Ensuring Reliable Access Systems in Power Outages
FEB 27, 20269 MIN READ
Generate Your Research Report Instantly with AI Agent
PatSnap Eureka helps you evaluate technical feasibility & market potential.
Power Outage Access Control Background and Objectives
Access control systems have evolved from simple mechanical locks to sophisticated electronic and biometric solutions over the past several decades. Traditional access control relied heavily on physical keys and manual verification processes, which gradually transitioned to magnetic stripe cards, proximity cards, and eventually to smart cards and biometric authentication systems. The integration of network connectivity and cloud-based management platforms has further transformed these systems into comprehensive security ecosystems that can monitor, log, and control access across multiple facilities simultaneously.
The critical dependency on electrical power has emerged as a fundamental vulnerability in modern access control infrastructure. As organizations increasingly adopt electronic locks, card readers, biometric scanners, and networked security systems, the risk of complete system failure during power outages has become a significant concern. This vulnerability is particularly pronounced in mission-critical facilities such as hospitals, data centers, emergency services, and secure government installations where continuous access control is essential for both security and operational continuity.
Recent technological advancements have introduced various approaches to address power-related vulnerabilities in access control systems. Battery backup solutions, uninterruptible power supplies, and energy harvesting technologies have become integral components of resilient access control designs. Additionally, the development of low-power communication protocols and energy-efficient hardware has enabled the creation of systems that can operate for extended periods during power disruptions while maintaining full functionality.
The primary objective of ensuring reliable access systems during power outages encompasses multiple technical goals. First, maintaining authentication capabilities to verify authorized personnel and prevent unauthorized access during emergency situations. Second, preserving audit trail functionality to ensure security events are properly logged even during power disruptions. Third, enabling emergency access procedures that balance security requirements with safety considerations during crisis situations.
Furthermore, the technical objectives include developing fail-safe mechanisms that default to appropriate security postures based on facility requirements. Some environments may require fail-secure operations where doors remain locked during power failures, while others may need fail-safe configurations that allow emergency egress. The challenge lies in creating intelligent systems that can differentiate between various emergency scenarios and respond accordingly while maintaining the integrity of security protocols and ensuring compliance with safety regulations.
The critical dependency on electrical power has emerged as a fundamental vulnerability in modern access control infrastructure. As organizations increasingly adopt electronic locks, card readers, biometric scanners, and networked security systems, the risk of complete system failure during power outages has become a significant concern. This vulnerability is particularly pronounced in mission-critical facilities such as hospitals, data centers, emergency services, and secure government installations where continuous access control is essential for both security and operational continuity.
Recent technological advancements have introduced various approaches to address power-related vulnerabilities in access control systems. Battery backup solutions, uninterruptible power supplies, and energy harvesting technologies have become integral components of resilient access control designs. Additionally, the development of low-power communication protocols and energy-efficient hardware has enabled the creation of systems that can operate for extended periods during power disruptions while maintaining full functionality.
The primary objective of ensuring reliable access systems during power outages encompasses multiple technical goals. First, maintaining authentication capabilities to verify authorized personnel and prevent unauthorized access during emergency situations. Second, preserving audit trail functionality to ensure security events are properly logged even during power disruptions. Third, enabling emergency access procedures that balance security requirements with safety considerations during crisis situations.
Furthermore, the technical objectives include developing fail-safe mechanisms that default to appropriate security postures based on facility requirements. Some environments may require fail-secure operations where doors remain locked during power failures, while others may need fail-safe configurations that allow emergency egress. The challenge lies in creating intelligent systems that can differentiate between various emergency scenarios and respond accordingly while maintaining the integrity of security protocols and ensuring compliance with safety regulations.
Market Demand for Backup Access Systems
The global market for backup access systems has experienced substantial growth driven by increasing dependency on electronic security infrastructure and rising awareness of power grid vulnerabilities. Critical facilities including data centers, healthcare institutions, financial services, and government buildings represent the primary demand drivers, as these sectors cannot afford access control failures during power disruptions.
Commercial real estate and corporate facilities constitute another significant market segment, particularly in regions prone to natural disasters or experiencing aging electrical infrastructure. The shift toward smart building technologies has further amplified demand, as modern access systems integrate multiple electronic components that require continuous power supply to maintain security protocols.
Healthcare facilities demonstrate particularly strong demand patterns due to regulatory requirements and patient safety considerations. Hospitals and medical centers require uninterrupted access control to secure pharmaceutical storage areas, patient records, and restricted medical equipment zones. Similarly, financial institutions face stringent compliance requirements that mandate continuous security system operation regardless of power conditions.
