Best Practices for Access Control Audit Trails
FEB 27, 20269 MIN READ
Generate Your Research Report Instantly with AI Agent
PatSnap Eureka helps you evaluate technical feasibility & market potential.
Access Control Audit Evolution and Security Goals
Access control audit trails have undergone significant evolution since the early days of computing, transforming from simple log files to sophisticated security monitoring systems. Initially, audit mechanisms were primarily designed for system administration purposes, focusing on basic user authentication and file access logging. These early implementations were reactive in nature, serving mainly as forensic tools after security incidents occurred.
The emergence of regulatory compliance requirements in the 1990s and 2000s marked a pivotal shift in audit trail development. Standards such as SOX, HIPAA, and PCI-DSS mandated comprehensive logging and monitoring capabilities, driving organizations to implement more robust audit systems. This period witnessed the transition from passive logging to active monitoring, with real-time alerting mechanisms becoming standard practice.
Modern access control audit systems have evolved into proactive security tools that leverage advanced analytics and machine learning algorithms. Contemporary implementations focus on behavioral analysis, anomaly detection, and predictive threat modeling. The integration of artificial intelligence has enabled systems to identify subtle patterns indicative of insider threats or compromised accounts that traditional rule-based systems might miss.
The primary security goals of access control audit trails encompass multiple dimensions of organizational protection. Deterrence represents a fundamental objective, as comprehensive logging creates psychological barriers against unauthorized activities. When users understand that their actions are monitored and recorded, they are significantly less likely to engage in malicious behavior or policy violations.
Detection capabilities form another critical security goal, enabling organizations to identify unauthorized access attempts, privilege escalation, and data exfiltration activities in real-time or near real-time. Advanced audit systems can correlate events across multiple systems and timeframes, revealing complex attack patterns that might otherwise remain undetected.
Forensic investigation support constitutes an essential objective, providing detailed evidence trails for incident response and legal proceedings. Comprehensive audit logs enable security teams to reconstruct attack sequences, determine the scope of breaches, and identify affected resources. This capability is crucial for both internal investigations and regulatory reporting requirements.
Compliance demonstration has become increasingly important as organizations face growing regulatory scrutiny. Audit trails serve as evidence of due diligence in implementing security controls and maintaining data protection standards. They provide auditors and regulators with verifiable proof of access control effectiveness and policy adherence.
The evolution toward zero-trust architectures has further refined security goals, emphasizing continuous verification and least-privilege access principles. Modern audit systems support dynamic risk assessment, enabling adaptive security policies based on user behavior, device characteristics, and environmental factors.
The emergence of regulatory compliance requirements in the 1990s and 2000s marked a pivotal shift in audit trail development. Standards such as SOX, HIPAA, and PCI-DSS mandated comprehensive logging and monitoring capabilities, driving organizations to implement more robust audit systems. This period witnessed the transition from passive logging to active monitoring, with real-time alerting mechanisms becoming standard practice.
Modern access control audit systems have evolved into proactive security tools that leverage advanced analytics and machine learning algorithms. Contemporary implementations focus on behavioral analysis, anomaly detection, and predictive threat modeling. The integration of artificial intelligence has enabled systems to identify subtle patterns indicative of insider threats or compromised accounts that traditional rule-based systems might miss.
The primary security goals of access control audit trails encompass multiple dimensions of organizational protection. Deterrence represents a fundamental objective, as comprehensive logging creates psychological barriers against unauthorized activities. When users understand that their actions are monitored and recorded, they are significantly less likely to engage in malicious behavior or policy violations.
Detection capabilities form another critical security goal, enabling organizations to identify unauthorized access attempts, privilege escalation, and data exfiltration activities in real-time or near real-time. Advanced audit systems can correlate events across multiple systems and timeframes, revealing complex attack patterns that might otherwise remain undetected.
Forensic investigation support constitutes an essential objective, providing detailed evidence trails for incident response and legal proceedings. Comprehensive audit logs enable security teams to reconstruct attack sequences, determine the scope of breaches, and identify affected resources. This capability is crucial for both internal investigations and regulatory reporting requirements.
Compliance demonstration has become increasingly important as organizations face growing regulatory scrutiny. Audit trails serve as evidence of due diligence in implementing security controls and maintaining data protection standards. They provide auditors and regulators with verifiable proof of access control effectiveness and policy adherence.
The evolution toward zero-trust architectures has further refined security goals, emphasizing continuous verification and least-privilege access principles. Modern audit systems support dynamic risk assessment, enabling adaptive security policies based on user behavior, device characteristics, and environmental factors.
