Access Control Systems vs Biometric Entry: Security Efficacy
FEB 27, 20269 MIN READ
Generate Your Research Report Instantly with AI Agent
PatSnap Eureka helps you evaluate technical feasibility & market potential.
Access Control and Biometric Security Evolution Goals
The evolution of access control systems has undergone a remarkable transformation from mechanical locks to sophisticated biometric authentication technologies. Traditional access control methods, including key-based systems, magnetic stripe cards, and proximity cards, have served as foundational security measures for decades. However, the increasing demand for enhanced security, reduced administrative overhead, and improved user experience has driven the industry toward biometric solutions that leverage unique physiological and behavioral characteristics for identity verification.
The primary technological goal in this evolution centers on achieving higher security efficacy while maintaining operational efficiency. Traditional access control systems face inherent vulnerabilities such as credential sharing, theft, and unauthorized duplication. The transition to biometric entry systems aims to eliminate these weaknesses by implementing authentication methods based on immutable human characteristics including fingerprints, iris patterns, facial geometry, and voice recognition.
Current development objectives focus on creating hybrid systems that combine the reliability of traditional access control with the advanced security features of biometric technology. These integrated approaches seek to establish multi-factor authentication protocols that significantly reduce false acceptance rates while maintaining acceptable false rejection rates. The goal is to achieve security levels that exceed 99.9% accuracy in legitimate user identification while preventing unauthorized access attempts.
The technological roadmap emphasizes the development of contactless biometric solutions, particularly in response to hygiene concerns and operational efficiency requirements. Advanced facial recognition systems, iris scanning technologies, and palm vein authentication represent the cutting edge of this evolution, offering both enhanced security and improved user convenience.
Future evolution goals include the implementation of artificial intelligence and machine learning algorithms to continuously improve recognition accuracy and adapt to changing user characteristics over time. The integration of blockchain technology for secure credential management and the development of quantum-resistant encryption methods represent additional strategic objectives in the ongoing advancement of access control and biometric security systems.
The primary technological goal in this evolution centers on achieving higher security efficacy while maintaining operational efficiency. Traditional access control systems face inherent vulnerabilities such as credential sharing, theft, and unauthorized duplication. The transition to biometric entry systems aims to eliminate these weaknesses by implementing authentication methods based on immutable human characteristics including fingerprints, iris patterns, facial geometry, and voice recognition.
Current development objectives focus on creating hybrid systems that combine the reliability of traditional access control with the advanced security features of biometric technology. These integrated approaches seek to establish multi-factor authentication protocols that significantly reduce false acceptance rates while maintaining acceptable false rejection rates. The goal is to achieve security levels that exceed 99.9% accuracy in legitimate user identification while preventing unauthorized access attempts.
The technological roadmap emphasizes the development of contactless biometric solutions, particularly in response to hygiene concerns and operational efficiency requirements. Advanced facial recognition systems, iris scanning technologies, and palm vein authentication represent the cutting edge of this evolution, offering both enhanced security and improved user convenience.
Future evolution goals include the implementation of artificial intelligence and machine learning algorithms to continuously improve recognition accuracy and adapt to changing user characteristics over time. The integration of blockchain technology for secure credential management and the development of quantum-resistant encryption methods represent additional strategic objectives in the ongoing advancement of access control and biometric security systems.
Market Demand for Enhanced Entry Security Solutions
The global security landscape has witnessed unprecedented demand for sophisticated entry control solutions, driven by escalating security threats across multiple sectors. Organizations worldwide are increasingly recognizing that traditional lock-and-key mechanisms are insufficient to address modern security challenges, creating substantial market opportunities for advanced access control technologies.
Corporate enterprises represent the largest demand segment, with businesses seeking comprehensive security solutions that can manage multiple access points, track employee movements, and integrate with existing security infrastructure. The rise of hybrid work models has further intensified this need, as organizations require flexible systems capable of managing both permanent staff and temporary visitors while maintaining stringent security protocols.
Government facilities and critical infrastructure sectors demonstrate particularly strong demand for high-security entry solutions. These environments require systems capable of handling multiple authentication factors, maintaining detailed audit trails, and providing rapid response capabilities during security incidents. The increasing frequency of security breaches in sensitive facilities has accelerated adoption timelines and expanded budget allocations for advanced entry systems.
Healthcare institutions have emerged as a rapidly growing market segment, driven by regulatory compliance requirements and the need to protect sensitive patient data and controlled substances. These facilities require solutions that can differentiate between various user categories, from medical staff to visitors, while ensuring seamless access during emergency situations.
Educational institutions, particularly higher education facilities, are experiencing growing demand for scalable entry solutions that can manage large, diverse populations while maintaining campus safety. Recent security incidents have prompted increased investment in comprehensive access control systems that can secure multiple buildings and outdoor areas.
