Enhance Access Control Systems with Multi-Factor Authentication
FEB 27, 20269 MIN READ
Generate Your Research Report Instantly with AI Agent
Patsnap Eureka helps you evaluate technical feasibility & market potential.
Multi-Factor Authentication Evolution and Security Goals
Multi-factor authentication has undergone significant evolution since its inception in the 1960s, transforming from simple password-based systems to sophisticated biometric and behavioral authentication mechanisms. The journey began with basic two-factor authentication combining passwords with physical tokens, progressing through SMS-based verification, hardware security keys, and ultimately reaching today's advanced biometric systems incorporating fingerprint, facial recognition, and voice authentication technologies.
The evolution accelerated dramatically in the 2000s with the widespread adoption of mobile devices, enabling SMS and app-based authentication methods. The 2010s witnessed the emergence of biometric authentication becoming mainstream, while the current decade has introduced behavioral biometrics, risk-based authentication, and AI-driven adaptive security measures that continuously assess user behavior patterns and environmental factors.
Modern MFA systems have evolved beyond traditional static factors to incorporate dynamic elements such as geolocation, device fingerprinting, and contextual analysis. This progression reflects the growing sophistication of cyber threats and the need for more robust security frameworks that balance user convenience with protection effectiveness.
The primary security goal of enhanced access control systems centers on establishing multiple layers of verification to significantly reduce the probability of unauthorized access. Traditional single-factor authentication presents a single point of failure, whereas MFA creates multiple barriers that attackers must overcome simultaneously, exponentially increasing security effectiveness.
Contemporary MFA implementations aim to achieve adaptive security that responds dynamically to risk levels. High-risk scenarios trigger additional authentication factors, while routine access from trusted environments may require fewer verification steps. This approach optimizes both security posture and user experience, addressing the historical tension between robust protection and operational efficiency.
The overarching objective encompasses creating seamless yet secure authentication experiences that protect against diverse threat vectors including credential theft, social engineering, device compromise, and sophisticated phishing attacks. Modern systems target zero-trust architecture principles, where every access request undergoes continuous verification regardless of user location or previous authentication status.
Future security goals focus on achieving passwordless authentication environments, leveraging advanced biometric fusion, and implementing quantum-resistant cryptographic methods to prepare for emerging computational threats while maintaining backward compatibility with existing infrastructure investments.
The evolution accelerated dramatically in the 2000s with the widespread adoption of mobile devices, enabling SMS and app-based authentication methods. The 2010s witnessed the emergence of biometric authentication becoming mainstream, while the current decade has introduced behavioral biometrics, risk-based authentication, and AI-driven adaptive security measures that continuously assess user behavior patterns and environmental factors.
Modern MFA systems have evolved beyond traditional static factors to incorporate dynamic elements such as geolocation, device fingerprinting, and contextual analysis. This progression reflects the growing sophistication of cyber threats and the need for more robust security frameworks that balance user convenience with protection effectiveness.
The primary security goal of enhanced access control systems centers on establishing multiple layers of verification to significantly reduce the probability of unauthorized access. Traditional single-factor authentication presents a single point of failure, whereas MFA creates multiple barriers that attackers must overcome simultaneously, exponentially increasing security effectiveness.
Contemporary MFA implementations aim to achieve adaptive security that responds dynamically to risk levels. High-risk scenarios trigger additional authentication factors, while routine access from trusted environments may require fewer verification steps. This approach optimizes both security posture and user experience, addressing the historical tension between robust protection and operational efficiency.
The overarching objective encompasses creating seamless yet secure authentication experiences that protect against diverse threat vectors including credential theft, social engineering, device compromise, and sophisticated phishing attacks. Modern systems target zero-trust architecture principles, where every access request undergoes continuous verification regardless of user location or previous authentication status.
Future security goals focus on achieving passwordless authentication environments, leveraging advanced biometric fusion, and implementing quantum-resistant cryptographic methods to prepare for emerging computational threats while maintaining backward compatibility with existing infrastructure investments.
Market Demand for Enhanced Access Control Solutions
The global access control market has experienced substantial growth driven by escalating security concerns across multiple sectors. Organizations worldwide are increasingly recognizing the inadequacy of traditional single-factor authentication methods in protecting sensitive assets and data. This recognition has created a robust demand for enhanced access control solutions that incorporate multi-factor authentication capabilities.
Enterprise environments represent the largest demand segment, with corporations seeking comprehensive security frameworks to protect intellectual property, financial data, and operational systems. The rise in remote work arrangements has further amplified this demand, as organizations require secure access mechanisms that can verify user identities regardless of location or device. Financial institutions, healthcare providers, and government agencies demonstrate particularly strong demand due to stringent regulatory compliance requirements.
