabric without compromising speed or efficiency.
The primary objective of enhancing network security through advanced optical switching is to develop integrated solutions that provide robust protection against evolving cyber threats while maintaining the high-speed, low-latency characteristics essential for modern applications. This involves creating optical switching architectures that can perform real-time traffic analysis, implement dynamic security policies, and respond to threats at the speed of light.
Key technical objectives include developing optical switching systems capable of deep packet inspection without electronic conversion, implementing quantum-resistant security protocols within optical networks, and creating adaptive switching mechanisms that can isolate compromised network segments instantaneously. Additionally, the integration of machine learning algorithms with optical switching hardware aims to enable predictive threat detection and automated response capabilities.
The strategic goal extends beyond mere performance improvements to establish a new security paradigm where protection mechanisms are inherently embedded within the network infrastructure rather than applied as external layers. This approach promises to deliver unprecedented levels of security while enabling the ultra-low latency and high bandwidth requirements of next-generation applications.
Market Demand for Advanced Optical Network Security Solutions
The global network security market is experiencing unprecedented growth driven by escalating cyber threats and the increasing digitization of enterprise operations. Organizations across industries are recognizing that traditional electronic switching infrastructure presents inherent vulnerabilities that sophisticated attackers can exploit. This recognition has created substantial demand for next-generation security solutions that can operate at the physical layer of network communications.
Financial services institutions represent one of the most significant demand drivers for advanced optical network security solutions. Banks, investment firms, and insurance companies require ultra-secure communication channels for high-frequency trading, customer data protection, and regulatory compliance. The immutable nature of optical switching provides these organizations with security guarantees that software-based solutions cannot match.
Government and defense sectors constitute another major market segment actively seeking optical switching security technologies. National security agencies and military organizations require communication systems that are inherently resistant to electronic surveillance and cyber espionage. The physical properties of optical switching make it extremely difficult for adversaries to intercept or manipulate data transmissions without detection.
Healthcare organizations are increasingly demanding robust network security solutions as they digitize patient records and implement telemedicine platforms. The sensitive nature of medical data and strict regulatory requirements under frameworks like HIPAA create strong market pull for technologies that can provide verifiable security at the hardware level.
Critical infrastructure operators, including power grid managers, water treatment facilities, and transportation systems, represent an emerging high-growth segment. These organizations face sophisticated nation-state attacks targeting industrial control systems, driving demand for security solutions that can isolate and protect operational technology networks through optical switching mechanisms.
The telecommunications industry itself presents substantial market opportunities as service providers seek to offer differentiated security services to enterprise customers. Carriers are exploring optical switching technologies to create premium network tiers with enhanced security guarantees, particularly for customers in regulated industries or those handling sensitive intellectual property.
Market research indicates that enterprise willingness to invest in advanced optical security solutions correlates strongly with recent breach experiences and regulatory pressure. Organizations that have suffered significant security incidents demonstrate accelerated adoption timelines and higher budget allocations for innovative protection technologies.
Financial services institutions represent one of the most significant demand drivers for advanced optical network security solutions. Banks, investment firms, and insurance companies require ultra-secure communication channels for high-frequency trading, customer data protection, and regulatory compliance. The immutable nature of optical switching provides these organizations with security guarantees that software-based solutions cannot match.
Government and defense sectors constitute another major market segment actively seeking optical switching security technologies. National security agencies and military organizations require communication systems that are inherently resistant to electronic surveillance and cyber espionage. The physical properties of optical switching make it extremely difficult for adversaries to intercept or manipulate data transmissions without detection.
Healthcare organizations are increasingly demanding robust network security solutions as they digitize patient records and implement telemedicine platforms. The sensitive nature of medical data and strict regulatory requirements under frameworks like HIPAA create strong market pull for technologies that can provide verifiable security at the hardware level.
Critical infrastructure operators, including power grid managers, water treatment facilities, and transportation systems, represent an emerging high-growth segment. These organizations face sophisticated nation-state attacks targeting industrial control systems, driving demand for security solutions that can isolate and protect operational technology networks through optical switching mechanisms.
The telecommunications industry itself presents substantial market opportunities as service providers seek to offer differentiated security services to enterprise customers. Carriers are exploring optical switching technologies to create premium network tiers with enhanced security guarantees, particularly for customers in regulated industries or those handling sensitive intellectual property.
