How to Maximize Throughput in Access System Peak Usage
FEB 27, 20269 MIN READ
Generate Your Research Report Instantly with AI Agent
PatSnap Eureka helps you evaluate technical feasibility & market potential.
Access System Peak Throughput Background and Objectives
Access systems have evolved significantly over the past two decades, transforming from simple authentication mechanisms to complex, multi-layered infrastructures that serve millions of concurrent users. The evolution began with basic username-password systems in the early 2000s, progressed through multi-factor authentication implementations, and now encompasses sophisticated distributed architectures capable of handling massive scale operations. This technological progression has been driven by the exponential growth in digital services adoption and the increasing complexity of user access patterns.
The contemporary landscape presents unprecedented challenges as organizations face peak usage scenarios that can exceed normal traffic by 10-50 times during critical periods. These peak events, whether planned such as product launches and promotional campaigns, or unplanned like viral content distribution and emergency situations, expose the limitations of traditional access system architectures. The surge in remote work, mobile-first applications, and IoT device proliferation has further intensified the demand for robust, scalable access solutions.
Current access systems struggle with several fundamental bottlenecks during peak usage periods. Database connection limitations, authentication server capacity constraints, and network bandwidth restrictions create cascading failures that impact user experience and business operations. Traditional scaling approaches often prove inadequate when faced with sudden traffic spikes, leading to system timeouts, failed login attempts, and complete service unavailability.
The primary objective of maximizing throughput in access systems during peak usage centers on achieving seamless user authentication and authorization while maintaining system stability and security integrity. This involves developing architectures that can dynamically scale resources, implement intelligent load distribution, and maintain consistent response times regardless of concurrent user volume. The goal extends beyond mere capacity increase to encompass predictive scaling capabilities and automated resource optimization.
Secondary objectives include minimizing infrastructure costs through efficient resource utilization, ensuring compliance with security standards during high-load scenarios, and maintaining comprehensive audit trails for regulatory requirements. The solution must also provide real-time monitoring capabilities and automated failover mechanisms to prevent service disruptions. Additionally, the system should support graceful degradation strategies that prioritize critical functions when resources become constrained, ensuring that essential services remain operational even under extreme load conditions.
The contemporary landscape presents unprecedented challenges as organizations face peak usage scenarios that can exceed normal traffic by 10-50 times during critical periods. These peak events, whether planned such as product launches and promotional campaigns, or unplanned like viral content distribution and emergency situations, expose the limitations of traditional access system architectures. The surge in remote work, mobile-first applications, and IoT device proliferation has further intensified the demand for robust, scalable access solutions.
Current access systems struggle with several fundamental bottlenecks during peak usage periods. Database connection limitations, authentication server capacity constraints, and network bandwidth restrictions create cascading failures that impact user experience and business operations. Traditional scaling approaches often prove inadequate when faced with sudden traffic spikes, leading to system timeouts, failed login attempts, and complete service unavailability.
The primary objective of maximizing throughput in access systems during peak usage centers on achieving seamless user authentication and authorization while maintaining system stability and security integrity. This involves developing architectures that can dynamically scale resources, implement intelligent load distribution, and maintain consistent response times regardless of concurrent user volume. The goal extends beyond mere capacity increase to encompass predictive scaling capabilities and automated resource optimization.
Secondary objectives include minimizing infrastructure costs through efficient resource utilization, ensuring compliance with security standards during high-load scenarios, and maintaining comprehensive audit trails for regulatory requirements. The solution must also provide real-time monitoring capabilities and automated failover mechanisms to prevent service disruptions. Additionally, the system should support graceful degradation strategies that prioritize critical functions when resources become constrained, ensuring that essential services remain operational even under extreme load conditions.
Market Demand for High-Performance Access Systems
The global demand for high-performance access systems has experienced unprecedented growth driven by the exponential increase in data consumption and the proliferation of connected devices. Organizations across industries are grappling with network congestion during peak usage periods, creating substantial market opportunities for solutions that can effectively maximize throughput. This demand spans multiple sectors including telecommunications, enterprise networks, cloud service providers, and content delivery networks.
Enterprise organizations represent a significant portion of this market demand, particularly as remote work and digital transformation initiatives have intensified network traffic patterns. Companies are seeking access systems capable of handling simultaneous connections from hundreds or thousands of users without performance degradation. The shift toward cloud-based applications and services has further amplified the need for robust access infrastructure that can maintain consistent performance during peak operational hours.