The healthcare sector exhibits growing demand for enhanced access control systems to protect patient data and comply with regulations such as HIPAA. Medical facilities require solutions that balance security with operational efficiency, enabling healthcare professionals to access critical information quickly while maintaining strict access controls. The integration of electronic health records and connected medical devices has intensified the need for robust authentication mechanisms.
Critical infrastructure sectors, including energy, transportation, and utilities, are driving significant demand for advanced access control solutions. These industries face increasing cyber threats targeting operational technology systems, necessitating multi-layered security approaches that combine physical and logical access controls. The potential consequences of unauthorized access in these sectors create strong economic incentives for implementing comprehensive authentication systems.
Educational institutions represent an emerging demand segment, particularly as campuses digitize operations and expand online learning platforms. Universities and schools require scalable solutions that can accommodate diverse user populations while maintaining appropriate security levels for different access scenarios.
The retail and hospitality industries are increasingly adopting enhanced access control systems to protect customer data and comply with payment card industry standards. These sectors require solutions that can integrate with existing point-of-sale systems while providing seamless user experiences for both employees and customers.
Small and medium-sized enterprises constitute a rapidly growing market segment, driven by increasing awareness of cybersecurity risks and the availability of cloud-based access control solutions. These organizations seek cost-effective implementations that can scale with business growth while providing enterprise-grade security capabilities.
Enterprise environments represent the largest demand segment, with corporations seeking comprehensive security frameworks to protect intellectual property, financial data, and operational systems. The rise in remote work arrangements has further amplified this demand, as organizations require secure access mechanisms that can verify user identities regardless of location or device. Financial institutions, healthcare providers, and government agencies demonstrate particularly strong demand due to stringent regulatory compliance requirements.
The healthcare sector exhibits growing demand for enhanced access control systems to protect patient data and comply with regulations such as HIPAA. Medical facilities require solutions that balance security with operational efficiency, enabling healthcare professionals to access critical information quickly while maintaining strict access controls. The integration of electronic health records and connected medical devices has intensified the need for robust authentication mechanisms.
Critical infrastructure sectors, including energy, transportation, and utilities, are driving significant demand for advanced access control solutions. These industries face increasing cyber threats targeting operational technology systems, necessitating multi-layered security approaches that combine physical and logical access controls. The potential consequences of unauthorized access in these sectors create strong economic incentives for implementing comprehensive authentication systems.
Educational institutions represent an emerging demand segment, particularly as campuses digitize operations and expand online learning platforms. Universities and schools require scalable solutions that can accommodate diverse user populations while maintaining appropriate security levels for different access scenarios.
The retail and hospitality industries are increasingly adopting enhanced access control systems to protect customer data and comply with payment card industry standards. These sectors require solutions that can integrate with existing point-of-sale systems while providing seamless user experiences for both employees and customers.
Small and medium-sized enterprises constitute a rapidly growing market segment, driven by increasing awareness of cybersecurity risks and the availability of cloud-based access control solutions. These organizations seek cost-effective implementations that can scale with business growth while providing enterprise-grade security capabilities.
Current MFA Implementation Challenges and Limitations
Despite the widespread adoption of multi-factor authentication systems, organizations continue to face significant implementation challenges that hinder optimal security outcomes. User experience friction remains one of the most persistent obstacles, as traditional MFA methods often create cumbersome authentication workflows that negatively impact productivity and user satisfaction. Many employees express frustration with time-consuming verification processes, leading to resistance and potential workarounds that compromise security effectiveness.
Integration complexity poses another substantial barrier, particularly for organizations operating legacy systems or heterogeneous IT environments. Existing access control infrastructures frequently lack native MFA capabilities, requiring extensive customization or complete system overhauls. This technical debt creates compatibility issues between different authentication protocols and identity management systems, resulting in fragmented security architectures that are difficult to maintain and monitor effectively.
Scalability limitations become increasingly apparent as organizations expand their digital footprint and remote workforce. Current MFA solutions often struggle to handle peak authentication loads during business hours, causing system slowdowns and authentication failures. The challenge intensifies when supporting diverse device ecosystems and varying network conditions across global operations, where consistent performance becomes difficult to guarantee.
Cost considerations significantly impact MFA deployment strategies, as comprehensive implementations require substantial investments in hardware tokens, mobile device management, and specialized software licenses. Many organizations find themselves balancing security requirements against budget constraints, often resulting in partial implementations that leave critical systems inadequately protected.
Administrative overhead represents a growing concern as MFA systems require continuous management of user enrollments, device registrations, and policy configurations. IT teams frequently struggle with the complexity of managing multiple authentication factors across different user groups while maintaining compliance with evolving regulatory requirements. The lack of standardized management interfaces across vendors further complicates centralized administration efforts.