Market research indicates that enterprise willingness to invest in advanced optical security solutions correlates strongly with recent breach experiences and regulatory pressure. Organizations that have suffered significant security incidents demonstrate accelerated adoption timelines and higher budget allocations for innovative protection technologies.
Current State and Challenges of Optical Switching Security
The current landscape of optical switching security presents a complex array of technological achievements alongside significant vulnerabilities that demand immediate attention. Traditional optical networks have primarily focused on performance optimization, with security considerations often treated as secondary concerns. This approach has resulted in sophisticated switching capabilities that can handle massive data throughput but lack comprehensive protection mechanisms against emerging cyber threats.
Contemporary optical switching systems face unprecedented security challenges stemming from their inherent physical properties and operational characteristics. The transparency of optical signals, while beneficial for network efficiency, creates vulnerabilities where malicious actors can intercept, manipulate, or inject unauthorized data without detection. Current optical switches operate with limited built-in security features, relying heavily on higher-layer protocols for protection, which creates gaps in the security architecture.
The geographical distribution of optical switching security expertise reveals significant disparities across global markets. North American and European research institutions lead in developing advanced security frameworks, while Asia-Pacific regions demonstrate strong manufacturing capabilities but face challenges in implementing comprehensive security standards. This uneven distribution creates vulnerabilities in global optical networks where security implementations vary dramatically across different regions and vendors.
Existing optical switching infrastructure confronts multiple technical constraints that impede security enhancement efforts. The high-speed nature of optical switching leaves minimal processing time for real-time security analysis, creating trade-offs between performance and protection. Additionally, the analog nature of optical signals complicates the implementation of digital security measures, requiring innovative approaches that can operate effectively in the optical domain without compromising signal integrity.
Current security implementations in optical switching systems primarily rely on perimeter defense strategies and encryption at network edges. However, these approaches fail to address internal threats and sophisticated attacks that exploit the optical layer directly. The lack of standardized security protocols specifically designed for optical switching environments further exacerbates these vulnerabilities, creating inconsistent protection levels across different network segments and vendor implementations.
The integration challenges between optical switching hardware and security software represent another critical obstacle. Legacy optical switching equipment often lacks the computational resources necessary for advanced security processing, while newer systems struggle with compatibility issues when implementing security enhancements. These technical limitations necessitate innovative solutions that can provide robust security without requiring complete infrastructure overhauls.
Contemporary optical switching systems face unprecedented security challenges stemming from their inherent physical properties and operational characteristics. The transparency of optical signals, while beneficial for network efficiency, creates vulnerabilities where malicious actors can intercept, manipulate, or inject unauthorized data without detection. Current optical switches operate with limited built-in security features, relying heavily on higher-layer protocols for protection, which creates gaps in the security architecture.
The geographical distribution of optical switching security expertise reveals significant disparities across global markets. North American and European research institutions lead in developing advanced security frameworks, while Asia-Pacific regions demonstrate strong manufacturing capabilities but face challenges in implementing comprehensive security standards. This uneven distribution creates vulnerabilities in global optical networks where security implementations vary dramatically across different regions and vendors.
Existing optical switching infrastructure confronts multiple technical constraints that impede security enhancement efforts. The high-speed nature of optical switching leaves minimal processing time for real-time security analysis, creating trade-offs between performance and protection. Additionally, the analog nature of optical signals complicates the implementation of digital security measures, requiring innovative approaches that can operate effectively in the optical domain without compromising signal integrity.
Current security implementations in optical switching systems primarily rely on perimeter defense strategies and encryption at network edges. However, these approaches fail to address internal threats and sophisticated attacks that exploit the optical layer directly. The lack of standardized security protocols specifically designed for optical switching environments further exacerbates these vulnerabilities, creating inconsistent protection levels across different network segments and vendor implementations.
The integration challenges between optical switching hardware and security software represent another critical obstacle. Legacy optical switching equipment often lacks the computational resources necessary for advanced security processing, while newer systems struggle with compatibility issues when implementing security enhancements. These technical limitations necessitate innovative solutions that can provide robust security without requiring complete infrastructure overhauls.