The residential sector has emerged as a growing market segment, driven by increased adoption of smart home technologies and electronic access systems. High-end residential developments and gated communities increasingly specify backup power solutions for access control systems to maintain security during outages.
Geographic demand patterns reflect regional infrastructure reliability and regulatory environments. Markets with frequent power disruptions or extreme weather events show higher adoption rates of backup access systems. Developing economies experiencing rapid urbanization but inconsistent power supply represent significant growth opportunities.
Technology evolution has expanded market scope beyond traditional battery backup solutions. Integration requirements with cloud-based access management systems, mobile credentials, and IoT devices have created demand for more sophisticated backup power architectures that support data connectivity and real-time monitoring capabilities.
Regulatory compliance requirements continue to drive market expansion, particularly in sectors subject to security standards and emergency preparedness mandates. Building codes in many jurisdictions now specify backup power requirements for electronic access systems in commercial and institutional facilities.
The market demonstrates strong correlation with broader trends in building automation and security system integration, suggesting continued growth as organizations prioritize comprehensive security infrastructure resilience.
Commercial real estate and corporate facilities constitute another significant market segment, particularly in regions prone to natural disasters or experiencing aging electrical infrastructure. The shift toward smart building technologies has further amplified demand, as modern access systems integrate multiple electronic components that require continuous power supply to maintain security protocols.
Healthcare facilities demonstrate particularly strong demand patterns due to regulatory requirements and patient safety considerations. Hospitals and medical centers require uninterrupted access control to secure pharmaceutical storage areas, patient records, and restricted medical equipment zones. Similarly, financial institutions face stringent compliance requirements that mandate continuous security system operation regardless of power conditions.
The residential sector has emerged as a growing market segment, driven by increased adoption of smart home technologies and electronic access systems. High-end residential developments and gated communities increasingly specify backup power solutions for access control systems to maintain security during outages.
Geographic demand patterns reflect regional infrastructure reliability and regulatory environments. Markets with frequent power disruptions or extreme weather events show higher adoption rates of backup access systems. Developing economies experiencing rapid urbanization but inconsistent power supply represent significant growth opportunities.
Technology evolution has expanded market scope beyond traditional battery backup solutions. Integration requirements with cloud-based access management systems, mobile credentials, and IoT devices have created demand for more sophisticated backup power architectures that support data connectivity and real-time monitoring capabilities.
Regulatory compliance requirements continue to drive market expansion, particularly in sectors subject to security standards and emergency preparedness mandates. Building codes in many jurisdictions now specify backup power requirements for electronic access systems in commercial and institutional facilities.
The market demonstrates strong correlation with broader trends in building automation and security system integration, suggesting continued growth as organizations prioritize comprehensive security infrastructure resilience.
Current Challenges in Power-Independent Access Control
Power-independent access control systems face significant technical challenges that stem from the fundamental conflict between maintaining security and ensuring operational continuity during electrical disruptions. Traditional electronic access control systems rely heavily on continuous power supply to operate door locks, card readers, communication networks, and central management servers. When power outages occur, these interconnected components often fail simultaneously, creating cascading system failures that compromise both security and accessibility.
Battery backup systems, while commonly deployed, present substantial limitations in extended outage scenarios. Most standard uninterruptible power supply units provide only 2-4 hours of operation under normal load conditions. During emergencies when access frequency increases dramatically, battery depletion accelerates significantly. Additionally, battery degradation over time reduces actual backup duration below rated specifications, often discovered only during critical situations when replacement is impossible.
Communication infrastructure breakdown represents another critical challenge during power outages. Network switches, wireless access points, and cellular towers typically lose power simultaneously with access control systems. This communication failure prevents remote monitoring, real-time access logging, and centralized security management. Cloud-based access control systems become particularly vulnerable as local internet connectivity disappears, rendering sophisticated security features inoperable.
Mechanical lock integration poses complex engineering challenges in power-independent designs. Fail-safe versus fail-secure lock configurations must balance security requirements with emergency egress needs. Electromagnetic locks require continuous power to maintain security, while electric strikes and motorized locks consume significant power during each operation. Hybrid mechanical-electronic solutions often introduce additional failure points and maintenance complexity.
Environmental factors compound these technical challenges significantly. Extreme temperatures affect battery performance and electronic component reliability. Humidity and water ingress during storm-related outages can damage sensitive electronic components. Backup power systems must operate reliably across wide temperature ranges while maintaining consistent performance characteristics.
System scalability presents ongoing difficulties in large installations. Enterprise facilities with hundreds of access points require substantial backup power infrastructure, creating cost and space constraints. Distributed backup systems increase complexity and maintenance requirements, while centralized backup power creates single points of failure that can compromise entire facility security.
