Access Control System Scalability in Growing Enterprises
FEB 27, 20269 MIN READ
Generate Your Research Report Instantly with AI Agent
PatSnap Eureka helps you evaluate technical feasibility & market potential.
Enterprise Access Control Growth Challenges and Objectives
Access control systems in modern enterprises have evolved from simple perimeter-based security models to complex, multi-layered frameworks that must accommodate diverse user populations, applications, and infrastructure components. The traditional approach of managing user permissions through static role assignments and manual provisioning processes has become increasingly inadequate as organizations expand their digital footprint and workforce. This evolution reflects the fundamental shift from centralized, on-premises computing environments to distributed, cloud-native architectures that span multiple geographic locations and technology platforms.
The historical development of enterprise access control demonstrates a clear progression from basic authentication mechanisms to sophisticated identity and access management (IAM) ecosystems. Early implementations focused primarily on network access control and file system permissions, operating within relatively homogeneous IT environments. However, the proliferation of software-as-a-service applications, mobile devices, remote work arrangements, and third-party integrations has created unprecedented complexity in access management requirements.
Contemporary access control challenges stem from the exponential growth in digital touchpoints that require secure authentication and authorization. Organizations now must manage access across hybrid cloud environments, legacy systems, modern applications, IoT devices, and partner ecosystems simultaneously. This complexity is compounded by the need to maintain security posture while enabling seamless user experiences and supporting business agility requirements.
The primary technical objectives for scalable access control systems center on achieving dynamic, context-aware security decisions that can adapt to changing organizational structures and threat landscapes. These systems must demonstrate the capability to handle massive user populations while maintaining sub-second response times for authentication and authorization requests. Additionally, they must support automated provisioning and deprovisioning workflows that can respond to organizational changes without manual intervention.
Emerging requirements include the integration of artificial intelligence and machine learning capabilities to enable predictive access management and anomaly detection. Organizations seek solutions that can automatically adjust access privileges based on user behavior patterns, risk assessments, and business context. The ultimate goal is to create self-managing access control infrastructures that can scale seamlessly with organizational growth while reducing administrative overhead and security risks.
The historical development of enterprise access control demonstrates a clear progression from basic authentication mechanisms to sophisticated identity and access management (IAM) ecosystems. Early implementations focused primarily on network access control and file system permissions, operating within relatively homogeneous IT environments. However, the proliferation of software-as-a-service applications, mobile devices, remote work arrangements, and third-party integrations has created unprecedented complexity in access management requirements.
Contemporary access control challenges stem from the exponential growth in digital touchpoints that require secure authentication and authorization. Organizations now must manage access across hybrid cloud environments, legacy systems, modern applications, IoT devices, and partner ecosystems simultaneously. This complexity is compounded by the need to maintain security posture while enabling seamless user experiences and supporting business agility requirements.
The primary technical objectives for scalable access control systems center on achieving dynamic, context-aware security decisions that can adapt to changing organizational structures and threat landscapes. These systems must demonstrate the capability to handle massive user populations while maintaining sub-second response times for authentication and authorization requests. Additionally, they must support automated provisioning and deprovisioning workflows that can respond to organizational changes without manual intervention.
Emerging requirements include the integration of artificial intelligence and machine learning capabilities to enable predictive access management and anomaly detection. Organizations seek solutions that can automatically adjust access privileges based on user behavior patterns, risk assessments, and business context. The ultimate goal is to create self-managing access control infrastructures that can scale seamlessly with organizational growth while reducing administrative overhead and security risks.
Market Demand for Scalable Enterprise Access Solutions
The enterprise access control market is experiencing unprecedented growth driven by digital transformation initiatives and the increasing complexity of organizational structures. Organizations worldwide are transitioning from traditional perimeter-based security models to comprehensive identity and access management solutions that can accommodate dynamic business environments. This shift has created substantial demand for scalable access control systems capable of supporting thousands to hundreds of thousands of users across multiple locations and platforms.
Remote work adoption has fundamentally altered enterprise security requirements, with organizations needing solutions that seamlessly manage access for distributed workforces. The hybrid work model has become permanent for many enterprises, necessitating access control systems that can scale dynamically based on user location, device type, and security context. This evolution has expanded the addressable market beyond traditional on-premises solutions to cloud-native and hybrid architectures.
Growing enterprises face unique challenges as they expand their operations, acquire new companies, or enter new markets. These organizations require access control solutions that can rapidly onboard new users, integrate with diverse technology stacks, and maintain consistent security policies across heterogeneous environments. The ability to scale without compromising performance or security has become a critical differentiator in vendor selection processes.
