Enhance Autonomous System Defense with Adaptive Security
MAR 5, 20269 MIN READ
Generate Your Research Report Instantly with AI Agent
PatSnap Eureka helps you evaluate technical feasibility & market potential.
Autonomous System Security Background and Defense Goals
Autonomous systems have evolved from simple automated processes to sophisticated networks capable of independent decision-making across critical infrastructure, transportation, healthcare, and defense sectors. The proliferation of Internet of Things devices, artificial intelligence integration, and machine learning capabilities has exponentially expanded the attack surface of these systems. Traditional security paradigms, designed for human-operated systems, prove inadequate against the dynamic threat landscape targeting autonomous operations.
The convergence of cyber-physical systems with autonomous decision-making creates unprecedented vulnerabilities. Attackers can exploit sensor manipulation, communication protocols, and algorithmic weaknesses to compromise system integrity. Recent incidents involving autonomous vehicle hacking, industrial control system breaches, and drone hijacking demonstrate the urgent need for adaptive security frameworks that can evolve alongside emerging threats.
Current autonomous systems face multifaceted security challenges including adversarial machine learning attacks, sensor spoofing, communication interception, and supply chain compromises. The interconnected nature of these systems means that a single point of failure can cascade across entire networks, potentially causing catastrophic consequences in critical applications such as autonomous transportation, smart grid management, and medical device networks.
The primary defense goal centers on developing adaptive security mechanisms that can autonomously detect, analyze, and respond to novel attack vectors without human intervention. This requires implementing self-healing capabilities that enable systems to maintain operational continuity even under active attack conditions. The security framework must demonstrate resilience against both known and zero-day exploits while preserving system performance and functionality.
Secondary objectives include establishing robust threat intelligence sharing mechanisms between autonomous systems to enable collective defense strategies. The framework should incorporate predictive security analytics to anticipate potential attack scenarios and proactively strengthen vulnerable components. Additionally, the system must maintain compliance with regulatory requirements while ensuring privacy protection and data integrity across all operational domains.
The ultimate technological goal involves creating a comprehensive adaptive security ecosystem that seamlessly integrates with existing autonomous system architectures. This ecosystem should provide real-time threat assessment, automated incident response, and continuous security posture optimization. The solution must scale effectively across diverse autonomous system deployments while maintaining cost-effectiveness and operational efficiency.
The convergence of cyber-physical systems with autonomous decision-making creates unprecedented vulnerabilities. Attackers can exploit sensor manipulation, communication protocols, and algorithmic weaknesses to compromise system integrity. Recent incidents involving autonomous vehicle hacking, industrial control system breaches, and drone hijacking demonstrate the urgent need for adaptive security frameworks that can evolve alongside emerging threats.
Current autonomous systems face multifaceted security challenges including adversarial machine learning attacks, sensor spoofing, communication interception, and supply chain compromises. The interconnected nature of these systems means that a single point of failure can cascade across entire networks, potentially causing catastrophic consequences in critical applications such as autonomous transportation, smart grid management, and medical device networks.
The primary defense goal centers on developing adaptive security mechanisms that can autonomously detect, analyze, and respond to novel attack vectors without human intervention. This requires implementing self-healing capabilities that enable systems to maintain operational continuity even under active attack conditions. The security framework must demonstrate resilience against both known and zero-day exploits while preserving system performance and functionality.
Secondary objectives include establishing robust threat intelligence sharing mechanisms between autonomous systems to enable collective defense strategies. The framework should incorporate predictive security analytics to anticipate potential attack scenarios and proactively strengthen vulnerable components. Additionally, the system must maintain compliance with regulatory requirements while ensuring privacy protection and data integrity across all operational domains.
The ultimate technological goal involves creating a comprehensive adaptive security ecosystem that seamlessly integrates with existing autonomous system architectures. This ecosystem should provide real-time threat assessment, automated incident response, and continuous security posture optimization. The solution must scale effectively across diverse autonomous system deployments while maintaining cost-effectiveness and operational efficiency.
Market Demand for Adaptive Autonomous Security Solutions
The global cybersecurity market is experiencing unprecedented growth driven by the escalating sophistication of cyber threats targeting autonomous systems across multiple industries. Organizations operating critical infrastructure, including transportation networks, manufacturing facilities, and energy grids, are increasingly recognizing the limitations of traditional static security measures in protecting autonomous operations.
Autonomous vehicles represent one of the most significant market drivers for adaptive security solutions. The automotive industry faces mounting pressure to secure connected and self-driving vehicles against evolving cyber threats that could compromise passenger safety and operational integrity. Fleet operators and automotive manufacturers are actively seeking security frameworks that can dynamically respond to new attack vectors without requiring manual intervention or system downtime.
