Baseline Cyber Resilience Techniques for Emerging AV Technologies
MAR 5, 20269 MIN READ
Generate Your Research Report Instantly with AI Agent
PatSnap Eureka helps you evaluate technical feasibility & market potential.
AV Cyber Resilience Background and Security Objectives
The automotive industry is undergoing a revolutionary transformation with the emergence of autonomous vehicles (AV) and connected car technologies. This paradigm shift has fundamentally altered the cybersecurity landscape, introducing unprecedented attack surfaces and vulnerabilities that traditional automotive security frameworks were never designed to address. The evolution from mechanical systems to software-defined vehicles has created complex interconnected networks that extend far beyond the vehicle itself, encompassing cloud infrastructure, mobile applications, and smart city ecosystems.
Historically, automotive cybersecurity concerns were minimal due to the isolated nature of vehicle systems. However, the integration of advanced driver assistance systems (ADAS), vehicle-to-everything (V2X) communication protocols, and over-the-air (OTA) update capabilities has exponentially increased the potential entry points for malicious actors. The transition from closed automotive networks to internet-connected platforms has necessitated a complete reimagining of security architectures and defense mechanisms.
The primary security objectives for emerging AV technologies encompass multiple critical dimensions that must be addressed simultaneously. Confidentiality remains paramount, ensuring that sensitive data including passenger information, location tracking, and behavioral patterns are protected from unauthorized access. The vast amounts of personal and operational data generated by modern vehicles require robust encryption and access control mechanisms to prevent privacy breaches and corporate espionage.
Integrity represents another fundamental objective, focusing on maintaining the authenticity and accuracy of critical vehicle functions and communications. Any compromise to system integrity could result in catastrophic safety failures, making tamper detection and prevention mechanisms essential components of AV security frameworks. This includes protecting against malicious code injection, sensor spoofing, and communication manipulation attacks that could alter vehicle behavior or decision-making processes.
Availability ensures that critical vehicle systems remain operational and accessible when needed, preventing denial-of-service attacks that could disable essential safety functions or strand passengers. The real-time nature of autonomous driving systems demands continuous availability of navigation, collision avoidance, and emergency response capabilities, making resilience against cyber attacks a life-critical requirement.
Safety emerges as the overarching objective that encompasses all other security considerations in the AV context. Unlike traditional IT systems where security breaches primarily result in data loss or financial damage, compromised vehicle systems pose direct threats to human life and public safety. This unique characteristic necessitates security-by-design approaches that prioritize fail-safe mechanisms and graceful degradation under attack conditions.
Historically, automotive cybersecurity concerns were minimal due to the isolated nature of vehicle systems. However, the integration of advanced driver assistance systems (ADAS), vehicle-to-everything (V2X) communication protocols, and over-the-air (OTA) update capabilities has exponentially increased the potential entry points for malicious actors. The transition from closed automotive networks to internet-connected platforms has necessitated a complete reimagining of security architectures and defense mechanisms.
The primary security objectives for emerging AV technologies encompass multiple critical dimensions that must be addressed simultaneously. Confidentiality remains paramount, ensuring that sensitive data including passenger information, location tracking, and behavioral patterns are protected from unauthorized access. The vast amounts of personal and operational data generated by modern vehicles require robust encryption and access control mechanisms to prevent privacy breaches and corporate espionage.
Integrity represents another fundamental objective, focusing on maintaining the authenticity and accuracy of critical vehicle functions and communications. Any compromise to system integrity could result in catastrophic safety failures, making tamper detection and prevention mechanisms essential components of AV security frameworks. This includes protecting against malicious code injection, sensor spoofing, and communication manipulation attacks that could alter vehicle behavior or decision-making processes.
Availability ensures that critical vehicle systems remain operational and accessible when needed, preventing denial-of-service attacks that could disable essential safety functions or strand passengers. The real-time nature of autonomous driving systems demands continuous availability of navigation, collision avoidance, and emergency response capabilities, making resilience against cyber attacks a life-critical requirement.
Safety emerges as the overarching objective that encompasses all other security considerations in the AV context. Unlike traditional IT systems where security breaches primarily result in data loss or financial damage, compromised vehicle systems pose direct threats to human life and public safety. This unique characteristic necessitates security-by-design approaches that prioritize fail-safe mechanisms and graceful degradation under attack conditions.
Market Demand for Secure Autonomous Vehicle Technologies
The autonomous vehicle market is experiencing unprecedented growth driven by increasing consumer demand for enhanced safety, convenience, and mobility solutions. However, this expansion is fundamentally contingent upon establishing robust cybersecurity frameworks that can protect against evolving digital threats. Market research indicates that consumer confidence in autonomous vehicle adoption directly correlates with perceived security measures, making cyber resilience a critical market differentiator rather than merely a technical requirement.