The residential sector shows increasing interest in biometric and smart access solutions, particularly in high-end developments and urban areas with elevated security concerns. Property developers are incorporating advanced entry systems as standard features to meet buyer expectations and differentiate their offerings in competitive markets.
Market drivers include regulatory compliance requirements, insurance considerations, and the growing awareness of security vulnerabilities in traditional systems. Organizations are increasingly viewing advanced entry control as essential infrastructure rather than optional enhancement, fundamentally shifting procurement approaches and budget priorities across industries.
Corporate enterprises represent the largest demand segment, with businesses seeking comprehensive security solutions that can manage multiple access points, track employee movements, and integrate with existing security infrastructure. The rise of hybrid work models has further intensified this need, as organizations require flexible systems capable of managing both permanent staff and temporary visitors while maintaining stringent security protocols.
Government facilities and critical infrastructure sectors demonstrate particularly strong demand for high-security entry solutions. These environments require systems capable of handling multiple authentication factors, maintaining detailed audit trails, and providing rapid response capabilities during security incidents. The increasing frequency of security breaches in sensitive facilities has accelerated adoption timelines and expanded budget allocations for advanced entry systems.
Healthcare institutions have emerged as a rapidly growing market segment, driven by regulatory compliance requirements and the need to protect sensitive patient data and controlled substances. These facilities require solutions that can differentiate between various user categories, from medical staff to visitors, while ensuring seamless access during emergency situations.
Educational institutions, particularly higher education facilities, are experiencing growing demand for scalable entry solutions that can manage large, diverse populations while maintaining campus safety. Recent security incidents have prompted increased investment in comprehensive access control systems that can secure multiple buildings and outdoor areas.
The residential sector shows increasing interest in biometric and smart access solutions, particularly in high-end developments and urban areas with elevated security concerns. Property developers are incorporating advanced entry systems as standard features to meet buyer expectations and differentiate their offerings in competitive markets.
Market drivers include regulatory compliance requirements, insurance considerations, and the growing awareness of security vulnerabilities in traditional systems. Organizations are increasingly viewing advanced entry control as essential infrastructure rather than optional enhancement, fundamentally shifting procurement approaches and budget priorities across industries.
Current Biometric vs Traditional Access Control Limitations
Traditional access control systems face significant limitations in contemporary security environments. Card-based systems remain vulnerable to credential theft, duplication, and unauthorized sharing among users. Physical tokens can be easily lost, stolen, or cloned using readily available technology, creating substantial security gaps. PIN-based systems suffer from predictable human behavior patterns, with users frequently selecting weak combinations or sharing codes with colleagues, undermining the system's integrity.
Biometric access control systems, while offering enhanced security through unique physiological characteristics, encounter distinct technical and operational challenges. Fingerprint recognition systems struggle with environmental factors such as moisture, dirt, or temporary skin damage that can prevent legitimate users from gaining access. False rejection rates typically range from 1-5%, creating operational friction and user frustration in high-traffic environments.
Facial recognition technology demonstrates inconsistencies when confronted with lighting variations, facial hair changes, aging, or the use of masks and accessories. These systems often require controlled environmental conditions to maintain acceptable accuracy levels, limiting their deployment flexibility. Additionally, spoofing attacks using photographs or video recordings pose ongoing security concerns for less sophisticated implementations.
Both biometric and traditional systems face scalability constraints in large organizational deployments. Traditional systems require extensive physical infrastructure for card readers and secure credential distribution networks. Biometric systems demand significant computational resources for real-time processing and large-scale template storage, particularly in environments with thousands of users.
Integration challenges persist across both approaches when interfacing with existing security infrastructure. Legacy traditional systems often lack modern communication protocols, while biometric systems require specialized hardware and software components that may not seamlessly integrate with established security management platforms.
Privacy concerns represent a growing limitation for biometric systems, as they involve collecting and storing sensitive personal data. Regulatory compliance requirements, particularly under frameworks like GDPR, create additional operational complexity and potential liability exposure that traditional systems typically avoid.
Cost considerations further constrain both approaches, with biometric systems requiring higher initial capital investment and ongoing maintenance, while traditional systems incur continuous operational costs through credential replacement and administrative overhead.
Biometric access control systems, while offering enhanced security through unique physiological characteristics, encounter distinct technical and operational challenges. Fingerprint recognition systems struggle with environmental factors such as moisture, dirt, or temporary skin damage that can prevent legitimate users from gaining access. False rejection rates typically range from 1-5%, creating operational friction and user frustration in high-traffic environments.