Telecommunications service providers face mounting pressure to deliver superior user experiences while managing increasingly complex traffic loads. The deployment of advanced wireless technologies and the growing adoption of bandwidth-intensive applications have created critical requirements for access systems that can dynamically scale throughput based on real-time demand patterns. Service providers are actively investing in infrastructure upgrades to maintain competitive positioning and customer satisfaction.
The emergence of edge computing and Internet of Things deployments has generated new market segments requiring specialized high-performance access solutions. These applications demand ultra-low latency and high-throughput capabilities to support real-time data processing and decision-making. Industrial automation, smart city initiatives, and autonomous vehicle networks represent rapidly expanding market opportunities for advanced access system technologies.
Cloud service providers and content delivery networks constitute another major demand driver, as they require access systems capable of handling massive concurrent user loads while maintaining service quality guarantees. The increasing consumption of streaming media, online gaming, and interactive applications has created stringent performance requirements that traditional access systems struggle to meet during peak usage scenarios.
Market research indicates strong growth trajectories across all these segments, with organizations demonstrating willingness to invest significantly in access system upgrades that can deliver measurable throughput improvements and enhanced user experiences during critical peak usage periods.
Enterprise organizations represent a significant portion of this market demand, particularly as remote work and digital transformation initiatives have intensified network traffic patterns. Companies are seeking access systems capable of handling simultaneous connections from hundreds or thousands of users without performance degradation. The shift toward cloud-based applications and services has further amplified the need for robust access infrastructure that can maintain consistent performance during peak operational hours.
Telecommunications service providers face mounting pressure to deliver superior user experiences while managing increasingly complex traffic loads. The deployment of advanced wireless technologies and the growing adoption of bandwidth-intensive applications have created critical requirements for access systems that can dynamically scale throughput based on real-time demand patterns. Service providers are actively investing in infrastructure upgrades to maintain competitive positioning and customer satisfaction.
The emergence of edge computing and Internet of Things deployments has generated new market segments requiring specialized high-performance access solutions. These applications demand ultra-low latency and high-throughput capabilities to support real-time data processing and decision-making. Industrial automation, smart city initiatives, and autonomous vehicle networks represent rapidly expanding market opportunities for advanced access system technologies.
Cloud service providers and content delivery networks constitute another major demand driver, as they require access systems capable of handling massive concurrent user loads while maintaining service quality guarantees. The increasing consumption of streaming media, online gaming, and interactive applications has created stringent performance requirements that traditional access systems struggle to meet during peak usage scenarios.
Market research indicates strong growth trajectories across all these segments, with organizations demonstrating willingness to invest significantly in access system upgrades that can deliver measurable throughput improvements and enhanced user experiences during critical peak usage periods.
Current Throughput Bottlenecks and Technical Challenges
Access systems face multiple throughput bottlenecks during peak usage periods, primarily stemming from hardware limitations, software inefficiencies, and architectural constraints. The most critical bottleneck occurs at the network interface level, where bandwidth saturation creates cascading effects throughout the entire system infrastructure. Traditional access systems typically experience performance degradation when concurrent user connections exceed 70-80% of theoretical capacity, well before reaching absolute hardware limits.
Database connection pooling represents another significant constraint, as most access systems rely on relational databases that struggle with high-concurrency scenarios. Connection establishment overhead, lock contention, and query optimization failures compound during peak loads, creating exponential performance degradation rather than linear scaling. Legacy database architectures often become the primary limiting factor in modern high-throughput scenarios.
Memory management inefficiencies plague many access systems, particularly those handling session state and user authentication data. Inadequate garbage collection strategies, memory leaks in long-running processes, and insufficient buffer allocation lead to system instability during sustained high-load periods. These issues are exacerbated by the unpredictable nature of peak usage patterns, making capacity planning extremely challenging.
Load balancing algorithms present technical challenges in maintaining optimal resource distribution across multiple system nodes. Traditional round-robin and least-connection methods fail to account for varying request complexity and processing requirements, resulting in uneven load distribution and underutilized resources. Geographic distribution of users further complicates load balancing effectiveness, as network latency variations impact perceived system performance.
Authentication and authorization processes create significant bottlenecks due to cryptographic operations and external service dependencies. Multi-factor authentication, while enhancing security, introduces additional latency and processing overhead that scales poorly with user volume. Token validation, session management, and permission checking operations consume substantial computational resources during peak periods.
Caching strategies often prove inadequate for dynamic content and personalized user experiences. Cache invalidation complexity, memory constraints, and cache miss penalties during peak loads create performance inconsistencies. The challenge intensifies with geographically distributed systems where cache synchronization becomes a limiting factor.
Monitoring and observability limitations hinder real-time bottleneck identification and resolution. Insufficient granularity in performance metrics, delayed alerting systems, and inadequate correlation between system components prevent proactive optimization during critical peak usage periods.