Recovery and backup authentication mechanisms present ongoing vulnerabilities, as organizations must provide alternative access methods for users who lose devices or encounter technical issues. These fallback procedures often introduce security weaknesses that attackers can exploit, creating a fundamental tension between accessibility and protection that remains difficult to resolve effectively.
Integration complexity poses another substantial barrier, particularly for organizations operating legacy systems or heterogeneous IT environments. Existing access control infrastructures frequently lack native MFA capabilities, requiring extensive customization or complete system overhauls. This technical debt creates compatibility issues between different authentication protocols and identity management systems, resulting in fragmented security architectures that are difficult to maintain and monitor effectively.
Scalability limitations become increasingly apparent as organizations expand their digital footprint and remote workforce. Current MFA solutions often struggle to handle peak authentication loads during business hours, causing system slowdowns and authentication failures. The challenge intensifies when supporting diverse device ecosystems and varying network conditions across global operations, where consistent performance becomes difficult to guarantee.
Cost considerations significantly impact MFA deployment strategies, as comprehensive implementations require substantial investments in hardware tokens, mobile device management, and specialized software licenses. Many organizations find themselves balancing security requirements against budget constraints, often resulting in partial implementations that leave critical systems inadequately protected.
Administrative overhead represents a growing concern as MFA systems require continuous management of user enrollments, device registrations, and policy configurations. IT teams frequently struggle with the complexity of managing multiple authentication factors across different user groups while maintaining compliance with evolving regulatory requirements. The lack of standardized management interfaces across vendors further complicates centralized administration efforts.
Recovery and backup authentication mechanisms present ongoing vulnerabilities, as organizations must provide alternative access methods for users who lose devices or encounter technical issues. These fallback procedures often introduce security weaknesses that attackers can exploit, creating a fundamental tension between accessibility and protection that remains difficult to resolve effectively.
Existing Multi-Factor Authentication Frameworks
01 Biometric-based multi-factor authentication systems
Multi-factor authentication systems can incorporate biometric verification methods such as fingerprint recognition, facial recognition, iris scanning, or voice recognition as one of the authentication factors. These biometric factors provide enhanced security by verifying the unique physical characteristics of users. The biometric data can be combined with other authentication factors like passwords or tokens to create a robust multi-layered security approach. This method significantly reduces the risk of unauthorized access as biometric features are difficult to replicate or steal.- Biometric-based multi-factor authentication systems: Multi-factor authentication systems can incorporate biometric verification methods such as fingerprint recognition, facial recognition, iris scanning, or voice recognition as one of the authentication factors. These biometric factors provide enhanced security by verifying the physical characteristics of users, making it difficult for unauthorized individuals to gain access. The combination of biometric data with other authentication factors like passwords or tokens creates a robust access control mechanism that significantly reduces the risk of unauthorized access.
- Token-based and one-time password authentication: Authentication systems can utilize hardware or software tokens that generate one-time passwords or time-based codes as an additional authentication factor. These tokens provide dynamic credentials that change periodically, making them more secure than static passwords. Users must possess the physical token or have access to the token-generating application on their device, combined with knowledge of their primary credentials, to successfully authenticate and gain access to protected resources.