Facial recognition technology demonstrates inconsistencies when confronted with lighting variations, facial hair changes, aging, or the use of masks and accessories. These systems often require controlled environmental conditions to maintain acceptable accuracy levels, limiting their deployment flexibility. Additionally, spoofing attacks using photographs or video recordings pose ongoing security concerns for less sophisticated implementations.
Both biometric and traditional systems face scalability constraints in large organizational deployments. Traditional systems require extensive physical infrastructure for card readers and secure credential distribution networks. Biometric systems demand significant computational resources for real-time processing and large-scale template storage, particularly in environments with thousands of users.
Integration challenges persist across both approaches when interfacing with existing security infrastructure. Legacy traditional systems often lack modern communication protocols, while biometric systems require specialized hardware and software components that may not seamlessly integrate with established security management platforms.
Privacy concerns represent a growing limitation for biometric systems, as they involve collecting and storing sensitive personal data. Regulatory compliance requirements, particularly under frameworks like GDPR, create additional operational complexity and potential liability exposure that traditional systems typically avoid.
Cost considerations further constrain both approaches, with biometric systems requiring higher initial capital investment and ongoing maintenance, while traditional systems incur continuous operational costs through credential replacement and administrative overhead.
Comparative Analysis of Current Security Entry Methods
01 Biometric authentication methods for access control
Access control systems utilize various biometric authentication methods to verify user identity and grant entry. These methods include fingerprint recognition, facial recognition, iris scanning, and voice recognition. Biometric data is captured, processed, and compared against stored templates to authenticate users. The systems can operate in standalone mode or be integrated with centralized databases for enhanced security and management capabilities.- Biometric authentication methods for access control: Access control systems utilize various biometric authentication methods to verify user identity and grant entry. These methods include fingerprint recognition, facial recognition, iris scanning, and voice recognition. Biometric data is captured, processed, and compared against stored templates to authenticate users. Multi-modal biometric systems combine multiple biometric traits to enhance security and accuracy. These authentication methods provide higher security levels compared to traditional password or card-based systems by ensuring that only authorized individuals can gain access.
- Integration of access control with surveillance and monitoring systems: Modern access control systems are integrated with surveillance cameras, motion detectors, and monitoring platforms to provide comprehensive security solutions. The integration enables real-time monitoring of entry points, automatic recording of access events, and immediate alert generation for unauthorized access attempts. Video analytics and artificial intelligence can be employed to detect suspicious behavior patterns and enhance threat detection capabilities. This integration creates a unified security ecosystem that improves overall facility protection and incident response.
- Mobile and wireless biometric access control solutions: Wireless and mobile-based access control systems enable flexible and convenient entry management through smartphones and portable devices. These solutions utilize Bluetooth, NFC, or cloud-based authentication to grant access without physical keys or cards. Mobile credentials can be easily distributed, updated, or revoked remotely, providing enhanced administrative control. Biometric sensors integrated into mobile devices can perform authentication before transmitting access credentials, adding an additional security layer. This approach reduces infrastructure costs and improves user convenience while maintaining security standards.
- Anti-spoofing and liveness detection in biometric systems: Advanced biometric access control systems incorporate anti-spoofing measures and liveness detection to prevent fraudulent access attempts using fake biometric samples. These technologies can detect presentation attacks such as photographs, masks, or artificial fingerprints. Liveness detection methods analyze physiological characteristics like blood flow, skin texture, or involuntary movements to verify that biometric samples come from living individuals. Multi-spectral imaging and challenge-response mechanisms further enhance the ability to distinguish genuine users from spoofing attempts, significantly improving system security efficacy.
- Cloud-based access control management and data security: Cloud-based access control platforms provide centralized management of multiple entry points across distributed locations with enhanced scalability and flexibility. These systems enable remote administration, real-time access monitoring, and automated reporting through web-based interfaces. Encrypted communication protocols and secure data storage protect biometric templates and access logs from unauthorized access. Cloud solutions facilitate integration with other enterprise security systems and support advanced analytics for identifying security trends and vulnerabilities. Regular software updates and security patches can be deployed automatically to maintain system integrity.
