Comparing Encryption Techniques for Connected Vehicle Data
MAR 5, 20269 MIN READ
Generate Your Research Report Instantly with AI Agent
PatSnap Eureka helps you evaluate technical feasibility & market potential.
Connected Vehicle Encryption Background and Objectives
Connected vehicles represent a paradigm shift in automotive technology, fundamentally transforming how vehicles communicate with infrastructure, other vehicles, and cloud-based services. This revolutionary ecosystem, commonly referred to as Vehicle-to-Everything (V2X) communication, encompasses Vehicle-to-Vehicle (V2V), Vehicle-to-Infrastructure (V2I), Vehicle-to-Network (V2N), and Vehicle-to-Pedestrian (V2P) interactions. The evolution from isolated mechanical systems to interconnected intelligent platforms has created unprecedented opportunities for enhanced safety, traffic optimization, and autonomous driving capabilities.
The historical development of connected vehicle technology traces back to early telematics systems in the 1990s, progressing through GPS-enabled navigation systems, cellular-based emergency services, and eventually evolving into today's sophisticated multi-protocol communication networks. Modern connected vehicles generate and exchange vast amounts of sensitive data, including real-time location information, driving patterns, biometric data, personal preferences, and critical safety messages that directly impact vehicle operation and passenger safety.
The exponential growth in data generation and exchange has intensified security concerns, making robust encryption techniques absolutely critical for protecting both individual privacy and overall system integrity. Current connected vehicles can generate up to 25 gigabytes of data per hour, creating massive attack surfaces that malicious actors could potentially exploit. The consequences of inadequate encryption extend beyond privacy violations to include life-threatening scenarios where compromised safety-critical communications could result in accidents or system-wide transportation disruptions.
The primary objective of implementing advanced encryption techniques in connected vehicle ecosystems is to establish a comprehensive security framework that ensures data confidentiality, integrity, authentication, and non-repudiation across all communication channels. This framework must address the unique challenges posed by vehicular networks, including high mobility, intermittent connectivity, real-time communication requirements, and resource constraints inherent in automotive computing environments.
Achieving optimal encryption implementation requires balancing multiple competing factors: computational efficiency to meet real-time processing demands, energy consumption considerations for battery-powered systems, scalability to accommodate millions of connected vehicles, and interoperability across diverse manufacturers and communication protocols. The ultimate goal is developing encryption solutions that provide robust security without compromising the performance, reliability, and user experience that modern connected vehicle applications demand.
The historical development of connected vehicle technology traces back to early telematics systems in the 1990s, progressing through GPS-enabled navigation systems, cellular-based emergency services, and eventually evolving into today's sophisticated multi-protocol communication networks. Modern connected vehicles generate and exchange vast amounts of sensitive data, including real-time location information, driving patterns, biometric data, personal preferences, and critical safety messages that directly impact vehicle operation and passenger safety.
The exponential growth in data generation and exchange has intensified security concerns, making robust encryption techniques absolutely critical for protecting both individual privacy and overall system integrity. Current connected vehicles can generate up to 25 gigabytes of data per hour, creating massive attack surfaces that malicious actors could potentially exploit. The consequences of inadequate encryption extend beyond privacy violations to include life-threatening scenarios where compromised safety-critical communications could result in accidents or system-wide transportation disruptions.
The primary objective of implementing advanced encryption techniques in connected vehicle ecosystems is to establish a comprehensive security framework that ensures data confidentiality, integrity, authentication, and non-repudiation across all communication channels. This framework must address the unique challenges posed by vehicular networks, including high mobility, intermittent connectivity, real-time communication requirements, and resource constraints inherent in automotive computing environments.
Achieving optimal encryption implementation requires balancing multiple competing factors: computational efficiency to meet real-time processing demands, energy consumption considerations for battery-powered systems, scalability to accommodate millions of connected vehicles, and interoperability across diverse manufacturers and communication protocols. The ultimate goal is developing encryption solutions that provide robust security without compromising the performance, reliability, and user experience that modern connected vehicle applications demand.
Market Demand for Secure Vehicle Data Transmission
The global automotive industry is experiencing unprecedented transformation driven by the proliferation of connected vehicles, autonomous driving technologies, and vehicle-to-everything communication systems. This technological evolution has created substantial market demand for robust data security solutions, as modern vehicles generate and transmit vast amounts of sensitive information including location data, driving patterns, personal preferences, and vehicle diagnostics.
Connected vehicles are projected to become the dominant vehicle type across major automotive markets, with manufacturers increasingly integrating advanced telematics systems, over-the-air update capabilities, and cloud-based services. This connectivity expansion directly correlates with growing security vulnerabilities, creating urgent market demand for sophisticated encryption solutions that can protect data integrity during transmission between vehicles, infrastructure, and cloud platforms.
