How to Optimize Cyber Standards for Autonomous Logistics Fleets
MAR 5, 20269 MIN READ
Generate Your Research Report Instantly with AI Agent
PatSnap Eureka helps you evaluate technical feasibility & market potential.
Autonomous Logistics Cyber Standards Background and Objectives
The autonomous logistics industry has experienced unprecedented growth over the past decade, driven by advances in artificial intelligence, sensor technologies, and connectivity solutions. This evolution has fundamentally transformed supply chain operations, enabling unmanned vehicles, drones, and robotic systems to handle complex logistics tasks with minimal human intervention. However, this technological revolution has simultaneously introduced significant cybersecurity vulnerabilities that threaten the integrity, safety, and reliability of autonomous logistics operations.
Current cyber standards for autonomous logistics fleets remain fragmented and inadequate to address the unique challenges posed by interconnected, mobile, and semi-autonomous systems. Traditional cybersecurity frameworks were designed for static IT infrastructure and fail to account for the dynamic nature of logistics operations, real-time decision-making requirements, and the critical safety implications of compromised autonomous systems. The absence of comprehensive, industry-specific cyber standards has created a security gap that malicious actors increasingly exploit.
The complexity of autonomous logistics ecosystems compounds these challenges. Modern fleets integrate multiple communication protocols, cloud-based management systems, edge computing devices, and third-party software components, creating an expanded attack surface. Each component represents a potential entry point for cyber threats, while the interconnected nature of these systems means that a breach in one area can cascade throughout the entire network.
The primary objective of optimizing cyber standards for autonomous logistics fleets is to establish a comprehensive, adaptive security framework that addresses the unique operational requirements and threat landscape of autonomous logistics systems. This framework must balance security imperatives with operational efficiency, ensuring that protective measures do not compromise the speed, flexibility, and cost-effectiveness that make autonomous logistics attractive.
Key objectives include developing standardized security protocols for vehicle-to-vehicle and vehicle-to-infrastructure communications, establishing robust authentication and authorization mechanisms for fleet management systems, and creating incident response procedures tailored to mobile autonomous systems. Additionally, the standards must address data protection requirements for sensitive logistics information while enabling the real-time data sharing necessary for optimal fleet coordination.
The ultimate goal is to create a security ecosystem that enhances stakeholder confidence in autonomous logistics technologies, facilitates regulatory compliance, and supports the continued growth and adoption of autonomous systems across the logistics industry while maintaining the highest levels of operational security and safety.
Current cyber standards for autonomous logistics fleets remain fragmented and inadequate to address the unique challenges posed by interconnected, mobile, and semi-autonomous systems. Traditional cybersecurity frameworks were designed for static IT infrastructure and fail to account for the dynamic nature of logistics operations, real-time decision-making requirements, and the critical safety implications of compromised autonomous systems. The absence of comprehensive, industry-specific cyber standards has created a security gap that malicious actors increasingly exploit.
The complexity of autonomous logistics ecosystems compounds these challenges. Modern fleets integrate multiple communication protocols, cloud-based management systems, edge computing devices, and third-party software components, creating an expanded attack surface. Each component represents a potential entry point for cyber threats, while the interconnected nature of these systems means that a breach in one area can cascade throughout the entire network.
The primary objective of optimizing cyber standards for autonomous logistics fleets is to establish a comprehensive, adaptive security framework that addresses the unique operational requirements and threat landscape of autonomous logistics systems. This framework must balance security imperatives with operational efficiency, ensuring that protective measures do not compromise the speed, flexibility, and cost-effectiveness that make autonomous logistics attractive.
Key objectives include developing standardized security protocols for vehicle-to-vehicle and vehicle-to-infrastructure communications, establishing robust authentication and authorization mechanisms for fleet management systems, and creating incident response procedures tailored to mobile autonomous systems. Additionally, the standards must address data protection requirements for sensitive logistics information while enabling the real-time data sharing necessary for optimal fleet coordination.
The ultimate goal is to create a security ecosystem that enhances stakeholder confidence in autonomous logistics technologies, facilitates regulatory compliance, and supports the continued growth and adoption of autonomous systems across the logistics industry while maintaining the highest levels of operational security and safety.
Market Demand for Secure Autonomous Fleet Solutions
The global autonomous logistics market is experiencing unprecedented growth driven by the convergence of artificial intelligence, Internet of Things technologies, and increasing demand for supply chain efficiency. Organizations across industries are recognizing the transformative potential of autonomous fleet solutions, particularly in addressing labor shortages, reducing operational costs, and improving delivery precision. However, the widespread adoption of these technologies is fundamentally dependent on establishing robust cybersecurity frameworks that can protect critical infrastructure and sensitive data.
E-commerce giants and traditional logistics providers are actively investing in autonomous delivery systems, ranging from last-mile delivery drones to fully automated warehouse operations. The surge in online shopping, accelerated by global events and changing consumer behaviors, has created an urgent need for scalable logistics solutions that can operate with minimal human intervention while maintaining high security standards.