Database connection pooling represents another significant constraint, as most access systems rely on relational databases that struggle with high-concurrency scenarios. Connection establishment overhead, lock contention, and query optimization failures compound during peak loads, creating exponential performance degradation rather than linear scaling. Legacy database architectures often become the primary limiting factor in modern high-throughput scenarios.
Memory management inefficiencies plague many access systems, particularly those handling session state and user authentication data. Inadequate garbage collection strategies, memory leaks in long-running processes, and insufficient buffer allocation lead to system instability during sustained high-load periods. These issues are exacerbated by the unpredictable nature of peak usage patterns, making capacity planning extremely challenging.
Load balancing algorithms present technical challenges in maintaining optimal resource distribution across multiple system nodes. Traditional round-robin and least-connection methods fail to account for varying request complexity and processing requirements, resulting in uneven load distribution and underutilized resources. Geographic distribution of users further complicates load balancing effectiveness, as network latency variations impact perceived system performance.
Authentication and authorization processes create significant bottlenecks due to cryptographic operations and external service dependencies. Multi-factor authentication, while enhancing security, introduces additional latency and processing overhead that scales poorly with user volume. Token validation, session management, and permission checking operations consume substantial computational resources during peak periods.
Caching strategies often prove inadequate for dynamic content and personalized user experiences. Cache invalidation complexity, memory constraints, and cache miss penalties during peak loads create performance inconsistencies. The challenge intensifies with geographically distributed systems where cache synchronization becomes a limiting factor.
Monitoring and observability limitations hinder real-time bottleneck identification and resolution. Insufficient granularity in performance metrics, delayed alerting systems, and inadequate correlation between system components prevent proactive optimization during critical peak usage periods.
Existing Throughput Maximization Solutions
01 Dynamic bandwidth allocation and resource management
Access system throughput can be improved through dynamic allocation of bandwidth and network resources based on real-time traffic demands. This involves monitoring network conditions and adjusting resource distribution to optimize data transmission rates. Adaptive scheduling algorithms and quality of service mechanisms ensure efficient utilization of available capacity while maintaining performance standards across multiple users and applications.- Dynamic bandwidth allocation and resource management: Access system throughput can be improved through dynamic allocation of bandwidth and network resources based on real-time traffic demands. This involves monitoring network conditions and adjusting resource distribution to optimize data transmission rates. Adaptive scheduling algorithms and quality of service mechanisms ensure efficient utilization of available capacity while maintaining performance standards across multiple users and applications.
- Multi-channel and parallel processing techniques: Throughput enhancement can be achieved by implementing multi-channel communication and parallel data processing architectures. These systems utilize multiple transmission paths simultaneously to increase aggregate data rates. Load balancing across channels and coordinated transmission scheduling help maximize overall system capacity while reducing bottlenecks and latency in high-traffic scenarios.
- Advanced modulation and coding schemes: System throughput can be increased through the implementation of sophisticated modulation techniques and error correction coding. Adaptive modulation adjusts signal encoding based on channel conditions to maximize data rates while maintaining acceptable error rates. Forward error correction and advanced coding algorithms improve spectral efficiency and enable higher throughput under varying signal quality conditions.
- Access control and collision avoidance mechanisms: Throughput optimization involves implementing efficient medium access control protocols and collision avoidance strategies. These mechanisms coordinate transmission timing among multiple users to minimize interference and retransmissions. Priority-based access schemes and contention resolution algorithms ensure fair resource allocation while maximizing overall system efficiency and reducing overhead from failed transmission attempts.
- Caching and data optimization strategies: Access system throughput can be enhanced through intelligent caching mechanisms and data optimization techniques. Pre-fetching frequently accessed content and storing it closer to end users reduces transmission delays and network congestion. Data compression, deduplication, and protocol optimization further improve effective throughput by reducing the volume of data that needs to be transmitted across the network.