Integration with fire safety and emergency systems creates additional technical constraints. Access control systems must coordinate with fire alarm systems, emergency lighting, and evacuation procedures during power outages. Conflicting requirements between security protocols and emergency egress regulations require sophisticated system design and failover logic.
Battery backup systems, while commonly deployed, present substantial limitations in extended outage scenarios. Most standard uninterruptible power supply units provide only 2-4 hours of operation under normal load conditions. During emergencies when access frequency increases dramatically, battery depletion accelerates significantly. Additionally, battery degradation over time reduces actual backup duration below rated specifications, often discovered only during critical situations when replacement is impossible.
Communication infrastructure breakdown represents another critical challenge during power outages. Network switches, wireless access points, and cellular towers typically lose power simultaneously with access control systems. This communication failure prevents remote monitoring, real-time access logging, and centralized security management. Cloud-based access control systems become particularly vulnerable as local internet connectivity disappears, rendering sophisticated security features inoperable.
Mechanical lock integration poses complex engineering challenges in power-independent designs. Fail-safe versus fail-secure lock configurations must balance security requirements with emergency egress needs. Electromagnetic locks require continuous power to maintain security, while electric strikes and motorized locks consume significant power during each operation. Hybrid mechanical-electronic solutions often introduce additional failure points and maintenance complexity.
Environmental factors compound these technical challenges significantly. Extreme temperatures affect battery performance and electronic component reliability. Humidity and water ingress during storm-related outages can damage sensitive electronic components. Backup power systems must operate reliably across wide temperature ranges while maintaining consistent performance characteristics.
System scalability presents ongoing difficulties in large installations. Enterprise facilities with hundreds of access points require substantial backup power infrastructure, creating cost and space constraints. Distributed backup systems increase complexity and maintenance requirements, while centralized backup power creates single points of failure that can compromise entire facility security.
Integration with fire safety and emergency systems creates additional technical constraints. Access control systems must coordinate with fire alarm systems, emergency lighting, and evacuation procedures during power outages. Conflicting requirements between security protocols and emergency egress regulations require sophisticated system design and failover logic.
Existing Backup Power Solutions for Access Systems
01 Redundancy and failover mechanisms in access control systems
Access systems can incorporate redundant components and automatic failover mechanisms to ensure continuous operation even when primary components fail. This includes backup power supplies, duplicate communication paths, and redundant authentication servers. When a failure is detected, the system automatically switches to backup components without interrupting access control functions. These mechanisms significantly improve system availability and prevent single points of failure from compromising security or accessibility.- Redundancy and failover mechanisms in access control systems: Access systems can incorporate redundant components and automatic failover mechanisms to ensure continuous operation even when primary components fail. This includes backup power supplies, duplicate communication paths, and redundant authentication servers. When a failure is detected, the system automatically switches to backup components without interrupting access control functions. These mechanisms significantly improve system availability and prevent single points of failure from compromising security or accessibility.
- Real-time monitoring and diagnostic systems for access control: Advanced monitoring systems continuously track the operational status of access control components including readers, locks, controllers, and network connections. These systems collect performance metrics, detect anomalies, and generate alerts when potential failures are identified. Diagnostic capabilities enable predictive maintenance by identifying components that may fail before actual failure occurs. This proactive approach minimizes downtime and ensures consistent system reliability through early intervention.
- Distributed architecture for enhanced system resilience: Implementing distributed system architectures where access control intelligence is distributed across multiple nodes rather than centralized in a single location. This approach ensures that if one node fails, other nodes continue to operate independently, maintaining access control functionality. Local processing capabilities at edge devices allow continued operation even during network disruptions. The distributed design improves overall system reliability by eliminating central points of failure and enabling graceful degradation.
- Self-healing and automatic recovery mechanisms: Access systems equipped with self-healing capabilities can automatically detect, diagnose, and recover from various failure conditions without human intervention. These systems include automatic restart procedures, configuration restoration, and error correction algorithms. When communication failures occur, the system can automatically re-establish connections and synchronize data. Self-healing mechanisms reduce mean time to recovery and minimize the impact of transient failures on system availability.
- Data integrity and backup strategies for access systems: Robust data management strategies ensure that access control data including credentials, access rights, and audit logs are protected against loss or corruption. This includes regular automated backups, data replication across multiple storage locations, and integrity verification mechanisms. Transaction logging and rollback capabilities allow recovery to known good states after failures. These strategies ensure that access control decisions remain accurate and that historical records are preserved even during system failures or data corruption events.