The automotive cybersecurity market has emerged as a critical segment, driven by stringent regulatory requirements and consumer privacy concerns. Government agencies worldwide are implementing comprehensive cybersecurity standards for connected vehicles, mandating encryption protocols for data transmission. These regulatory frameworks are accelerating market adoption of advanced encryption technologies, as automotive manufacturers must comply with security standards to maintain market access.
Fleet operators and commercial vehicle segments represent particularly strong demand drivers for secure data transmission solutions. These operators rely heavily on real-time vehicle monitoring, route optimization, and predictive maintenance systems that require continuous data exchange. The economic value of protecting operational data and preventing cyber attacks has made encryption investment a strategic priority for fleet management companies.
Consumer awareness regarding data privacy has significantly influenced market dynamics. Vehicle owners increasingly demand transparency about data collection practices and expect robust protection of personal information. This consumer pressure has prompted automotive manufacturers to prioritize encryption capabilities as competitive differentiators, driving market demand for comprehensive security solutions.
The emergence of vehicle-as-a-service models and shared mobility platforms has further intensified security requirements. These business models involve multiple stakeholders accessing vehicle data, creating complex security challenges that require sophisticated encryption frameworks to maintain data confidentiality across different user groups and service providers.
Insurance companies and financial service providers are also driving market demand through their integration with connected vehicle ecosystems. Usage-based insurance models and vehicle financing solutions require secure transmission of driving behavior data and vehicle performance metrics, creating additional market opportunities for encryption technology providers.
Connected vehicles are projected to become the dominant vehicle type across major automotive markets, with manufacturers increasingly integrating advanced telematics systems, over-the-air update capabilities, and cloud-based services. This connectivity expansion directly correlates with growing security vulnerabilities, creating urgent market demand for sophisticated encryption solutions that can protect data integrity during transmission between vehicles, infrastructure, and cloud platforms.
The automotive cybersecurity market has emerged as a critical segment, driven by stringent regulatory requirements and consumer privacy concerns. Government agencies worldwide are implementing comprehensive cybersecurity standards for connected vehicles, mandating encryption protocols for data transmission. These regulatory frameworks are accelerating market adoption of advanced encryption technologies, as automotive manufacturers must comply with security standards to maintain market access.
Fleet operators and commercial vehicle segments represent particularly strong demand drivers for secure data transmission solutions. These operators rely heavily on real-time vehicle monitoring, route optimization, and predictive maintenance systems that require continuous data exchange. The economic value of protecting operational data and preventing cyber attacks has made encryption investment a strategic priority for fleet management companies.
Consumer awareness regarding data privacy has significantly influenced market dynamics. Vehicle owners increasingly demand transparency about data collection practices and expect robust protection of personal information. This consumer pressure has prompted automotive manufacturers to prioritize encryption capabilities as competitive differentiators, driving market demand for comprehensive security solutions.
The emergence of vehicle-as-a-service models and shared mobility platforms has further intensified security requirements. These business models involve multiple stakeholders accessing vehicle data, creating complex security challenges that require sophisticated encryption frameworks to maintain data confidentiality across different user groups and service providers.
Insurance companies and financial service providers are also driving market demand through their integration with connected vehicle ecosystems. Usage-based insurance models and vehicle financing solutions require secure transmission of driving behavior data and vehicle performance metrics, creating additional market opportunities for encryption technology providers.
Current Encryption Challenges in Connected Vehicles
Connected vehicles face unprecedented encryption challenges as they generate and transmit massive volumes of sensitive data across multiple communication channels. The automotive industry's rapid digitization has created a complex ecosystem where vehicles continuously exchange information with infrastructure, other vehicles, cloud services, and mobile devices, making data protection a critical concern.
The heterogeneous nature of connected vehicle networks presents significant encryption complexity. Vehicles must simultaneously handle Vehicle-to-Vehicle (V2V), Vehicle-to-Infrastructure (V2I), Vehicle-to-Cloud (V2C), and Vehicle-to-Everything (V2X) communications, each requiring different encryption protocols and security levels. This multi-layered communication architecture creates interoperability challenges when implementing consistent encryption standards across diverse platforms and manufacturers.
Real-time processing requirements impose severe constraints on encryption implementation. Connected vehicles demand ultra-low latency for safety-critical applications such as collision avoidance and emergency braking systems. Traditional encryption methods often introduce computational overhead that conflicts with the millisecond response times required for autonomous driving functions, forcing engineers to balance security strength against performance requirements.
Resource limitations in automotive Electronic Control Units (ECUs) create additional encryption barriers. Many existing vehicle components operate with limited processing power, memory, and energy resources, making it challenging to implement robust encryption algorithms without compromising system performance or battery life in electric vehicles.
Key management represents another fundamental challenge in connected vehicle encryption. The dynamic nature of vehicular networks, where vehicles constantly join and leave communication groups, requires sophisticated key distribution and rotation mechanisms. Establishing secure communication channels between previously unknown vehicles while maintaining privacy and preventing unauthorized access demands innovative cryptographic solutions.