Manufacturing sectors, particularly automotive and pharmaceutical industries, are driving demand for secure autonomous fleet solutions to manage their complex supply chains. These industries require stringent cybersecurity measures due to the sensitive nature of their operations and the potential consequences of security breaches. The integration of autonomous vehicles in industrial logistics operations demands comprehensive cyber standards that can protect against both external threats and internal vulnerabilities.
Government agencies and defense organizations represent another significant market segment, requiring autonomous logistics solutions with military-grade security protocols. These entities are particularly focused on developing cyber standards that can withstand sophisticated attack vectors while ensuring operational continuity in critical missions.
The financial implications of cybersecurity breaches in autonomous logistics systems are substantial, encompassing direct financial losses, regulatory penalties, and reputational damage. This reality is driving organizations to prioritize investments in secure autonomous fleet solutions, even when they come with higher initial costs. The market demand is increasingly shifting toward comprehensive security-by-design approaches rather than retrofitted security measures.
Regional variations in regulatory requirements and cybersecurity standards are creating diverse market demands. European markets emphasize data privacy and GDPR compliance, while North American markets focus on critical infrastructure protection. Asian markets are rapidly developing their own cybersecurity frameworks, creating opportunities for standardized yet flexible security solutions that can adapt to different regulatory environments.
E-commerce giants and traditional logistics providers are actively investing in autonomous delivery systems, ranging from last-mile delivery drones to fully automated warehouse operations. The surge in online shopping, accelerated by global events and changing consumer behaviors, has created an urgent need for scalable logistics solutions that can operate with minimal human intervention while maintaining high security standards.
Manufacturing sectors, particularly automotive and pharmaceutical industries, are driving demand for secure autonomous fleet solutions to manage their complex supply chains. These industries require stringent cybersecurity measures due to the sensitive nature of their operations and the potential consequences of security breaches. The integration of autonomous vehicles in industrial logistics operations demands comprehensive cyber standards that can protect against both external threats and internal vulnerabilities.
Government agencies and defense organizations represent another significant market segment, requiring autonomous logistics solutions with military-grade security protocols. These entities are particularly focused on developing cyber standards that can withstand sophisticated attack vectors while ensuring operational continuity in critical missions.
The financial implications of cybersecurity breaches in autonomous logistics systems are substantial, encompassing direct financial losses, regulatory penalties, and reputational damage. This reality is driving organizations to prioritize investments in secure autonomous fleet solutions, even when they come with higher initial costs. The market demand is increasingly shifting toward comprehensive security-by-design approaches rather than retrofitted security measures.
Regional variations in regulatory requirements and cybersecurity standards are creating diverse market demands. European markets emphasize data privacy and GDPR compliance, while North American markets focus on critical infrastructure protection. Asian markets are rapidly developing their own cybersecurity frameworks, creating opportunities for standardized yet flexible security solutions that can adapt to different regulatory environments.
Current Cybersecurity Challenges in Autonomous Logistics
Autonomous logistics fleets face unprecedented cybersecurity challenges as they integrate advanced technologies including artificial intelligence, Internet of Things sensors, 5G connectivity, and cloud computing platforms. The attack surface has expanded exponentially compared to traditional logistics operations, creating multiple entry points for malicious actors to exploit system vulnerabilities and compromise fleet operations.
Vehicle-to-vehicle and vehicle-to-infrastructure communication protocols present significant security gaps in current implementations. Many autonomous logistics vehicles rely on wireless communication standards that lack robust encryption mechanisms, making them susceptible to man-in-the-middle attacks, signal jamming, and data interception. The real-time nature of these communications often prioritizes speed over security, creating inherent vulnerabilities in fleet coordination systems.
Supply chain security represents another critical challenge, as autonomous logistics fleets depend on complex networks of third-party software providers, hardware manufacturers, and service integrators. Each component in this ecosystem introduces potential security weaknesses, from compromised firmware in sensors to backdoors in navigation software. The interconnected nature of these systems means that a breach in one component can cascade throughout the entire fleet infrastructure.
Data privacy and protection concerns have intensified as autonomous logistics vehicles collect vast amounts of sensitive information, including cargo details, route patterns, customer data, and operational metrics. Current data governance frameworks struggle to address the cross-border nature of logistics operations, where data may traverse multiple jurisdictions with varying privacy regulations and security requirements.
Legacy system integration poses substantial security risks as many logistics companies attempt to retrofit existing infrastructure with autonomous capabilities. These hybrid environments often create security gaps where modern autonomous systems interface with older, less secure legacy platforms that were not designed with current cybersecurity threats in mind.
The shortage of cybersecurity expertise specifically trained in autonomous logistics systems compounds these challenges. Traditional IT security professionals may lack the specialized knowledge required to address the unique vulnerabilities present in autonomous vehicle networks, real-time logistics optimization algorithms, and distributed fleet management systems.