Existing Advanced Optical Switching Security Solutions
01 Optical network authentication and access control mechanisms
Security mechanisms for optical switching networks that implement authentication protocols and access control systems to verify and authorize network users and devices. These systems ensure that only legitimate entities can access the optical network infrastructure, preventing unauthorized access and potential security breaches. The mechanisms include multi-level authentication, credential verification, and dynamic access permission management tailored for high-speed optical switching environments.- Optical network encryption and authentication mechanisms: Advanced optical switching networks implement encryption protocols and authentication mechanisms to secure data transmission across optical channels. These security measures include cryptographic techniques specifically designed for high-speed optical communications, ensuring data integrity and preventing unauthorized access. Authentication protocols verify the identity of network nodes and users before granting access to network resources.
- Intrusion detection and prevention systems for optical networks: Security systems are deployed to monitor optical switching networks for suspicious activities and potential threats. These systems analyze traffic patterns, detect anomalies, and implement preventive measures against network attacks. Real-time monitoring capabilities enable rapid response to security breaches and unauthorized access attempts in optical network infrastructure.
- Secure optical switching fabric architecture: The design of optical switching fabrics incorporates security features at the hardware level to protect against physical and logical attacks. These architectures include secure routing mechanisms, isolated switching domains, and protected control planes. The implementation ensures that optical signals are switched securely without compromising network integrity or exposing sensitive data.
- Access control and privilege management in optical networks: Comprehensive access control frameworks manage user permissions and network resource allocation in optical switching environments. These systems implement role-based access controls, dynamic privilege assignment, and secure credential management. The frameworks ensure that only authorized entities can configure, monitor, or utilize optical network resources.
- Optical network security monitoring and threat intelligence: Advanced monitoring systems collect and analyze security-related data from optical switching networks to identify emerging threats and vulnerabilities. These systems integrate threat intelligence feeds, perform behavioral analysis, and generate security alerts. The monitoring infrastructure provides visibility into network operations and enables proactive security management.
02 Encryption and secure data transmission in optical networks
Technologies for implementing encryption protocols and secure data transmission methods specifically designed for optical switching networks. These solutions protect data integrity and confidentiality during transmission through optical channels by employing advanced cryptographic techniques. The systems address the unique challenges of securing high-bandwidth optical communications while maintaining network performance and minimizing latency impacts.Expand Specific Solutions03 Intrusion detection and threat monitoring systems
Advanced monitoring and detection systems designed to identify and respond to security threats in optical switching networks. These systems continuously analyze network traffic patterns, detect anomalies, and identify potential intrusions or malicious activities. The solutions incorporate real-time threat assessment capabilities and automated response mechanisms to protect the optical network infrastructure from various security attacks.Expand Specific Solutions04 Secure optical switching fabric architecture
Architectural designs for optical switching fabrics that incorporate built-in security features at the hardware and protocol levels. These architectures implement secure routing mechanisms, isolated switching domains, and protected control planes to prevent unauthorized manipulation of optical paths. The designs ensure that the fundamental switching infrastructure maintains security integrity while supporting high-performance optical data transmission.Expand Specific Solutions05 Network management and security policy enforcement
Comprehensive network management systems that enforce security policies across optical switching networks. These solutions provide centralized control for implementing and maintaining security configurations, managing security credentials, and ensuring compliance with security standards. The systems enable administrators to define, deploy, and monitor security policies throughout the optical network infrastructure while providing audit capabilities and security event logging.Expand Specific Solutions
Key Players in Optical Switching and Network Security Industry
The advanced optical switching for network security sector represents a rapidly evolving market in the growth phase, driven by increasing cybersecurity threats and demand for high-speed, secure data transmission. The market demonstrates substantial expansion potential as enterprises and telecommunications providers seek enhanced protection mechanisms. Technology maturity varies significantly across key players, with established telecommunications giants like Huawei Technologies, ZTE Corp., Ericsson, and Samsung Electronics leading in comprehensive optical networking solutions. Infrastructure specialists including Cisco Technology, Fujitsu, and Hitachi offer mature switching platforms, while semiconductor leaders Intel and Toshiba provide underlying component technologies. Research institutions such as Beijing University of Posts & Telecommunications and University of Electronic Science & Technology of China contribute foundational innovations. Emerging players like NeoPhotonics focus on specialized optical components, indicating a competitive landscape where established network equipment manufacturers dominate deployment-ready solutions while specialized firms drive component-level innovations.