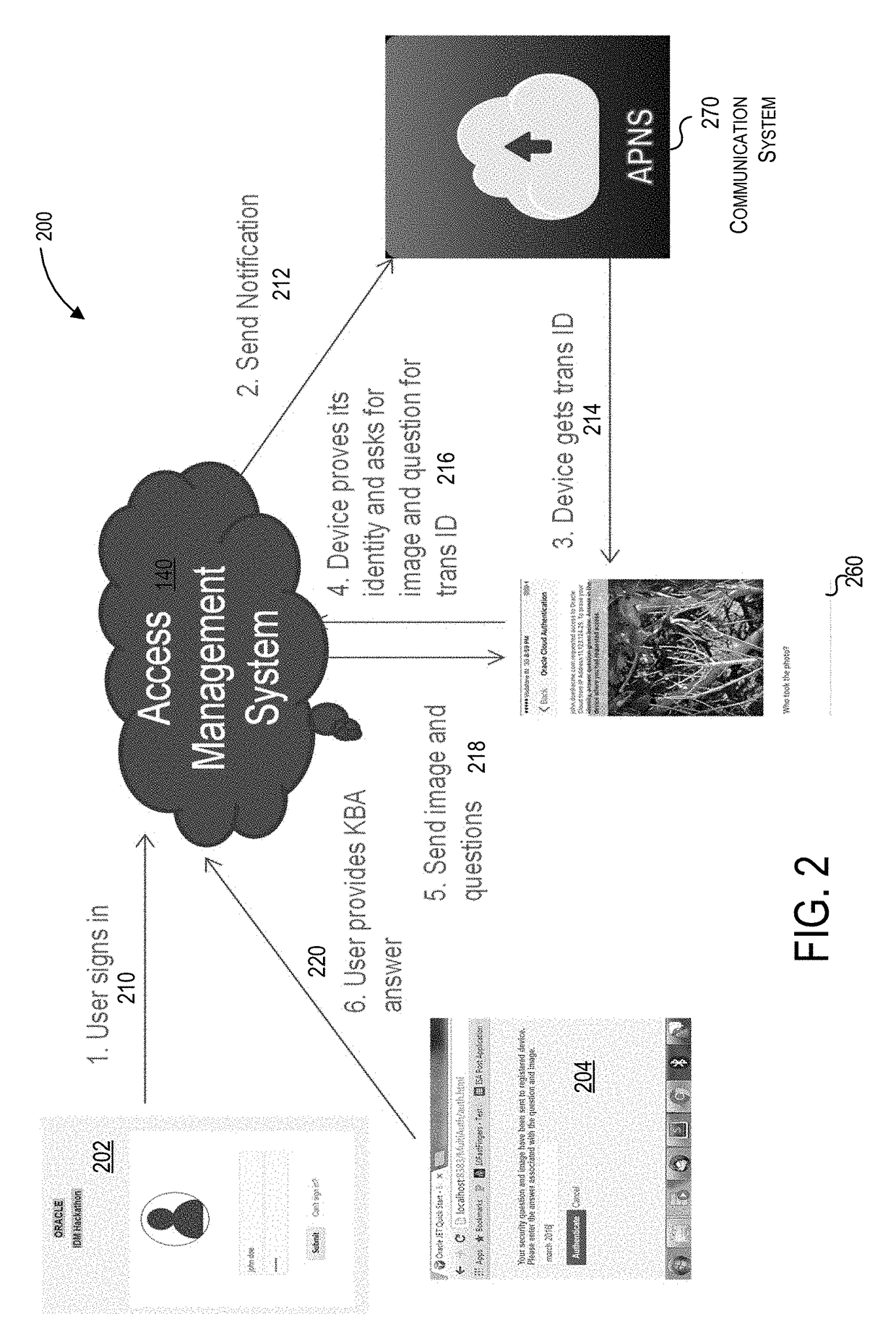
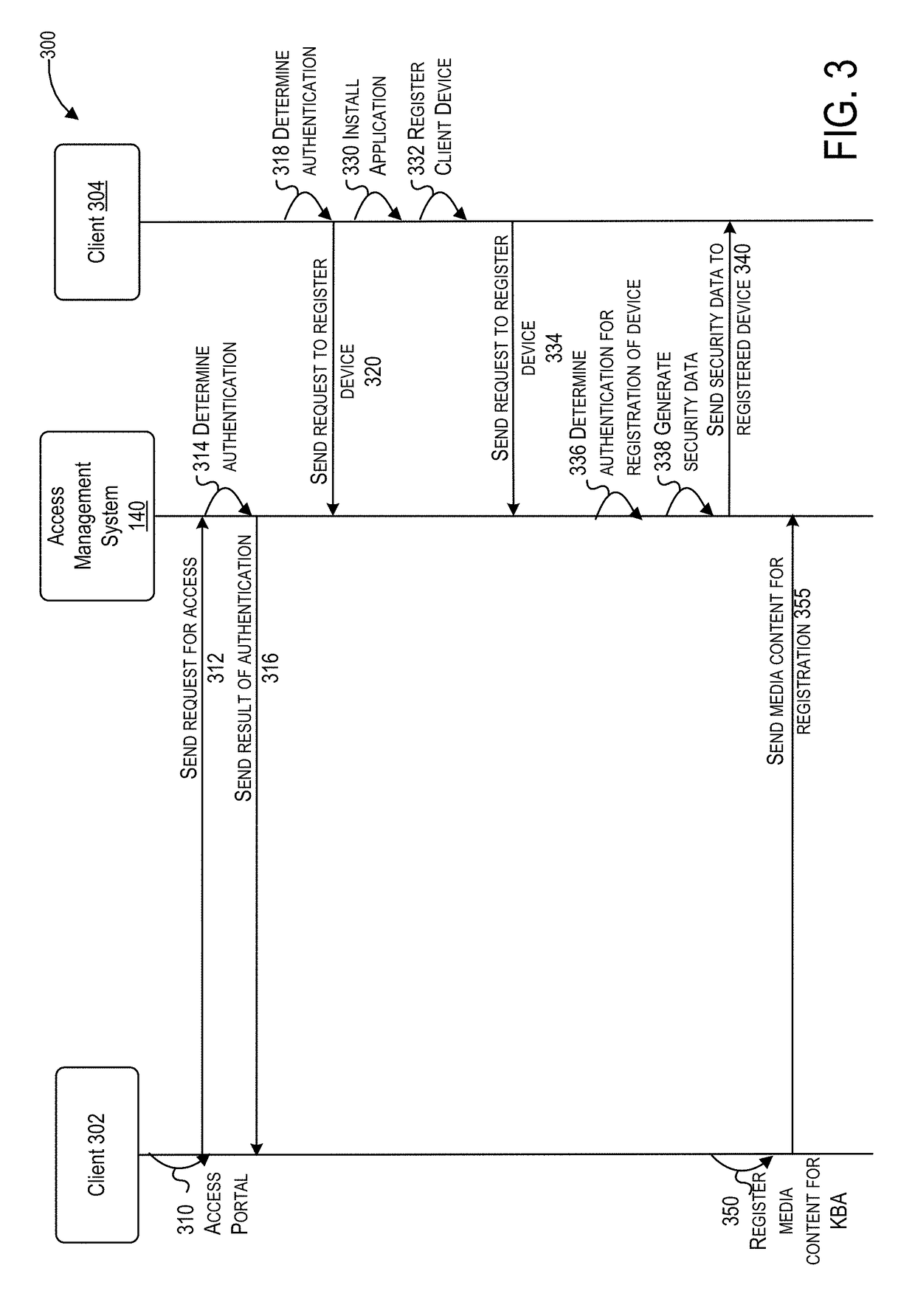
- Mobile device-based authentication and push notifications: Multi-factor authentication can leverage mobile devices as a secondary authentication factor through push notifications, SMS codes, or dedicated authentication applications. When a user attempts to access a system, a notification is sent to their registered mobile device requiring approval or verification. This method ensures that even if primary credentials are compromised, unauthorized access is prevented unless the attacker also has physical access to the user's mobile device.
- Risk-based and adaptive authentication mechanisms: Advanced access control systems can implement risk-based authentication that dynamically adjusts authentication requirements based on contextual factors such as user location, device characteristics, access time, and behavioral patterns. When suspicious activity or anomalies are detected, the system can require additional authentication factors or increase security measures. This adaptive approach balances security with user convenience by applying stricter authentication only when necessary based on assessed risk levels.
- Certificate-based and cryptographic authentication: Multi-factor authentication systems can employ digital certificates and cryptographic keys as authentication factors. These methods use public key infrastructure and encryption techniques to verify user identity through certificate validation and challenge-response protocols. The combination of certificate-based authentication with other factors such as passwords or biometrics provides strong cryptographic assurance of user identity and protects against various attack vectors including man-in-the-middle attacks and credential theft.
02 Token-based and one-time password authentication
Authentication systems can utilize hardware or software tokens that generate one-time passwords or time-based codes as an additional authentication factor. These tokens can be physical devices or mobile applications that produce temporary codes synchronized with the authentication server. The one-time passwords expire after a single use or short time period, providing dynamic security credentials that cannot be reused by attackers. This approach adds a layer of security beyond static passwords and can be combined with other authentication methods for comprehensive access control.Expand Specific Solutions03 Risk-based adaptive authentication
Advanced authentication systems can implement risk-based or adaptive authentication that dynamically adjusts security requirements based on contextual factors. These systems analyze various parameters such as user location, device information, network characteristics, time of access, and behavioral patterns to assess the risk level of each authentication attempt. When anomalies or high-risk conditions are detected, the system can require additional authentication factors or deny access. This intelligent approach balances security with user convenience by applying stricter controls only when necessary.Expand Specific Solutions04 Mobile device-based authentication