Industrial automation sectors, particularly smart manufacturing and Industry 4.0 implementations, demonstrate substantial demand for adaptive autonomous security. Manufacturing facilities deploying interconnected robotic systems, IoT sensors, and automated production lines require security solutions capable of real-time threat detection and response. The potential for cyber attacks to disrupt production schedules or compromise product quality creates urgent market demand for self-adapting security mechanisms.
Critical infrastructure operators, including power utilities, water treatment facilities, and telecommunications networks, represent another major market segment. These organizations face regulatory compliance requirements and operational continuity mandates that traditional security approaches struggle to meet. The need for security systems that can autonomously adapt to emerging threats while maintaining operational availability drives significant investment in adaptive security technologies.
The financial services sector shows growing interest in adaptive autonomous security for protecting algorithmic trading systems, digital payment platforms, and automated risk management tools. The high-frequency nature of financial operations demands security solutions that can make instantaneous decisions without human intervention while maintaining system performance.
Enterprise cloud environments and data centers constitute an expanding market segment where adaptive security solutions address the complexity of protecting dynamic, scalable infrastructure. Organizations migrating to hybrid and multi-cloud architectures require security frameworks that can automatically adjust protection mechanisms based on changing workload patterns and threat landscapes.
Government and defense agencies represent a specialized but significant market segment seeking adaptive security for unmanned systems, surveillance networks, and classified data processing environments. The sensitive nature of these applications demands security solutions capable of autonomous threat response while maintaining operational secrecy and mission continuity.
Autonomous vehicles represent one of the most significant market drivers for adaptive security solutions. The automotive industry faces mounting pressure to secure connected and self-driving vehicles against evolving cyber threats that could compromise passenger safety and operational integrity. Fleet operators and automotive manufacturers are actively seeking security frameworks that can dynamically respond to new attack vectors without requiring manual intervention or system downtime.
Industrial automation sectors, particularly smart manufacturing and Industry 4.0 implementations, demonstrate substantial demand for adaptive autonomous security. Manufacturing facilities deploying interconnected robotic systems, IoT sensors, and automated production lines require security solutions capable of real-time threat detection and response. The potential for cyber attacks to disrupt production schedules or compromise product quality creates urgent market demand for self-adapting security mechanisms.
Critical infrastructure operators, including power utilities, water treatment facilities, and telecommunications networks, represent another major market segment. These organizations face regulatory compliance requirements and operational continuity mandates that traditional security approaches struggle to meet. The need for security systems that can autonomously adapt to emerging threats while maintaining operational availability drives significant investment in adaptive security technologies.
The financial services sector shows growing interest in adaptive autonomous security for protecting algorithmic trading systems, digital payment platforms, and automated risk management tools. The high-frequency nature of financial operations demands security solutions that can make instantaneous decisions without human intervention while maintaining system performance.
Enterprise cloud environments and data centers constitute an expanding market segment where adaptive security solutions address the complexity of protecting dynamic, scalable infrastructure. Organizations migrating to hybrid and multi-cloud architectures require security frameworks that can automatically adjust protection mechanisms based on changing workload patterns and threat landscapes.
Government and defense agencies represent a specialized but significant market segment seeking adaptive security for unmanned systems, surveillance networks, and classified data processing environments. The sensitive nature of these applications demands security solutions capable of autonomous threat response while maintaining operational secrecy and mission continuity.
Current Security Challenges in Autonomous Systems
Autonomous systems face unprecedented security challenges as they become increasingly integrated into critical infrastructure and daily operations. The attack surface of these systems has expanded dramatically due to their reliance on multiple interconnected components including sensors, communication networks, decision-making algorithms, and actuators. Each component represents a potential entry point for malicious actors seeking to compromise system integrity.
Traditional cybersecurity approaches prove inadequate for autonomous systems due to their dynamic operational environments and real-time decision-making requirements. Static security measures cannot adapt to the evolving threat landscape that autonomous systems encounter during operation. The distributed nature of these systems, often operating across multiple domains and networks, creates additional vulnerabilities that conventional security frameworks struggle to address effectively.
Data integrity attacks pose significant risks to autonomous systems, as adversaries can manipulate sensor inputs or training data to cause system malfunctions or erroneous decisions. Machine learning models powering autonomous systems are particularly vulnerable to adversarial attacks, where carefully crafted inputs can fool AI algorithms into making incorrect classifications or predictions. These attacks can be subtle and difficult to detect using traditional monitoring approaches.