02 Multi-factor authentication and security enhancement
To improve security efficacy, access control systems implement multi-factor authentication combining biometric verification with additional security layers. These may include password verification, security tokens, smart cards, or mobile device authentication. The combination of multiple authentication factors significantly reduces the risk of unauthorized access and enhances overall system security by requiring multiple forms of verification before granting entry.Expand Specific Solutions03 Real-time monitoring and alert systems
Advanced access control systems incorporate real-time monitoring capabilities to track entry attempts, detect anomalies, and generate alerts for security personnel. These systems can identify suspicious activities, failed authentication attempts, and unauthorized access patterns. Integration with surveillance cameras and logging systems provides comprehensive security oversight and enables rapid response to potential security breaches.Expand Specific Solutions04 Cloud-based and networked access control infrastructure
Modern access control systems leverage cloud computing and network connectivity to enable centralized management, remote administration, and scalable deployment across multiple locations. These systems allow administrators to manage user credentials, update access permissions, and monitor security events from anywhere. The networked infrastructure supports integration with other security systems and enables data synchronization across distributed facilities.Expand Specific Solutions05 Anti-spoofing and liveness detection technologies
To counter fraudulent access attempts, biometric entry systems incorporate anti-spoofing measures and liveness detection capabilities. These technologies can distinguish between genuine biometric samples and fake reproductions such as photographs, masks, or artificial fingerprints. Advanced algorithms analyze multiple characteristics including depth perception, thermal signatures, and behavioral patterns to ensure the authenticity of biometric data presented during authentication.Expand Specific Solutions
Leading Access Control and Biometric Technology Providers
The access control systems versus biometric entry security landscape represents a mature market undergoing technological transformation, with the industry transitioning from traditional card-based systems to advanced biometric solutions. The market demonstrates substantial scale, driven by increasing security demands across commercial, residential, and government sectors. Technology maturity varies significantly among key players: established giants like Siemens AG, Honeywell International, and ASSA ABLOY AB leverage decades of infrastructure expertise, while specialized firms such as DERMALOG Identification Systems and HID Global focus on cutting-edge biometric innovations. Companies like Tencent Technology and Intel Corp. bring advanced AI and processing capabilities, enhancing system intelligence. The competitive landscape shows convergence between traditional access control manufacturers and biometric specialists, with dormakaba Schweiz AG and Motorola Solutions exemplifying hybrid approaches that integrate both technologies for comprehensive security solutions.
Hid Global GmbH
Technical Solution: HID Global provides comprehensive access control solutions combining traditional card-based systems with advanced biometric technologies. Their platform integrates multi-factor authentication using proximity cards, smart cards, and biometric readers including fingerprint, facial recognition, and iris scanning. The system offers centralized management through cloud-based platforms, enabling real-time monitoring and access control across multiple locations. Their biometric solutions utilize advanced algorithms for liveness detection and anti-spoofing measures, ensuring high security standards. The platform supports various authentication modes including single-factor card access, biometric-only verification, and multi-modal biometric fusion combining multiple biometric traits for enhanced accuracy and security.
Strengths: Industry-leading expertise in both traditional and biometric access control, comprehensive multi-modal authentication options, strong anti-spoofing capabilities. Weaknesses: Higher implementation costs, complex integration requirements for legacy systems.
DERMALOG Identification Systems GmbH
Technical Solution: DERMALOG specializes in advanced biometric identification systems with focus on fingerprint, face, and iris recognition technologies. Their access control solutions feature high-precision biometric sensors with FBI-certified fingerprint recognition algorithms and real-time facial recognition capabilities. The system supports large-scale deployments with centralized biometric template management and cross-matching capabilities across multiple locations. Their technology includes advanced liveness detection, 3D facial recognition, and multi-spectral imaging for enhanced security and accuracy. The platform offers flexible deployment options including standalone biometric terminals, integrated access control systems, and mobile biometric authentication solutions with processing speeds of under one second for identification.
Strengths: Specialized biometric expertise with government-grade security standards, high accuracy rates, fast processing speeds. Weaknesses: Limited traditional access control integration, higher costs for small-scale implementations.
Core Patents in Biometric Authentication Technologies
Access control to secured locations using relaxed biometrics
PatentWO2024026375A1
Innovation
- A method and apparatus using a machine learning model to process biometric information samples, assigning cluster identifiers, and matching them with authenticated clusters, allowing access only when the identifiers match, thus avoiding the storage of unique personal data and utilizing existing hardware for efficient processing.