Market Demand for Comprehensive Audit Trail Solutions
The market demand for comprehensive audit trail solutions has experienced substantial growth driven by escalating cybersecurity threats and increasingly stringent regulatory requirements across industries. Organizations worldwide are recognizing that traditional access control mechanisms alone are insufficient to meet modern security challenges, creating a pressing need for robust audit trail capabilities that provide complete visibility into user activities and system access patterns.
Financial services sector represents one of the most significant demand drivers, where institutions must comply with regulations such as SOX, PCI-DSS, and Basel III. These organizations require audit trail solutions that can track every access attempt, modification, and administrative action across their complex IT infrastructures. The healthcare industry similarly demonstrates strong demand due to HIPAA compliance requirements, necessitating detailed logging of patient data access and healthcare provider activities.
Government agencies and defense contractors constitute another major market segment, driven by requirements for security clearance management and classified information protection. These organizations demand audit trail solutions capable of supporting multi-level security classifications and providing forensic-quality evidence for security investigations.
The enterprise market shows increasing adoption of comprehensive audit trail solutions as organizations implement zero-trust security architectures. Companies are seeking solutions that integrate seamlessly with existing identity and access management systems while providing real-time monitoring capabilities and automated compliance reporting features.
Cloud migration trends have further amplified market demand, as organizations require audit trail solutions that span hybrid and multi-cloud environments. The complexity of modern IT infrastructures, including containerized applications and microservices architectures, has created demand for solutions capable of providing unified audit trails across diverse technology stacks.
Small and medium enterprises represent an emerging market segment, driven by cyber insurance requirements and supply chain security mandates from larger partners. These organizations seek cost-effective audit trail solutions that provide enterprise-grade capabilities without requiring extensive technical expertise for implementation and management.
The market also shows growing demand for artificial intelligence and machine learning capabilities within audit trail solutions, enabling automated anomaly detection and behavioral analysis to identify potential security threats proactively.
Financial services sector represents one of the most significant demand drivers, where institutions must comply with regulations such as SOX, PCI-DSS, and Basel III. These organizations require audit trail solutions that can track every access attempt, modification, and administrative action across their complex IT infrastructures. The healthcare industry similarly demonstrates strong demand due to HIPAA compliance requirements, necessitating detailed logging of patient data access and healthcare provider activities.
Government agencies and defense contractors constitute another major market segment, driven by requirements for security clearance management and classified information protection. These organizations demand audit trail solutions capable of supporting multi-level security classifications and providing forensic-quality evidence for security investigations.
The enterprise market shows increasing adoption of comprehensive audit trail solutions as organizations implement zero-trust security architectures. Companies are seeking solutions that integrate seamlessly with existing identity and access management systems while providing real-time monitoring capabilities and automated compliance reporting features.
Cloud migration trends have further amplified market demand, as organizations require audit trail solutions that span hybrid and multi-cloud environments. The complexity of modern IT infrastructures, including containerized applications and microservices architectures, has created demand for solutions capable of providing unified audit trails across diverse technology stacks.
Small and medium enterprises represent an emerging market segment, driven by cyber insurance requirements and supply chain security mandates from larger partners. These organizations seek cost-effective audit trail solutions that provide enterprise-grade capabilities without requiring extensive technical expertise for implementation and management.
The market also shows growing demand for artificial intelligence and machine learning capabilities within audit trail solutions, enabling automated anomaly detection and behavioral analysis to identify potential security threats proactively.
Current State and Challenges in Access Control Auditing
Access control auditing currently operates within a fragmented landscape where organizations struggle to maintain comprehensive visibility across their diverse IT environments. Traditional audit systems primarily focus on authentication events and basic access logging, often missing critical authorization decisions and contextual information that would enable meaningful security analysis. Most enterprises rely on disparate logging mechanisms across different systems, creating silos of audit data that resist unified analysis and correlation.
The predominant approach involves collecting raw access logs from various sources including directory services, application servers, databases, and network devices. However, these logs frequently lack standardization in format, timestamp precision, and semantic meaning, making cross-system correlation extremely challenging. Many organizations find themselves drowning in audit data volume while simultaneously lacking actionable insights about actual security posture and access patterns.
Current audit trail implementations face significant scalability constraints as enterprise environments continue expanding. Cloud migration has introduced additional complexity layers, with hybrid architectures requiring audit trail synchronization across on-premises and cloud-based identity providers. The emergence of microservices architectures and API-driven interactions has exponentially increased the volume and granularity of access events that require monitoring and analysis.
Data retention and storage costs represent major operational challenges, particularly for organizations subject to compliance requirements demanding extended audit trail preservation. Traditional database-centric storage approaches struggle with the write-heavy nature of audit logging while maintaining query performance for investigative activities. Real-time analysis capabilities remain limited, with most organizations relying on batch processing that introduces dangerous delays in threat detection.