Communication security represents another critical challenge, as autonomous systems rely heavily on wireless networks and inter-system communication protocols. Man-in-the-middle attacks, signal jamming, and protocol exploitation can disrupt system coordination and compromise operational safety. The need for low-latency communication in autonomous systems often conflicts with robust encryption and authentication mechanisms.
Supply chain security concerns have intensified as autonomous systems incorporate components from multiple vendors and open-source software libraries. Hardware trojans, compromised firmware, and malicious code injection during the development lifecycle can create persistent vulnerabilities that remain undetected until exploitation. The complexity of modern autonomous systems makes comprehensive security auditing increasingly challenging.
Real-time threat detection and response capabilities remain limited in current autonomous systems. The computational overhead of continuous security monitoring can impact system performance, creating trade-offs between security and operational efficiency. Additionally, the lack of standardized security frameworks specifically designed for autonomous systems hampers the implementation of consistent security measures across different platforms and applications.
Traditional cybersecurity approaches prove inadequate for autonomous systems due to their dynamic operational environments and real-time decision-making requirements. Static security measures cannot adapt to the evolving threat landscape that autonomous systems encounter during operation. The distributed nature of these systems, often operating across multiple domains and networks, creates additional vulnerabilities that conventional security frameworks struggle to address effectively.
Data integrity attacks pose significant risks to autonomous systems, as adversaries can manipulate sensor inputs or training data to cause system malfunctions or erroneous decisions. Machine learning models powering autonomous systems are particularly vulnerable to adversarial attacks, where carefully crafted inputs can fool AI algorithms into making incorrect classifications or predictions. These attacks can be subtle and difficult to detect using traditional monitoring approaches.
Communication security represents another critical challenge, as autonomous systems rely heavily on wireless networks and inter-system communication protocols. Man-in-the-middle attacks, signal jamming, and protocol exploitation can disrupt system coordination and compromise operational safety. The need for low-latency communication in autonomous systems often conflicts with robust encryption and authentication mechanisms.
Supply chain security concerns have intensified as autonomous systems incorporate components from multiple vendors and open-source software libraries. Hardware trojans, compromised firmware, and malicious code injection during the development lifecycle can create persistent vulnerabilities that remain undetected until exploitation. The complexity of modern autonomous systems makes comprehensive security auditing increasingly challenging.
Real-time threat detection and response capabilities remain limited in current autonomous systems. The computational overhead of continuous security monitoring can impact system performance, creating trade-offs between security and operational efficiency. Additionally, the lack of standardized security frameworks specifically designed for autonomous systems hampers the implementation of consistent security measures across different platforms and applications.
Existing Adaptive Defense Solutions for Autonomous Systems
01 AI-based threat detection and response systems
Autonomous defense systems utilize artificial intelligence and machine learning algorithms to detect, analyze, and respond to security threats in real-time. These systems can identify anomalous patterns, predict potential attacks, and automatically initiate countermeasures without human intervention. The technology enables continuous monitoring and adaptive defense mechanisms that evolve based on emerging threat landscapes.- AI-based threat detection and response systems: Autonomous defense systems utilize artificial intelligence and machine learning algorithms to detect, analyze, and respond to security threats in real-time. These systems can identify anomalous behavior patterns, predict potential attacks, and automatically initiate countermeasures without human intervention. The AI-driven approach enables continuous learning and adaptation to evolving threat landscapes, improving detection accuracy and response speed over time.
- Distributed autonomous defense architecture: Implementation of decentralized defense mechanisms that operate across multiple nodes or systems to provide comprehensive protection. This architecture enables autonomous systems to coordinate defense strategies, share threat intelligence, and maintain operational continuity even when individual components are compromised. The distributed approach enhances resilience and reduces single points of failure in defense infrastructure.
- Automated vulnerability assessment and patching: Systems that autonomously scan for security vulnerabilities, assess risk levels, and deploy patches or mitigation measures without manual intervention. These solutions continuously monitor system configurations, software versions, and security postures to identify weaknesses before they can be exploited. The automated approach significantly reduces the window of exposure to known vulnerabilities.
- Behavioral analysis and anomaly detection: Advanced monitoring systems that establish baseline behavioral patterns for networks, applications, and users, then autonomously detect deviations that may indicate security threats. These systems employ statistical analysis, pattern recognition, and heuristic methods to identify suspicious activities such as unauthorized access attempts, data exfiltration, or malware propagation. The behavioral approach enables detection of zero-day attacks and previously unknown threats.
- Autonomous incident response and recovery: Integrated systems that automatically execute predefined response protocols when security incidents are detected, including isolation of affected systems, blocking malicious traffic, and initiating recovery procedures. These solutions can autonomously contain threats, preserve forensic evidence, and restore normal operations while minimizing damage and downtime. The automated response capability ensures rapid mitigation of security incidents regardless of time or availability of security personnel.