Multi-factor authentication can leverage mobile devices as a trusted authentication factor through various mechanisms. Mobile phones can receive push notifications for approval, SMS codes, or utilize dedicated authentication applications. The mobile device itself can serve as a possession factor, with the system verifying device identity through unique identifiers or certificates. Some implementations use the mobile device's built-in security features such as secure enclaves or trusted execution environments to store and process authentication credentials securely.Expand Specific Solutions05 Certificate-based and cryptographic authentication
Authentication systems can employ digital certificates and cryptographic keys as authentication factors for secure access control. Public key infrastructure can be utilized where users possess private keys stored on smart cards, hardware security modules, or secure software containers. The authentication process involves cryptographic challenge-response protocols that verify possession of the private key without transmitting it. This method provides strong authentication through mathematical proof of identity and can be integrated with other factors to create a comprehensive multi-factor authentication framework.Expand Specific Solutions
Leading MFA and Access Control System Providers
The multi-factor authentication (MFA) access control market is experiencing rapid growth as organizations prioritize enhanced security measures. The industry has evolved from early-stage adoption to mainstream implementation, driven by increasing cyber threats and regulatory compliance requirements. Market expansion is significant, with enterprises across sectors investing heavily in sophisticated authentication solutions. Technology maturity varies considerably among market participants. Established players like Intel Corp., Amazon Technologies, and Oracle International Corp. leverage their extensive infrastructure and R&D capabilities to deliver comprehensive MFA platforms. Specialized identity management companies such as Okta, Inc. demonstrate advanced technical sophistication with cloud-native solutions. Financial institutions including Bank of America Corp. and Capital One Services LLC showcase mature implementations for high-security environments. Traditional security providers like ADT Security Corp. and Sensormatic Electronics LLC are integrating MFA into physical access systems. Meanwhile, emerging companies like Soloinsight, Inc. focus on specialized PIAM solutions, while international players including Sony Group Corp. and KT Corp. contribute diverse technological approaches to this competitive landscape.