Integration complexity continues plaguing audit trail implementations, as legacy systems often lack modern logging APIs or standardized event formats. Organizations frequently encounter gaps in audit coverage where critical access decisions occur outside monitored boundaries. The absence of unified identity correlation across federated environments creates blind spots where malicious actors can exploit inconsistent audit coverage to mask unauthorized activities.
The predominant approach involves collecting raw access logs from various sources including directory services, application servers, databases, and network devices. However, these logs frequently lack standardization in format, timestamp precision, and semantic meaning, making cross-system correlation extremely challenging. Many organizations find themselves drowning in audit data volume while simultaneously lacking actionable insights about actual security posture and access patterns.
Current audit trail implementations face significant scalability constraints as enterprise environments continue expanding. Cloud migration has introduced additional complexity layers, with hybrid architectures requiring audit trail synchronization across on-premises and cloud-based identity providers. The emergence of microservices architectures and API-driven interactions has exponentially increased the volume and granularity of access events that require monitoring and analysis.
Data retention and storage costs represent major operational challenges, particularly for organizations subject to compliance requirements demanding extended audit trail preservation. Traditional database-centric storage approaches struggle with the write-heavy nature of audit logging while maintaining query performance for investigative activities. Real-time analysis capabilities remain limited, with most organizations relying on batch processing that introduces dangerous delays in threat detection.
Integration complexity continues plaguing audit trail implementations, as legacy systems often lack modern logging APIs or standardized event formats. Organizations frequently encounter gaps in audit coverage where critical access decisions occur outside monitored boundaries. The absence of unified identity correlation across federated environments creates blind spots where malicious actors can exploit inconsistent audit coverage to mask unauthorized activities.
Existing Best Practices for Audit Trail Implementation
01 Audit trail generation and logging mechanisms
Systems and methods for generating comprehensive audit trails that record access control events, including user authentication attempts, resource access requests, and system modifications. These mechanisms capture detailed information such as timestamps, user identities, accessed resources, and action types. The audit logs are stored in secure repositories with tamper-proof features to ensure data integrity and provide reliable records for security analysis and compliance purposes.- Audit trail generation and logging mechanisms: Systems and methods for generating comprehensive audit trails that record access control events, including user authentication attempts, resource access requests, and permission changes. These mechanisms capture detailed information such as timestamps, user identities, accessed resources, and action types. The audit logs are stored in secure repositories and can be configured to track various levels of granularity depending on security requirements and compliance needs.
- Audit trail analysis and anomaly detection: Technologies for analyzing audit trail data to identify suspicious patterns, unauthorized access attempts, and security violations. These systems employ various techniques including pattern recognition, behavioral analysis, and machine learning algorithms to detect anomalies in access control activities. The analysis can trigger alerts when unusual activities are detected, enabling proactive security responses and forensic investigations.
- Secure storage and integrity protection of audit records: Methods for ensuring the integrity and tamper-proof storage of audit trail records. These approaches utilize cryptographic techniques, digital signatures, and blockchain-based technologies to prevent unauthorized modification or deletion of audit logs. The systems implement secure storage mechanisms that maintain chain of custody and provide verifiable proof of audit record authenticity for compliance and legal purposes.
- Real-time audit monitoring and reporting: Solutions for real-time monitoring of access control events and generation of audit reports. These systems provide dashboards and visualization tools that enable security administrators to monitor ongoing access activities, generate compliance reports, and track security metrics. The reporting capabilities support various formats and can be customized to meet different regulatory requirements and organizational policies.
- Distributed and centralized audit trail management: Architectures for managing audit trails across distributed systems and centralized platforms. These frameworks enable collection, aggregation, and correlation of audit data from multiple sources including cloud environments, network devices, and applications. The systems support scalable storage solutions and provide unified interfaces for querying and analyzing audit information across enterprise infrastructures.