02 Integrated multi-layer defense architecture
Autonomous defense systems employ multi-layered security architectures that combine various defense mechanisms including perimeter protection, intrusion detection, and internal security controls. These integrated systems coordinate different security components to provide comprehensive protection against diverse attack vectors. The architecture ensures redundancy and fail-safe operations through distributed defense nodes.Expand Specific Solutions03 Automated vulnerability assessment and patching
Systems that automatically scan for security vulnerabilities, assess risk levels, and deploy patches or updates without manual intervention. These solutions continuously monitor system configurations, identify weaknesses, and implement corrective measures to maintain security posture. The automation reduces response time and minimizes exposure windows to potential exploits.Expand Specific Solutions04 Autonomous network traffic analysis and filtering
Defense mechanisms that autonomously monitor network traffic patterns, identify malicious data flows, and implement filtering or blocking actions. These systems use deep packet inspection, behavioral analysis, and protocol validation to distinguish legitimate traffic from potential threats. Real-time processing capabilities enable immediate response to detected anomalies.Expand Specific Solutions05 Self-healing and resilience mechanisms
Autonomous systems equipped with self-recovery capabilities that can detect system compromises, isolate affected components, and restore normal operations automatically. These mechanisms include backup activation, redundant system deployment, and automatic reconfiguration to maintain service continuity during attacks. The technology ensures minimal downtime and maintains operational integrity under adverse conditions.Expand Specific Solutions
Key Players in Autonomous Security Industry
The autonomous system defense market is experiencing rapid growth driven by escalating cybersecurity threats and increasing digitalization across critical infrastructure sectors. The industry is in an expansion phase with significant market opportunities, particularly in power grid security, industrial automation, and telecommunications. Technology maturity varies considerably among key players: established giants like Intel, Qualcomm, and Thales SA lead with advanced AI-driven security solutions, while specialized firms such as Venustech Group, SecureSky, and China Electronic Tech Network Information Security focus on niche adaptive defense technologies. State-owned enterprises including State Grid Corp. of China and various power companies are driving demand through infrastructure modernization initiatives. The competitive landscape shows a mix of mature multinational corporations and emerging specialized security providers, indicating a dynamic market with both established solutions and innovative adaptive technologies still evolving toward full commercial maturity.
Venustech Group Inc.
Technical Solution: Venustech specializes in developing intelligent adaptive security platforms for autonomous systems through their proprietary threat detection and response technologies. Their security framework utilizes machine learning algorithms to continuously analyze system behavior patterns and automatically adjust defense mechanisms against evolving cyber threats. The company's adaptive security solution includes real-time vulnerability assessment, dynamic firewall configuration, and automated patch management systems. Venustech's approach emphasizes proactive threat hunting and predictive security analytics that enable autonomous systems to anticipate and mitigate potential security breaches before they occur. Their platform supports seamless integration with existing infrastructure while providing comprehensive security orchestration capabilities.
Strengths: Strong focus on AI-driven security, comprehensive threat intelligence, cost-effective solutions. Weaknesses: Limited global market presence, dependency on regional expertise.
Schneider Electric Systems USA, Inc.
Technical Solution: Schneider Electric develops adaptive security solutions for industrial autonomous systems through their EcoStruxure cybersecurity framework. Their approach focuses on operational technology (OT) security with adaptive threat detection capabilities that can distinguish between normal operational variations and malicious activities. The company's security platform incorporates industrial-grade firewalls, secure remote access solutions, and automated security policy enforcement mechanisms. Schneider Electric's adaptive defense system utilizes industrial IoT sensors and edge analytics to provide real-time security monitoring and automated incident response for critical infrastructure autonomous systems. Their solutions emphasize maintaining operational availability while ensuring robust security posture through continuous adaptation to emerging industrial cyber threats.
Strengths: Deep industrial automation expertise, proven OT security solutions, comprehensive infrastructure integration. Weaknesses: Limited AI/ML capabilities, slower adaptation to emerging technologies.
Core Innovations in Adaptive Security Mechanisms
An autonomous intelligent self-learning defense system for detecting and mitigating cyber attacks in smart systems
PatentActiveZA202200322B
Innovation
- An autonomous intelligent self-learning defense system is deployed at the Fog Computing Layer, utilizing unsupervised machine/deep learning algorithms for real-time attack detection and mitigation, with a modular structure comprising traffic collection, attack detection, security analysis, and attack mitigation modules, distributed across cloud computing nodes to reduce latency and enhance scalability.