Regulatory compliance requirements continue to drive market demand, particularly in highly regulated industries such as healthcare, financial services, and government sectors. Organizations must implement access control systems that not only scale with business growth but also maintain detailed audit trails and support compliance frameworks like SOX, HIPAA, and GDPR. The complexity of managing compliance across multiple jurisdictions has increased demand for centralized, scalable access management platforms.
The market shows strong preference for solutions offering elastic scalability, where organizations can adjust capacity based on actual usage rather than peak projections. This demand pattern reflects the need for cost-effective scaling that aligns with business growth trajectories. Cloud-based access control solutions have gained significant traction due to their ability to provide instant scalability without substantial infrastructure investments.
Enterprise buyers increasingly prioritize solutions that integrate seamlessly with existing technology ecosystems while providing room for future expansion. The demand extends beyond basic authentication to comprehensive access governance, including automated provisioning, role-based access control, and intelligent access analytics that can scale across enterprise boundaries.
Remote work adoption has fundamentally altered enterprise security requirements, with organizations needing solutions that seamlessly manage access for distributed workforces. The hybrid work model has become permanent for many enterprises, necessitating access control systems that can scale dynamically based on user location, device type, and security context. This evolution has expanded the addressable market beyond traditional on-premises solutions to cloud-native and hybrid architectures.
Growing enterprises face unique challenges as they expand their operations, acquire new companies, or enter new markets. These organizations require access control solutions that can rapidly onboard new users, integrate with diverse technology stacks, and maintain consistent security policies across heterogeneous environments. The ability to scale without compromising performance or security has become a critical differentiator in vendor selection processes.
Regulatory compliance requirements continue to drive market demand, particularly in highly regulated industries such as healthcare, financial services, and government sectors. Organizations must implement access control systems that not only scale with business growth but also maintain detailed audit trails and support compliance frameworks like SOX, HIPAA, and GDPR. The complexity of managing compliance across multiple jurisdictions has increased demand for centralized, scalable access management platforms.
The market shows strong preference for solutions offering elastic scalability, where organizations can adjust capacity based on actual usage rather than peak projections. This demand pattern reflects the need for cost-effective scaling that aligns with business growth trajectories. Cloud-based access control solutions have gained significant traction due to their ability to provide instant scalability without substantial infrastructure investments.
Enterprise buyers increasingly prioritize solutions that integrate seamlessly with existing technology ecosystems while providing room for future expansion. The demand extends beyond basic authentication to comprehensive access governance, including automated provisioning, role-based access control, and intelligent access analytics that can scale across enterprise boundaries.
Current Scalability Limitations in Access Control Systems
Traditional access control systems face significant scalability challenges when enterprises experience rapid growth in user populations, resource volumes, and organizational complexity. Legacy systems typically rely on centralized architectures that create bottlenecks during peak authentication periods, resulting in degraded performance and user experience as concurrent access requests increase exponentially.
Database performance limitations represent a critical constraint in current access control implementations. Most systems utilize relational databases with rigid schemas that struggle to accommodate dynamic permission structures and frequent policy updates. As user bases expand beyond several thousand entities, query response times deteriorate significantly, particularly when complex role hierarchies and attribute-based access control policies are evaluated in real-time.
Network infrastructure constraints further compound scalability issues, especially in geographically distributed enterprises. Current systems often require centralized policy decision points that introduce latency for remote locations. The bandwidth requirements for continuous policy synchronization and audit logging can overwhelm existing network capacity, creating performance degradation across the entire access control infrastructure.
Memory and processing limitations in existing hardware architectures create additional bottlenecks. Traditional access control systems maintain session states and cache policy information in limited server memory, leading to frequent cache misses and increased processing overhead as user populations grow. The computational complexity of evaluating nested group memberships and dynamic attribute conditions scales poorly with organizational size.
Administrative overhead becomes increasingly problematic as enterprises expand their digital footprint. Current role-based access control models require manual configuration of permissions for new applications, departments, and user categories. This administrative burden grows exponentially with organizational complexity, creating delays in provisioning access and increasing the likelihood of configuration errors that compromise security posture.
Integration challenges with heterogeneous enterprise systems create additional scalability constraints. Existing access control solutions often lack standardized APIs and protocols for seamless integration with cloud services, legacy applications, and third-party platforms. This fragmentation requires custom integration efforts that become increasingly complex and resource-intensive as the technology stack expands.
Policy management complexity escalates dramatically in growing enterprises with diverse business units and regulatory requirements. Current systems struggle to maintain consistent policy enforcement across multiple domains while accommodating varying compliance standards and business rules. The lack of automated policy lifecycle management tools results in policy drift and inconsistent access controls across the enterprise ecosystem.