Legacy system integration poses significant obstacles for encryption deployment. The automotive industry's long product lifecycles mean that new encryption technologies must coexist with older systems that may lack adequate security features. This creates vulnerabilities in the overall security architecture and complicates the implementation of end-to-end encryption across the entire vehicle ecosystem.
Regulatory compliance adds another layer of complexity to encryption challenges. Different regions impose varying data protection requirements, privacy regulations, and cybersecurity standards, forcing manufacturers to develop flexible encryption frameworks that can adapt to multiple jurisdictional requirements while maintaining consistent security levels globally.
The heterogeneous nature of connected vehicle networks presents significant encryption complexity. Vehicles must simultaneously handle Vehicle-to-Vehicle (V2V), Vehicle-to-Infrastructure (V2I), Vehicle-to-Cloud (V2C), and Vehicle-to-Everything (V2X) communications, each requiring different encryption protocols and security levels. This multi-layered communication architecture creates interoperability challenges when implementing consistent encryption standards across diverse platforms and manufacturers.
Real-time processing requirements impose severe constraints on encryption implementation. Connected vehicles demand ultra-low latency for safety-critical applications such as collision avoidance and emergency braking systems. Traditional encryption methods often introduce computational overhead that conflicts with the millisecond response times required for autonomous driving functions, forcing engineers to balance security strength against performance requirements.
Resource limitations in automotive Electronic Control Units (ECUs) create additional encryption barriers. Many existing vehicle components operate with limited processing power, memory, and energy resources, making it challenging to implement robust encryption algorithms without compromising system performance or battery life in electric vehicles.
Key management represents another fundamental challenge in connected vehicle encryption. The dynamic nature of vehicular networks, where vehicles constantly join and leave communication groups, requires sophisticated key distribution and rotation mechanisms. Establishing secure communication channels between previously unknown vehicles while maintaining privacy and preventing unauthorized access demands innovative cryptographic solutions.
Legacy system integration poses significant obstacles for encryption deployment. The automotive industry's long product lifecycles mean that new encryption technologies must coexist with older systems that may lack adequate security features. This creates vulnerabilities in the overall security architecture and complicates the implementation of end-to-end encryption across the entire vehicle ecosystem.
Regulatory compliance adds another layer of complexity to encryption challenges. Different regions impose varying data protection requirements, privacy regulations, and cybersecurity standards, forcing manufacturers to develop flexible encryption frameworks that can adapt to multiple jurisdictional requirements while maintaining consistent security levels globally.
Existing Encryption Solutions for Vehicle Communications
01 Symmetric and asymmetric encryption algorithms
Encryption techniques utilize both symmetric and asymmetric cryptographic algorithms to secure data. Symmetric encryption uses the same key for both encryption and decryption, providing fast processing for large data volumes. Asymmetric encryption employs public and private key pairs, offering enhanced security for key exchange and digital signatures. These algorithms can be combined in hybrid systems to leverage the advantages of both approaches, ensuring confidentiality and integrity of sensitive information across various applications.- Symmetric and asymmetric encryption algorithms: Encryption techniques utilize both symmetric and asymmetric cryptographic algorithms to secure data. Symmetric encryption uses the same key for both encryption and decryption, providing fast processing for large data volumes. Asymmetric encryption employs public and private key pairs, enabling secure key exchange and digital signatures. These algorithms form the foundation of modern encryption systems and can be implemented in various combinations to balance security and performance requirements.
- Homomorphic and quantum-resistant encryption: Advanced encryption methods include homomorphic encryption that allows computations on encrypted data without decryption, and quantum-resistant algorithms designed to withstand attacks from quantum computers. These techniques address emerging security challenges in cloud computing and future-proof cryptographic systems against quantum threats. Implementation involves complex mathematical structures and novel cryptographic primitives that maintain data confidentiality while enabling processing.
- Key management and distribution systems: Secure key management encompasses generation, storage, distribution, and rotation of cryptographic keys throughout their lifecycle. These systems implement protocols for secure key exchange, hierarchical key structures, and hardware security modules for key protection. Effective key management ensures that encryption keys remain confidential and are properly distributed among authorized parties while preventing unauthorized access.
- Block cipher and stream cipher implementations: Encryption implementations utilize block ciphers that process fixed-size data blocks and stream ciphers that encrypt data continuously. Block cipher modes of operation provide different security properties for various applications, while stream ciphers offer efficient encryption for real-time data transmission. These implementations can be optimized for hardware or software environments and include padding schemes and initialization vectors for enhanced security.
- Authentication and integrity verification mechanisms: Encryption systems incorporate authentication mechanisms to verify data origin and integrity verification to detect unauthorized modifications. These include message authentication codes, digital signatures, and hash functions that work in conjunction with encryption algorithms. The combination of encryption with authentication provides comprehensive security by ensuring both confidentiality and authenticity of transmitted or stored data.