Enterprise fleet operators represent a significant early-adopter segment, particularly in logistics, ride-sharing, and public transportation sectors. These organizations prioritize secure autonomous vehicle technologies due to their operational scale and liability exposure. Fleet managers consistently identify cybersecurity as a primary concern when evaluating autonomous vehicle investments, recognizing that a single security breach could compromise entire operational networks and result in substantial financial losses.
Regulatory compliance requirements are creating substantial market demand for standardized security solutions. Government agencies worldwide are developing mandatory cybersecurity frameworks for autonomous vehicles, establishing minimum security baselines that manufacturers must meet. This regulatory environment is driving systematic demand for proven cyber resilience technologies, creating opportunities for specialized security solution providers.
Insurance industry dynamics are significantly influencing market demand patterns. Insurance providers are developing risk assessment models that heavily weight cybersecurity capabilities when determining coverage terms and premiums for autonomous vehicle deployments. Organizations with demonstrable cyber resilience measures receive preferential insurance rates, creating direct economic incentives for security technology adoption.
The competitive landscape reveals that automotive manufacturers are increasingly positioning cybersecurity as a core value proposition. Premium vehicle segments particularly emphasize advanced security features as luxury differentiators, while mass-market manufacturers focus on cost-effective baseline security implementations. This segmentation is creating diverse market opportunities for security technology providers across different price points and capability levels.
Supply chain security concerns are generating additional demand for comprehensive cyber resilience solutions. Autonomous vehicle ecosystems involve complex networks of suppliers, software providers, and service partners, each representing potential security vulnerabilities. Organizations are seeking integrated security platforms that can manage risks across entire supply chains, driving demand for holistic cyber resilience approaches rather than point solutions.
Enterprise fleet operators represent a significant early-adopter segment, particularly in logistics, ride-sharing, and public transportation sectors. These organizations prioritize secure autonomous vehicle technologies due to their operational scale and liability exposure. Fleet managers consistently identify cybersecurity as a primary concern when evaluating autonomous vehicle investments, recognizing that a single security breach could compromise entire operational networks and result in substantial financial losses.
Regulatory compliance requirements are creating substantial market demand for standardized security solutions. Government agencies worldwide are developing mandatory cybersecurity frameworks for autonomous vehicles, establishing minimum security baselines that manufacturers must meet. This regulatory environment is driving systematic demand for proven cyber resilience technologies, creating opportunities for specialized security solution providers.
Insurance industry dynamics are significantly influencing market demand patterns. Insurance providers are developing risk assessment models that heavily weight cybersecurity capabilities when determining coverage terms and premiums for autonomous vehicle deployments. Organizations with demonstrable cyber resilience measures receive preferential insurance rates, creating direct economic incentives for security technology adoption.
The competitive landscape reveals that automotive manufacturers are increasingly positioning cybersecurity as a core value proposition. Premium vehicle segments particularly emphasize advanced security features as luxury differentiators, while mass-market manufacturers focus on cost-effective baseline security implementations. This segmentation is creating diverse market opportunities for security technology providers across different price points and capability levels.
Supply chain security concerns are generating additional demand for comprehensive cyber resilience solutions. Autonomous vehicle ecosystems involve complex networks of suppliers, software providers, and service partners, each representing potential security vulnerabilities. Organizations are seeking integrated security platforms that can manage risks across entire supply chains, driving demand for holistic cyber resilience approaches rather than point solutions.
Current AV Cybersecurity State and Attack Surface Challenges
The cybersecurity landscape for autonomous vehicles presents a complex and rapidly evolving challenge that extends far beyond traditional automotive security concerns. Current AV systems integrate multiple interconnected components including sensors, communication modules, processing units, and software platforms, creating an unprecedented attack surface that spans both physical and digital domains.
Modern autonomous vehicles rely heavily on sensor fusion technologies, incorporating LiDAR, cameras, radar, and ultrasonic sensors to perceive their environment. Each sensor type introduces unique vulnerabilities, from signal jamming and spoofing attacks on GPS and communication systems to more sophisticated adversarial attacks on machine learning models used for object recognition and decision-making.
The connectivity requirements of AV systems significantly expand the potential attack vectors. Vehicle-to-everything (V2X) communications, over-the-air update mechanisms, and cloud-based processing services create multiple entry points for malicious actors. These communication channels, while essential for AV functionality, introduce risks including man-in-the-middle attacks, data interception, and unauthorized system access.
Software complexity represents another critical challenge in the current AV cybersecurity state. Modern autonomous vehicles contain millions of lines of code distributed across multiple electronic control units (ECUs), real-time operating systems, and AI-driven decision engines. This software ecosystem often incorporates third-party components and open-source libraries, creating potential supply chain vulnerabilities that are difficult to monitor and secure comprehensively.