02 Real-time monitoring and alert systems for access control
Technologies that enable real-time monitoring of access control activities and generate alerts when suspicious or unauthorized access attempts are detected. These systems analyze audit trail data in real-time to identify anomalous patterns, policy violations, or security breaches. Automated notification mechanisms alert administrators immediately when predefined security thresholds are exceeded, enabling rapid response to potential security incidents.Expand Specific Solutions03 Audit trail analysis and reporting tools
Advanced analytical tools and reporting frameworks designed to process and visualize audit trail data for access control systems. These solutions provide capabilities for searching, filtering, and correlating audit records to identify security trends, compliance gaps, and user behavior patterns. The tools generate comprehensive reports that support forensic investigations, compliance audits, and security assessments by presenting audit data in meaningful and actionable formats.Expand Specific Solutions04 Secure storage and retention of audit records
Methods and systems for securely storing audit trail data with appropriate retention policies and protection mechanisms. These approaches implement encryption, access controls, and backup strategies to prevent unauthorized modification or deletion of audit records. The solutions ensure long-term preservation of audit data to meet regulatory requirements and support historical analysis, while managing storage resources efficiently through data compression and archival techniques.Expand Specific Solutions05 Integration of audit trails with identity and access management systems
Integrated frameworks that combine audit trail functionality with identity and access management platforms to provide unified visibility into user access activities. These systems correlate audit data with user profiles, roles, and permissions to enable comprehensive access governance. The integration facilitates automated compliance reporting, access certification processes, and risk assessment by linking audit events to identity information and organizational policies.Expand Specific Solutions
Key Players in Access Control and Audit Solutions
The access control audit trails market represents a mature technology sector experiencing steady growth driven by increasing regulatory compliance requirements and cybersecurity concerns. The industry has evolved from basic logging systems to sophisticated AI-powered analytics platforms, with market size expanding significantly across enterprise, government, and critical infrastructure segments. Technology maturity varies considerably among key players, with established giants like IBM, Thales SA, and Huawei Technologies offering comprehensive enterprise-grade solutions with advanced machine learning capabilities. Traditional security specialists such as ASSA ABLOY AB and Johnson Controls (Tyco Fire & Security) provide proven hardware-integrated audit systems, while emerging players like Uptake Technologies and Ping An Technology focus on cloud-native analytics platforms. Infrastructure leaders including State Grid Corp. of China and BNSF Railway demonstrate real-world deployment at massive scale. The competitive landscape shows clear segmentation between legacy system providers, cloud-first innovators, and integrated hardware-software vendors, with increasing convergence toward AI-enhanced predictive analytics and real-time threat detection capabilities across all market segments.
ASSA ABLOY AB
Technical Solution: ASSA ABLOY's access control audit trail solution is built into their comprehensive physical and logical access management systems. Their approach includes detailed logging of door access events, biometric authentication records, and integration with video surveillance systems for complete audit trails. The system provides real-time monitoring dashboards, automated compliance reporting, and mobile access management with full audit capabilities. Their solution emphasizes privacy protection while maintaining comprehensive security logging for both physical and digital access points.
Strengths: Leading physical access control expertise, comprehensive integration capabilities, strong privacy protection features. Weaknesses: Primarily focused on physical access rather than comprehensive IT security, limited cybersecurity analytics capabilities compared to pure IT security vendors.
International Business Machines Corp.
Technical Solution: IBM implements comprehensive access control audit trails through its Security QRadar SIEM platform, which provides real-time monitoring and logging of all access events across enterprise systems. The solution features automated compliance reporting, behavioral analytics for anomaly detection, and centralized log management with tamper-proof storage mechanisms. IBM's approach includes role-based access control (RBAC) integration, privileged access management (PAM) auditing, and machine learning algorithms that can identify suspicious access patterns and potential security breaches in real-time.
Strengths: Advanced AI-driven analytics, comprehensive compliance framework support, scalable enterprise architecture. Weaknesses: High implementation complexity, significant resource requirements, expensive licensing costs.
Core Innovations in Access Control Audit Technologies
System and method for configuring and viewing audit trails in an information network
PatentInactiveUS7574501B2
Innovation
- An audit trail system that allows users to create and manage audit trails without interacting with the database structure, enabling tracking of specific operations (updates, creations, deletions, and copies) and storing these trails locally or centrally, while also allowing administrators to restrict access based on employee identifiers and responsibilities.