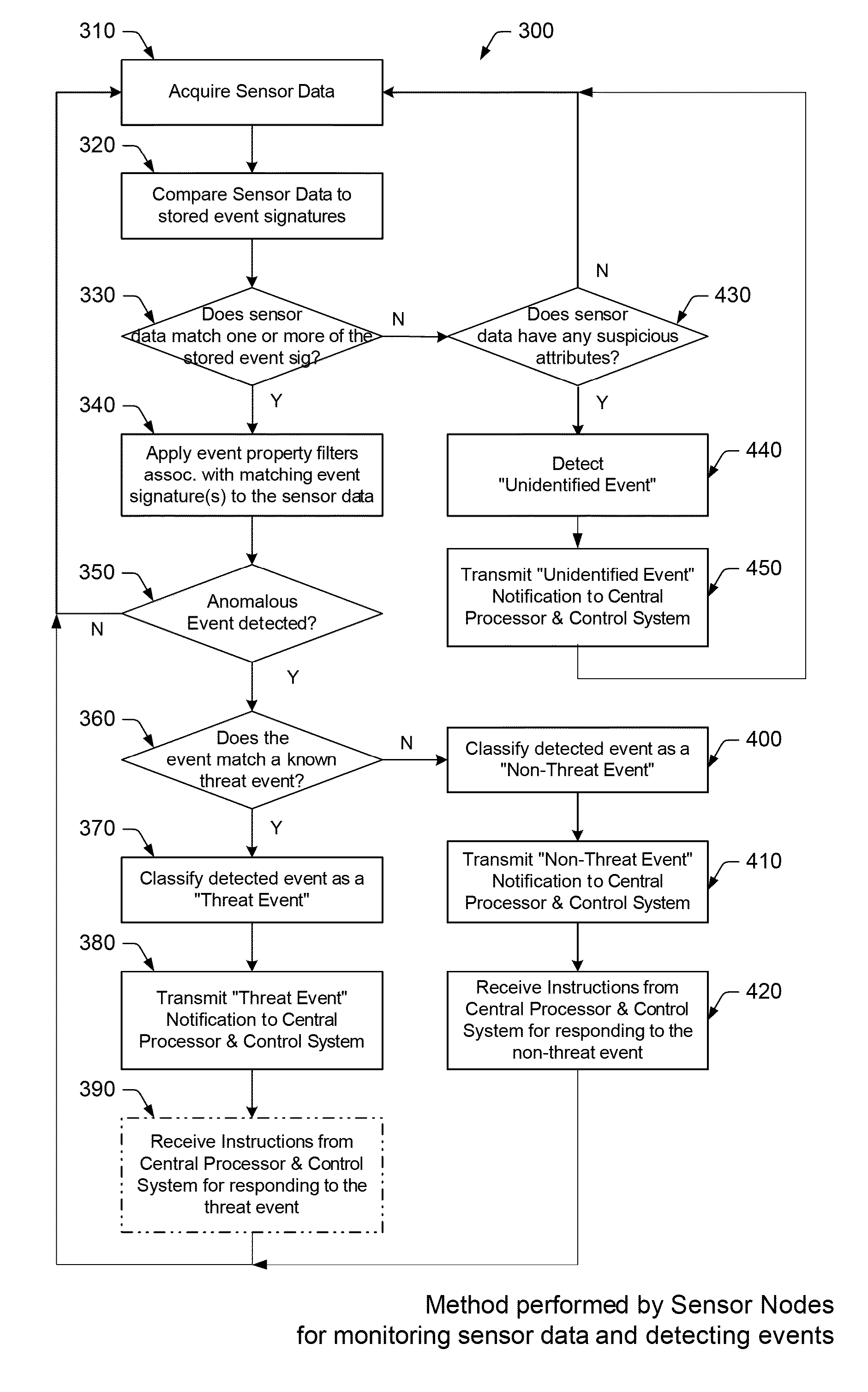
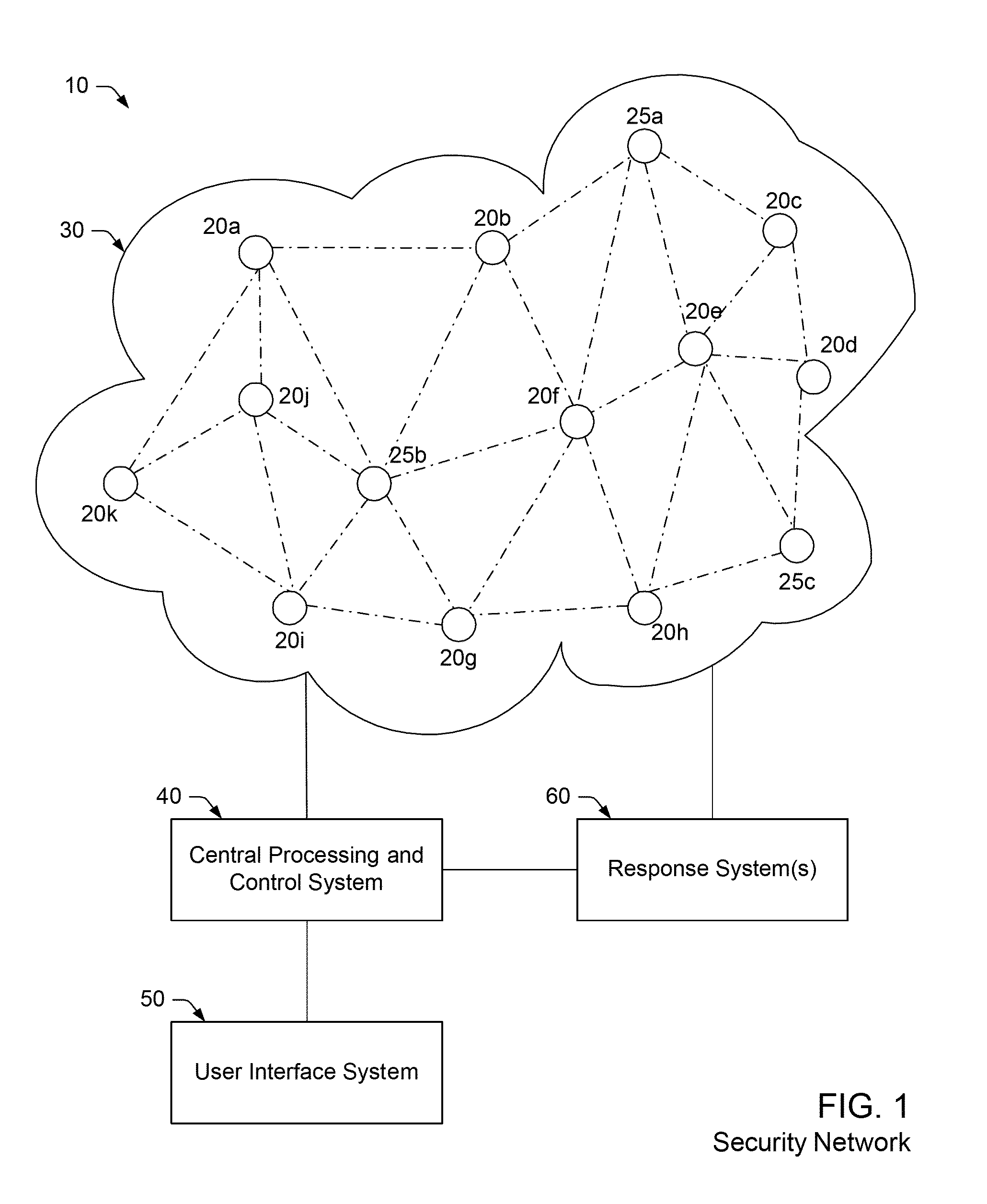
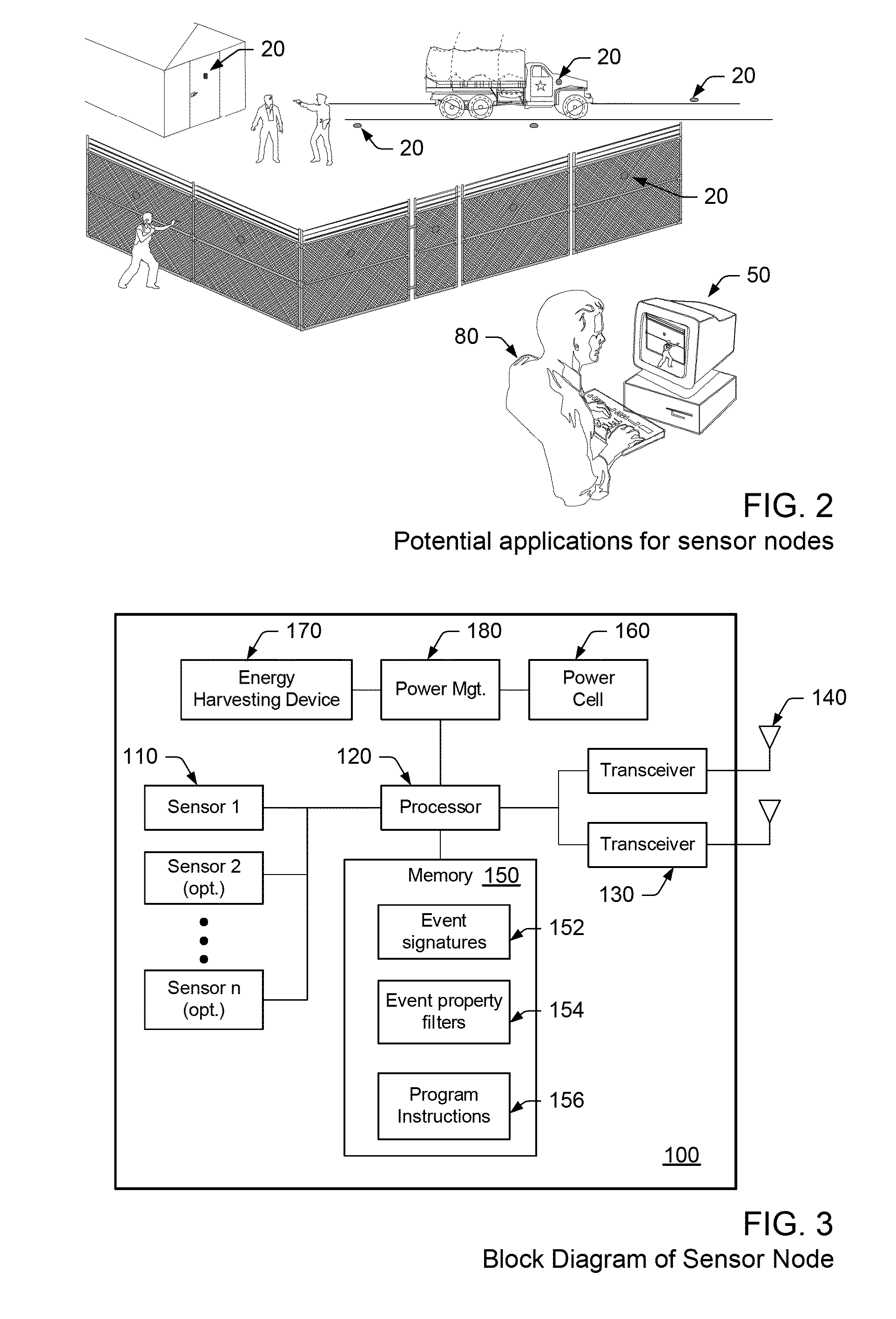
Adaptive security network, sensor node and method for detecting anomalous events in a security network
PatentActiveUS8779921B1
Innovation
- A security network comprising interconnected sensor nodes, a central processing and control system, and a user interface, which classifies anomalous events as threats, non-threats, or unidentified events, and adjusts sensitivity levels to filter out non-threat events while continuing to monitor for potential threats, using a combination of sensor technologies and adaptive algorithms.
Cybersecurity Regulatory Framework for Autonomous Systems
The regulatory landscape for autonomous systems cybersecurity is rapidly evolving as governments and international bodies recognize the critical need for comprehensive frameworks to address emerging security challenges. Current regulatory approaches vary significantly across jurisdictions, with