02 Multi-channel and parallel processing techniques
Throughput enhancement can be achieved by implementing multi-channel communication and parallel processing architectures. These systems utilize multiple transmission paths simultaneously to increase aggregate data rates. Load balancing across channels and coordinated transmission scheduling help maximize overall system capacity while reducing bottlenecks and latency in high-traffic scenarios.Expand Specific Solutions03 Advanced modulation and coding schemes
System throughput can be optimized through the implementation of sophisticated modulation and error correction coding techniques. Adaptive modulation adjusts signal encoding based on channel conditions to maximize data rates while maintaining acceptable error rates. Forward error correction and advanced coding algorithms improve spectral efficiency and enable higher throughput under varying signal quality conditions.Expand Specific Solutions04 Traffic prioritization and queue management
Effective throughput management involves implementing intelligent traffic prioritization and queue management strategies. These systems classify data packets based on priority levels and application requirements, ensuring critical traffic receives preferential treatment. Buffer management and congestion control mechanisms prevent packet loss and maintain optimal flow rates during peak usage periods.Expand Specific Solutions05 Protocol optimization and overhead reduction
Access system throughput can be increased by optimizing communication protocols and minimizing transmission overhead. This includes streamlining header information, reducing acknowledgment traffic, and implementing efficient handshaking mechanisms. Protocol enhancements such as packet aggregation and compressed signaling reduce the ratio of control data to payload, thereby improving effective data transmission rates.Expand Specific Solutions
Key Players in Access System and Network Infrastructure
The access system throughput maximization market represents a mature, high-growth sector driven by exponential data demands and 5G/6G transitions. The competitive landscape spans multiple technology layers, from semiconductor foundations to cloud infrastructure solutions. Market leaders like Qualcomm, Huawei, and NVIDIA demonstrate advanced technological maturity through comprehensive patent portfolios and integrated hardware-software solutions. Traditional infrastructure giants including IBM, Microsoft, and Cisco leverage decades of enterprise experience, while telecommunications operators like T-Mobile and China Mobile drive real-world implementation requirements. Emerging players such as ChangXin Memory Technologies indicate continued innovation in specialized components. The technology maturity varies significantly across segments, with established networking protocols reaching optimization phases while AI-driven optimization and edge computing integration remain in rapid development stages, creating diverse competitive opportunities.
QUALCOMM, Inc.
Technical Solution: QUALCOMM employs advanced carrier aggregation and MIMO technologies to maximize throughput during peak usage periods. Their Snapdragon X series modems support up to 10 Gbps download speeds through 5G mmWave and sub-6 GHz spectrum aggregation. The company implements intelligent traffic management algorithms that dynamically allocate bandwidth based on real-time network conditions and user demand patterns. Their solutions include adaptive beamforming, interference cancellation, and multi-user MIMO capabilities that can serve multiple users simultaneously without significant throughput degradation. Additionally, QUALCOMM's network slicing technology allows operators to create dedicated virtual networks for different service types, ensuring critical applications maintain performance during peak hours.
Strengths: Industry-leading 5G modem technology, comprehensive spectrum aggregation capabilities, strong patent portfolio in wireless communications. Weaknesses: High licensing costs, dependency on semiconductor manufacturing partners, limited control over network infrastructure deployment.
Huawei Technologies Co., Ltd.
Technical Solution: Huawei's approach to maximizing access system throughput centers on their Massive MIMO and CloudAIR technologies. Their base stations can support up to 320 antenna elements, significantly increasing spectral efficiency and user capacity during peak periods. The company's intelligent resource scheduling algorithms use machine learning to predict traffic patterns and pre-allocate resources accordingly. Huawei's CloudRAN architecture enables centralized processing and dynamic resource pooling across multiple cell sites, allowing load balancing during peak usage. Their solutions also incorporate advanced interference coordination techniques and real-time optimization of transmission parameters to maintain high throughput even under heavy network load conditions.
Strengths: Advanced Massive MIMO technology, comprehensive end-to-end network solutions, strong R&D capabilities in wireless infrastructure. Weaknesses: Geopolitical restrictions limiting market access, concerns about security and data privacy in some regions.