Intel Corp.
Technical Solution: Intel develops hardware-based multi-factor authentication solutions through Intel Identity Protection Technology (IPT) and Intel Authenticate. Their approach leverages hardware security modules embedded in processors to provide tamper-resistant authentication factors including biometric sensors, near-field communication, and encrypted hardware tokens. The technology integrates with existing enterprise security infrastructure and supports FIDO Alliance standards for passwordless authentication across various device types.
Strengths: Hardware-level security provides superior tamper resistance and performance optimization. Weaknesses: Limited to Intel-based systems and requires specific hardware components for full functionality.
Amazon Technologies, Inc.
Technical Solution: Amazon Web Services offers multi-factor authentication through AWS Identity and Access Management (IAM) and Amazon Cognito services. Their solution supports virtual and hardware MFA devices, including FIDO security keys, time-based one-time passwords, and SMS verification. The platform provides centralized identity management for millions of users with automatic scaling capabilities and integrates with over 200 AWS services, offering fine-grained access control policies and real-time monitoring of authentication events.
Strengths: Massive scalability and comprehensive cloud integration with robust monitoring capabilities. Weaknesses: Complexity in configuration and potential high costs for large-scale implementations.
Core MFA Technologies and Authentication Methods
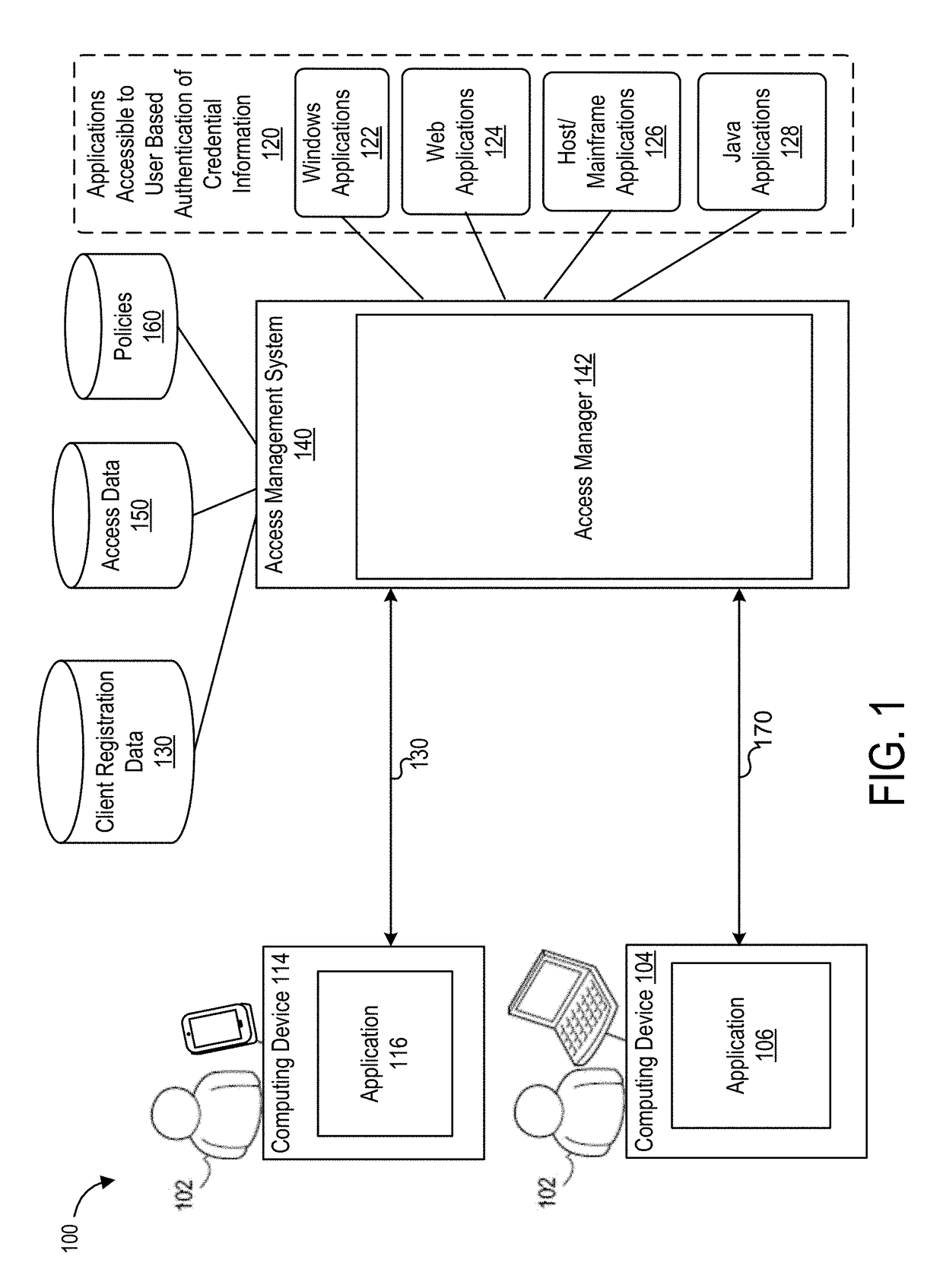
Electronic access control multi-factor authentication using centralized hardware secured credential system and methods of use thereof
PatentActiveUS12166872B2
Innovation
- A tokenless, software-based PKI electronic access control system that utilizes a centralized Credential Hardware Security Module (HSM) for secure cryptographic storage and processing of user credentials, allowing authentication without requiring personal or organizational information to leave a restricted location, and enabling access for both human and non-human entities.
Techniques for access management based on multi-factor authentication including knowledge-based authentication
PatentActiveUS10157275B1
Innovation
- Implementing a multi-factor authentication system that utilizes multiple clients, including a trusted device, to provide knowledge-based authentication (KBA) through media content registration, ensuring stronger authentication by combining 'what you know' and 'what you have' factors, and using secure communication mechanisms like push and pull notification systems to enhance security.
Cybersecurity Compliance and Privacy Regulations