The integration of artificial intelligence and machine learning algorithms introduces novel attack surfaces specific to AV technologies. Adversarial machine learning attacks can manipulate sensor inputs or training data to cause misclassification of objects, potentially leading to dangerous driving decisions. These AI-specific vulnerabilities require specialized detection and mitigation strategies that differ significantly from conventional cybersecurity approaches.
Current regulatory frameworks and industry standards are struggling to keep pace with the rapid technological advancement in AV systems. The lack of comprehensive cybersecurity standards specifically tailored for autonomous vehicles creates inconsistencies in security implementation across different manufacturers and technology providers, potentially leaving critical vulnerabilities unaddressed across the industry.
Modern autonomous vehicles rely heavily on sensor fusion technologies, incorporating LiDAR, cameras, radar, and ultrasonic sensors to perceive their environment. Each sensor type introduces unique vulnerabilities, from signal jamming and spoofing attacks on GPS and communication systems to more sophisticated adversarial attacks on machine learning models used for object recognition and decision-making.
The connectivity requirements of AV systems significantly expand the potential attack vectors. Vehicle-to-everything (V2X) communications, over-the-air update mechanisms, and cloud-based processing services create multiple entry points for malicious actors. These communication channels, while essential for AV functionality, introduce risks including man-in-the-middle attacks, data interception, and unauthorized system access.
Software complexity represents another critical challenge in the current AV cybersecurity state. Modern autonomous vehicles contain millions of lines of code distributed across multiple electronic control units (ECUs), real-time operating systems, and AI-driven decision engines. This software ecosystem often incorporates third-party components and open-source libraries, creating potential supply chain vulnerabilities that are difficult to monitor and secure comprehensively.
The integration of artificial intelligence and machine learning algorithms introduces novel attack surfaces specific to AV technologies. Adversarial machine learning attacks can manipulate sensor inputs or training data to cause misclassification of objects, potentially leading to dangerous driving decisions. These AI-specific vulnerabilities require specialized detection and mitigation strategies that differ significantly from conventional cybersecurity approaches.
Current regulatory frameworks and industry standards are struggling to keep pace with the rapid technological advancement in AV systems. The lack of comprehensive cybersecurity standards specifically tailored for autonomous vehicles creates inconsistencies in security implementation across different manufacturers and technology providers, potentially leaving critical vulnerabilities unaddressed across the industry.
Existing Baseline Cyber Resilience Solutions for AVs
01 Threat detection and anomaly identification systems
Cyber resilience techniques incorporate advanced threat detection mechanisms that continuously monitor network traffic and system behavior to identify anomalies and potential security breaches. These systems utilize machine learning algorithms and behavioral analysis to detect unusual patterns that may indicate cyber attacks. Real-time monitoring capabilities enable organizations to quickly identify and respond to security incidents before they cause significant damage. The detection systems can be integrated with automated response mechanisms to provide immediate countermeasures against identified threats.- Threat detection and anomaly identification systems: Cyber resilience techniques incorporate advanced threat detection mechanisms that continuously monitor network traffic and system behavior to identify anomalies and potential security breaches. These systems utilize machine learning algorithms and behavioral analysis to detect unusual patterns that may indicate cyber attacks. Real-time monitoring capabilities enable rapid identification of threats before they can cause significant damage to critical infrastructure.
- Automated incident response and recovery mechanisms: Implementation of automated response systems that can quickly react to detected threats and initiate recovery procedures without human intervention. These mechanisms include automated backup restoration, system isolation protocols, and failover procedures that maintain service continuity during cyber incidents. The automation reduces response time and minimizes the impact of security breaches on business operations.
- Multi-layered security architecture and defense strategies: Development of comprehensive security frameworks that employ multiple layers of protection including firewalls, intrusion prevention systems, and encryption protocols. This defense-in-depth approach ensures that if one security layer is compromised, additional layers continue to provide protection. The architecture integrates various security technologies to create a robust defensive posture against diverse cyber threats.
- Continuous security assessment and vulnerability management: Regular evaluation of system vulnerabilities through automated scanning tools and penetration testing methodologies. These assessment techniques identify weaknesses in infrastructure before they can be exploited by malicious actors. Continuous monitoring and updating of security patches ensure that systems remain protected against emerging threats and known vulnerabilities.
- Data protection and secure backup solutions: Implementation of robust data protection strategies including encryption, secure storage, and redundant backup systems to ensure data integrity and availability during cyber incidents. These solutions provide mechanisms for rapid data recovery and maintain business continuity even in the event of ransomware attacks or data breaches. Regular backup verification and testing ensure the reliability of recovery procedures.