Regulatory compliance presents an additional layer of complexity, as cybersecurity standards for autonomous logistics remain fragmented across different regions and industries. The absence of unified global standards creates confusion for fleet operators and may result in inconsistent security implementations that leave critical vulnerabilities unaddressed.
Vehicle-to-vehicle and vehicle-to-infrastructure communication protocols present significant security gaps in current implementations. Many autonomous logistics vehicles rely on wireless communication standards that lack robust encryption mechanisms, making them susceptible to man-in-the-middle attacks, signal jamming, and data interception. The real-time nature of these communications often prioritizes speed over security, creating inherent vulnerabilities in fleet coordination systems.
Supply chain security represents another critical challenge, as autonomous logistics fleets depend on complex networks of third-party software providers, hardware manufacturers, and service integrators. Each component in this ecosystem introduces potential security weaknesses, from compromised firmware in sensors to backdoors in navigation software. The interconnected nature of these systems means that a breach in one component can cascade throughout the entire fleet infrastructure.
Data privacy and protection concerns have intensified as autonomous logistics vehicles collect vast amounts of sensitive information, including cargo details, route patterns, customer data, and operational metrics. Current data governance frameworks struggle to address the cross-border nature of logistics operations, where data may traverse multiple jurisdictions with varying privacy regulations and security requirements.
Legacy system integration poses substantial security risks as many logistics companies attempt to retrofit existing infrastructure with autonomous capabilities. These hybrid environments often create security gaps where modern autonomous systems interface with older, less secure legacy platforms that were not designed with current cybersecurity threats in mind.
The shortage of cybersecurity expertise specifically trained in autonomous logistics systems compounds these challenges. Traditional IT security professionals may lack the specialized knowledge required to address the unique vulnerabilities present in autonomous vehicle networks, real-time logistics optimization algorithms, and distributed fleet management systems.
Regulatory compliance presents an additional layer of complexity, as cybersecurity standards for autonomous logistics remain fragmented across different regions and industries. The absence of unified global standards creates confusion for fleet operators and may result in inconsistent security implementations that leave critical vulnerabilities unaddressed.
Existing Cyber Standard Solutions for Fleet Management
01 Cybersecurity risk assessment and compliance frameworks
Systems and methods for evaluating cybersecurity risks and ensuring compliance with established standards and regulations. These approaches involve automated assessment tools that analyze security postures, identify vulnerabilities, and measure adherence to industry standards. The frameworks provide structured methodologies for organizations to evaluate their security controls and implement necessary improvements to meet regulatory requirements.- Cybersecurity threat detection and monitoring systems: Systems and methods for detecting, monitoring, and analyzing cybersecurity threats in real-time across networks and digital infrastructure. These solutions employ advanced algorithms and monitoring techniques to identify potential security breaches, malicious activities, and vulnerabilities. The systems can automatically assess risk levels, generate alerts, and provide comprehensive threat intelligence to enable proactive security measures and rapid response to cyber incidents.
- Secure data transmission and encryption protocols: Technologies for ensuring secure communication and data transmission across networks through encryption, authentication, and secure protocol implementation. These methods establish secure channels for data exchange, protect sensitive information during transmission, and verify the identity of communicating parties. The solutions incorporate cryptographic techniques and security standards to prevent unauthorized access, data interception, and tampering during digital communications.
- Compliance and security policy management frameworks: Frameworks and systems for managing, implementing, and enforcing cybersecurity policies and compliance standards across organizations. These solutions provide tools for defining security requirements, monitoring adherence to regulatory standards, and ensuring consistent application of security policies. The frameworks enable automated compliance checking, policy enforcement, and documentation of security measures to meet industry regulations and best practices.
- Identity and access management systems: Systems for controlling and managing user identities, authentication, and access privileges within digital environments. These solutions implement mechanisms for verifying user identities, managing credentials, and enforcing access control policies based on roles and permissions. The systems provide centralized management of user accounts, support multi-factor authentication, and enable granular control over resource access to prevent unauthorized entry and maintain security boundaries.
- Cyber incident response and recovery mechanisms: Methods and systems for responding to cybersecurity incidents, mitigating damage, and recovering from security breaches. These solutions provide automated and manual procedures for incident detection, containment, investigation, and remediation. The mechanisms include backup and recovery capabilities, forensic analysis tools, and coordinated response protocols to minimize impact, restore normal operations, and prevent future incidents through lessons learned and improved security measures.