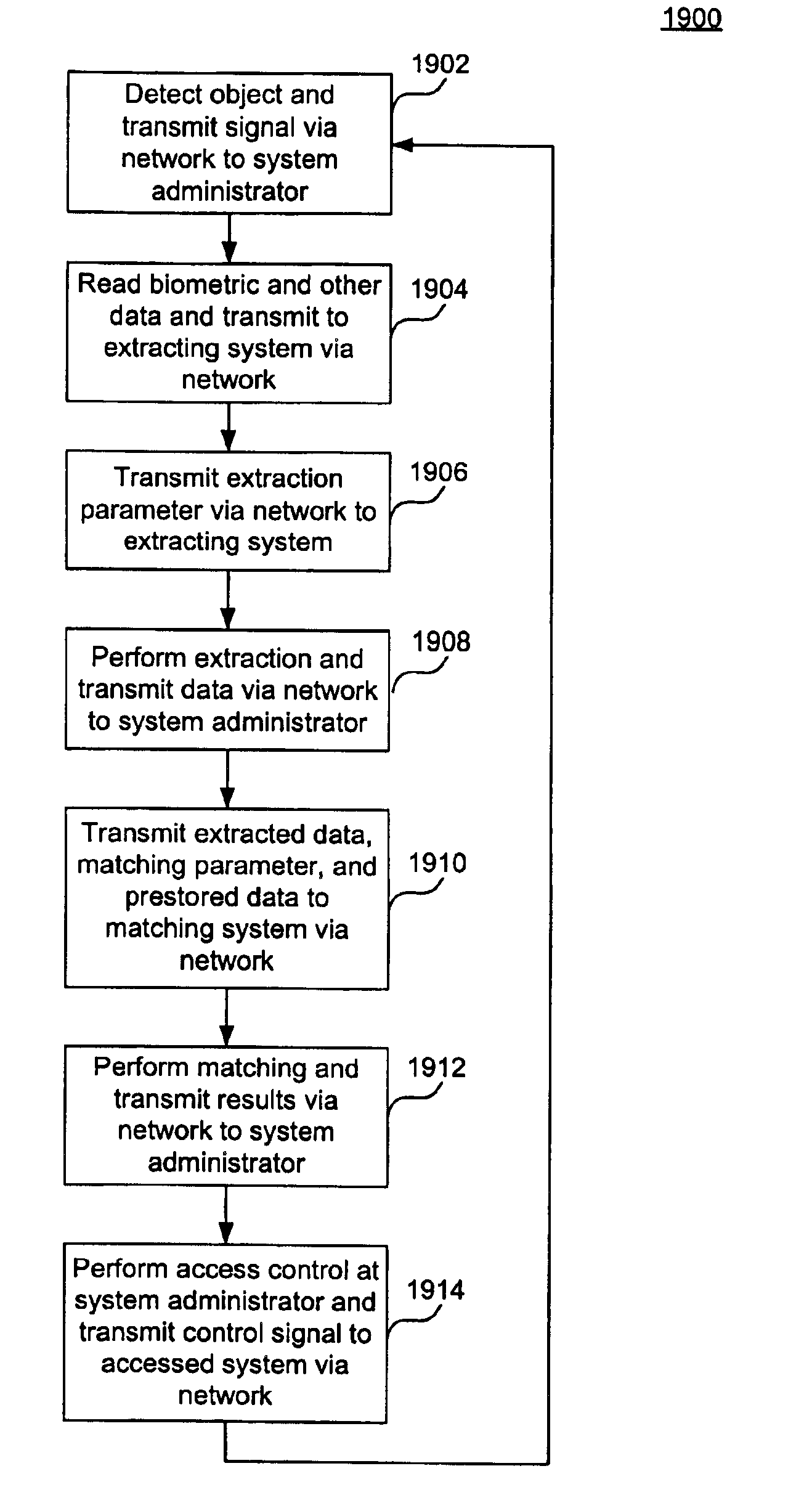
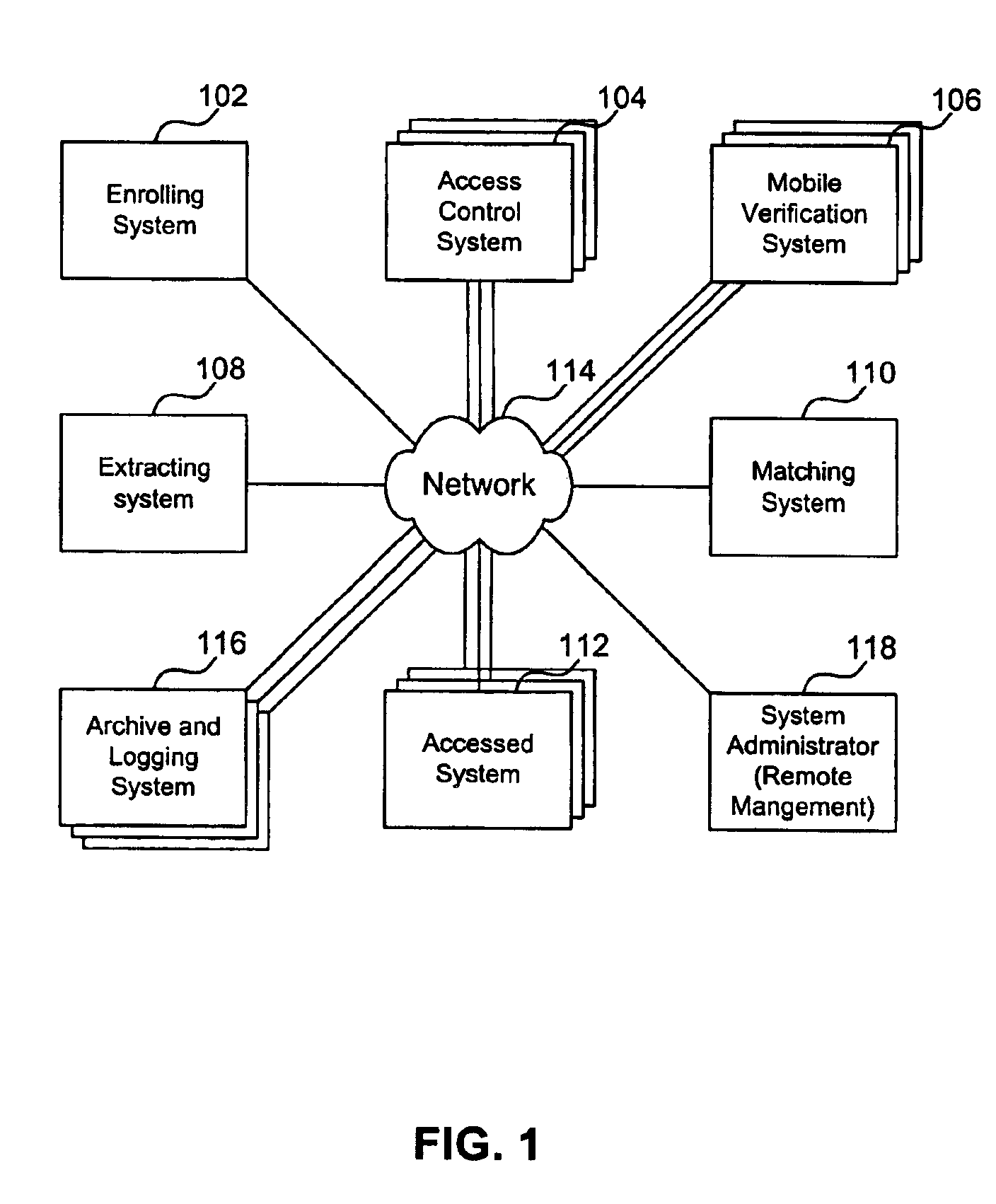
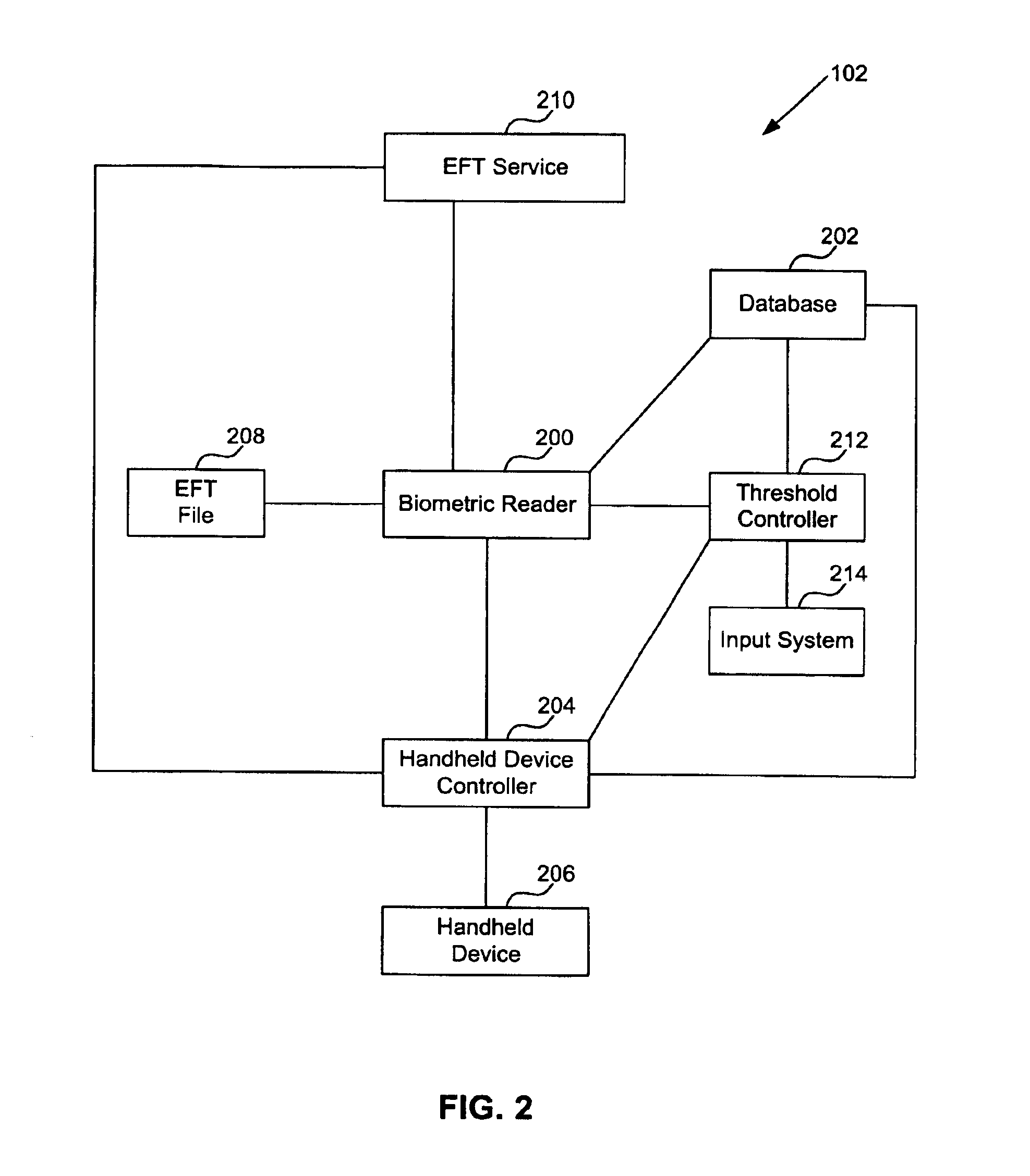
Systems and methods utilizing biometric data
PatentInactiveUS7079007B2
Innovation
- A system that includes an enrollment system for storing biometric data, an access control system for reading and managing biometric data, and a networked architecture for distributed processing of extraction and matching, utilizing threshold values to enhance security and reduce false rejections, allowing for easy scalability and minimal updating needs.
Privacy Regulations Impact on Biometric Data Usage
The implementation of biometric entry systems in access control faces increasingly complex regulatory landscapes that significantly impact their deployment and operational effectiveness. Privacy regulations worldwide have established stringent requirements for biometric data collection, storage, and processing, fundamentally altering how organizations approach biometric security solutions.
The European Union's General Data Protection Regulation (GDPR) represents the most comprehensive framework affecting biometric data usage, classifying biometric identifiers as sensitive personal data requiring explicit consent and heightened protection measures. Under GDPR, organizations must demonstrate legitimate interests for biometric data processing, implement data minimization principles, and provide clear opt-out mechanisms. This regulatory framework has created substantial compliance costs and operational constraints for biometric access control systems across European markets.