Database performance limitations represent a critical constraint in current access control implementations. Most systems utilize relational databases with rigid schemas that struggle to accommodate dynamic permission structures and frequent policy updates. As user bases expand beyond several thousand entities, query response times deteriorate significantly, particularly when complex role hierarchies and attribute-based access control policies are evaluated in real-time.
Network infrastructure constraints further compound scalability issues, especially in geographically distributed enterprises. Current systems often require centralized policy decision points that introduce latency for remote locations. The bandwidth requirements for continuous policy synchronization and audit logging can overwhelm existing network capacity, creating performance degradation across the entire access control infrastructure.
Memory and processing limitations in existing hardware architectures create additional bottlenecks. Traditional access control systems maintain session states and cache policy information in limited server memory, leading to frequent cache misses and increased processing overhead as user populations grow. The computational complexity of evaluating nested group memberships and dynamic attribute conditions scales poorly with organizational size.
Administrative overhead becomes increasingly problematic as enterprises expand their digital footprint. Current role-based access control models require manual configuration of permissions for new applications, departments, and user categories. This administrative burden grows exponentially with organizational complexity, creating delays in provisioning access and increasing the likelihood of configuration errors that compromise security posture.
Integration challenges with heterogeneous enterprise systems create additional scalability constraints. Existing access control solutions often lack standardized APIs and protocols for seamless integration with cloud services, legacy applications, and third-party platforms. This fragmentation requires custom integration efforts that become increasingly complex and resource-intensive as the technology stack expands.
Policy management complexity escalates dramatically in growing enterprises with diverse business units and regulatory requirements. Current systems struggle to maintain consistent policy enforcement across multiple domains while accommodating varying compliance standards and business rules. The lack of automated policy lifecycle management tools results in policy drift and inconsistent access controls across the enterprise ecosystem.
Existing Scalable Access Control Architectures
01 Distributed access control architecture
Implementing distributed access control systems that utilize multiple control nodes or servers to handle authentication and authorization requests. This architecture allows the system to scale horizontally by adding more nodes as the number of users or access points increases. The distributed approach reduces bottlenecks and single points of failure, enabling the system to handle larger volumes of access requests efficiently across multiple locations or facilities.- Distributed access control architecture: Implementing distributed access control systems that utilize multiple control nodes or servers to handle authentication and authorization requests. This architecture allows the system to scale horizontally by adding more nodes as the number of users or access points increases. The distributed approach reduces bottlenecks and single points of failure, enabling the system to handle larger volumes of access requests efficiently across multiple locations or facilities.
- Hierarchical access control management: Utilizing hierarchical structures for managing access control policies and permissions across large-scale systems. This approach organizes access control into multiple levels or tiers, allowing for efficient delegation of authority and simplified management of permissions across different organizational units or geographical locations. The hierarchical model enables scalability by distributing administrative responsibilities and reducing the complexity of managing large numbers of users and resources.
- Cloud-based access control systems: Leveraging cloud computing infrastructure to provide scalable access control solutions that can dynamically adjust resources based on demand. Cloud-based systems offer virtually unlimited scalability by utilizing elastic computing resources, allowing organizations to expand their access control capabilities without significant hardware investments. These systems support remote management and can easily accommodate growing numbers of users, devices, and access points across multiple sites.
- Database optimization and caching mechanisms: Implementing advanced database architectures and caching strategies to improve the performance and scalability of access control systems. These techniques include using distributed databases, implementing efficient indexing methods, and employing caching layers to reduce database query loads. By optimizing data storage and retrieval processes, the system can handle increased numbers of access control transactions while maintaining fast response times and supporting larger user populations.
- Modular and extensible system design: Designing access control systems with modular components and standardized interfaces that allow for easy expansion and integration of additional functionality. This approach enables organizations to scale their systems incrementally by adding new modules, such as additional readers, controllers, or authentication methods, without requiring complete system overhauls. The modular design supports various communication protocols and integration standards, facilitating seamless expansion as organizational needs grow.