02 Cyber threat detection and monitoring systems
Technologies for continuous monitoring and detection of cyber threats through advanced analytics and real-time surveillance. These systems employ machine learning algorithms and behavioral analysis to identify anomalous activities and potential security breaches. The solutions enable organizations to maintain situational awareness and respond promptly to emerging threats while adhering to security standards.Expand Specific Solutions03 Standardized authentication and access control mechanisms
Methods and systems for implementing standardized authentication protocols and access control policies across digital platforms. These technologies ensure secure user verification and authorization processes that comply with industry security standards. The implementations include multi-factor authentication, role-based access controls, and identity management solutions that protect against unauthorized access.Expand Specific Solutions04 Data protection and encryption standards implementation
Technologies for implementing data protection measures and encryption standards to safeguard sensitive information. These solutions provide cryptographic methods and secure data handling practices that align with privacy regulations and security standards. The systems ensure data confidentiality, integrity, and availability throughout storage and transmission processes.Expand Specific Solutions05 Cyber incident response and recovery protocols
Frameworks and systems for managing cyber incidents and implementing recovery procedures according to established standards. These solutions provide structured approaches for incident detection, containment, eradication, and recovery processes. The protocols enable organizations to minimize damage from security breaches and restore normal operations while maintaining compliance with regulatory requirements.Expand Specific Solutions
Key Players in Autonomous Logistics and Cybersecurity
The autonomous logistics fleet cybersecurity landscape is in a nascent but rapidly evolving stage, driven by the convergence of autonomous vehicle technology and critical infrastructure protection needs. The market represents a multi-billion dollar opportunity as logistics companies increasingly adopt autonomous systems requiring robust cyber protection frameworks. Technology maturity varies significantly across key players, with established tech giants like Huawei Technologies and Sharp Corp. leading in foundational IoT and connectivity solutions, while specialized firms such as Penta Security Systems and Orange Security focus on dedicated cybersecurity applications. Research institutions including MITRE Corp., Beihang University, and North China Electric Power University are advancing theoretical frameworks and standards development. Industrial players like Samsung Heavy Industries, Hyundai Motor, and logistics specialists such as Zum Services and Pathover are integrating practical security implementations. The competitive landscape shows a fragmented ecosystem where traditional automotive manufacturers, cybersecurity specialists, and technology infrastructure providers are converging to establish comprehensive security standards for autonomous fleet operations.
Beijing Jingdong Zhenshi Information Technology Co Ltd
Technical Solution: JD Technology has developed cybersecurity standards for autonomous logistics fleets based on their extensive experience in e-commerce logistics operations, focusing on practical implementation in real-world delivery scenarios. Their solution includes secure fleet orchestration systems that can manage thousands of autonomous delivery vehicles simultaneously, implementing end-to-end encryption for package tracking and delivery confirmation systems. The platform incorporates machine learning algorithms trained on actual logistics data to detect potential security threats or operational anomalies, along with secure integration capabilities with existing warehouse management and customer service systems. Their approach emphasizes scalability and cost-effectiveness for large-scale commercial deployment.
Strengths: Extensive real-world logistics experience and proven scalability in high-volume operations with cost-effective implementation. Weaknesses: May have limited applicability outside of e-commerce logistics scenarios and potential concerns about data privacy in certain markets.
The MITRE Corp.
Technical Solution: MITRE has developed a comprehensive cybersecurity optimization framework for autonomous logistics fleets based on their ATT&CK methodology, focusing on threat modeling and risk assessment specific to autonomous vehicle operations. Their approach includes developing standardized security metrics and benchmarks for fleet operations, implementing continuous monitoring systems that can adapt to evolving threat landscapes, and creating incident response protocols tailored to autonomous logistics scenarios. The framework emphasizes interoperability between different fleet management systems while maintaining security boundaries, and includes machine learning algorithms for predictive threat analysis and automated security policy updates based on emerging attack patterns.
Strengths: Deep expertise in cybersecurity frameworks and government-grade security standards with strong research foundation. Weaknesses: Solutions may be over-engineered for commercial applications and require significant customization for private sector deployment.
Core Innovations in Autonomous Fleet Cyber Protection
Cyber security rule authentication system for maritime autonomous surface ship
PatentWO2023158112A1
Innovation
- A cyber security rule certification system that includes a data collection unit, cyber risk evaluation unit, security rule checking unit, and non-conformance checking unit to assess and manage cyber risks across multiple networks, allowing for automated generation of evaluation reports and evidence documents, enabling non-expert crew members to maintain compliance with international cyber security standards.