Similar regulatory trends have emerged globally, with jurisdictions like California's Consumer Privacy Act (CCPA) and various state-level biometric privacy laws imposing specific requirements on biometric data handling. Illinois' Biometric Information Privacy Act (BIPA) has proven particularly influential, requiring written consent before biometric data collection and establishing private rights of action that have resulted in significant litigation costs for organizations.
These regulatory requirements have driven technological adaptations in biometric systems, including the development of template-on-card solutions that store biometric templates locally rather than in centralized databases. Edge computing approaches and federated authentication systems have gained prominence as methods to minimize biometric data transmission and storage while maintaining security effectiveness.
The regulatory impact extends beyond technical implementation to affect system architecture decisions and vendor selection criteria. Organizations increasingly prioritize biometric solutions offering privacy-by-design features, such as irreversible template encryption, local processing capabilities, and automated data deletion functions. These compliance-driven requirements often increase system complexity and deployment costs while potentially limiting certain advanced biometric features.
Cross-border data transfer restrictions have particularly affected multinational organizations implementing unified biometric access control systems. Regulatory requirements for data localization and transfer impact assessments have necessitated regionalized system architectures and increased operational complexity for global enterprises seeking consistent security standards across multiple jurisdictions.
The European Union's General Data Protection Regulation (GDPR) represents the most comprehensive framework affecting biometric data usage, classifying biometric identifiers as sensitive personal data requiring explicit consent and heightened protection measures. Under GDPR, organizations must demonstrate legitimate interests for biometric data processing, implement data minimization principles, and provide clear opt-out mechanisms. This regulatory framework has created substantial compliance costs and operational constraints for biometric access control systems across European markets.
Similar regulatory trends have emerged globally, with jurisdictions like California's Consumer Privacy Act (CCPA) and various state-level biometric privacy laws imposing specific requirements on biometric data handling. Illinois' Biometric Information Privacy Act (BIPA) has proven particularly influential, requiring written consent before biometric data collection and establishing private rights of action that have resulted in significant litigation costs for organizations.