02 Hierarchical access control management
Utilizing hierarchical structures for managing access control systems where access rights and permissions are organized in multiple levels. This approach enables efficient scaling by delegating control to different organizational levels while maintaining centralized oversight. The hierarchical model allows for easier management of large numbers of users and access points by grouping them into logical units that can be administered independently.Expand Specific Solutions03 Cloud-based access control platforms
Leveraging cloud computing infrastructure to provide scalable access control solutions that can dynamically adjust resources based on demand. Cloud-based systems eliminate the need for on-premises hardware expansion and allow for virtually unlimited scaling capabilities. These platforms can handle growing numbers of users, devices, and access points while providing centralized management and real-time updates across distributed locations.Expand Specific Solutions04 Modular access control system design
Designing access control systems with modular components that can be easily added or removed to accommodate changing requirements. This modular approach allows organizations to start with a basic system and expand incrementally by adding modules for additional doors, readers, or functionality. The modular design supports scalability by enabling flexible configuration and reducing the complexity of system expansion.Expand Specific Solutions05 Database optimization and caching mechanisms
Implementing advanced database management techniques and caching strategies to improve the performance of access control systems as they scale. These optimizations include indexing, query optimization, and distributed caching to reduce database load and response times. Efficient data management ensures that the system can handle increasing numbers of access events, user records, and audit logs without degradation in performance.Expand Specific Solutions