the European Union leading through initiatives like the Cybersecurity Act and proposed AI liability frameworks, while the United States focuses on sector-specific guidelines through agencies like NIST and the Department of Transportation.
Existing frameworks primarily address traditional cybersecurity concerns but struggle to accommodate the dynamic nature of adaptive security systems. The challenge lies in creating regulations that are both prescriptive enough to ensure baseline security standards and flexible enough to allow for innovative adaptive defense mechanisms. Current regulatory gaps include insufficient guidance on AI-driven security decision-making, unclear liability frameworks for autonomous security responses, and limited standards for real-time threat adaptation.
International harmonization efforts are underway through organizations like ISO/IEC, which is developing standards for AI system security, and the UN's working groups on autonomous systems governance. However, the pace of regulatory development significantly lags behind technological advancement, creating compliance uncertainties for organizations implementing adaptive security solutions.
Key regulatory considerations for adaptive security systems include data protection requirements during threat response, algorithmic transparency mandates, and certification processes for self-modifying security protocols. The challenge of maintaining compliance while enabling autonomous adaptation requires new regulatory paradigms that focus on outcome-based standards rather than prescriptive technical requirements.
Emerging regulatory trends indicate a shift toward risk-based frameworks that emphasize continuous monitoring and adaptive compliance mechanisms. This evolution suggests future regulations will need to incorporate provisions for self-certifying systems and real-time compliance validation, fundamentally changing how organizations approach cybersecurity governance in autonomous environments.