02 Real-time monitoring and diagnostic systems for access control
Advanced monitoring systems continuously track the operational status of access control components including readers, locks, controllers, and network connections. These systems collect performance metrics, detect anomalies, and generate alerts when potential failures are identified. Diagnostic capabilities enable predictive maintenance by identifying components that may fail before actual failure occurs. This proactive approach minimizes downtime and ensures consistent system reliability through early intervention.Expand Specific Solutions03 Distributed architecture for enhanced system resilience
Implementing distributed system architectures where access control intelligence is distributed across multiple nodes rather than centralized improves overall reliability. Local controllers can continue operating independently even when communication with central servers is interrupted. This architecture prevents complete system failure due to network issues or central server problems. Edge computing capabilities allow critical access decisions to be made locally, ensuring continued operation during network outages.Expand Specific Solutions04 Self-healing and automatic recovery protocols
Access systems can be designed with self-healing capabilities that automatically detect, diagnose, and recover from failures without human intervention. These protocols include automatic system restarts, configuration restoration, and database synchronization after failures. The systems maintain transaction logs and state information to ensure data integrity during recovery processes. Automatic recovery mechanisms reduce mean time to repair and minimize the impact of system failures on operations.Expand Specific Solutions05 Secure communication protocols and data integrity verification
Reliable access systems employ robust communication protocols with error detection, correction, and encryption to ensure data integrity and prevent unauthorized access. These protocols include checksums, acknowledgment mechanisms, and retry logic to handle transmission errors. Regular verification of system configurations and access databases ensures consistency across distributed components. Secure communication channels prevent tampering and ensure that access control decisions are based on accurate, uncompromised information.Expand Specific Solutions
Key Players in Emergency Access Control Industry
The reliable access systems market during power outages represents a mature yet rapidly evolving sector driven by increasing infrastructure vulnerabilities and extreme weather events. The industry has reached significant scale, with established players like Huawei, Siemens Industry, and Eaton Intelligent Power leading traditional UPS and backup power solutions. Technology maturity varies considerably across segments - while conventional battery backup systems from companies like Panasonic Holdings and Toshiba are well-established, emerging solutions show innovation gaps. Advanced players including IBM, Hitachi, and GE Technology are developing smart grid integration and IoT-enabled monitoring systems. The competitive landscape features diverse participants from telecommunications (AT&T, Verizon Patent & Licensing), utilities (Korea Electric Power, Eversource Energy), and specialized providers (Joule Case, DataRemote). Market growth is accelerated by digital transformation demands and regulatory requirements for critical infrastructure resilience, creating opportunities for both established manufacturers and innovative startups offering modular, scalable solutions.
Huawei Technologies Co., Ltd.
Technical Solution: Huawei offers intelligent power solutions and backup systems designed to maintain telecommunications and access control infrastructure during power outages. Their technology includes distributed power architectures with redundant backup systems, advanced battery management using lithium iron phosphate technology for enhanced safety and longevity, and AI-powered energy management systems that optimize power consumption and extend backup duration. The solutions feature modular designs that allow for easy scalability and maintenance, integrated monitoring systems that provide real-time status updates and predictive failure analysis, and compatibility with various access control protocols and systems. Their approach emphasizes high efficiency power conversion and intelligent load management to maximize system uptime.
Strengths: Advanced AI-powered energy management, modular and scalable architecture, strong telecommunications infrastructure expertise. Weaknesses: Potential regulatory restrictions in certain markets, complex integration with non-Huawei systems, requires specialized technical knowledge for optimization.
Eaton Intelligent Power Ltd.
Technical Solution: Eaton develops comprehensive uninterruptible power supply (UPS) systems and backup power solutions specifically designed to maintain critical access control systems during power outages. Their technology includes intelligent power management systems that automatically switch to battery backup within milliseconds of detecting power loss, ensuring continuous operation of electronic locks, card readers, and security monitoring systems. The company's solutions feature advanced battery management with lithium-ion technology providing extended runtime, remote monitoring capabilities for proactive maintenance, and scalable power architectures that can support everything from single-door access points to enterprise-wide security infrastructures.
Strengths: Industry-leading UPS technology with rapid switchover times, extensive product portfolio covering various power requirements, proven reliability in mission-critical applications. Weaknesses: Higher initial investment costs, requires regular battery maintenance and replacement, complex installation for large-scale deployments.