Key Players in Enterprise Access Control Market
The access control system scalability market for growing enterprises is experiencing rapid expansion, driven by increasing security demands and digital transformation initiatives. The industry is in a mature growth phase, with established technology giants like Oracle, IBM, Microsoft, and Amazon Technologies leading through comprehensive cloud-based solutions and enterprise platforms. Specialized security providers such as Forescout Technologies and SailPoint Technologies offer targeted access management solutions, while telecommunications leaders including Huawei Cloud, ZTE Corp, and NEC Corp leverage their infrastructure expertise. Chinese companies like Beijing Hardrock Technology and Shenzhen Das Intellitech contribute innovative hardware and intelligent building solutions. The technology demonstrates high maturity levels, with cloud integration, AI-powered analytics, and IoT compatibility becoming standard features, indicating a competitive landscape where scalability, integration capabilities, and enterprise-grade security determine market positioning.
Oracle International Corp.
Technical Solution: Oracle provides comprehensive Identity and Access Management (IAM) solutions designed for enterprise scalability. Their Oracle Identity Cloud Service offers centralized identity governance, single sign-on (SSO), and multi-factor authentication across hybrid and multi-cloud environments. The platform supports automated user provisioning and de-provisioning, role-based access control (RBAC), and privileged access management. Oracle's solution can handle millions of users and thousands of applications simultaneously, with elastic scaling capabilities that automatically adjust resources based on demand. The system includes advanced analytics for access risk assessment and compliance reporting, supporting regulatory requirements like GDPR and SOX.