02 Automated incident response and recovery mechanisms
Cyber resilience frameworks include automated incident response capabilities that enable systems to quickly recover from cyber attacks and security breaches. These mechanisms involve predefined response protocols, backup systems, and failover procedures that can be triggered automatically when threats are detected. The recovery processes are designed to minimize downtime and ensure business continuity during and after security incidents. Automated recovery systems can restore critical functions and data from secure backups while isolating compromised components.Expand Specific Solutions03 Security architecture and network segmentation
Cyber resilience is enhanced through robust security architecture that implements network segmentation and isolation techniques to contain potential breaches. This approach divides networks into separate zones with controlled access points, limiting the lateral movement of attackers within the system. Security architecture includes multiple layers of defense mechanisms, including firewalls, access controls, and encryption protocols. The segmented architecture ensures that even if one component is compromised, the entire system remains protected.Expand Specific Solutions04 Continuous security assessment and vulnerability management
Cyber resilience strategies incorporate continuous security assessment processes that regularly evaluate system vulnerabilities and security posture. These assessments involve automated scanning tools, penetration testing, and security audits to identify weaknesses before they can be exploited. Vulnerability management systems prioritize identified risks and provide remediation recommendations to strengthen overall security. Regular assessments ensure that security measures remain effective against evolving cyber threats and new attack vectors.Expand Specific Solutions05 Data protection and encryption technologies
Cyber resilience incorporates comprehensive data protection measures including encryption technologies to safeguard sensitive information from unauthorized access. These technologies ensure data confidentiality and integrity both at rest and in transit through advanced cryptographic methods. Data protection strategies include secure key management systems, access control mechanisms, and data loss prevention tools. The encryption frameworks are designed to maintain data security even in the event of system compromise or breach attempts.Expand Specific Solutions
Key Players in AV Cybersecurity and Defense Solutions
The baseline cyber resilience techniques for emerging autonomous vehicle (AV) technologies represent a rapidly evolving competitive landscape characterized by early-stage market development with significant growth potential. The market encompasses diverse players ranging from established technology giants like QUALCOMM, Canon, and Toshiba to specialized cybersecurity firms such as Nightwing Group and Akamai Technologies. Leading Chinese universities including Zhejiang University, Southeast University, and University of Electronic Science & Technology of China demonstrate strong academic research contributions, while telecommunications leaders like SK Telecom drive practical implementation. Technology maturity varies significantly across participants, with semiconductor companies like Realtek and Motorola providing foundational hardware security, while emerging players focus on software-based resilience solutions, indicating a fragmented but rapidly consolidating industry approaching commercial viability.
QUALCOMM, Inc.
Technical Solution: QUALCOMM has developed comprehensive cybersecurity frameworks for automotive applications, including secure boot processes, hardware security modules (HSMs), and over-the-air (OTA) update protection mechanisms. Their Snapdragon Automotive platforms integrate multiple layers of security including trusted execution environments (TEE), secure element integration, and real-time threat detection capabilities. The company implements cryptographic key management systems and secure communication protocols specifically designed for vehicle-to-everything (V2X) communications, ensuring data integrity and authentication in connected vehicle ecosystems.
Strengths: Industry-leading chipset integration with built-in security features, extensive automotive partnerships. Weaknesses: High licensing costs, dependency on proprietary solutions.
Raytheon Co.
Technical Solution: Raytheon specializes in defense-grade cybersecurity solutions for autonomous vehicles, focusing on threat intelligence, intrusion detection systems, and secure communications. Their approach includes advanced anomaly detection algorithms, machine learning-based threat identification, and robust encryption protocols for military and commercial AV applications. The company develops resilient architectures that can maintain operational capability even under cyber attack, incorporating redundant systems and fail-safe mechanisms. Their solutions emphasize real-time monitoring and response capabilities for critical infrastructure protection.
Strengths: Military-grade security expertise, proven defense applications, robust threat detection. Weaknesses: High cost, complex implementation, limited commercial market penetration.