These regulatory requirements have driven technological adaptations in biometric systems, including the development of template-on-card solutions that store biometric templates locally rather than in centralized databases. Edge computing approaches and federated authentication systems have gained prominence as methods to minimize biometric data transmission and storage while maintaining security effectiveness.
The regulatory impact extends beyond technical implementation to affect system architecture decisions and vendor selection criteria. Organizations increasingly prioritize biometric solutions offering privacy-by-design features, such as irreversible template encryption, local processing capabilities, and automated data deletion functions. These compliance-driven requirements often increase system complexity and deployment costs while potentially limiting certain advanced biometric features.
Cross-border data transfer restrictions have particularly affected multinational organizations implementing unified biometric access control systems. Regulatory requirements for data localization and transfer impact assessments have necessitated regionalized system architectures and increased operational complexity for global enterprises seeking consistent security standards across multiple jurisdictions.
Cybersecurity Vulnerabilities in Digital Access Systems
Digital access systems face an evolving landscape of cybersecurity threats that compromise both traditional access control mechanisms and advanced biometric entry solutions. These vulnerabilities stem from multiple attack vectors, ranging from network-based intrusions to sophisticated spoofing techniques that exploit inherent weaknesses in authentication protocols.
Traditional access control systems utilizing card-based or PIN-based authentication are particularly susceptible to credential theft, replay attacks, and social engineering exploits. Attackers can intercept RFID signals, clone access cards, or capture authentication data through man-in-the-middle attacks. The centralized nature of many access control databases creates single points of failure, where successful penetration can compromise entire organizational security infrastructures.
Biometric systems, while offering enhanced security through unique physiological identifiers, introduce distinct vulnerability categories. Presentation attacks, commonly known as spoofing, exploit biometric sensors through artificial replicas of fingerprints, facial images, or iris patterns. Advanced deepfake technologies and 3D printing capabilities have significantly lowered the barrier for sophisticated biometric circumvention attempts.
Network infrastructure vulnerabilities represent a critical concern across both system types. Inadequate encryption protocols, unpatched firmware, and weak network segmentation create pathways for unauthorized access. IoT-enabled access devices often lack robust security frameworks, making them attractive targets for botnet recruitment and lateral movement within corporate networks.
Data storage and transmission vulnerabilities pose additional risks, particularly for biometric systems that handle irreplaceable biological data. Unlike passwords or access cards, compromised biometric templates cannot be easily replaced, creating permanent security liabilities. Inadequate template protection, insufficient encryption during transmission, and vulnerable cloud storage implementations expose sensitive biometric data to theft and misuse.
Emerging threats include AI-powered attack methodologies that can systematically probe system weaknesses, adaptive malware targeting access control infrastructure, and quantum computing implications for current encryption standards. These evolving threat vectors necessitate continuous security assessment and adaptive defense strategies to maintain system integrity and organizational security posture.
Traditional access control systems utilizing card-based or PIN-based authentication are particularly susceptible to credential theft, replay attacks, and social engineering exploits. Attackers can intercept RFID signals, clone access cards, or capture authentication data through man-in-the-middle attacks. The centralized nature of many access control databases creates single points of failure, where successful penetration can compromise entire organizational security infrastructures.
Biometric systems, while offering enhanced security through unique physiological identifiers, introduce distinct vulnerability categories. Presentation attacks, commonly known as spoofing, exploit biometric sensors through artificial replicas of fingerprints, facial images, or iris patterns. Advanced deepfake technologies and 3D printing capabilities have significantly lowered the barrier for sophisticated biometric circumvention attempts.
Network infrastructure vulnerabilities represent a critical concern across both system types. Inadequate encryption protocols, unpatched firmware, and weak network segmentation create pathways for unauthorized access. IoT-enabled access devices often lack robust security frameworks, making them attractive targets for botnet recruitment and lateral movement within corporate networks.
Data storage and transmission vulnerabilities pose additional risks, particularly for biometric systems that handle irreplaceable biological data. Unlike passwords or access cards, compromised biometric templates cannot be easily replaced, creating permanent security liabilities. Inadequate template protection, insufficient encryption during transmission, and vulnerable cloud storage implementations expose sensitive biometric data to theft and misuse.
Emerging threats include AI-powered attack methodologies that can systematically probe system weaknesses, adaptive malware targeting access control infrastructure, and quantum computing implications for current encryption standards. These evolving threat vectors necessitate continuous security assessment and adaptive defense strategies to maintain system integrity and organizational security posture.
Unlock deeper insights with PatSnap Eureka Quick Research — get a full tech report to explore trends and direct your research. Try now!
Generate Your Research Report Instantly with AI Agent
Supercharge your innovation with PatSnap Eureka AI Agent Platform!