Strengths: Proven enterprise-grade scalability, comprehensive feature set, strong integration with Oracle ecosystem, robust compliance capabilities. Weaknesses: High implementation complexity, significant licensing costs, potential vendor lock-in concerns.
International Business Machines Corp.
Technical Solution: IBM Security Verify provides a cloud-native identity and access management platform built for enterprise scalability. The solution leverages microservices architecture and containerization to enable horizontal scaling across distributed environments. IBM's approach includes AI-powered risk assessment, adaptive authentication, and zero-trust security models. The platform supports federated identity management across multiple domains and can integrate with existing enterprise directories like Active Directory. IBM's solution offers API-first design enabling seamless integration with third-party applications and supports both on-premises and cloud deployments. The system includes advanced threat detection capabilities and behavioral analytics to identify anomalous access patterns in real-time.
Strengths: AI-driven security features, flexible deployment options, strong enterprise integration capabilities, comprehensive threat detection. Weaknesses: Complex configuration requirements, higher total cost of ownership, steep learning curve for administrators.
Core Innovations in Distributed Access Management
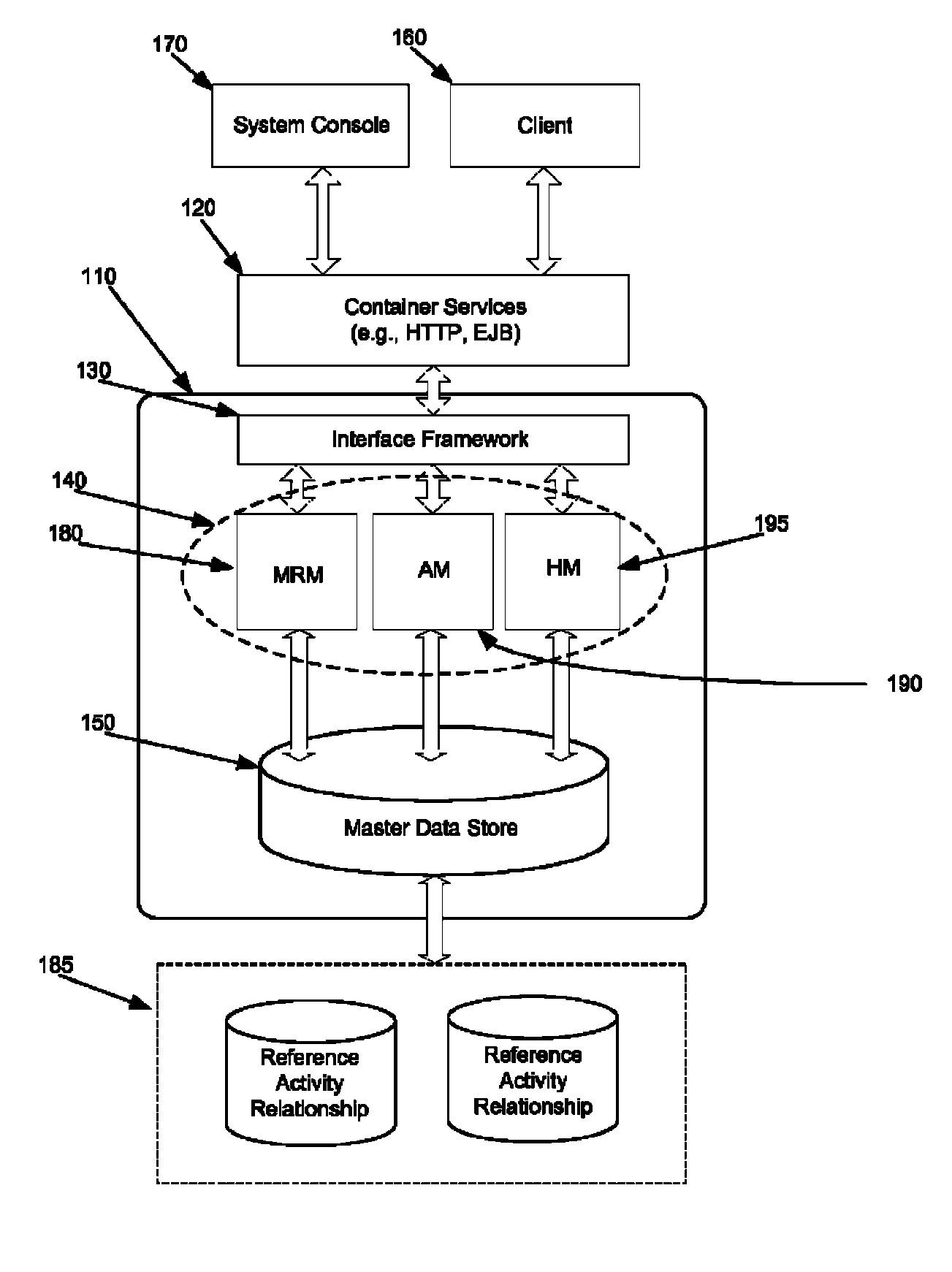
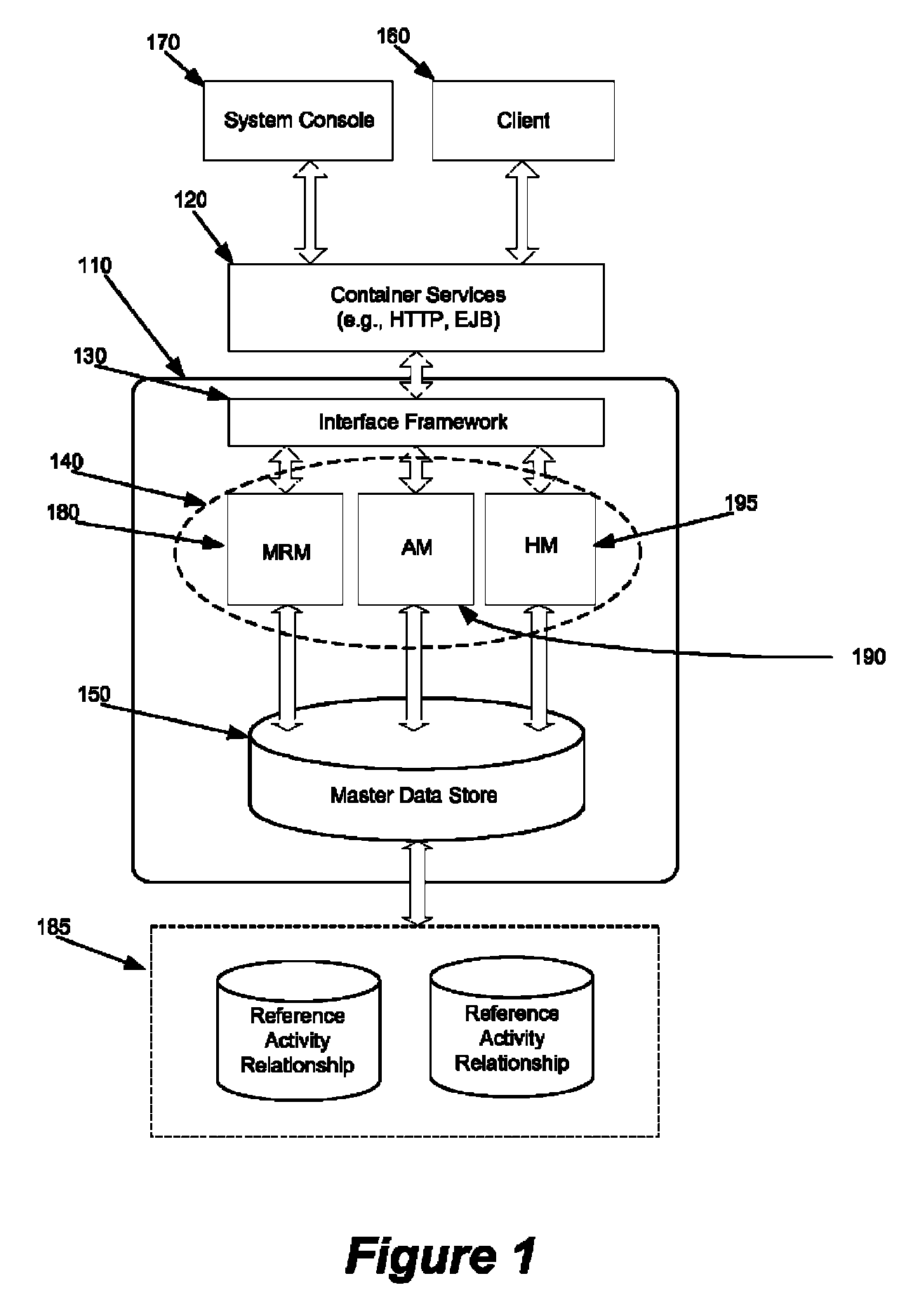
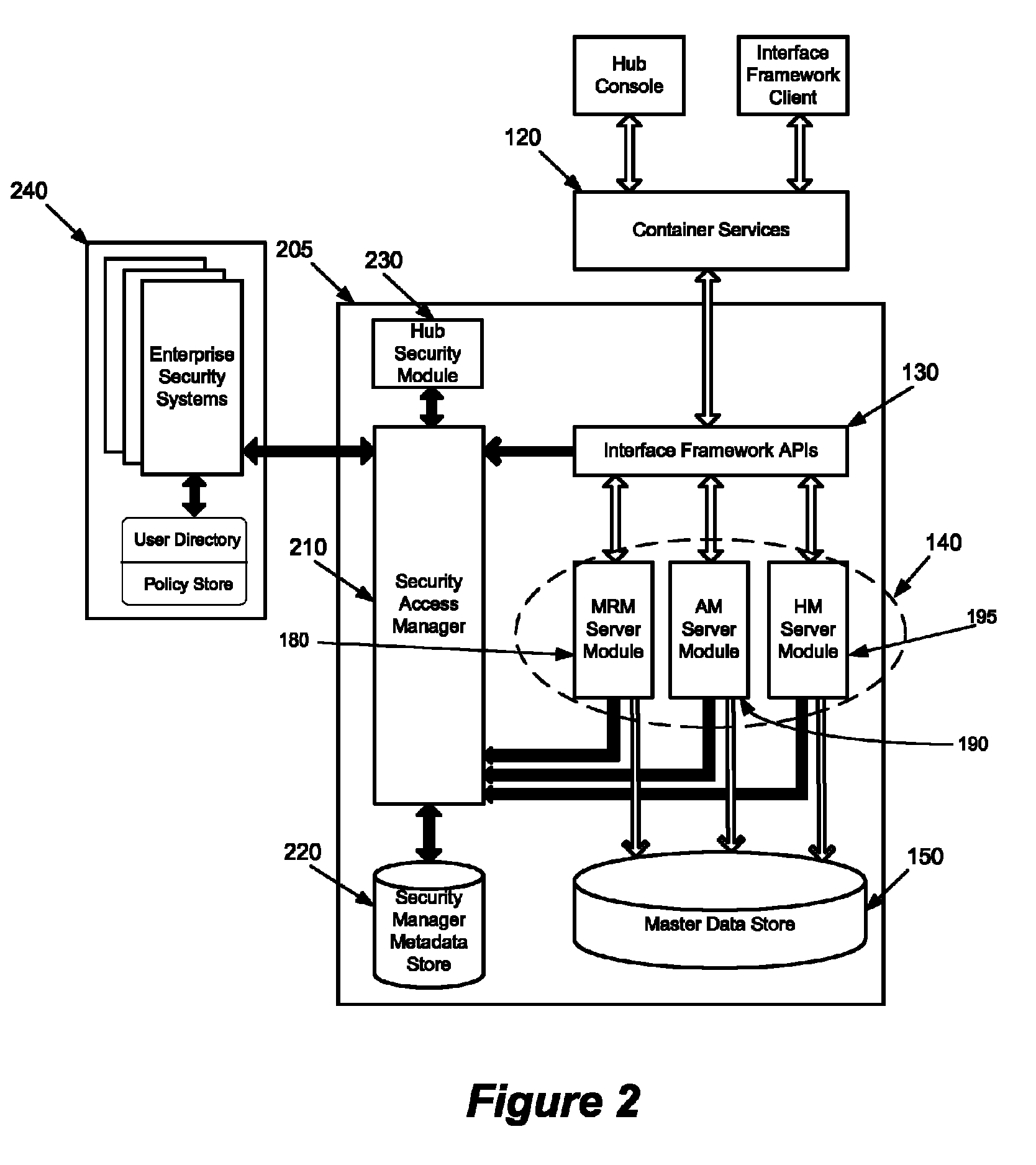
System and method for flexible security access management in an enterprise
PatentActiveUS8224873B1
Innovation
- A security access manager (SAM) that integrates with multiple security systems, providing configurable management modules for authentication, authorization, and role mapping, allowing for distributed security access control and the ability to scale by adding or removing security systems, while leveraging different security models such as role-based and policy-based access.