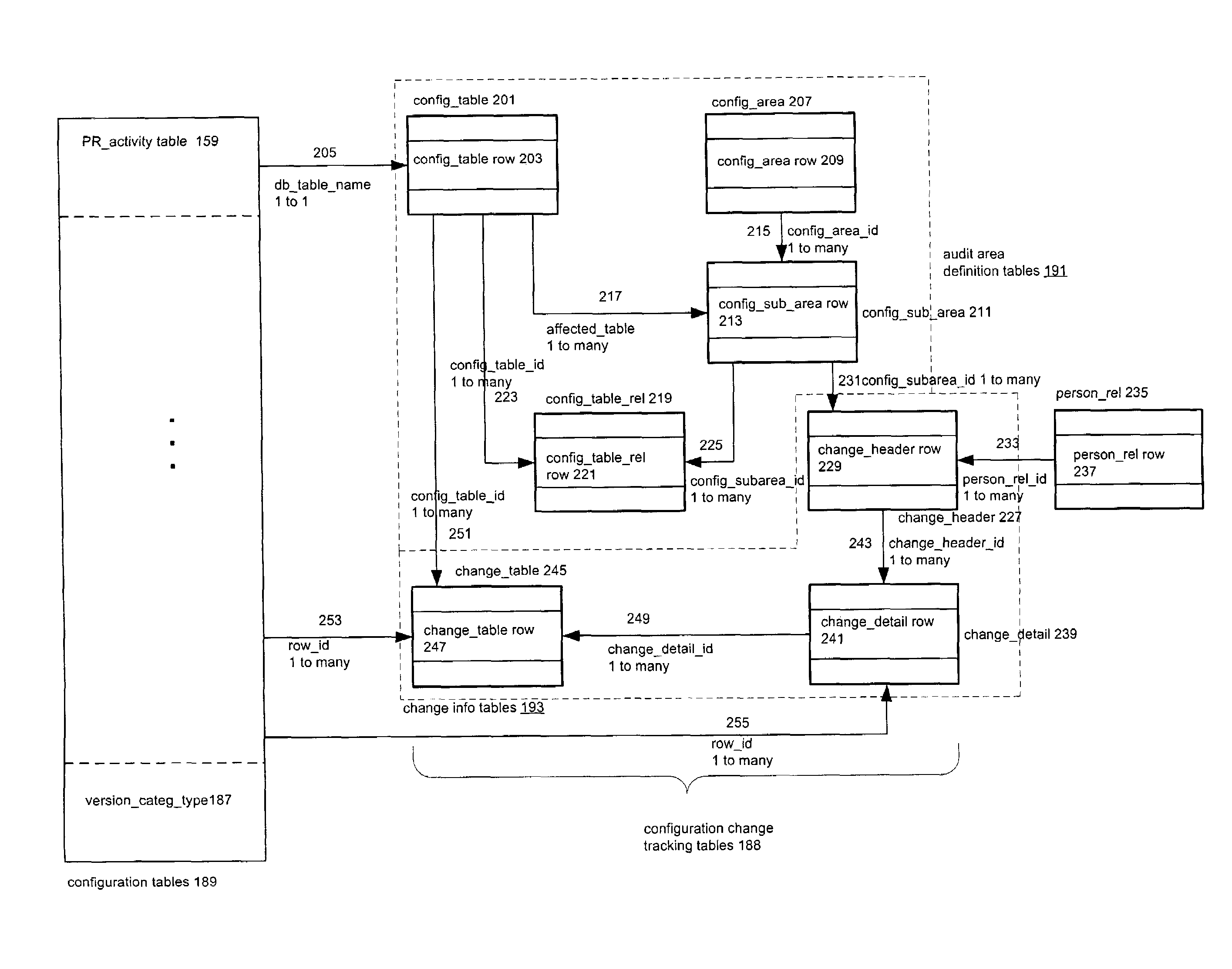
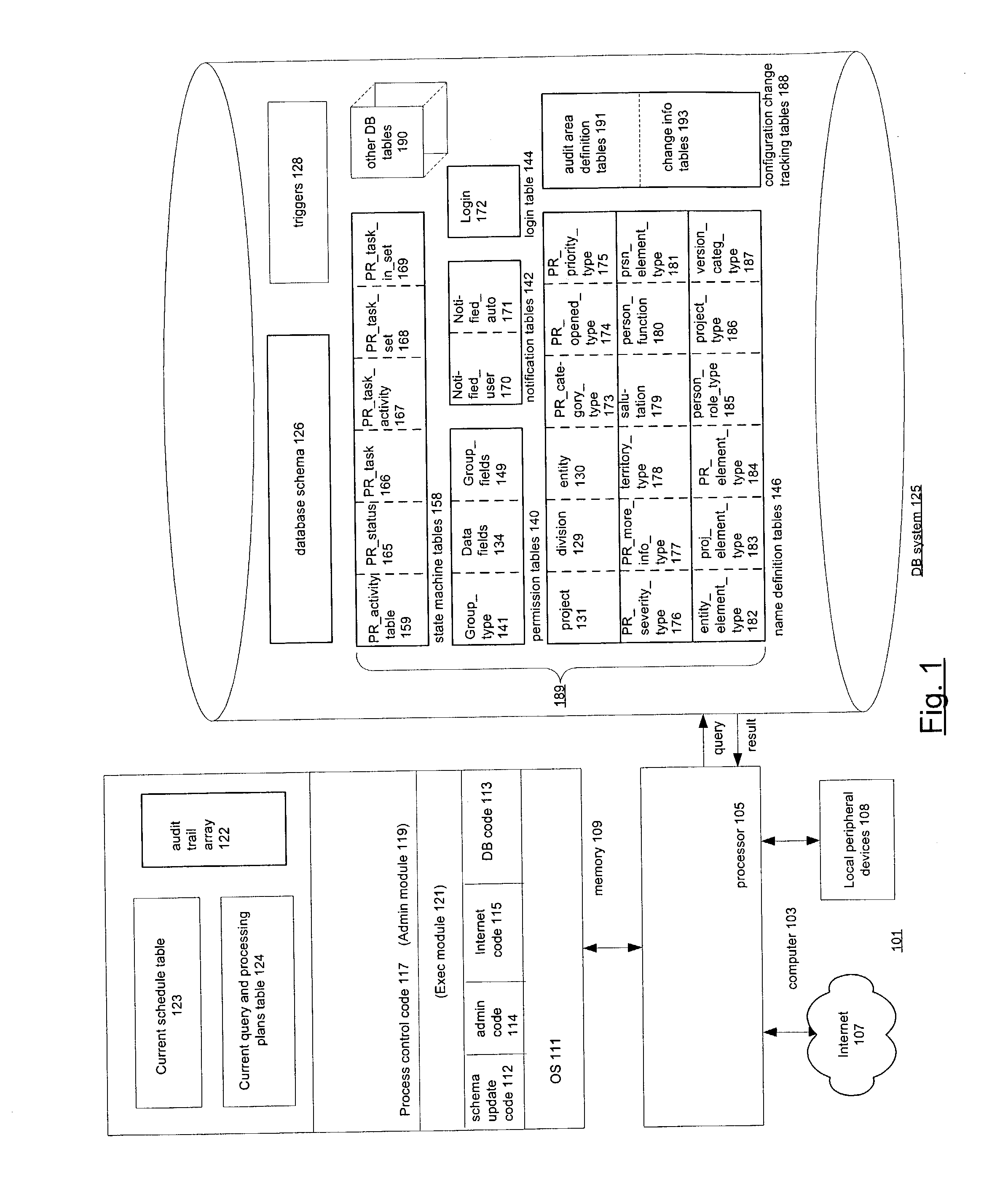
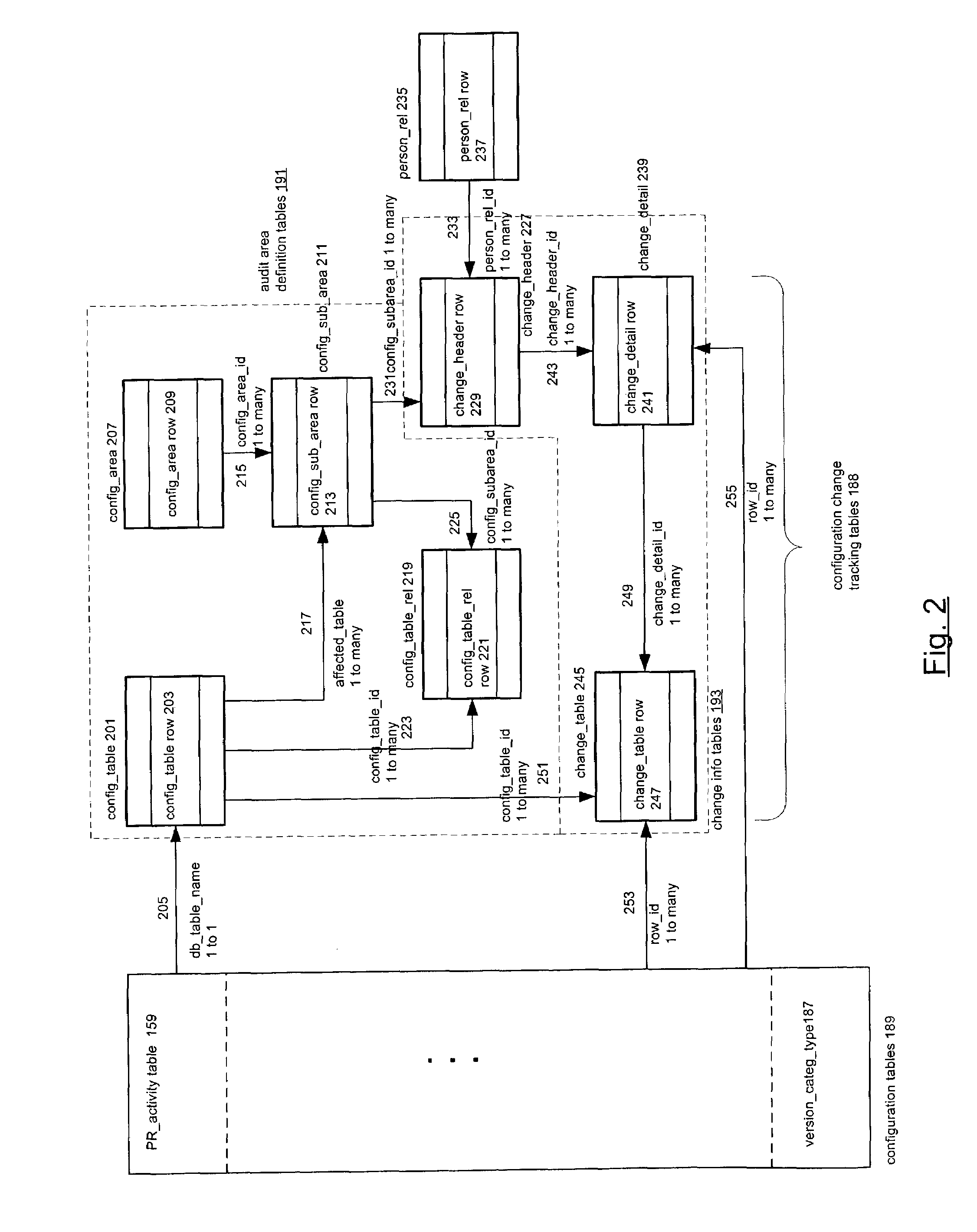
Techniques for providing audit trails of configuration changes
PatentInactiveUS7409398B1
Innovation
- A configurable system with a database management system that includes configuration tables, change recording tables, and a graphical user interface for specifying queries, allowing users to track changes, record user identity, and time stamps, and constrain queries by user or time period.