Core Innovations in Power-Independent Access Control
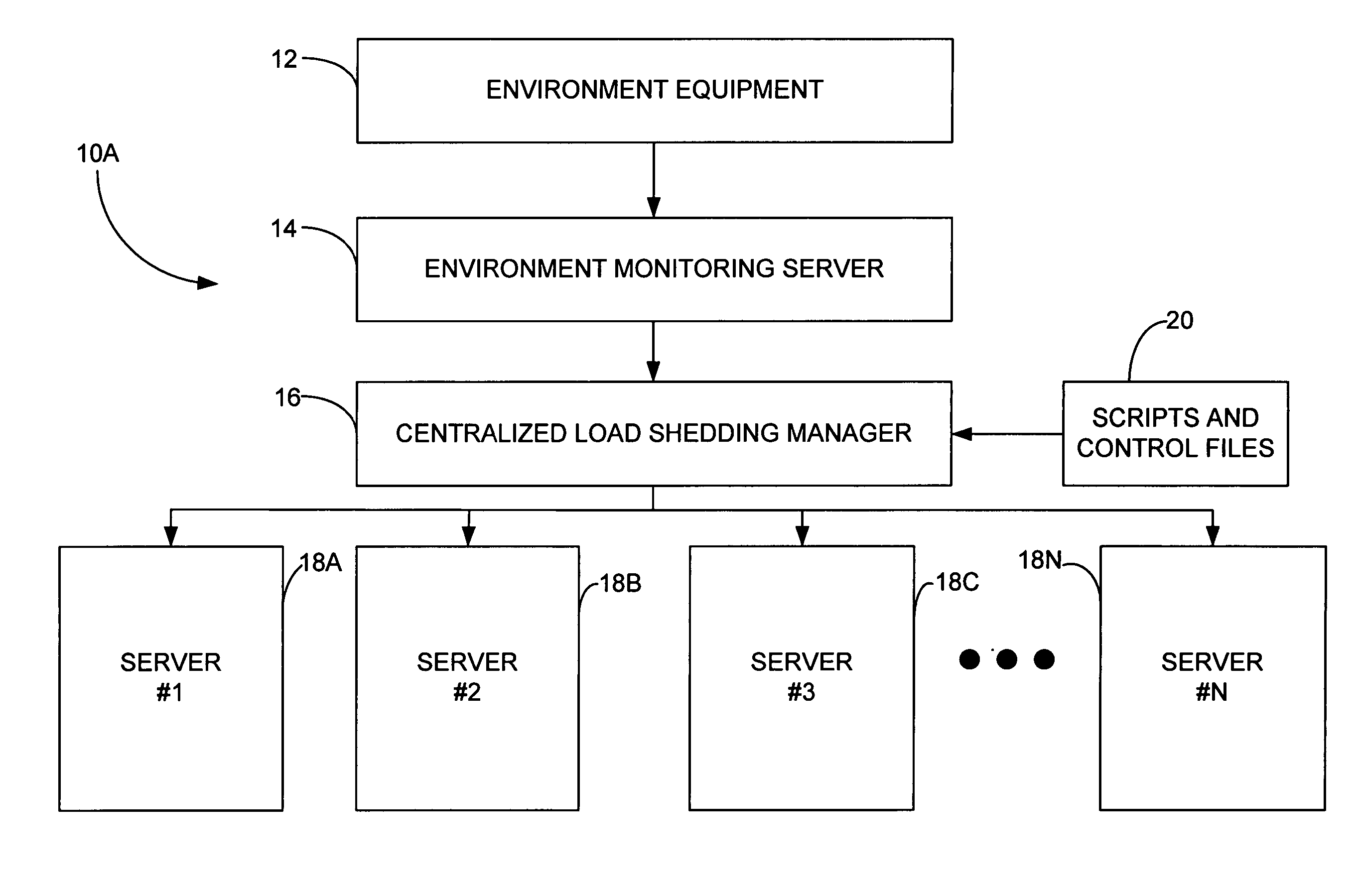
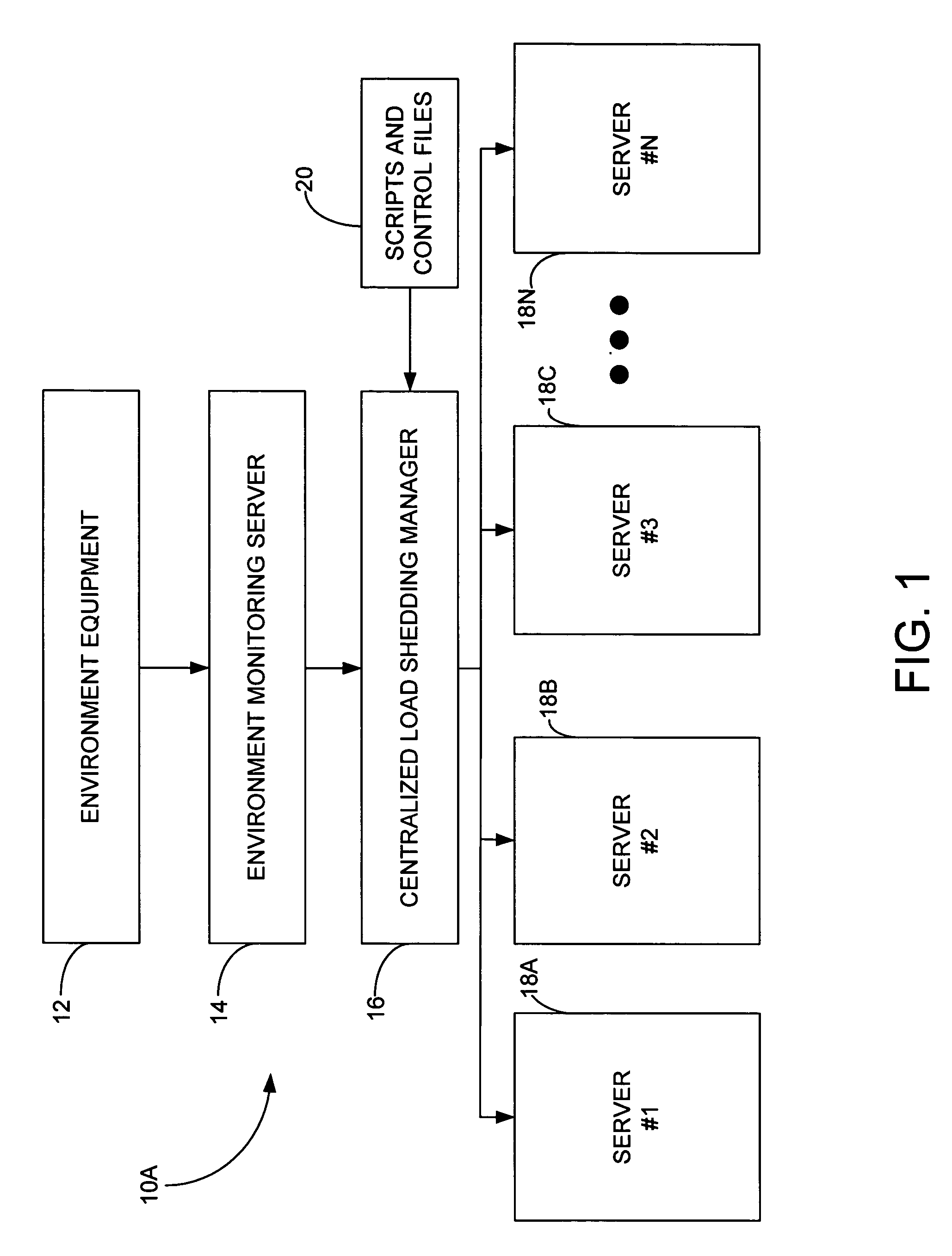
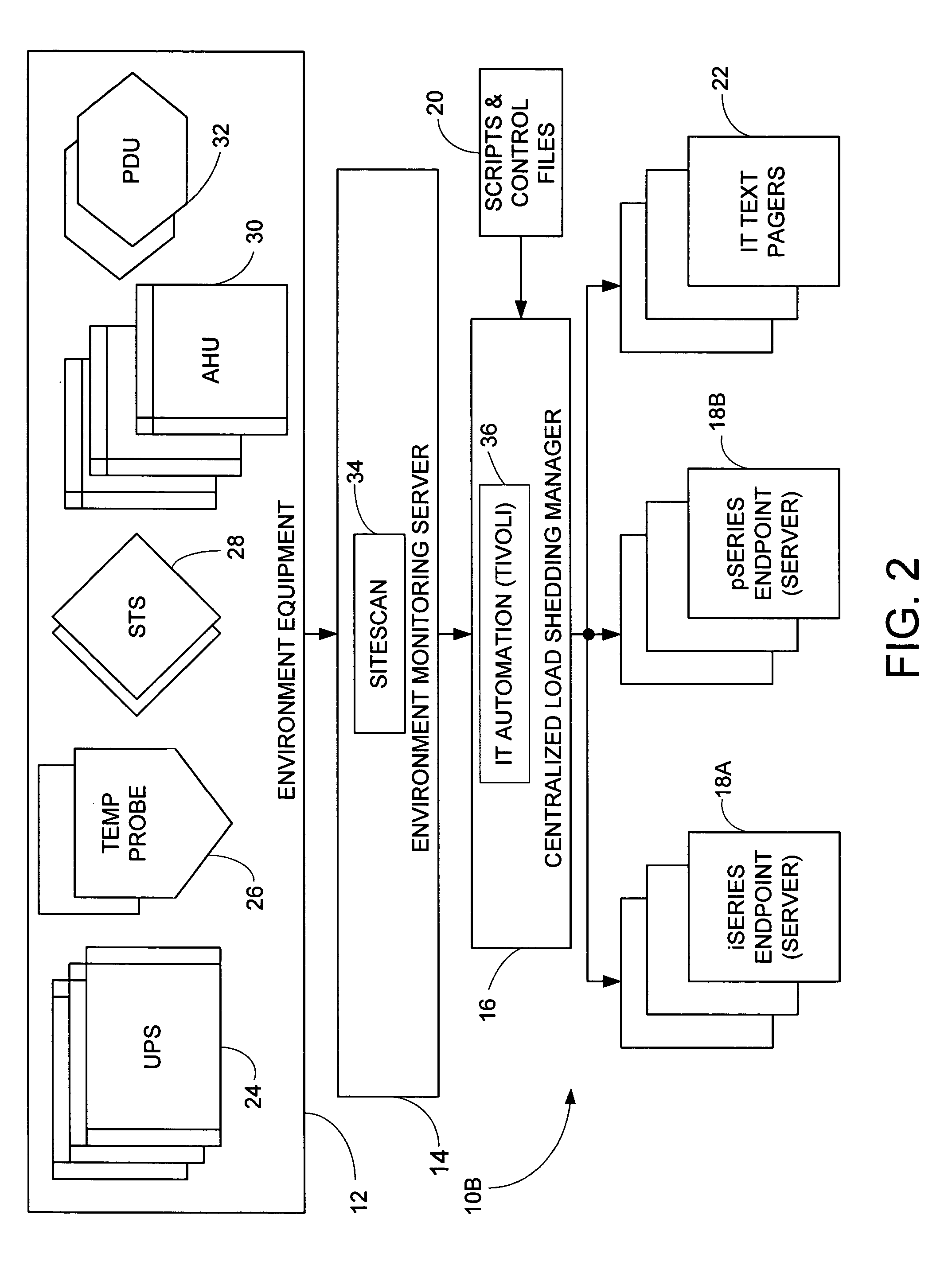
Method, apparatus and program product for managing the operation of a computing complex during a utility interruption
PatentInactiveUS20050086543A1
Innovation
- A method and apparatus that monitor operating environment parameters such as battery life, temperature, and time of day to selectively power down computer servers based on their criticality value, using a centralized load shedding manager and environment monitoring server to manage the shutdown process and send alerts to support personnel.
Systems and methods for redundant power supply
PatentWO2017079082A1
Innovation
- The implementation of a redundant power supply system that operates with multiple electrically independent power distribution paths from separate subsections of the electrical grid, ensuring continuous power availability by providing two independent active feeds to the destination, such as a data center, which can isolate faults and maintain operation even if one path fails.
Safety Standards for Emergency Access Systems
Emergency access systems operating during power outages must adhere to stringent safety standards to ensure both operational reliability and personnel protection. These standards encompass multiple regulatory frameworks, including NFPA 101 Life Safety Code, IBC International Building Code, and ADA accessibility requirements, which collectively establish minimum performance criteria for emergency access control systems.