Core Innovations in AV Threat Detection and Response
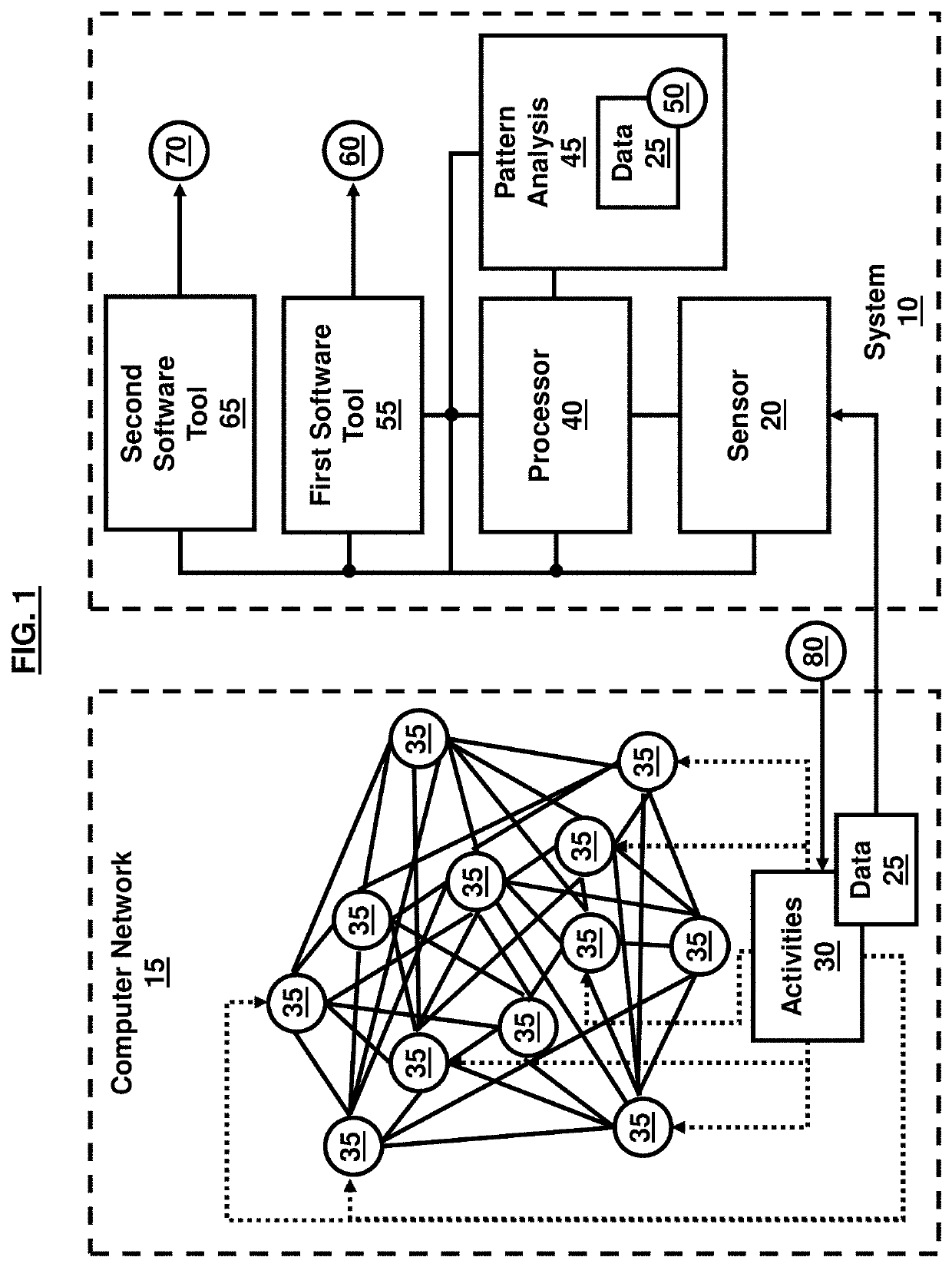
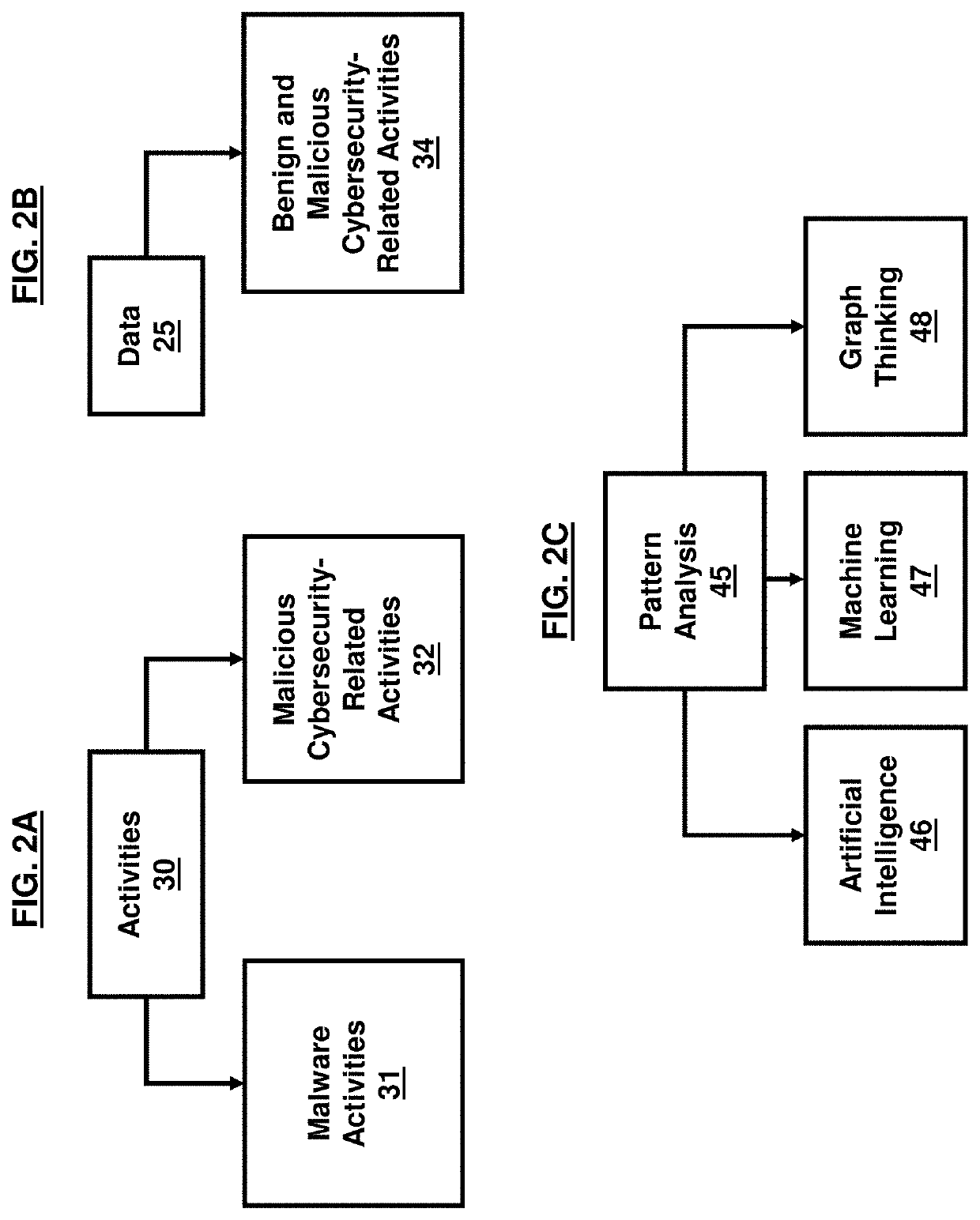
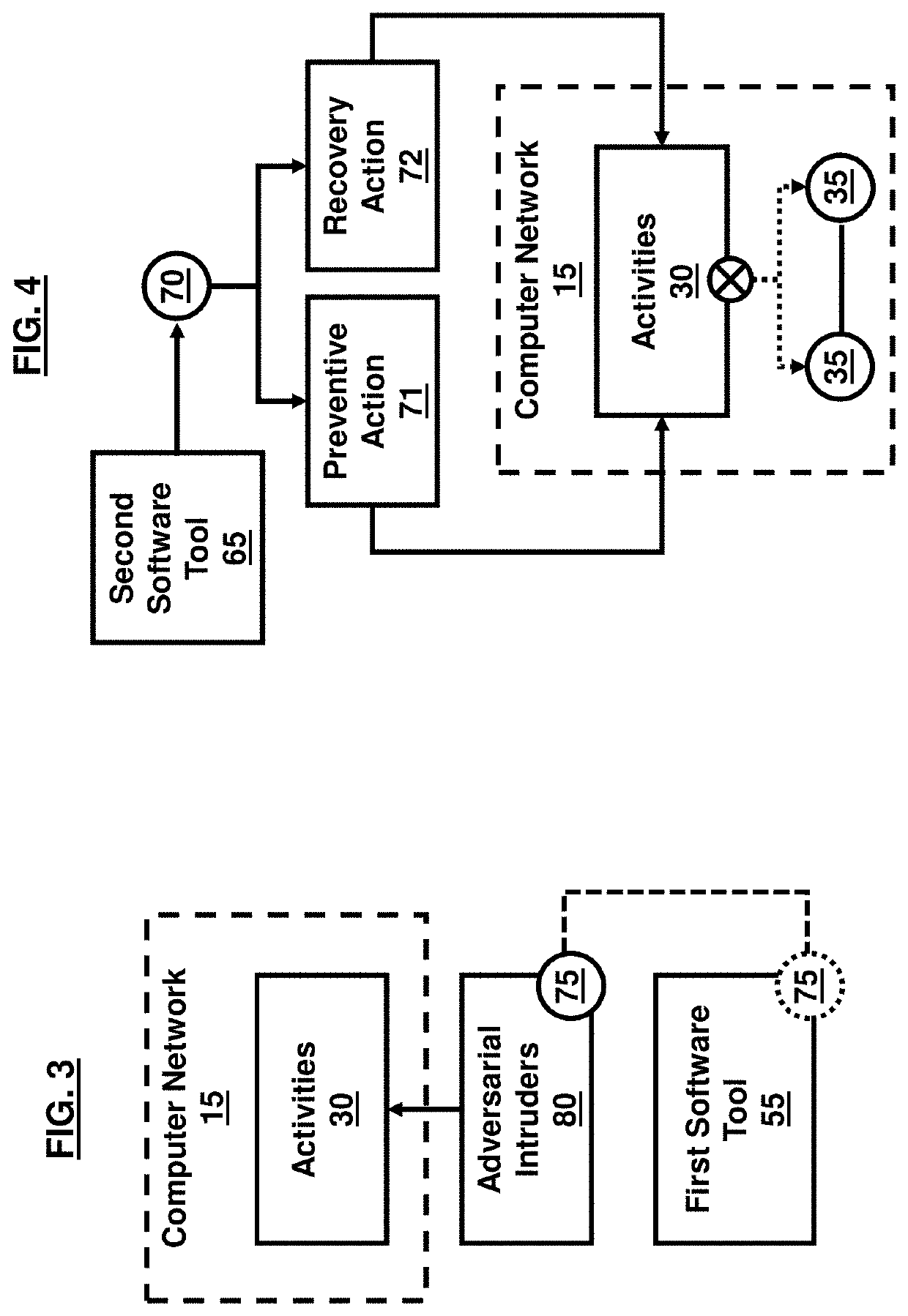
Cybersecurity resilience by integrating adversary and defender actions, deep learning, and graph thinking
PatentActiveUS20210352095A1
Innovation
- A system utilizing sensors to collect data on adversarial activities, a processor for pattern analysis, and machine learning techniques to predict adversary actions and intentions, as well as identify mitigation and recovery actions, creating a graphical representation of data paths to identify vulnerable nodes and predict malware infection propagation.
Modular autonomous vehicles
PatentActiveUS11840400B2
Innovation
- A modular and scalable autonomous vehicle system comprising interchangeable vehicular units with different propulsion systems and control units that can operate independently or synchronously, allowing for flexible configuration and adaptation to various tasks and environments.
Regulatory Framework for AV Cybersecurity Standards
The regulatory landscape for autonomous vehicle cybersecurity is rapidly evolving as governments and international organizations recognize the critical importance of establishing comprehensive standards. Current regulatory frameworks are being developed across multiple jurisdictions, with varying approaches to addressing the unique cybersecurity challenges posed by connected and autonomous vehicles.