Compliance Requirements for Access Control Auditing
Access control auditing operates within a complex regulatory landscape that demands strict adherence to multiple compliance frameworks. Organizations must navigate requirements from standards such as SOX, HIPAA, PCI DSS, GDPR, and ISO 27001, each imposing specific mandates for audit trail maintenance and reporting. These regulations typically require comprehensive logging of all access attempts, successful authentications, privilege escalations, and administrative actions, with retention periods ranging from three to seven years depending on the applicable framework.
The financial services sector faces particularly stringent requirements under regulations like SOX Section 404, which mandates detailed documentation of internal controls over financial reporting. This includes maintaining complete audit trails for all system access that could impact financial data integrity. Similarly, healthcare organizations must comply with HIPAA's audit trail requirements, which specify that all access to protected health information must be logged with sufficient detail to identify the user, timestamp, and nature of the access.
Data protection regulations such as GDPR introduce additional complexity by requiring organizations to demonstrate accountability and provide detailed access logs upon request from data subjects or regulatory authorities. The regulation's "right to audit" provisions necessitate maintaining granular records of data processing activities, including automated decision-making processes and data transfers. Organizations must ensure their audit trails can support data subject access requests and regulatory investigations within specified timeframes.
Industry-specific compliance frameworks impose unique technical requirements for audit trail implementation. PCI DSS mandates real-time monitoring and alerting for payment card data access, requiring automated correlation of events across multiple systems. Federal agencies must comply with FISMA requirements, which specify continuous monitoring capabilities and integration with security information and event management systems.
Cross-border data transfer regulations create additional compliance challenges, particularly for multinational organizations. Audit trails must demonstrate compliance with data localization requirements and provide evidence of appropriate safeguards for international data transfers. This often requires implementing region-specific logging configurations and ensuring audit data sovereignty aligns with applicable jurisdictions.
The evolving regulatory landscape continues to introduce new requirements, with emerging frameworks focusing on artificial intelligence governance and algorithmic accountability. Organizations must design flexible audit trail architectures capable of adapting to future compliance mandates while maintaining backward compatibility with existing regulatory requirements.
The financial services sector faces particularly stringent requirements under regulations like SOX Section 404, which mandates detailed documentation of internal controls over financial reporting. This includes maintaining complete audit trails for all system access that could impact financial data integrity. Similarly, healthcare organizations must comply with HIPAA's audit trail requirements, which specify that all access to protected health information must be logged with sufficient detail to identify the user, timestamp, and nature of the access.
Data protection regulations such as GDPR introduce additional complexity by requiring organizations to demonstrate accountability and provide detailed access logs upon request from data subjects or regulatory authorities. The regulation's "right to audit" provisions necessitate maintaining granular records of data processing activities, including automated decision-making processes and data transfers. Organizations must ensure their audit trails can support data subject access requests and regulatory investigations within specified timeframes.
Industry-specific compliance frameworks impose unique technical requirements for audit trail implementation. PCI DSS mandates real-time monitoring and alerting for payment card data access, requiring automated correlation of events across multiple systems. Federal agencies must comply with FISMA requirements, which specify continuous monitoring capabilities and integration with security information and event management systems.
Cross-border data transfer regulations create additional compliance challenges, particularly for multinational organizations. Audit trails must demonstrate compliance with data localization requirements and provide evidence of appropriate safeguards for international data transfers. This often requires implementing region-specific logging configurations and ensuring audit data sovereignty aligns with applicable jurisdictions.