The primary safety standard governing emergency access systems is the fail-safe operational principle, mandating that all electronically controlled access points must default to an unlocked state during power failures. This requirement ensures unimpeded egress during emergencies while maintaining life safety as the paramount concern. Additionally, systems must incorporate manual override mechanisms accessible to authorized personnel without requiring specialized tools or extensive training.
Battery backup systems supporting emergency access controls must comply with UL 2089 standards for health and life safety applications, requiring minimum 24-hour operational capacity under normal load conditions. These backup power systems must undergo regular testing protocols, typically monthly functional tests and annual capacity verification, to ensure reliable performance during actual emergencies.
Fire safety integration represents another critical standard requirement, where emergency access systems must interface seamlessly with fire alarm and suppression systems. Upon fire alarm activation, access controls must immediately release all secured doors along designated egress paths, regardless of power status. This integration must be hardwired rather than network-dependent to eliminate potential communication failures during emergencies.
Seismic and environmental resilience standards require emergency access hardware to maintain functionality under adverse conditions, including temperature extremes, humidity variations, and mechanical stress. Components must meet IP65 ingress protection ratings for harsh environments and demonstrate continued operation during seismic events up to specified intensity levels.
Regular compliance auditing and documentation requirements mandate comprehensive record-keeping of system performance, maintenance activities, and safety testing results. These standards ensure that emergency access systems maintain their critical safety functions throughout their operational lifecycle, providing reliable protection for building occupants during power outage scenarios.
The primary safety standard governing emergency access systems is the fail-safe operational principle, mandating that all electronically controlled access points must default to an unlocked state during power failures. This requirement ensures unimpeded egress during emergencies while maintaining life safety as the paramount concern. Additionally, systems must incorporate manual override mechanisms accessible to authorized personnel without requiring specialized tools or extensive training.