Core Technologies for Peak Usage Optimization
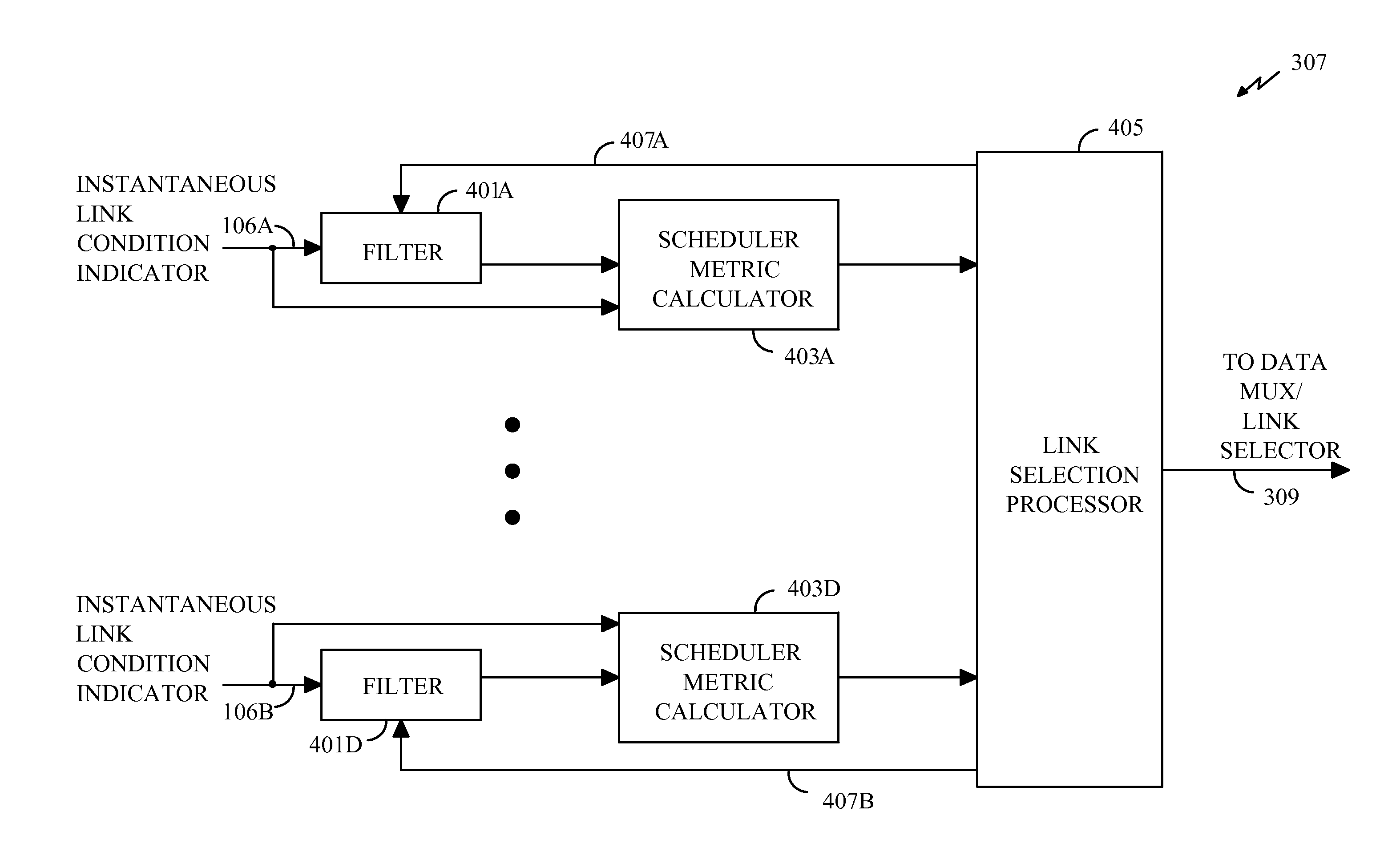
Method and System for Scheduling Data Transmission in Communication Systems
PatentInactiveUS20070091841A1
Innovation
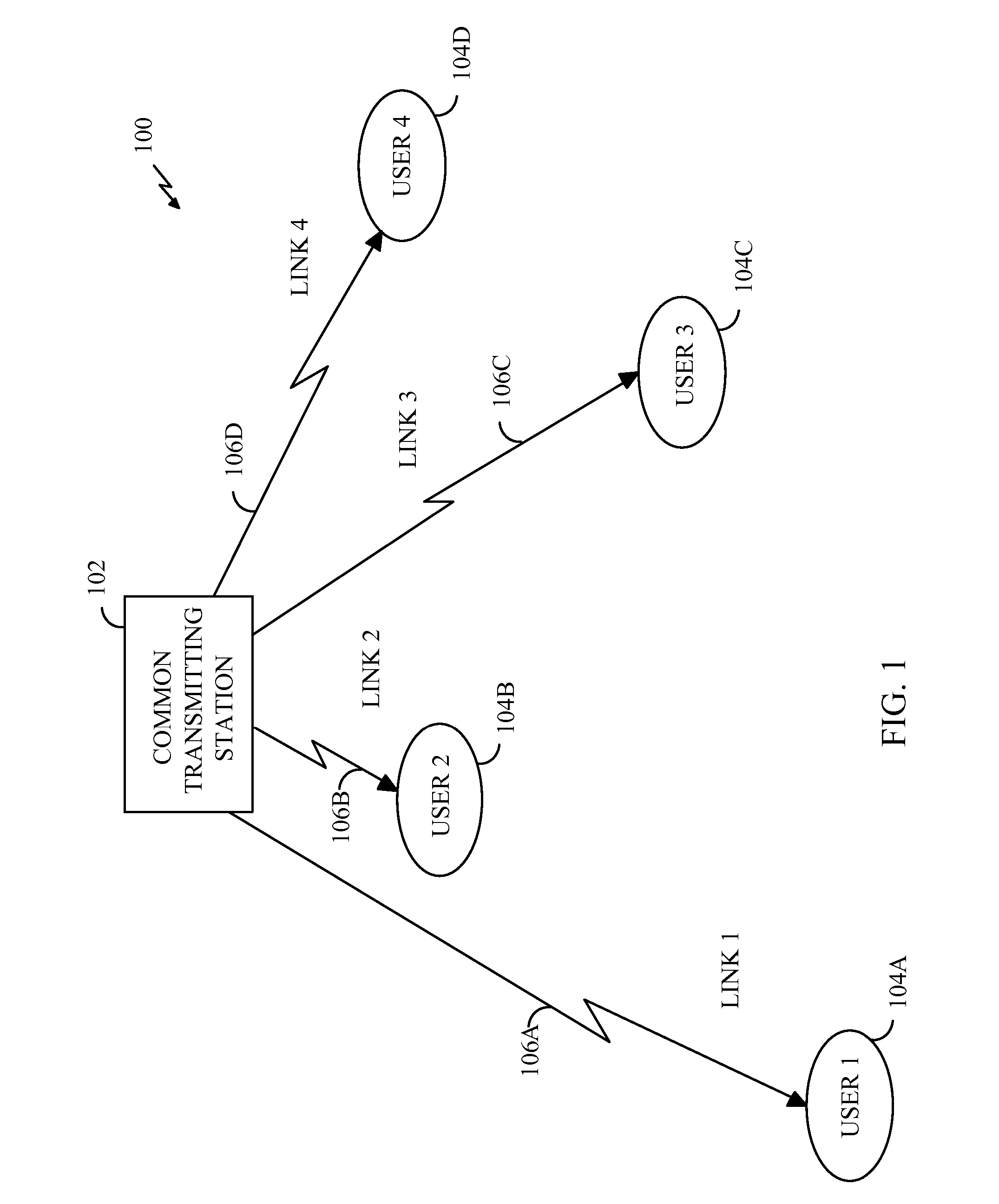
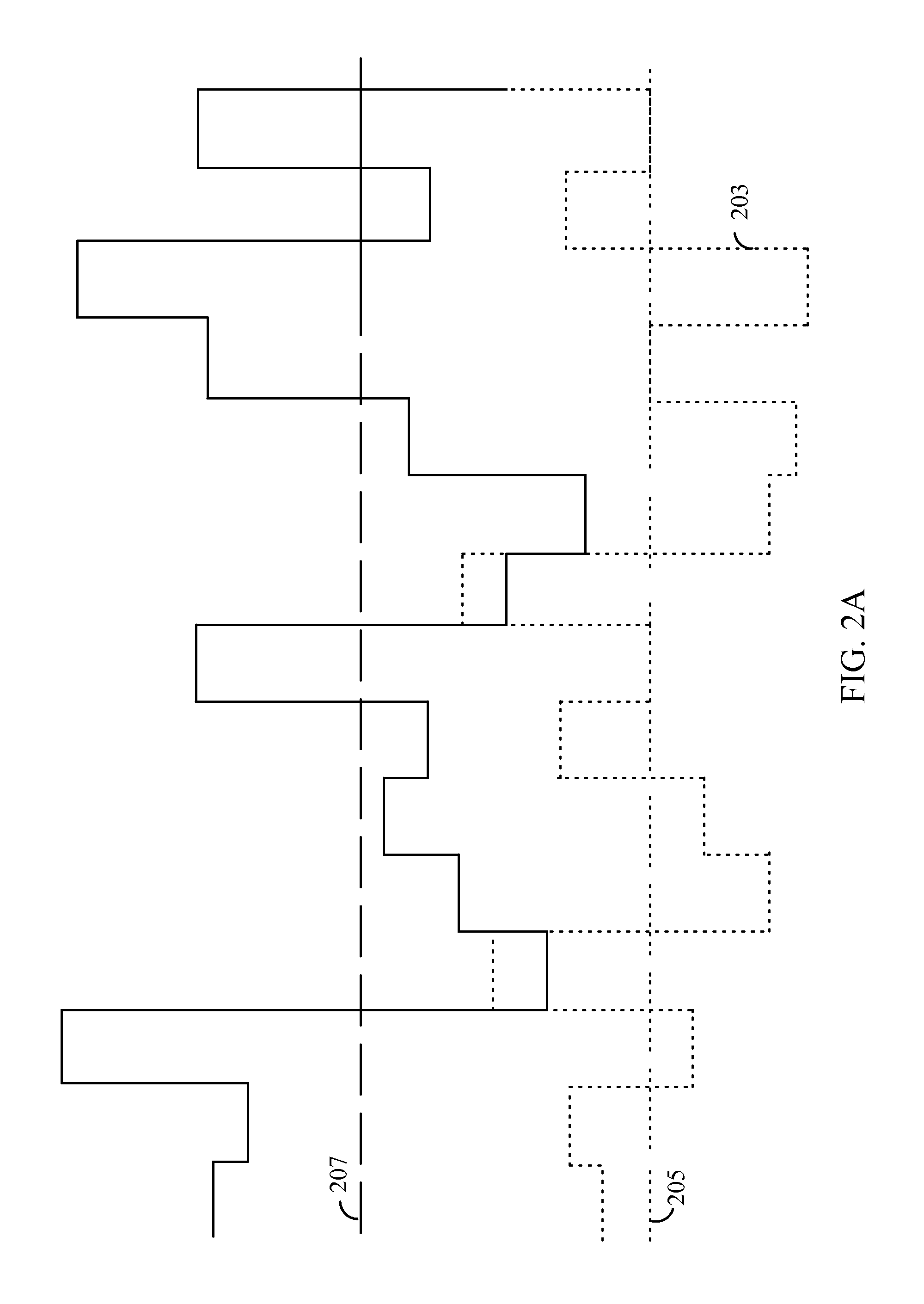
- A transmitter-directed communication system employing multi-user diversity, which uses scheduling algorithms to select users based on instantaneous link quality relative to average conditions, ensuring fair access and maximizing throughput by transmitting data to users with the best channel conditions at any given time.
Transmitter directed code division multiple access system using path diversity to equitably maximize throughput
PatentInactiveUS7123922B2
Innovation
- A transmitter-directed communication system utilizing path diversity, where receivers are uniquely located to provide uncorrelated channel conditions, uses instantaneous channel condition indicators to determine the best time to transmit to each user, balancing fairness and throughput by selecting channels with the highest instantaneous condition relative to average conditions, and employing a low-pass filter to maintain equitable access over a defined time scale.
Network Performance Standards and Compliance