The implementation of multi-factor authentication in access control systems operates within a complex regulatory landscape that demands strict adherence to cybersecurity compliance frameworks and privacy protection standards. Organizations must navigate an intricate web of regulations that vary significantly across jurisdictions, industries, and data types, creating substantial challenges for global enterprises seeking to deploy unified MFA solutions.
Data protection regulations such as the General Data Protection Regulation (GDPR) in Europe and the California Consumer Privacy Act (CCPA) impose stringent requirements on how biometric data, authentication credentials, and user behavioral patterns are collected, processed, and stored. These regulations mandate explicit user consent for biometric enrollment, require data minimization principles in authentication processes, and establish strict breach notification timelines that directly impact MFA system design and incident response procedures.
Industry-specific compliance frameworks add additional layers of complexity to MFA implementations. The Payment Card Industry Data Security Standard (PCI DSS) requires strong authentication mechanisms for cardholder data environments, while healthcare organizations must ensure MFA systems comply with HIPAA requirements for protecting electronic health information. Financial institutions face regulatory oversight from multiple agencies, including SOX compliance requirements that mandate robust access controls for financial reporting systems.
Cross-border data transfer restrictions significantly impact cloud-based MFA solutions and centralized authentication architectures. Organizations must implement data localization strategies, establish adequate safeguards for international data flows, and maintain compliance with varying national security requirements that may restrict certain authentication technologies or require local data residency.
The evolving nature of privacy regulations creates ongoing compliance challenges as new legislation emerges globally. Recent developments include sector-specific privacy laws, enhanced biometric protection statutes, and emerging artificial intelligence governance frameworks that may impact behavioral authentication and risk-based access control systems. Organizations must establish adaptive compliance frameworks that can accommodate regulatory changes while maintaining security effectiveness and operational efficiency across their MFA implementations.
Data protection regulations such as the General Data Protection Regulation (GDPR) in Europe and the California Consumer Privacy Act (CCPA) impose stringent requirements on how biometric data, authentication credentials, and user behavioral patterns are collected, processed, and stored. These regulations mandate explicit user consent for biometric enrollment, require data minimization principles in authentication processes, and establish strict breach notification timelines that directly impact MFA system design and incident response procedures.