Huawei Technologies Co., Ltd.
Technical Solution: Huawei has developed comprehensive optical switching solutions that integrate advanced security features through their OptiX series optical transport platforms. Their approach combines wavelength division multiplexing (WDM) technology with intelligent optical cross-connect (OXC) capabilities to create secure, high-capacity network infrastructures. The company implements optical layer encryption and dynamic wavelength allocation to enhance network security while maintaining ultra-low latency switching performance. Their solutions feature automated threat detection algorithms that monitor optical signal integrity and can rapidly reconfigure optical paths to isolate potential security breaches, providing both physical layer security and logical network protection.
Strengths: Market-leading optical networking expertise, comprehensive end-to-end solutions, strong R&D capabilities in optical security. Weaknesses: Geopolitical restrictions in some markets, potential supply chain vulnerabilities.
Telefonaktiebolaget LM Ericsson
Technical Solution: Ericsson's optical switching security solution is built around their Router 6000 series and optical transport platforms that integrate advanced security features with high-performance optical switching capabilities. Their approach implements secure optical wavelength services with integrated DDoS protection and encrypted optical channels that provide both confidentiality and integrity protection. The system features intelligent optical cross-connects with built-in security policy enforcement engines that can automatically detect and mitigate optical layer attacks while maintaining network performance. Ericsson's solution also includes cloud-native security orchestration that enables centralized management of distributed optical switching nodes and provides real-time visibility into network security posture across the entire optical infrastructure.