Network performance standards and compliance frameworks play a critical role in maximizing throughput during access system peak usage periods. Industry-standard benchmarks such as ITU-T recommendations, IEEE 802.11 specifications, and 3GPP standards establish baseline performance metrics that guide system optimization strategies. These standards define acceptable latency thresholds, packet loss rates, and minimum throughput requirements that access systems must maintain even under heavy load conditions.
Compliance with Quality of Service (QoS) standards becomes particularly crucial during peak usage scenarios. The implementation of traffic classification mechanisms according to DSCP markings and IEEE 802.1p priority queuing ensures that critical applications receive adequate bandwidth allocation. Network operators must adhere to Service Level Agreement (SLA) requirements that typically specify 99.9% uptime and maximum response times, necessitating robust performance monitoring and automated failover mechanisms.
Regulatory compliance frameworks such as FCC Part 15 rules and ETSI standards impose specific constraints on spectrum utilization and interference management. These regulations directly impact throughput optimization strategies, requiring careful balance between maximizing data rates and maintaining compliance with power emission limits and channel allocation requirements.
Performance measurement standards like RFC 2544 and Y.1564 provide standardized methodologies for throughput testing and validation. These frameworks enable consistent evaluation of access system performance under various load conditions, facilitating accurate capacity planning and optimization decisions. Regular compliance testing ensures that implemented solutions maintain their effectiveness as network conditions evolve.
Modern access systems must also comply with emerging standards for network slicing and edge computing, which introduce new performance requirements for ultra-low latency applications. The integration of these compliance requirements into throughput optimization strategies ensures sustainable performance improvements while maintaining regulatory adherence and service quality commitments across diverse user scenarios and application types.
Compliance with Quality of Service (QoS) standards becomes particularly crucial during peak usage scenarios. The implementation of traffic classification mechanisms according to DSCP markings and IEEE 802.1p priority queuing ensures that critical applications receive adequate bandwidth allocation. Network operators must adhere to Service Level Agreement (SLA) requirements that typically specify 99.9% uptime and maximum response times, necessitating robust performance monitoring and automated failover mechanisms.
Regulatory compliance frameworks such as FCC Part 15 rules and ETSI standards impose specific constraints on spectrum utilization and interference management. These regulations directly impact throughput optimization strategies, requiring careful balance between maximizing data rates and maintaining compliance with power emission limits and channel allocation requirements.