02 Homomorphic encryption for secure computation
Homomorphic encryption enables computations to be performed directly on encrypted data without requiring decryption, preserving privacy throughout the processing. This technique allows third parties to process sensitive information while maintaining confidentiality, making it particularly valuable for cloud computing and data analytics applications. The technology supports various mathematical operations on ciphertext, with results that remain encrypted and can be decrypted only by authorized parties holding the appropriate keys.Expand Specific Solutions03 Quantum-resistant cryptographic methods
Advanced encryption techniques incorporate quantum-resistant algorithms designed to withstand attacks from quantum computers. These methods utilize mathematical problems that remain computationally difficult even for quantum systems, such as lattice-based cryptography and hash-based signatures. Implementation of post-quantum cryptographic standards ensures long-term security of encrypted data against emerging quantum computing threats, providing future-proof protection for critical information infrastructure.Expand Specific Solutions04 Block cipher and stream cipher implementations
Encryption systems employ block ciphers that process fixed-size data blocks and stream ciphers that encrypt data continuously bit-by-bit or byte-by-byte. Block cipher modes of operation provide different security properties and performance characteristics for various use cases. Stream ciphers offer advantages in real-time communications and resource-constrained environments. These cipher implementations incorporate techniques such as substitution-permutation networks, key scheduling algorithms, and initialization vectors to achieve robust encryption strength.Expand Specific Solutions05 Key management and secure key exchange protocols
Effective encryption relies on secure key management systems that handle generation, distribution, storage, and rotation of cryptographic keys. Key exchange protocols enable secure establishment of shared secrets between parties over insecure channels, utilizing techniques such as Diffie-Hellman key exchange and elliptic curve cryptography. These systems incorporate hardware security modules, key derivation functions, and multi-factor authentication to protect keys throughout their lifecycle and prevent unauthorized access to encrypted data.Expand Specific Solutions
Key Players in Automotive Cybersecurity Industry
The connected vehicle data encryption landscape represents a rapidly evolving sector within the broader automotive cybersecurity market, currently valued at approximately $5.8 billion and projected to reach $14.9 billion by 2030. The industry is in a transitional phase, moving from traditional automotive manufacturing toward software-defined vehicles with advanced connectivity features. Technology maturity varies significantly across market participants, with established telecommunications companies like Huawei Technologies demonstrating advanced encryption capabilities, while traditional automakers including Geely Holding Group, Chery Automobile, Mercedes-Benz Group, Hyundai Motor, and Kia Corp are rapidly integrating sophisticated security solutions. Chinese manufacturers such as Guangzhou Automobile Group and Beijing Electric Vehicle Co. are particularly aggressive in implementing next-generation encryption protocols. Research institutions like Beijing Institute of Technology and Chongqing University of Posts & Telecommunications are driving innovation in quantum-resistant encryption methods, while specialized technology firms including Beijing Shudun Information Technology are developing enterprise-grade cryptographic solutions specifically for automotive applications, indicating a maturing but still fragmented competitive environment.
Zhejiang Geely Holding Group Co., Ltd.
Technical Solution: Geely has implemented the GKUI (Geely Keyless User Interface) security platform incorporating multiple encryption layers for connected vehicle data protection. Their system utilizes AES-256 encryption for vehicle data transmission and storage, combined with RSA-based public key infrastructure for secure device authentication. The platform features end-to-end encryption for vehicle-to-cloud communications and implements secure element technology for cryptographic key management. Geely's approach includes integration with their proprietary satellite constellation for secure global connectivity and encrypted emergency services. The company has also developed lightweight encryption protocols optimized for their electric vehicle platforms, ensuring minimal impact on battery performance while maintaining robust security standards.
Strengths: Cost-effective solutions and rapid deployment capabilities in Chinese market. Weaknesses: Limited global standardization compliance and newer technology maturity concerns.
GM Global Technology Operations LLC
Technical Solution: General Motors has implemented OnStar Guardian security platform featuring multi-layered encryption architecture for connected vehicle data protection. Their system employs AES-128/256 encryption for vehicle telemetry data transmission and RSA-2048 for secure authentication protocols. GM's approach includes dedicated security gateways within vehicle electronic control units (ECUs) that isolate critical systems from external communications. The company utilizes Transport Layer Security (TLS) 1.3 for secure cloud connectivity and implements certificate-based authentication for vehicle-to-infrastructure communications. Their encryption strategy also includes secure boot processes and encrypted storage for sensitive vehicle configuration data.
Strengths: Extensive real-world deployment experience and robust OTA update capabilities. Weaknesses: Legacy system integration challenges and higher computational overhead.