Strengths: Strong 5G and telecommunications expertise, proven carrier-grade reliability, comprehensive network management capabilities. Weaknesses: Higher focus on mobile networks may limit pure optical innovation, competitive pressure in traditional optical markets.
Core Innovations in Optical Switching Security Patents
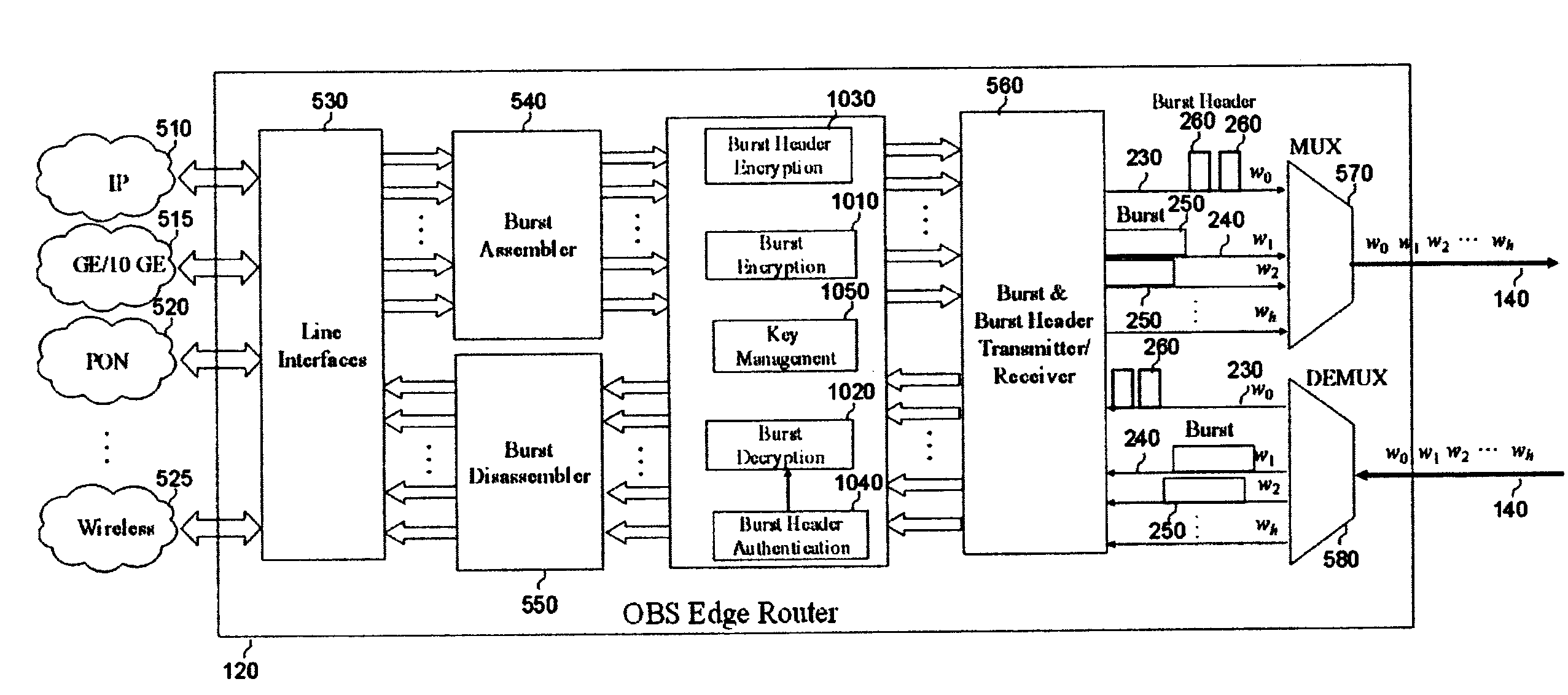
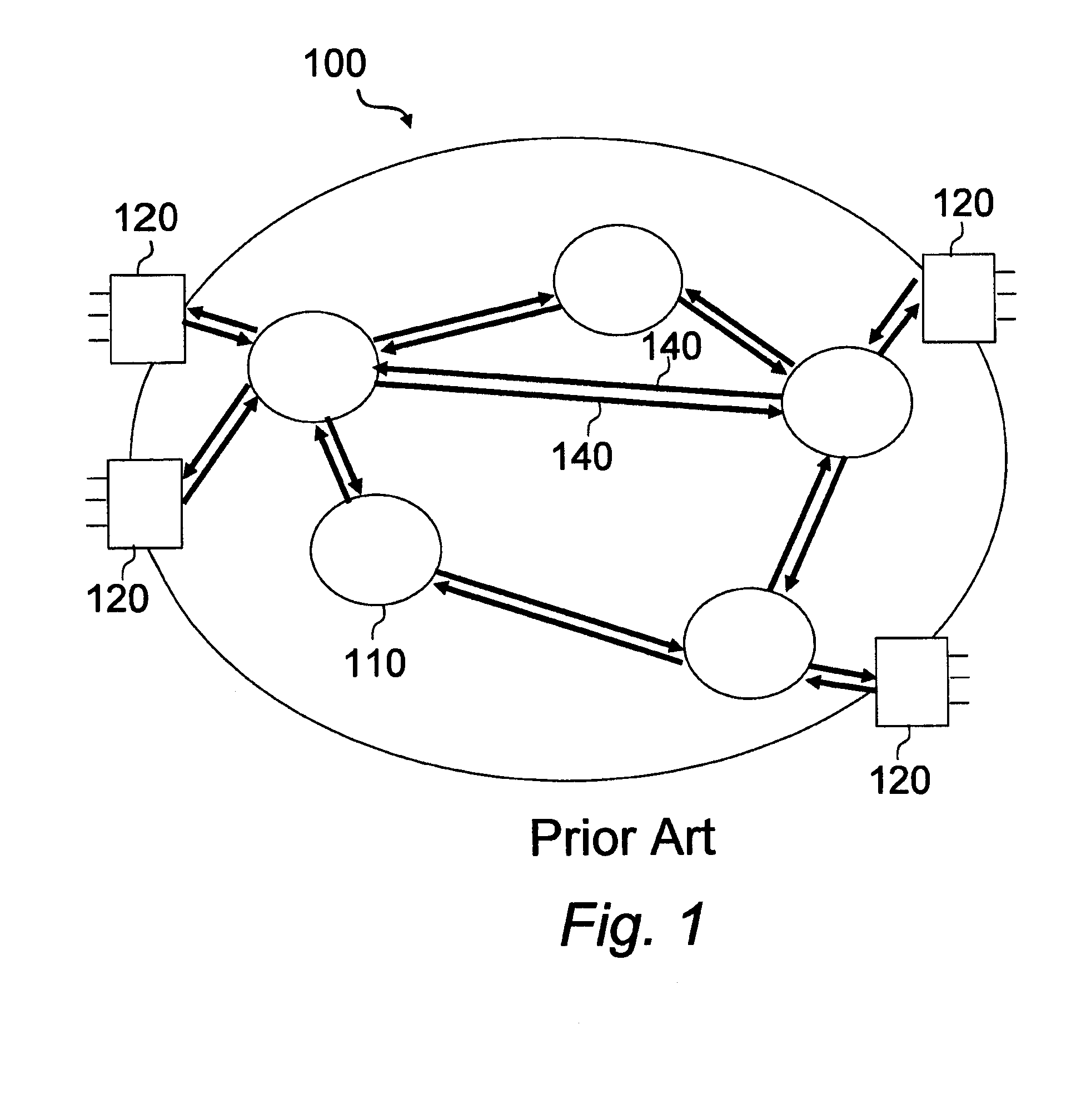
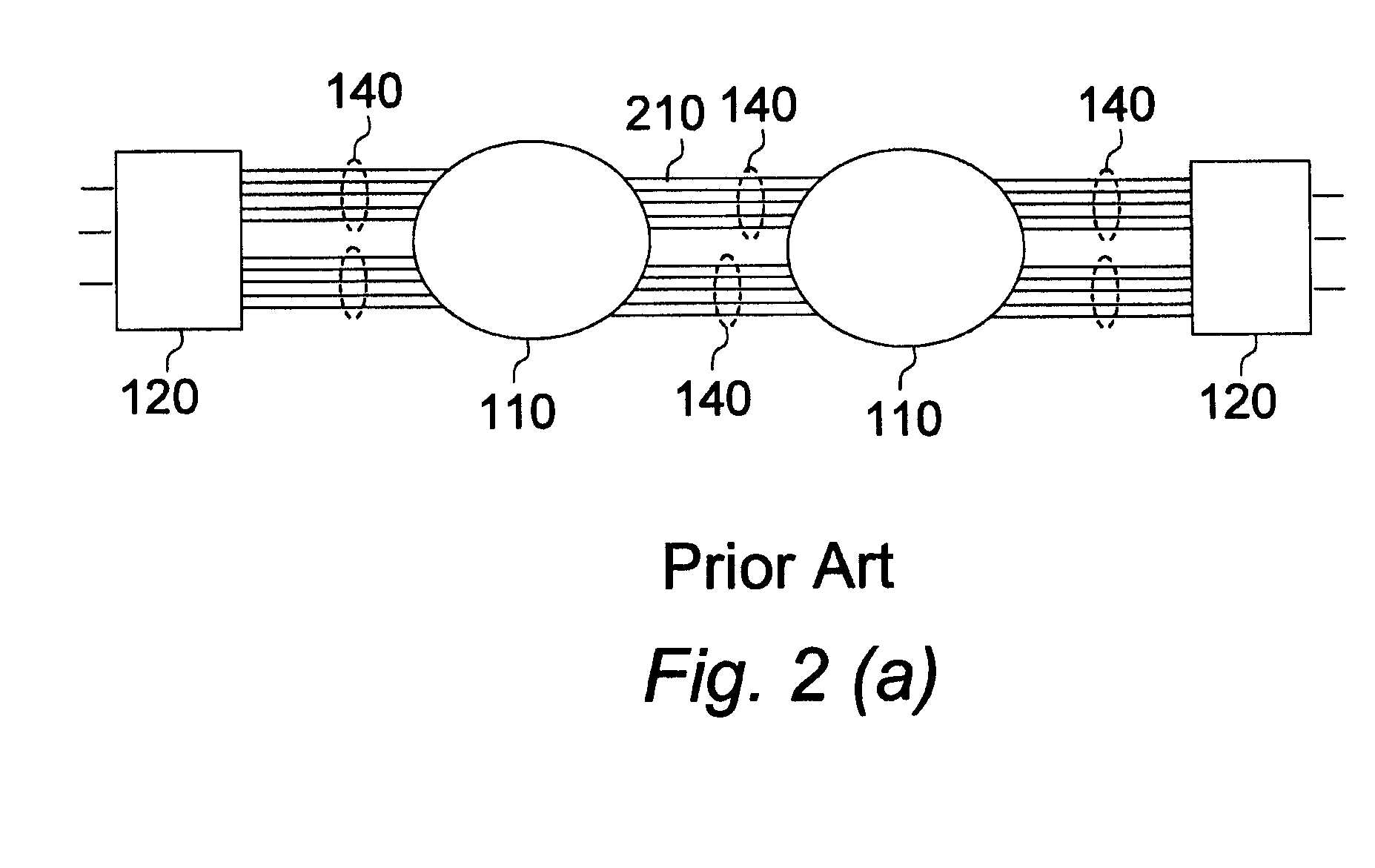
Methods and apparatus for securing optical burst switching (OBS) networks
PatentInactiveUS20090313465A1
Innovation
- Implementing key distribution, authentication of burst headers, and encryption of data bursts within the optical burst switching network to secure the transmission process, specifically by encrypting data bursts at ingress edge routers and decrypting them at egress edge routers, and authenticating burst headers at each core router to ensure only valid paths are set up for data transmission.