The evolving regulatory landscape continues to introduce new requirements, with emerging frameworks focusing on artificial intelligence governance and algorithmic accountability. Organizations must design flexible audit trail architectures capable of adapting to future compliance mandates while maintaining backward compatibility with existing regulatory requirements.
Privacy Protection in Access Control Audit Systems
Privacy protection in access control audit systems represents a critical balance between security monitoring requirements and individual privacy rights. Modern audit systems must implement sophisticated privacy-preserving mechanisms while maintaining the integrity and effectiveness of security monitoring capabilities. This challenge has become increasingly complex as organizations face stricter regulatory requirements and growing privacy concerns from stakeholders.
The fundamental privacy challenge in audit systems stems from the inherent tension between comprehensive logging and data minimization principles. Traditional audit trails often capture extensive user behavior data, including access patterns, resource usage, and temporal activities. However, privacy regulations such as GDPR and CCPA mandate that organizations limit data collection to what is strictly necessary for legitimate business purposes. This requires audit systems to implement intelligent filtering mechanisms that distinguish between security-relevant events and potentially invasive personal data collection.
Data anonymization and pseudonymization techniques have emerged as cornerstone approaches for privacy protection in audit systems. Advanced cryptographic methods enable the creation of audit records that preserve analytical value while obscuring individual identities. Hash-based pseudonymization allows for pattern analysis and anomaly detection without exposing actual user identities. Additionally, differential privacy mechanisms introduce controlled noise into audit data, preventing individual identification while maintaining statistical accuracy for security analysis.
Role-based access controls for audit data itself constitute another critical privacy protection layer. Not all security personnel require access to complete audit trails, and implementing granular permissions ensures that sensitive user information is only accessible to authorized individuals with legitimate operational needs. This approach includes implementing separate access levels for different types of audit data, from high-level security summaries to detailed individual activity logs.
Temporal data retention policies play a crucial role in privacy protection by automatically purging audit records after predetermined periods. These policies must balance legal compliance requirements, security investigation needs, and privacy protection goals. Advanced systems implement tiered retention strategies where detailed personal data is purged more quickly than aggregated security metrics, allowing for long-term trend analysis while minimizing individual privacy exposure.
Emerging privacy-preserving technologies such as homomorphic encryption and secure multi-party computation offer promising solutions for audit systems. These technologies enable security analysis on encrypted audit data without requiring decryption, providing unprecedented privacy protection while maintaining analytical capabilities. However, implementation complexity and computational overhead remain significant challenges for widespread adoption in enterprise environments.
The fundamental privacy challenge in audit systems stems from the inherent tension between comprehensive logging and data minimization principles. Traditional audit trails often capture extensive user behavior data, including access patterns, resource usage, and temporal activities. However, privacy regulations such as GDPR and CCPA mandate that organizations limit data collection to what is strictly necessary for legitimate business purposes. This requires audit systems to implement intelligent filtering mechanisms that distinguish between security-relevant events and potentially invasive personal data collection.
Data anonymization and pseudonymization techniques have emerged as cornerstone approaches for privacy protection in audit systems. Advanced cryptographic methods enable the creation of audit records that preserve analytical value while obscuring individual identities. Hash-based pseudonymization allows for pattern analysis and anomaly detection without exposing actual user identities. Additionally, differential privacy mechanisms introduce controlled noise into audit data, preventing individual identification while maintaining statistical accuracy for security analysis.
Role-based access controls for audit data itself constitute another critical privacy protection layer. Not all security personnel require access to complete audit trails, and implementing granular permissions ensures that sensitive user information is only accessible to authorized individuals with legitimate operational needs. This approach includes implementing separate access levels for different types of audit data, from high-level security summaries to detailed individual activity logs.
Temporal data retention policies play a crucial role in privacy protection by automatically purging audit records after predetermined periods. These policies must balance legal compliance requirements, security investigation needs, and privacy protection goals. Advanced systems implement tiered retention strategies where detailed personal data is purged more quickly than aggregated security metrics, allowing for long-term trend analysis while minimizing individual privacy exposure.
Emerging privacy-preserving technologies such as homomorphic encryption and secure multi-party computation offer promising solutions for audit systems. These technologies enable security analysis on encrypted audit data without requiring decryption, providing unprecedented privacy protection while maintaining analytical capabilities. However, implementation complexity and computational overhead remain significant challenges for widespread adoption in enterprise environments.
Unlock deeper insights with PatSnap Eureka Quick Research — get a full tech report to explore trends and direct your research. Try now!
Generate Your Research Report Instantly with AI Agent
Supercharge your innovation with PatSnap Eureka AI Agent Platform!