Existing frameworks primarily address traditional cybersecurity concerns but struggle to accommodate the dynamic nature of adaptive security systems. The challenge lies in creating regulations that are both prescriptive enough to ensure baseline security standards and flexible enough to allow for innovative adaptive defense mechanisms. Current regulatory gaps include insufficient guidance on AI-driven security decision-making, unclear liability frameworks for autonomous security responses, and limited standards for real-time threat adaptation.
International harmonization efforts are underway through organizations like ISO/IEC, which is developing standards for AI system security, and the UN's working groups on autonomous systems governance. However, the pace of regulatory development significantly lags behind technological advancement, creating compliance uncertainties for organizations implementing adaptive security solutions.
Key regulatory considerations for adaptive security systems include data protection requirements during threat response, algorithmic transparency mandates, and certification processes for self-modifying security protocols. The challenge of maintaining compliance while enabling autonomous adaptation requires new regulatory paradigms that focus on outcome-based standards rather than prescriptive technical requirements.
Emerging regulatory trends indicate a shift toward risk-based frameworks that emphasize continuous monitoring and adaptive compliance mechanisms. This evolution suggests future regulations will need to incorporate provisions for self-certifying systems and real-time compliance validation, fundamentally changing how organizations approach cybersecurity governance in autonomous environments.
AI Ethics and Safety Standards in Autonomous Defense
The integration of artificial intelligence into autonomous defense systems necessitates the establishment of comprehensive ethical frameworks and safety standards to ensure responsible deployment and operation. Current AI ethics guidelines emphasize principles of accountability, transparency, and human oversight, which become critically important when applied to defense applications where decisions can have life-or-death consequences.
International organizations and regulatory bodies are actively developing standardized frameworks for AI ethics in military applications. The IEEE Standards Association has proposed guidelines for ethical design in autonomous weapons systems, while NATO has established principles for responsible AI use in defense contexts. These frameworks emphasize the importance of meaningful human control, proportionality in response mechanisms, and adherence to international humanitarian law.
Safety standards for autonomous defense systems focus on reliability, predictability, and fail-safe mechanisms. The ISO/IEC 23053 standard provides guidance for AI risk management, while military-specific standards like STANAG 4586 address interoperability and safety requirements for unmanned systems. These standards mandate rigorous testing protocols, including adversarial testing scenarios and edge case validation to ensure system robustness under diverse operational conditions.
Ethical considerations extend beyond technical implementation to encompass decision-making algorithms and bias mitigation strategies. Autonomous defense systems must incorporate fairness constraints and discrimination prevention mechanisms to avoid targeting based on protected characteristics. Additionally, explainable AI requirements ensure that system decisions can be audited and justified, maintaining accountability chains essential for legal and operational compliance.
The challenge lies in balancing operational effectiveness with ethical constraints while maintaining system adaptability. Current approaches involve implementing ethical reasoning modules within AI architectures, establishing clear rules of engagement parameters, and developing real-time monitoring systems that can detect and prevent ethical violations. These measures ensure that adaptive security enhancements do not compromise fundamental ethical principles or safety requirements in autonomous defense operations.
International organizations and regulatory bodies are actively developing standardized frameworks for AI ethics in military applications. The IEEE Standards Association has proposed guidelines for ethical design in autonomous weapons systems, while NATO has established principles for responsible AI use in defense contexts. These frameworks emphasize the importance of meaningful human control, proportionality in response mechanisms, and adherence to international humanitarian law.
Safety standards for autonomous defense systems focus on reliability, predictability, and fail-safe mechanisms. The ISO/IEC 23053 standard provides guidance for AI risk management, while military-specific standards like STANAG 4586 address interoperability and safety requirements for unmanned systems. These standards mandate rigorous testing protocols, including adversarial testing scenarios and edge case validation to ensure system robustness under diverse operational conditions.
Ethical considerations extend beyond technical implementation to encompass decision-making algorithms and bias mitigation strategies. Autonomous defense systems must incorporate fairness constraints and discrimination prevention mechanisms to avoid targeting based on protected characteristics. Additionally, explainable AI requirements ensure that system decisions can be audited and justified, maintaining accountability chains essential for legal and operational compliance.
The challenge lies in balancing operational effectiveness with ethical constraints while maintaining system adaptability. Current approaches involve implementing ethical reasoning modules within AI architectures, establishing clear rules of engagement parameters, and developing real-time monitoring systems that can detect and prevent ethical violations. These measures ensure that adaptive security enhancements do not compromise fundamental ethical principles or safety requirements in autonomous defense operations.
Unlock deeper insights with PatSnap Eureka Quick Research — get a full tech report to explore trends and direct your research. Try now!
Generate Your Research Report Instantly with AI Agent
Supercharge your innovation with PatSnap Eureka AI Agent Platform!