Optical Switching Apparatus
PatentActiveUS20230097851A1
Innovation
- The development of a high-speed optical switch device with a distribution selective optical switch and MZI-type optical switch configurations, utilizing materials like InP-based waveguides with refractive index changes via the Franz-Keldysh effect, and incorporating circulators to manage optical signals and reduce crosstalk, allowing for efficient switching of both OCS and OPS signals.
Cybersecurity Standards for Optical Network Infrastructure
The cybersecurity landscape for optical network infrastructure has evolved significantly with the emergence of advanced optical switching technologies. Current standards frameworks primarily focus on traditional network security paradigms, creating gaps in addressing the unique vulnerabilities and attack vectors present in optical switching environments. The integration of software-defined optical networks and programmable optical switches introduces new security considerations that existing standards have yet to fully encompass.
International standards organizations including ITU-T, IEEE, and NIST have begun developing specialized guidelines for optical network security. ITU-T Recommendation G.8271 addresses timing and synchronization security in optical transport networks, while IEEE 802.1AE provides media access control security for optical Ethernet implementations. However, these standards primarily address conventional optical transmission rather than advanced switching architectures that incorporate dynamic reconfiguration capabilities and AI-driven optimization algorithms.
The Common Criteria framework has been adapted to evaluate optical switching equipment, establishing evaluation assurance levels specifically for photonic network components. This includes assessment methodologies for optical cross-connects, wavelength selective switches, and reconfigurable optical add-drop multiplexers. The framework emphasizes protection against optical layer attacks such as signal interception, wavelength hijacking, and optical power manipulation that can compromise network integrity without detection by traditional monitoring systems.
Emerging standards focus on quantum-safe cryptography implementation within optical switching infrastructure. The NIST Post-Quantum Cryptography standardization process has identified specific requirements for optical network environments where quantum key distribution and quantum-resistant algorithms must coexist with classical optical switching mechanisms. These standards address key management protocols, authentication mechanisms, and secure channel establishment procedures tailored for high-speed optical switching operations.
Industry consortiums including the Optical Internetworking Forum and OpenROADM have developed security specifications for disaggregated optical networks. These specifications establish security baselines for controller-to-device communications, northbound and southbound API security, and multi-vendor interoperability security protocols. The standards emphasize zero-trust architecture principles adapted for optical domain controllers and distributed optical switching fabrics, ensuring comprehensive security coverage across heterogeneous optical network deployments.
International standards organizations including ITU-T, IEEE, and NIST have begun developing specialized guidelines for optical network security. ITU-T Recommendation G.8271 addresses timing and synchronization security in optical transport networks, while IEEE 802.1AE provides media access control security for optical Ethernet implementations. However, these standards primarily address conventional optical transmission rather than advanced switching architectures that incorporate dynamic reconfiguration capabilities and AI-driven optimization algorithms.
The Common Criteria framework has been adapted to evaluate optical switching equipment, establishing evaluation assurance levels specifically for photonic network components. This includes assessment methodologies for optical cross-connects, wavelength selective switches, and reconfigurable optical add-drop multiplexers. The framework emphasizes protection against optical layer attacks such as signal interception, wavelength hijacking, and optical power manipulation that can compromise network integrity without detection by traditional monitoring systems.