Secure authorization provisioning using variant profiles
PatentWO2020243231A1
Innovation
- Implementing variant profiles to define and manage user authorizations, reducing the need for multiple roles by creating composite and sub-profiles that dynamically assign access permissions based on user-specific fields and resource authorizations, ensuring fine-grained access control with minimal roles.
Compliance Requirements for Enterprise Access Systems
Enterprise access control systems must navigate an increasingly complex regulatory landscape that varies significantly across industries, geographical regions, and organizational structures. The regulatory framework encompasses multiple layers of compliance requirements, from international standards like ISO 27001 and SOC 2 to industry-specific mandates such as HIPAA for healthcare, PCI DSS for payment processing, and SOX for publicly traded companies. These regulations establish fundamental principles for access governance, including the principle of least privilege, segregation of duties, and comprehensive audit trails.
Data protection regulations represent a critical compliance dimension for scalable access systems. The General Data Protection Regulation (GDPR) in Europe, California Consumer Privacy Act (CCPA), and similar privacy laws worldwide impose strict requirements on how organizations control access to personal data. These regulations mandate explicit consent mechanisms, data subject rights management, and the ability to demonstrate compliance through detailed access logs and control documentation. Scalable systems must incorporate privacy-by-design principles, ensuring that access controls can adapt to varying data sensitivity levels and jurisdictional requirements.
Financial services and healthcare sectors face particularly stringent compliance requirements that directly impact access system architecture. Banking regulations such as Basel III and PSD2 require robust authentication mechanisms, transaction monitoring, and real-time risk assessment capabilities. Healthcare organizations must comply with HIPAA's minimum necessary standard, requiring dynamic access controls that limit data exposure based on job functions and patient relationships. These sector-specific requirements often necessitate specialized access control modules and integration capabilities.
Audit and reporting requirements form the backbone of compliance frameworks, demanding comprehensive logging, monitoring, and reporting capabilities from access control systems. Organizations must maintain detailed records of access requests, approvals, modifications, and usage patterns. The systems must support automated compliance reporting, real-time monitoring of policy violations, and periodic access reviews. Scalable architectures must ensure that audit capabilities grow proportionally with system expansion, maintaining performance while capturing increasingly complex access patterns across distributed environments.
Cross-border operations introduce additional compliance complexity, as organizations must simultaneously satisfy multiple regulatory jurisdictions. This requires access systems to support jurisdiction-specific policies, data residency requirements, and varying authentication standards. The challenge intensifies for growing enterprises expanding into new markets, where access systems must rapidly adapt to local compliance requirements while maintaining global operational consistency and security standards.
Data protection regulations represent a critical compliance dimension for scalable access systems. The General Data Protection Regulation (GDPR) in Europe, California Consumer Privacy Act (CCPA), and similar privacy laws worldwide impose strict requirements on how organizations control access to personal data. These regulations mandate explicit consent mechanisms, data subject rights management, and the ability to demonstrate compliance through detailed access logs and control documentation. Scalable systems must incorporate privacy-by-design principles, ensuring that access controls can adapt to varying data sensitivity levels and jurisdictional requirements.
Financial services and healthcare sectors face particularly stringent compliance requirements that directly impact access system architecture. Banking regulations such as Basel III and PSD2 require robust authentication mechanisms, transaction monitoring, and real-time risk assessment capabilities. Healthcare organizations must comply with HIPAA's minimum necessary standard, requiring dynamic access controls that limit data exposure based on job functions and patient relationships. These sector-specific requirements often necessitate specialized access control modules and integration capabilities.