Industry-specific compliance frameworks add additional layers of complexity to MFA implementations. The Payment Card Industry Data Security Standard (PCI DSS) requires strong authentication mechanisms for cardholder data environments, while healthcare organizations must ensure MFA systems comply with HIPAA requirements for protecting electronic health information. Financial institutions face regulatory oversight from multiple agencies, including SOX compliance requirements that mandate robust access controls for financial reporting systems.
Cross-border data transfer restrictions significantly impact cloud-based MFA solutions and centralized authentication architectures. Organizations must implement data localization strategies, establish adequate safeguards for international data flows, and maintain compliance with varying national security requirements that may restrict certain authentication technologies or require local data residency.
The evolving nature of privacy regulations creates ongoing compliance challenges as new legislation emerges globally. Recent developments include sector-specific privacy laws, enhanced biometric protection statutes, and emerging artificial intelligence governance frameworks that may impact behavioral authentication and risk-based access control systems. Organizations must establish adaptive compliance frameworks that can accommodate regulatory changes while maintaining security effectiveness and operational efficiency across their MFA implementations.
Zero Trust Architecture Implementation Strategies
Zero Trust Architecture represents a paradigm shift from traditional perimeter-based security models to a comprehensive "never trust, always verify" approach. When implementing Zero Trust principles to enhance access control systems with multi-factor authentication, organizations must adopt a holistic strategy that encompasses network segmentation, identity verification, and continuous monitoring. The implementation requires careful orchestration of multiple security layers working in concert to create an impenetrable defense mechanism.
The foundational strategy begins with establishing micro-segmentation throughout the network infrastructure. This approach creates granular security zones where each segment operates under strict access controls, preventing lateral movement of potential threats. Network administrators must implement software-defined perimeters that dynamically adjust based on user behavior, device posture, and contextual factors. This segmentation works synergistically with multi-factor authentication by ensuring that even authenticated users can only access resources within their designated security zones.
Identity and access management forms the cornerstone of Zero Trust implementation. Organizations must deploy comprehensive identity governance frameworks that integrate seamlessly with multi-factor authentication mechanisms. This involves establishing centralized identity providers, implementing single sign-on solutions, and maintaining detailed user attribute repositories. The strategy requires continuous validation of user identities through behavioral analytics, device fingerprinting, and risk-based authentication protocols.
Device trust verification constitutes another critical implementation component. Organizations must establish device registration processes, implement endpoint detection and response solutions, and maintain comprehensive device inventories. The strategy involves creating device trust scores based on compliance status, security posture, and historical behavior patterns. These scores directly influence access decisions and authentication requirements.
Continuous monitoring and adaptive response mechanisms ensure the Zero Trust architecture remains effective against evolving threats. Implementation strategies must include real-time security analytics, automated threat detection, and dynamic policy enforcement. Organizations should deploy security orchestration platforms that can automatically adjust access controls based on threat intelligence and user behavior patterns, creating a self-healing security ecosystem that strengthens over time.
The foundational strategy begins with establishing micro-segmentation throughout the network infrastructure. This approach creates granular security zones where each segment operates under strict access controls, preventing lateral movement of potential threats. Network administrators must implement software-defined perimeters that dynamically adjust based on user behavior, device posture, and contextual factors. This segmentation works synergistically with multi-factor authentication by ensuring that even authenticated users can only access resources within their designated security zones.
Identity and access management forms the cornerstone of Zero Trust implementation. Organizations must deploy comprehensive identity governance frameworks that integrate seamlessly with multi-factor authentication mechanisms. This involves establishing centralized identity providers, implementing single sign-on solutions, and maintaining detailed user attribute repositories. The strategy requires continuous validation of user identities through behavioral analytics, device fingerprinting, and risk-based authentication protocols.
Device trust verification constitutes another critical implementation component. Organizations must establish device registration processes, implement endpoint detection and response solutions, and maintain comprehensive device inventories. The strategy involves creating device trust scores based on compliance status, security posture, and historical behavior patterns. These scores directly influence access decisions and authentication requirements.
Continuous monitoring and adaptive response mechanisms ensure the Zero Trust architecture remains effective against evolving threats. Implementation strategies must include real-time security analytics, automated threat detection, and dynamic policy enforcement. Organizations should deploy security orchestration platforms that can automatically adjust access controls based on threat intelligence and user behavior patterns, creating a self-healing security ecosystem that strengthens over time.
Unlock deeper insights with Patsnap Eureka Quick Research — get a full tech report to explore trends and direct your research. Try now!
Generate Your Research Report Instantly with AI Agent
Supercharge your innovation with Patsnap Eureka AI Agent Platform!