Emerging standards focus on quantum-safe cryptography implementation within optical switching infrastructure. The NIST Post-Quantum Cryptography standardization process has identified specific requirements for optical network environments where quantum key distribution and quantum-resistant algorithms must coexist with classical optical switching mechanisms. These standards address key management protocols, authentication mechanisms, and secure channel establishment procedures tailored for high-speed optical switching operations.
Industry consortiums including the Optical Internetworking Forum and OpenROADM have developed security specifications for disaggregated optical networks. These specifications establish security baselines for controller-to-device communications, northbound and southbound API security, and multi-vendor interoperability security protocols. The standards emphasize zero-trust architecture principles adapted for optical domain controllers and distributed optical switching fabrics, ensuring comprehensive security coverage across heterogeneous optical network deployments.
Risk Assessment Framework for Optical Switching Systems
The establishment of a comprehensive risk assessment framework for optical switching systems represents a critical component in enhancing network security infrastructure. This framework must address the unique vulnerabilities inherent in optical networking technologies while providing systematic methodologies for identifying, evaluating, and mitigating potential security threats.
The foundation of this framework begins with threat modeling specific to optical switching environments. Unlike traditional electronic switching systems, optical networks face distinct security challenges including signal interception through fiber tapping, wavelength hijacking, and optical layer denial-of-service attacks. The assessment framework must categorize these threats based on their probability of occurrence, potential impact on network operations, and the sophistication level required for exploitation.
Vulnerability assessment protocols within the framework should encompass both physical and logical security aspects of optical switching infrastructure. Physical vulnerabilities include unauthorized access to fiber optic cables, switching equipment tampering, and environmental factors that could compromise signal integrity. Logical vulnerabilities involve control plane security weaknesses, management interface exposures, and cross-layer attack vectors that exploit the interaction between optical and electronic network layers.
The framework incorporates quantitative risk scoring methodologies that assign numerical values to identified threats based on multiple criteria including asset criticality, threat likelihood, and vulnerability severity. This scoring system enables network operators to prioritize security investments and implement risk mitigation strategies in order of importance. The assessment process should be iterative, with regular updates reflecting evolving threat landscapes and technological advancements.
Implementation guidelines within the framework specify standardized procedures for conducting security audits, penetration testing adapted for optical networks, and continuous monitoring protocols. These guidelines ensure consistent application across different organizational contexts while maintaining flexibility to accommodate varying network architectures and operational requirements.
The framework also establishes clear escalation procedures and incident response protocols tailored to optical switching security events, ensuring rapid containment and recovery capabilities when security breaches occur.
The foundation of this framework begins with threat modeling specific to optical switching environments. Unlike traditional electronic switching systems, optical networks face distinct security challenges including signal interception through fiber tapping, wavelength hijacking, and optical layer denial-of-service attacks. The assessment framework must categorize these threats based on their probability of occurrence, potential impact on network operations, and the sophistication level required for exploitation.
Vulnerability assessment protocols within the framework should encompass both physical and logical security aspects of optical switching infrastructure. Physical vulnerabilities include unauthorized access to fiber optic cables, switching equipment tampering, and environmental factors that could compromise signal integrity. Logical vulnerabilities involve control plane security weaknesses, management interface exposures, and cross-layer attack vectors that exploit the interaction between optical and electronic network layers.
The framework incorporates quantitative risk scoring methodologies that assign numerical values to identified threats based on multiple criteria including asset criticality, threat likelihood, and vulnerability severity. This scoring system enables network operators to prioritize security investments and implement risk mitigation strategies in order of importance. The assessment process should be iterative, with regular updates reflecting evolving threat landscapes and technological advancements.
Implementation guidelines within the framework specify standardized procedures for conducting security audits, penetration testing adapted for optical networks, and continuous monitoring protocols. These guidelines ensure consistent application across different organizational contexts while maintaining flexibility to accommodate varying network architectures and operational requirements.
The framework also establishes clear escalation procedures and incident response protocols tailored to optical switching security events, ensuring rapid containment and recovery capabilities when security breaches occur.
Unlock deeper insights with Patsnap Eureka Quick Research — get a full tech report to explore trends and direct your research. Try now!
Generate Your Research Report Instantly with AI Agent
Supercharge your innovation with Patsnap Eureka AI Agent Platform!