Audit and reporting requirements form the backbone of compliance frameworks, demanding comprehensive logging, monitoring, and reporting capabilities from access control systems. Organizations must maintain detailed records of access requests, approvals, modifications, and usage patterns. The systems must support automated compliance reporting, real-time monitoring of policy violations, and periodic access reviews. Scalable architectures must ensure that audit capabilities grow proportionally with system expansion, maintaining performance while capturing increasingly complex access patterns across distributed environments.
Cross-border operations introduce additional compliance complexity, as organizations must simultaneously satisfy multiple regulatory jurisdictions. This requires access systems to support jurisdiction-specific policies, data residency requirements, and varying authentication standards. The challenge intensifies for growing enterprises expanding into new markets, where access systems must rapidly adapt to local compliance requirements while maintaining global operational consistency and security standards.
Security Risk Assessment in Scalable Access Frameworks
Security risk assessment in scalable access frameworks represents a critical evaluation process that identifies, analyzes, and mitigates potential vulnerabilities inherent in expanding access control infrastructures. As enterprises grow and their access control systems scale to accommodate increasing users, resources, and complexity, new attack vectors and security weaknesses emerge that require systematic assessment methodologies.
The primary security risks in scalable access frameworks stem from architectural complexity and distributed system vulnerabilities. Traditional centralized access control models face significant challenges when scaled horizontally, creating single points of failure and performance bottlenecks. Distributed architectures, while addressing scalability concerns, introduce new risks including inconsistent policy enforcement, synchronization delays, and increased attack surface areas across multiple nodes.
Authentication and authorization mechanisms present substantial risk factors during scaling operations. Token-based systems may experience security degradation through token proliferation, inadequate rotation policies, and compromised secret management. Multi-factor authentication systems face challenges in maintaining security standards while accommodating rapid user onboarding processes, potentially leading to weakened verification protocols or administrative shortcuts that compromise overall system integrity.
Data consistency and policy synchronization risks become pronounced in distributed access control environments. Eventual consistency models may create temporal security gaps where outdated permissions remain active, allowing unauthorized access during synchronization windows. Network partitions and communication failures can result in split-brain scenarios where different system components operate with conflicting access policies, creating exploitable inconsistencies.
Privilege escalation vulnerabilities increase exponentially with system complexity and user base expansion. Role-based access control systems may develop role explosion problems, where excessive granular permissions create management overhead and increase the likelihood of misconfiguration. Administrative burden growth often leads to over-privileged accounts and inadequate access reviews, creating persistent security risks.
Performance-driven security trade-offs represent another significant risk category in scalable frameworks. Caching mechanisms implemented to improve system responsiveness may retain stale authorization data, while load balancing strategies might bypass certain security checks. Session management across distributed systems introduces risks related to session hijacking, inadequate timeout policies, and cross-node session validation failures that attackers can exploit to maintain persistent unauthorized access.
The primary security risks in scalable access frameworks stem from architectural complexity and distributed system vulnerabilities. Traditional centralized access control models face significant challenges when scaled horizontally, creating single points of failure and performance bottlenecks. Distributed architectures, while addressing scalability concerns, introduce new risks including inconsistent policy enforcement, synchronization delays, and increased attack surface areas across multiple nodes.
Authentication and authorization mechanisms present substantial risk factors during scaling operations. Token-based systems may experience security degradation through token proliferation, inadequate rotation policies, and compromised secret management. Multi-factor authentication systems face challenges in maintaining security standards while accommodating rapid user onboarding processes, potentially leading to weakened verification protocols or administrative shortcuts that compromise overall system integrity.
Data consistency and policy synchronization risks become pronounced in distributed access control environments. Eventual consistency models may create temporal security gaps where outdated permissions remain active, allowing unauthorized access during synchronization windows. Network partitions and communication failures can result in split-brain scenarios where different system components operate with conflicting access policies, creating exploitable inconsistencies.
Privilege escalation vulnerabilities increase exponentially with system complexity and user base expansion. Role-based access control systems may develop role explosion problems, where excessive granular permissions create management overhead and increase the likelihood of misconfiguration. Administrative burden growth often leads to over-privileged accounts and inadequate access reviews, creating persistent security risks.
Performance-driven security trade-offs represent another significant risk category in scalable frameworks. Caching mechanisms implemented to improve system responsiveness may retain stale authorization data, while load balancing strategies might bypass certain security checks. Session management across distributed systems introduces risks related to session hijacking, inadequate timeout policies, and cross-node session validation failures that attackers can exploit to maintain persistent unauthorized access.
Unlock deeper insights with PatSnap Eureka Quick Research — get a full tech report to explore trends and direct your research. Try now!
Generate Your Research Report Instantly with AI Agent
Supercharge your innovation with PatSnap Eureka AI Agent Platform!