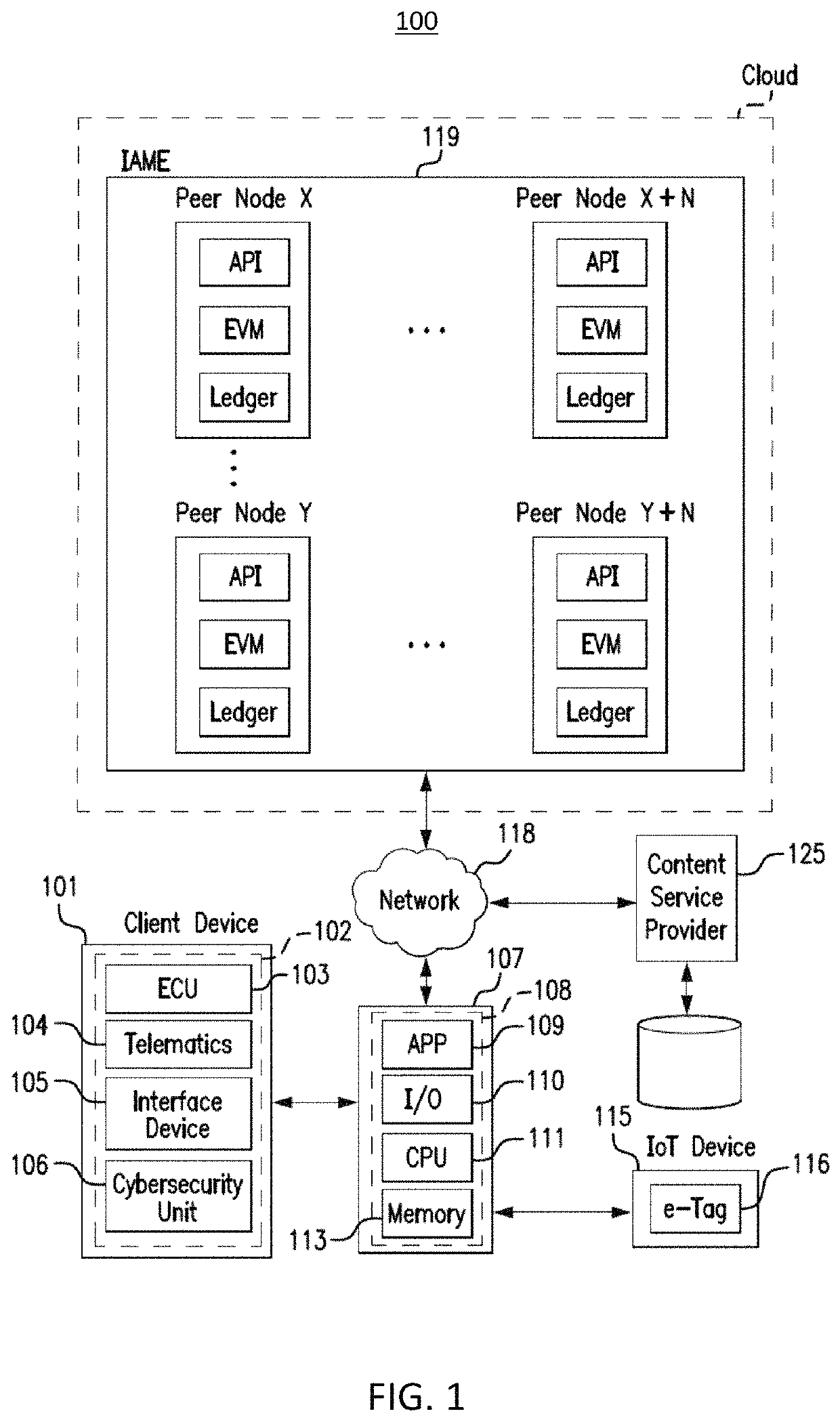
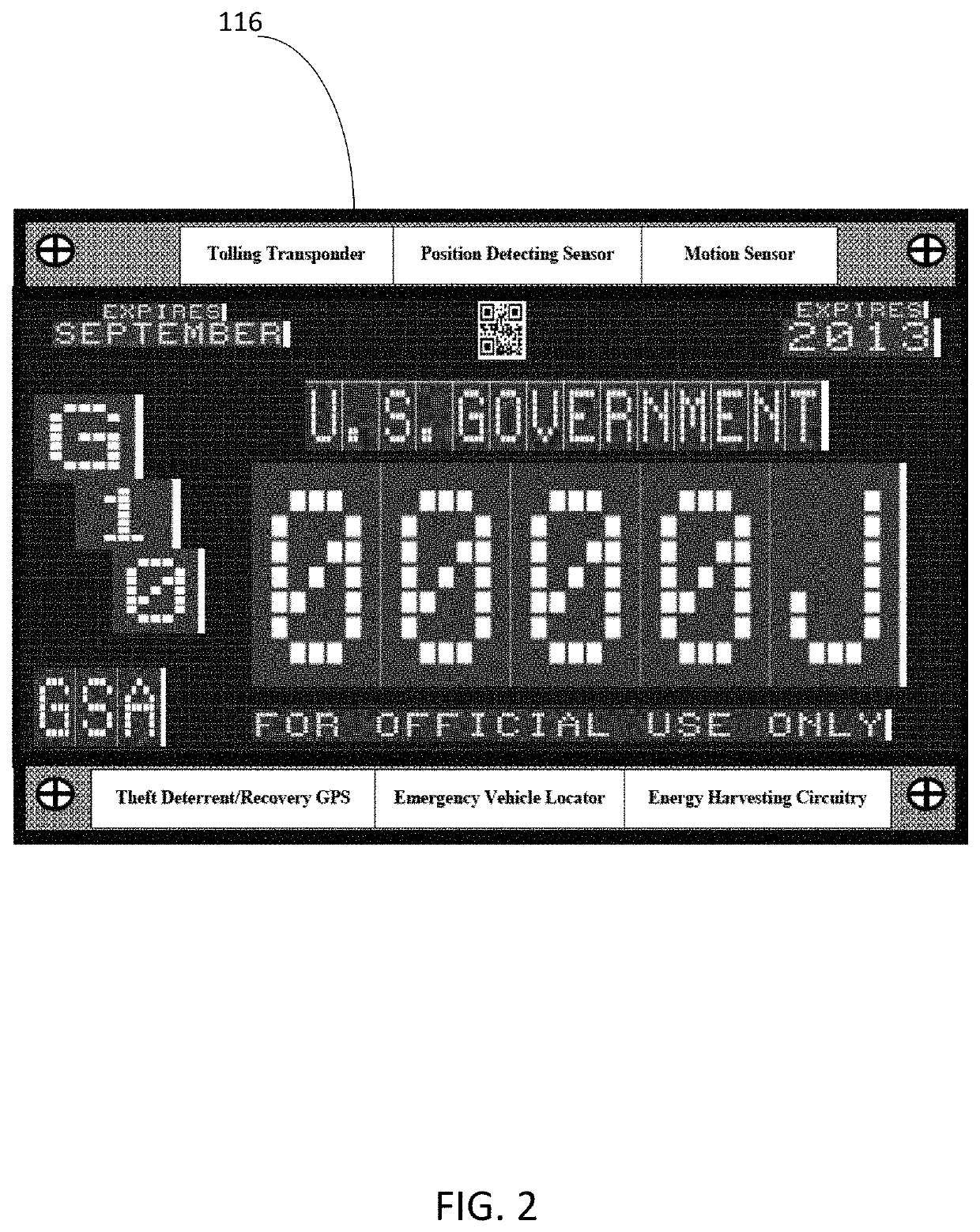
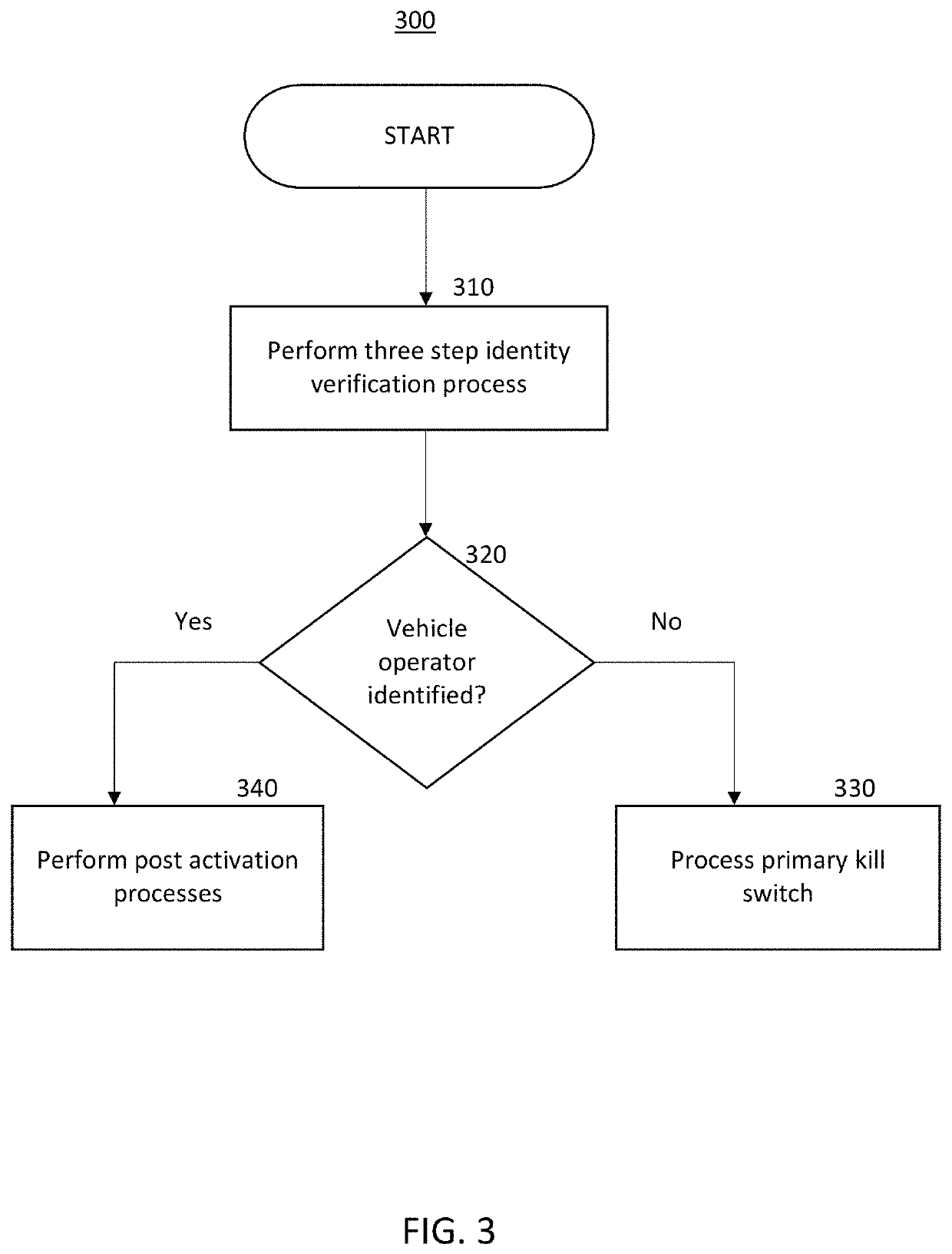
Methods and systems providing cyber defense for electronic identification, vehicles, ancillary vehicle platforms and telematics platforms
PatentActiveUS11057426B2
Innovation
- A computer-implemented method and system utilizing blockchain technology for cyber defense in electronic identification, vehicles, and telematics platforms, which includes identity verification protocols, kill switches, and continuous cyber security monitoring to prevent unauthorized access and detect cyber threats, ensuring only authorized operators can start and operate vehicles, and activating quarantine procedures if threats are detected.
Regulatory Framework for Autonomous Vehicle Cybersecurity
The regulatory framework for autonomous vehicle cybersecurity represents a complex and evolving landscape that directly impacts the optimization of cyber standards for autonomous logistics fleets. Current regulatory approaches vary significantly across jurisdictions, with the European Union leading through the WP.29 regulations, particularly UN Regulation No. 155 on Cybersecurity Management Systems and UN Regulation No. 156 on Software Update Management Systems. These regulations establish mandatory cybersecurity requirements for vehicle manufacturers and operators.