Core Encryption Innovations for Automotive Applications
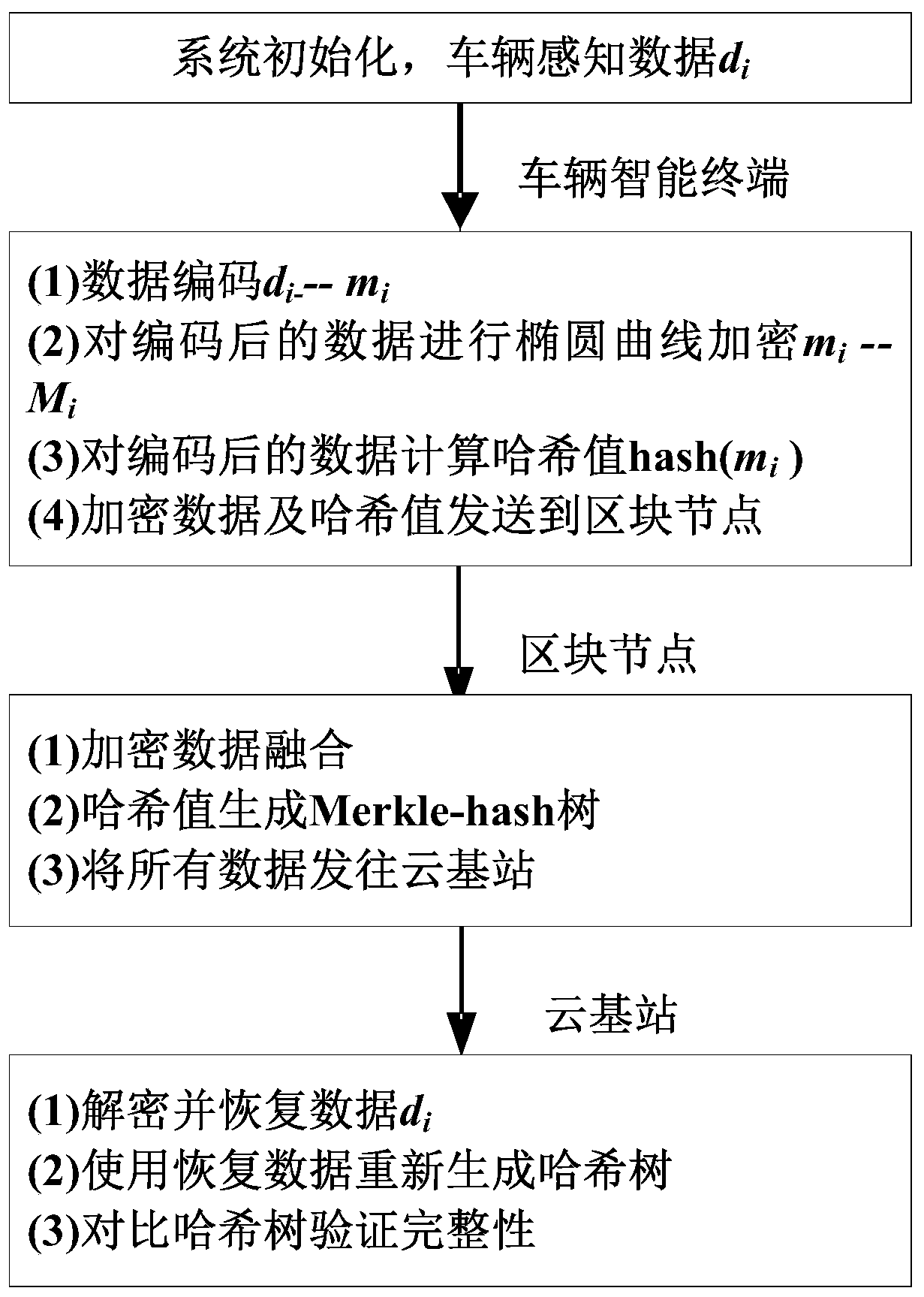
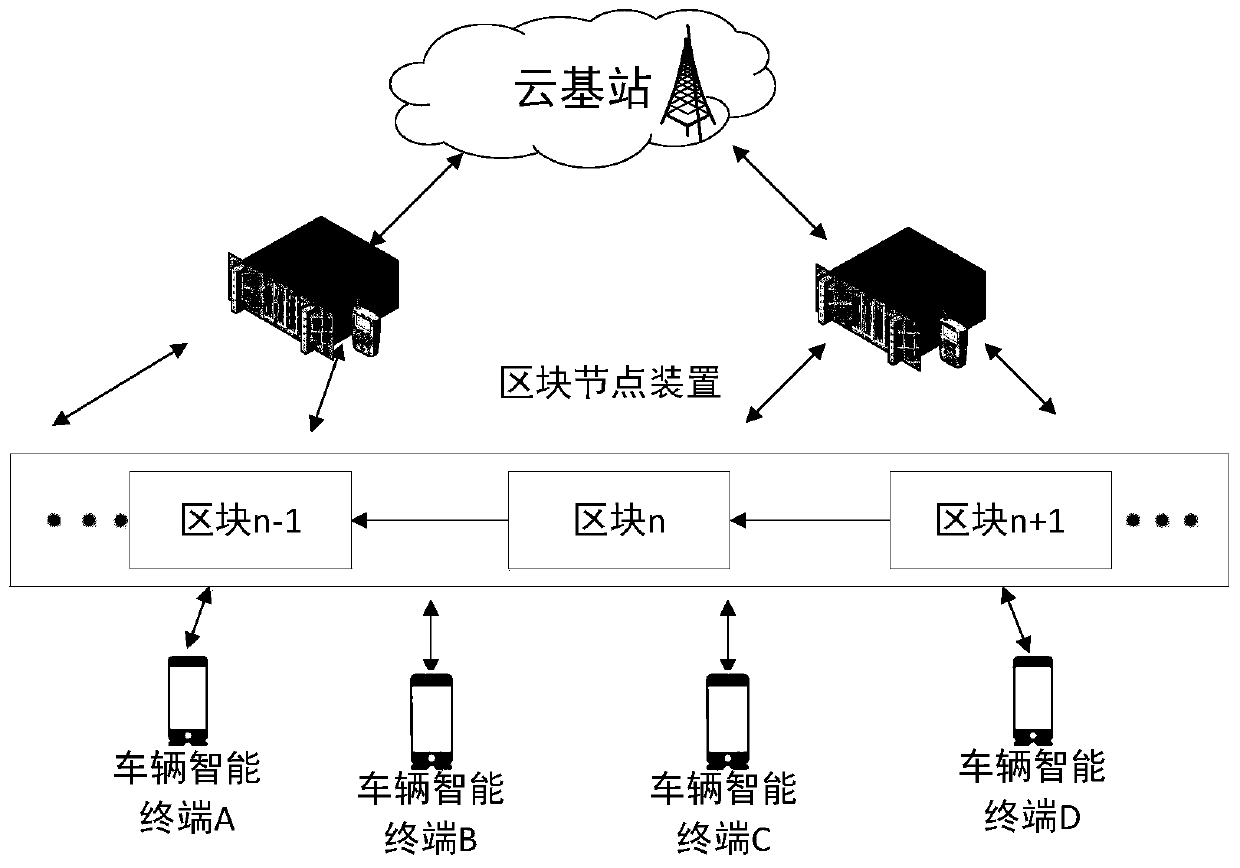
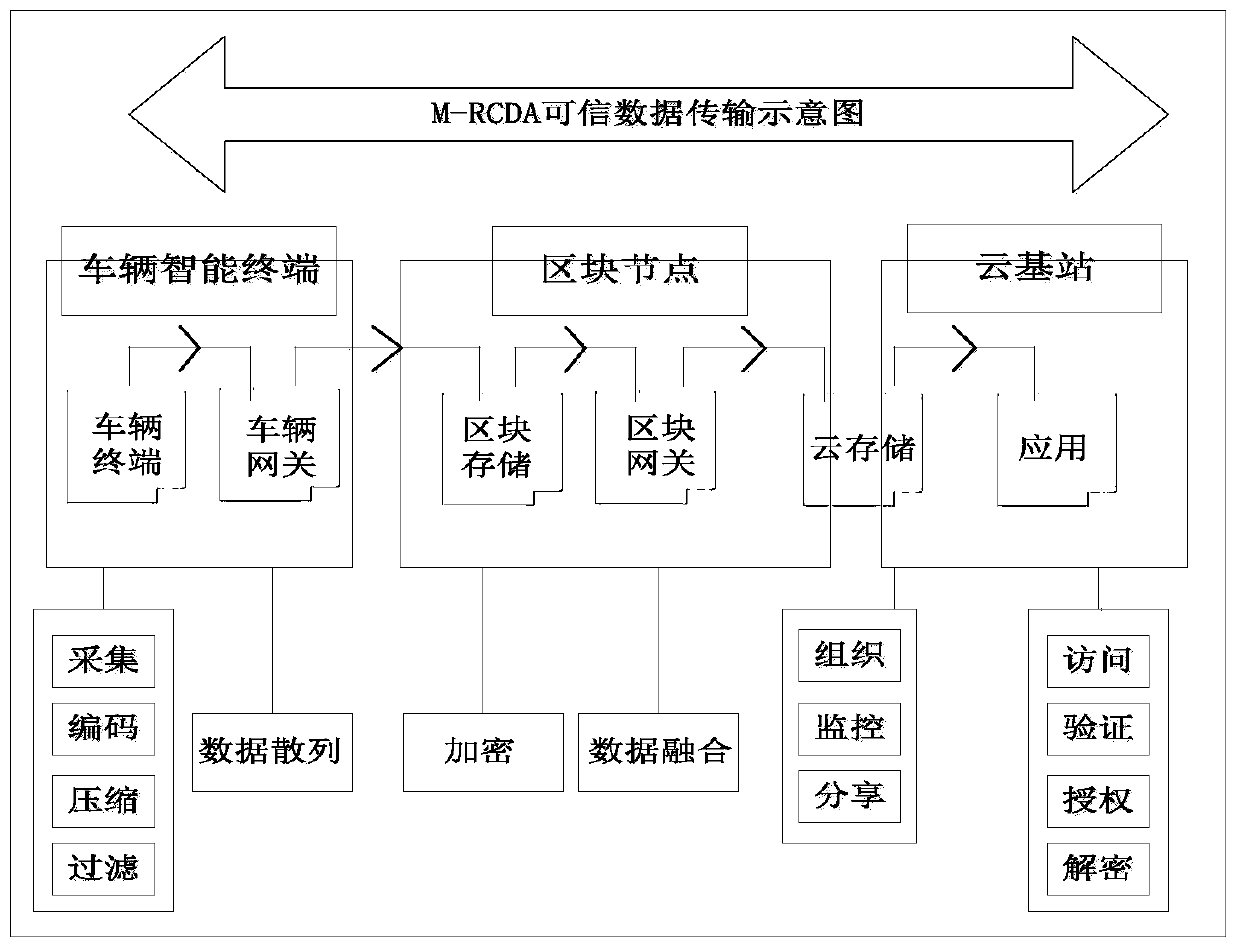
Intelligent Internet of Vehicles credible data encryption method and system based on block chain
PatentActiveCN110830235A
Innovation
- Adopting a blockchain-based Internet of Vehicles data encryption method, using elliptic curve encryption and Merkle-hash tree technology, the vehicle intelligent terminal encodes and encrypts the collected data, the block nodes perform data fusion and hash tree construction, and the cloud base station performs data processing Recovery and integrity verification ensure the confidentiality and integrity of data during transmission.
Multi-key data aggregation method for Internet of Vehicles
PatentPendingCN119629619A
Innovation
- Using a multi-key data aggregation method for the Internet of Vehicles, public parameters are generated through LWE and RLWE encryption technology, private keys are randomly generated and public keys, bootstrap keys and key conversion keys are generated based on the private keys. The ciphertext expansion and addition operations are used to generate the aggregated ciphertext, and the key conversion is converted into a ciphertext that can be decrypted by the joint key.
Automotive Cybersecurity Regulatory Framework