The United Nations Economic Commission for Europe has established WP.29 regulations, particularly UN Regulation No. 155 on Cybersecurity Management Systems and UN Regulation No. 156 on Software Update Management Systems. These regulations mandate that vehicle manufacturers implement cybersecurity management systems throughout the vehicle lifecycle and establish secure processes for over-the-air software updates. The framework requires risk assessment methodologies, incident response procedures, and continuous monitoring capabilities.
In the United States, the National Highway Traffic Safety Administration has issued cybersecurity guidance documents while working toward more formal regulatory requirements. The Federal Motor Vehicle Safety Standards are being updated to incorporate cybersecurity considerations, with particular emphasis on critical safety systems protection. The Department of Transportation has established voluntary guidance that addresses vehicle design, development, and post-production phases.
The European Union has implemented the Type Approval Framework, which integrates cybersecurity requirements into vehicle certification processes. This framework mandates compliance with international standards such as ISO/SAE 21434 for automotive cybersecurity engineering and ISO 26262 for functional safety. The regulations require manufacturers to demonstrate robust cybersecurity risk management throughout vehicle development and operation.
Emerging regulatory trends focus on supply chain security, requiring manufacturers to assess and manage cybersecurity risks across their entire vendor ecosystem. Cross-border harmonization efforts are underway to establish consistent global standards, facilitating international vehicle deployment while maintaining security requirements. Regulatory bodies are also developing frameworks for cybersecurity incident reporting and information sharing among stakeholders.
The regulatory framework continues to evolve as new threats emerge and technology advances, requiring adaptive approaches that balance innovation with security imperatives while ensuring public safety and consumer protection.
The United Nations Economic Commission for Europe has established WP.29 regulations, particularly UN Regulation No. 155 on Cybersecurity Management Systems and UN Regulation No. 156 on Software Update Management Systems. These regulations mandate that vehicle manufacturers implement cybersecurity management systems throughout the vehicle lifecycle and establish secure processes for over-the-air software updates. The framework requires risk assessment methodologies, incident response procedures, and continuous monitoring capabilities.
In the United States, the National Highway Traffic Safety Administration has issued cybersecurity guidance documents while working toward more formal regulatory requirements. The Federal Motor Vehicle Safety Standards are being updated to incorporate cybersecurity considerations, with particular emphasis on critical safety systems protection. The Department of Transportation has established voluntary guidance that addresses vehicle design, development, and post-production phases.