In the United States, the regulatory environment remains more fragmented, with the National Highway Traffic Safety Administration providing voluntary guidance rather than binding requirements. The Federal Motor Carrier Safety Administration has begun developing specific frameworks for commercial autonomous vehicles, recognizing the unique operational characteristics of logistics fleets. This regulatory divergence creates challenges for fleet operators seeking to deploy autonomous logistics systems across multiple jurisdictions.
The International Organization for Standardization has developed ISO/SAE 21434, which provides a comprehensive framework for cybersecurity engineering throughout the vehicle lifecycle. This standard emphasizes risk-based approaches and continuous monitoring, particularly relevant for logistics fleets operating in diverse environments. Additionally, the Society of Automotive Engineers has established SAE J3061, focusing specifically on cybersecurity guidebook for cyber-physical vehicle systems.
Emerging regulatory trends indicate a shift toward performance-based standards rather than prescriptive technical requirements. Regulators are increasingly recognizing that autonomous logistics fleets require adaptive cybersecurity measures capable of responding to evolving threat landscapes. This approach allows for technological innovation while maintaining security objectives through measurable outcomes and continuous assessment protocols.
The regulatory framework also addresses data protection and privacy concerns, particularly relevant for logistics operations that handle sensitive commercial information. The General Data Protection Regulation in Europe and similar privacy laws globally impose additional compliance requirements on autonomous fleet operators, creating intersections between cybersecurity and data governance frameworks.
Future regulatory developments are expected to focus on cross-border harmonization, real-time threat response requirements, and enhanced incident reporting mechanisms. These evolving frameworks will significantly influence how autonomous logistics fleets implement and optimize their cybersecurity standards to ensure compliance while maintaining operational efficiency.
In the United States, the regulatory environment remains more fragmented, with the National Highway Traffic Safety Administration providing voluntary guidance rather than binding requirements. The Federal Motor Carrier Safety Administration has begun developing specific frameworks for commercial autonomous vehicles, recognizing the unique operational characteristics of logistics fleets. This regulatory divergence creates challenges for fleet operators seeking to deploy autonomous logistics systems across multiple jurisdictions.
The International Organization for Standardization has developed ISO/SAE 21434, which provides a comprehensive framework for cybersecurity engineering throughout the vehicle lifecycle. This standard emphasizes risk-based approaches and continuous monitoring, particularly relevant for logistics fleets operating in diverse environments. Additionally, the Society of Automotive Engineers has established SAE J3061, focusing specifically on cybersecurity guidebook for cyber-physical vehicle systems.