Battery backup systems supporting emergency access controls must comply with UL 2089 standards for health and life safety applications, requiring minimum 24-hour operational capacity under normal load conditions. These backup power systems must undergo regular testing protocols, typically monthly functional tests and annual capacity verification, to ensure reliable performance during actual emergencies.
Fire safety integration represents another critical standard requirement, where emergency access systems must interface seamlessly with fire alarm and suppression systems. Upon fire alarm activation, access controls must immediately release all secured doors along designated egress paths, regardless of power status. This integration must be hardwired rather than network-dependent to eliminate potential communication failures during emergencies.
Seismic and environmental resilience standards require emergency access hardware to maintain functionality under adverse conditions, including temperature extremes, humidity variations, and mechanical stress. Components must meet IP65 ingress protection ratings for harsh environments and demonstrate continued operation during seismic events up to specified intensity levels.
Regular compliance auditing and documentation requirements mandate comprehensive record-keeping of system performance, maintenance activities, and safety testing results. These standards ensure that emergency access systems maintain their critical safety functions throughout their operational lifecycle, providing reliable protection for building occupants during power outage scenarios.
Business Continuity Impact of Access System Failures
Access system failures during power outages create cascading effects that extend far beyond simple inconvenience, fundamentally disrupting organizational operations and threatening business continuity. When electronic access control systems fail, organizations face immediate operational paralysis as employees cannot enter facilities, access critical areas, or retrieve essential resources needed for business functions.
The financial implications of access system failures are substantial and multifaceted. Direct costs include lost productivity from workforce displacement, emergency locksmith services, and temporary security measures. Indirect costs encompass delayed project deliveries, missed client commitments, and potential contract penalties. For organizations operating in time-sensitive industries such as healthcare, manufacturing, or financial services, even brief access disruptions can result in significant revenue losses and regulatory compliance violations.
Security vulnerabilities emerge as a critical concern when access systems fail during power outages. Organizations often resort to manual override procedures or propped-open doors to maintain operations, creating security gaps that expose facilities to unauthorized access, theft, or data breaches. These temporary measures compromise the integrity of security protocols and may violate industry regulations or insurance requirements.
Customer service delivery suffers considerably when access system failures prevent staff from reaching service areas or accessing customer data systems. This disruption directly impacts customer satisfaction, potentially damaging long-term relationships and brand reputation. Organizations in retail, hospitality, and service sectors face immediate customer-facing consequences that can have lasting business impacts.
Supply chain operations experience significant disruption when access failures prevent entry to warehouses, loading docks, or distribution centers. This creates bottlenecks that affect inventory management, order fulfillment, and delivery schedules, potentially impacting multiple stakeholders across the supply network.
The cumulative effect of these disruptions often exceeds the immediate operational impact, as organizations must invest additional resources in recovery efforts, reputation management, and system redundancy improvements to prevent future occurrences and maintain stakeholder confidence.
The financial implications of access system failures are substantial and multifaceted. Direct costs include lost productivity from workforce displacement, emergency locksmith services, and temporary security measures. Indirect costs encompass delayed project deliveries, missed client commitments, and potential contract penalties. For organizations operating in time-sensitive industries such as healthcare, manufacturing, or financial services, even brief access disruptions can result in significant revenue losses and regulatory compliance violations.
Security vulnerabilities emerge as a critical concern when access systems fail during power outages. Organizations often resort to manual override procedures or propped-open doors to maintain operations, creating security gaps that expose facilities to unauthorized access, theft, or data breaches. These temporary measures compromise the integrity of security protocols and may violate industry regulations or insurance requirements.
Customer service delivery suffers considerably when access system failures prevent staff from reaching service areas or accessing customer data systems. This disruption directly impacts customer satisfaction, potentially damaging long-term relationships and brand reputation. Organizations in retail, hospitality, and service sectors face immediate customer-facing consequences that can have lasting business impacts.
Supply chain operations experience significant disruption when access failures prevent entry to warehouses, loading docks, or distribution centers. This creates bottlenecks that affect inventory management, order fulfillment, and delivery schedules, potentially impacting multiple stakeholders across the supply network.
The cumulative effect of these disruptions often exceeds the immediate operational impact, as organizations must invest additional resources in recovery efforts, reputation management, and system redundancy improvements to prevent future occurrences and maintain stakeholder confidence.
Unlock deeper insights with PatSnap Eureka Quick Research — get a full tech report to explore trends and direct your research. Try now!
Generate Your Research Report Instantly with AI Agent
Supercharge your innovation with PatSnap Eureka AI Agent Platform!