The European Union has implemented the Type Approval Framework, which integrates cybersecurity requirements into vehicle certification processes. This framework mandates compliance with international standards such as ISO/SAE 21434 for automotive cybersecurity engineering and ISO 26262 for functional safety. The regulations require manufacturers to demonstrate robust cybersecurity risk management throughout vehicle development and operation.
Emerging regulatory trends focus on supply chain security, requiring manufacturers to assess and manage cybersecurity risks across their entire vendor ecosystem. Cross-border harmonization efforts are underway to establish consistent global standards, facilitating international vehicle deployment while maintaining security requirements. Regulatory bodies are also developing frameworks for cybersecurity incident reporting and information sharing among stakeholders.
The regulatory framework continues to evolve as new threats emerge and technology advances, requiring adaptive approaches that balance innovation with security imperatives while ensuring public safety and consumer protection.
Safety-Security Integration in Autonomous Driving Systems
The integration of safety and security in autonomous driving systems represents a fundamental paradigm shift from traditional automotive engineering approaches. Historically, automotive safety and cybersecurity have been addressed as separate domains, with safety focusing on preventing accidents through mechanical and electronic safeguards, while security concentrated on protecting against malicious attacks. However, the emergence of connected and autonomous vehicles has created unprecedented interdependencies between these two critical aspects.
Modern autonomous vehicles rely on complex sensor fusion systems, artificial intelligence algorithms, and continuous connectivity to cloud services and other vehicles. This interconnected architecture means that a cybersecurity breach can directly compromise safety-critical functions, while safety system failures can create new attack vectors for malicious actors. The traditional approach of implementing safety and security measures in isolation is no longer sufficient for emerging AV technologies.
The integration challenge is further complicated by the real-time nature of autonomous driving decisions. Safety systems must maintain deterministic response times and fail-safe behaviors, while security measures often introduce computational overhead and potential delays. Balancing these competing requirements requires innovative approaches that can provide robust protection without compromising the vehicle's ability to make split-second decisions in critical situations.
Current integration frameworks focus on establishing unified risk assessment methodologies that consider both safety hazards and security threats simultaneously. These frameworks evaluate potential failure modes through a combined lens, identifying scenarios where cybersecurity vulnerabilities could lead to safety incidents, and conversely, where safety system compromises might expose new security weaknesses.
The development of integrated safety-security architectures also involves implementing layered defense mechanisms that can gracefully degrade functionality when threats are detected. This includes designing redundant systems that can maintain essential safety functions even when certain components are compromised, and establishing secure communication protocols that preserve the integrity of safety-critical data exchanges between vehicle systems and external infrastructure.
Regulatory bodies and industry standards organizations are actively working to establish comprehensive guidelines that address this integration challenge, recognizing that the future of autonomous vehicle deployment depends on successfully merging these traditionally separate engineering disciplines into a cohesive, holistic approach to vehicle system design and operation.
Modern autonomous vehicles rely on complex sensor fusion systems, artificial intelligence algorithms, and continuous connectivity to cloud services and other vehicles. This interconnected architecture means that a cybersecurity breach can directly compromise safety-critical functions, while safety system failures can create new attack vectors for malicious actors. The traditional approach of implementing safety and security measures in isolation is no longer sufficient for emerging AV technologies.
The integration challenge is further complicated by the real-time nature of autonomous driving decisions. Safety systems must maintain deterministic response times and fail-safe behaviors, while security measures often introduce computational overhead and potential delays. Balancing these competing requirements requires innovative approaches that can provide robust protection without compromising the vehicle's ability to make split-second decisions in critical situations.
Current integration frameworks focus on establishing unified risk assessment methodologies that consider both safety hazards and security threats simultaneously. These frameworks evaluate potential failure modes through a combined lens, identifying scenarios where cybersecurity vulnerabilities could lead to safety incidents, and conversely, where safety system compromises might expose new security weaknesses.
The development of integrated safety-security architectures also involves implementing layered defense mechanisms that can gracefully degrade functionality when threats are detected. This includes designing redundant systems that can maintain essential safety functions even when certain components are compromised, and establishing secure communication protocols that preserve the integrity of safety-critical data exchanges between vehicle systems and external infrastructure.
Regulatory bodies and industry standards organizations are actively working to establish comprehensive guidelines that address this integration challenge, recognizing that the future of autonomous vehicle deployment depends on successfully merging these traditionally separate engineering disciplines into a cohesive, holistic approach to vehicle system design and operation.
Unlock deeper insights with PatSnap Eureka Quick Research — get a full tech report to explore trends and direct your research. Try now!
Generate Your Research Report Instantly with AI Agent
Supercharge your innovation with PatSnap Eureka AI Agent Platform!