The automotive cybersecurity regulatory landscape has evolved rapidly in response to the increasing connectivity and digitization of modern vehicles. As connected vehicles generate and transmit vast amounts of sensitive data, regulatory bodies worldwide have recognized the critical need for comprehensive cybersecurity frameworks to protect both vehicle operations and user privacy.
The United Nations Economic Commission for Europe (UNECE) has established WP.29 regulations, particularly UN Regulation No. 155 on Cybersecurity Management Systems (CSMS) and UN Regulation No. 156 on Software Update Management Systems (SUMS). These regulations mandate that vehicle manufacturers implement robust cybersecurity measures throughout the vehicle lifecycle, from design and production to post-market monitoring and incident response.
In the United States, the National Highway Traffic Safety Administration (NHTSA) has issued cybersecurity guidance for the automotive industry, emphasizing the importance of layered security approaches and risk-based cybersecurity programs. The Federal Trade Commission (FTC) also plays a crucial role in enforcing data protection requirements for connected vehicle services.
The European Union has implemented the General Data Protection Regulation (GDPR), which significantly impacts how automotive manufacturers handle personal data collected from connected vehicles. Additionally, the EU Cybersecurity Act and the proposed Cyber Resilience Act will further strengthen cybersecurity requirements for automotive systems and components.
China has established its own regulatory framework through the Cybersecurity Law and specific automotive data security regulations, requiring local data storage and strict controls on cross-border data transfers. The China Association of Automobile Manufacturers (CAAM) has also developed industry-specific cybersecurity guidelines.
These regulatory frameworks collectively emphasize several key principles: risk assessment and management, security by design, incident reporting and response, regular security updates, and data minimization. Compliance with these evolving regulations requires automotive manufacturers to implement comprehensive encryption strategies, secure communication protocols, and robust data protection mechanisms throughout their connected vehicle ecosystems.
The United Nations Economic Commission for Europe (UNECE) has established WP.29 regulations, particularly UN Regulation No. 155 on Cybersecurity Management Systems (CSMS) and UN Regulation No. 156 on Software Update Management Systems (SUMS). These regulations mandate that vehicle manufacturers implement robust cybersecurity measures throughout the vehicle lifecycle, from design and production to post-market monitoring and incident response.
In the United States, the National Highway Traffic Safety Administration (NHTSA) has issued cybersecurity guidance for the automotive industry, emphasizing the importance of layered security approaches and risk-based cybersecurity programs. The Federal Trade Commission (FTC) also plays a crucial role in enforcing data protection requirements for connected vehicle services.