Emerging regulatory trends indicate a shift toward performance-based standards rather than prescriptive technical requirements. Regulators are increasingly recognizing that autonomous logistics fleets require adaptive cybersecurity measures capable of responding to evolving threat landscapes. This approach allows for technological innovation while maintaining security objectives through measurable outcomes and continuous assessment protocols.
The regulatory framework also addresses data protection and privacy concerns, particularly relevant for logistics operations that handle sensitive commercial information. The General Data Protection Regulation in Europe and similar privacy laws globally impose additional compliance requirements on autonomous fleet operators, creating intersections between cybersecurity and data governance frameworks.
Future regulatory developments are expected to focus on cross-border harmonization, real-time threat response requirements, and enhanced incident reporting mechanisms. These evolving frameworks will significantly influence how autonomous logistics fleets implement and optimize their cybersecurity standards to ensure compliance while maintaining operational efficiency.
Risk Assessment and Compliance in Autonomous Logistics
Risk assessment in autonomous logistics represents a multifaceted challenge that encompasses cybersecurity vulnerabilities, operational safety concerns, and regulatory compliance requirements. The interconnected nature of autonomous fleet systems creates complex risk profiles where traditional assessment methodologies must be enhanced to address emerging threats. Cybersecurity risks include potential system breaches, data manipulation, communication interference, and unauthorized access to fleet management systems. These vulnerabilities can cascade through entire logistics networks, affecting multiple vehicles simultaneously and compromising operational integrity.
Operational risk assessment requires continuous monitoring of vehicle performance, environmental conditions, and system reliability metrics. Autonomous logistics fleets must implement real-time risk evaluation frameworks that can dynamically adjust operational parameters based on changing conditions. This includes assessing risks related to sensor failures, communication disruptions, weather impacts, and unexpected obstacles. The assessment framework must integrate predictive analytics to anticipate potential failure modes and implement preventive measures before critical incidents occur.
Compliance frameworks for autonomous logistics are evolving rapidly as regulatory bodies worldwide develop standards specific to unmanned vehicle operations. Current compliance requirements vary significantly across jurisdictions, creating challenges for fleet operators managing cross-border logistics operations. Key compliance areas include vehicle certification, operator licensing, insurance requirements, data protection regulations, and environmental impact assessments. Fleet operators must maintain comprehensive documentation systems to demonstrate adherence to applicable regulations and standards.
Regulatory compliance extends beyond basic operational requirements to encompass cybersecurity standards, data privacy protection, and cross-border transportation regulations. The General Data Protection Regulation and similar privacy frameworks impose strict requirements on data collection, processing, and storage practices. Autonomous logistics systems must implement privacy-by-design principles and maintain audit trails for all data handling activities.
Emerging compliance frameworks are incorporating risk-based approaches that require continuous assessment and adaptation. These frameworks emphasize the importance of establishing robust governance structures, implementing comprehensive risk management processes, and maintaining transparent reporting mechanisms. Fleet operators must develop integrated compliance management systems that can adapt to evolving regulatory requirements while maintaining operational efficiency and cost-effectiveness in their autonomous logistics operations.
Operational risk assessment requires continuous monitoring of vehicle performance, environmental conditions, and system reliability metrics. Autonomous logistics fleets must implement real-time risk evaluation frameworks that can dynamically adjust operational parameters based on changing conditions. This includes assessing risks related to sensor failures, communication disruptions, weather impacts, and unexpected obstacles. The assessment framework must integrate predictive analytics to anticipate potential failure modes and implement preventive measures before critical incidents occur.
Compliance frameworks for autonomous logistics are evolving rapidly as regulatory bodies worldwide develop standards specific to unmanned vehicle operations. Current compliance requirements vary significantly across jurisdictions, creating challenges for fleet operators managing cross-border logistics operations. Key compliance areas include vehicle certification, operator licensing, insurance requirements, data protection regulations, and environmental impact assessments. Fleet operators must maintain comprehensive documentation systems to demonstrate adherence to applicable regulations and standards.
Regulatory compliance extends beyond basic operational requirements to encompass cybersecurity standards, data privacy protection, and cross-border transportation regulations. The General Data Protection Regulation and similar privacy frameworks impose strict requirements on data collection, processing, and storage practices. Autonomous logistics systems must implement privacy-by-design principles and maintain audit trails for all data handling activities.
Emerging compliance frameworks are incorporating risk-based approaches that require continuous assessment and adaptation. These frameworks emphasize the importance of establishing robust governance structures, implementing comprehensive risk management processes, and maintaining transparent reporting mechanisms. Fleet operators must develop integrated compliance management systems that can adapt to evolving regulatory requirements while maintaining operational efficiency and cost-effectiveness in their autonomous logistics operations.
Unlock deeper insights with PatSnap Eureka Quick Research — get a full tech report to explore trends and direct your research. Try now!
Generate Your Research Report Instantly with AI Agent
Supercharge your innovation with PatSnap Eureka AI Agent Platform!