Performance measurement standards like RFC 2544 and Y.1564 provide standardized methodologies for throughput testing and validation. These frameworks enable consistent evaluation of access system performance under various load conditions, facilitating accurate capacity planning and optimization decisions. Regular compliance testing ensures that implemented solutions maintain their effectiveness as network conditions evolve.
Modern access systems must also comply with emerging standards for network slicing and edge computing, which introduce new performance requirements for ultra-low latency applications. The integration of these compliance requirements into throughput optimization strategies ensures sustainable performance improvements while maintaining regulatory adherence and service quality commitments across diverse user scenarios and application types.
Quality of Service Management in Peak Traffic
Quality of Service (QoS) management becomes critically important during peak traffic periods when access systems face maximum load conditions. Effective QoS strategies ensure that network resources are allocated efficiently while maintaining acceptable service levels for different user classes and application types. The fundamental challenge lies in balancing competing demands for limited bandwidth and processing resources while preventing system degradation.
Traffic classification and prioritization form the cornerstone of peak-period QoS management. Systems must implement intelligent classification mechanisms that can rapidly identify and categorize different traffic types based on application signatures, user profiles, and service level agreements. Real-time applications such as voice and video communications require immediate priority handling, while bulk data transfers can tolerate controlled delays during congestion periods.
Dynamic bandwidth allocation mechanisms play a crucial role in managing peak traffic scenarios. Advanced QoS systems employ adaptive algorithms that continuously monitor network conditions and adjust resource allocation in real-time. These systems implement sophisticated queuing disciplines, including weighted fair queuing and class-based queuing, to ensure that high-priority traffic maintains acceptable performance levels even when total demand exceeds available capacity.
Congestion control strategies must be proactive rather than reactive during peak usage periods. Effective QoS management incorporates admission control policies that prevent system overload by selectively accepting or deferring new connection requests based on current resource availability and service commitments. Traffic shaping and policing mechanisms ensure that individual users or applications cannot monopolize system resources at the expense of overall performance.
Service differentiation becomes essential when managing diverse application requirements during peak periods. QoS frameworks must support multiple service classes with distinct performance guarantees, including guaranteed bandwidth, maximum latency bounds, and packet loss thresholds. This differentiation enables systems to maintain critical service quality for premium applications while gracefully degrading less critical services when necessary.
Monitoring and feedback mechanisms provide essential visibility into QoS performance during peak traffic conditions. Real-time analytics enable network administrators to identify bottlenecks, track service level compliance, and implement corrective actions before user experience degrades significantly. These systems must provide granular visibility into per-class performance metrics and support automated policy adjustments based on predefined thresholds and business rules.
Traffic classification and prioritization form the cornerstone of peak-period QoS management. Systems must implement intelligent classification mechanisms that can rapidly identify and categorize different traffic types based on application signatures, user profiles, and service level agreements. Real-time applications such as voice and video communications require immediate priority handling, while bulk data transfers can tolerate controlled delays during congestion periods.
Dynamic bandwidth allocation mechanisms play a crucial role in managing peak traffic scenarios. Advanced QoS systems employ adaptive algorithms that continuously monitor network conditions and adjust resource allocation in real-time. These systems implement sophisticated queuing disciplines, including weighted fair queuing and class-based queuing, to ensure that high-priority traffic maintains acceptable performance levels even when total demand exceeds available capacity.
Congestion control strategies must be proactive rather than reactive during peak usage periods. Effective QoS management incorporates admission control policies that prevent system overload by selectively accepting or deferring new connection requests based on current resource availability and service commitments. Traffic shaping and policing mechanisms ensure that individual users or applications cannot monopolize system resources at the expense of overall performance.
Service differentiation becomes essential when managing diverse application requirements during peak periods. QoS frameworks must support multiple service classes with distinct performance guarantees, including guaranteed bandwidth, maximum latency bounds, and packet loss thresholds. This differentiation enables systems to maintain critical service quality for premium applications while gracefully degrading less critical services when necessary.
Monitoring and feedback mechanisms provide essential visibility into QoS performance during peak traffic conditions. Real-time analytics enable network administrators to identify bottlenecks, track service level compliance, and implement corrective actions before user experience degrades significantly. These systems must provide granular visibility into per-class performance metrics and support automated policy adjustments based on predefined thresholds and business rules.
Unlock deeper insights with PatSnap Eureka Quick Research — get a full tech report to explore trends and direct your research. Try now!
Generate Your Research Report Instantly with AI Agent
Supercharge your innovation with PatSnap Eureka AI Agent Platform!