The European Union has implemented the General Data Protection Regulation (GDPR), which significantly impacts how automotive manufacturers handle personal data collected from connected vehicles. Additionally, the EU Cybersecurity Act and the proposed Cyber Resilience Act will further strengthen cybersecurity requirements for automotive systems and components.
China has established its own regulatory framework through the Cybersecurity Law and specific automotive data security regulations, requiring local data storage and strict controls on cross-border data transfers. The China Association of Automobile Manufacturers (CAAM) has also developed industry-specific cybersecurity guidelines.
These regulatory frameworks collectively emphasize several key principles: risk assessment and management, security by design, incident reporting and response, regular security updates, and data minimization. Compliance with these evolving regulations requires automotive manufacturers to implement comprehensive encryption strategies, secure communication protocols, and robust data protection mechanisms throughout their connected vehicle ecosystems.
Privacy Protection Standards for Vehicle Data
The establishment of comprehensive privacy protection standards for vehicle data has become a critical imperative as connected vehicles generate unprecedented volumes of sensitive information. These standards serve as the foundational framework governing how personal and operational data collected from vehicles should be handled, processed, and protected throughout its lifecycle.
Current privacy protection standards for vehicle data are primarily anchored in existing regulatory frameworks such as the General Data Protection Regulation (GDPR) in Europe and the California Consumer Privacy Act (CCPA) in the United States. These regulations establish fundamental principles including data minimization, purpose limitation, and user consent requirements. However, the automotive industry faces unique challenges in applying these broad privacy laws to the specific context of connected vehicles, where data collection occurs continuously and often involves location tracking, driving behavior analysis, and biometric information.
The International Organization for Standardization (ISO) has developed ISO/SAE 21434, which addresses cybersecurity engineering for road vehicles and establishes requirements for privacy-by-design approaches. This standard mandates that privacy considerations be integrated into vehicle systems from the initial design phase rather than as an afterthought. Additionally, the Society of Automotive Engineers (SAE) has published guidelines specifically addressing data privacy in connected vehicle ecosystems.
Industry-specific standards are emerging to address the unique characteristics of vehicular data. The Automotive Industry Action Group (AIAG) has developed frameworks that define data classification levels, ranging from public information to highly sensitive personal data. These classifications determine appropriate encryption requirements, access controls, and retention policies for different types of vehicle-generated data.
Regional variations in privacy standards create additional complexity for global automotive manufacturers. European standards emphasize individual rights and data portability, while Asian markets often prioritize collective benefits and smart city integration. North American approaches tend to focus on sectoral regulations and industry self-governance mechanisms.
The evolution of privacy protection standards continues to adapt to emerging technologies such as vehicle-to-everything (V2X) communication, autonomous driving systems, and integrated infotainment platforms. Future standards development is expected to address cross-border data transfers, real-time anonymization techniques, and the balance between privacy protection and safety-critical data sharing requirements.
Current privacy protection standards for vehicle data are primarily anchored in existing regulatory frameworks such as the General Data Protection Regulation (GDPR) in Europe and the California Consumer Privacy Act (CCPA) in the United States. These regulations establish fundamental principles including data minimization, purpose limitation, and user consent requirements. However, the automotive industry faces unique challenges in applying these broad privacy laws to the specific context of connected vehicles, where data collection occurs continuously and often involves location tracking, driving behavior analysis, and biometric information.
The International Organization for Standardization (ISO) has developed ISO/SAE 21434, which addresses cybersecurity engineering for road vehicles and establishes requirements for privacy-by-design approaches. This standard mandates that privacy considerations be integrated into vehicle systems from the initial design phase rather than as an afterthought. Additionally, the Society of Automotive Engineers (SAE) has published guidelines specifically addressing data privacy in connected vehicle ecosystems.
Industry-specific standards are emerging to address the unique characteristics of vehicular data. The Automotive Industry Action Group (AIAG) has developed frameworks that define data classification levels, ranging from public information to highly sensitive personal data. These classifications determine appropriate encryption requirements, access controls, and retention policies for different types of vehicle-generated data.
Regional variations in privacy standards create additional complexity for global automotive manufacturers. European standards emphasize individual rights and data portability, while Asian markets often prioritize collective benefits and smart city integration. North American approaches tend to focus on sectoral regulations and industry self-governance mechanisms.
The evolution of privacy protection standards continues to adapt to emerging technologies such as vehicle-to-everything (V2X) communication, autonomous driving systems, and integrated infotainment platforms. Future standards development is expected to address cross-border data transfers, real-time anonymization techniques, and the balance between privacy protection and safety-critical data sharing requirements.
Unlock deeper insights with PatSnap Eureka Quick Research — get a full tech report to explore trends and direct your research. Try now!
Generate Your Research Report Instantly with AI Agent
Supercharge your innovation with PatSnap Eureka AI Agent Platform!