Improving Data Encryption Using Electromagnetic Modulation
MAR 6, 20269 MIN READ
Generate Your Research Report Instantly with AI Agent
PatSnap Eureka helps you evaluate technical feasibility & market potential.
Electromagnetic Encryption Background and Objectives
Electromagnetic encryption represents a paradigm shift in data security methodologies, leveraging the fundamental properties of electromagnetic fields to enhance cryptographic processes. This technology emerged from the convergence of classical electromagnetic theory and modern cryptographic requirements, addressing the growing need for more robust security mechanisms in an increasingly connected digital landscape. The foundational concept builds upon Maxwell's electromagnetic equations and their practical applications in signal processing and data transmission.
The historical development of electromagnetic encryption traces back to early radio communication security efforts during the mid-20th century, where researchers first explored using electromagnetic field variations for secure communications. However, significant advancement occurred only in recent decades with the availability of sophisticated electromagnetic field manipulation technologies and high-precision measurement instruments. The integration of quantum electromagnetic principles has further expanded the theoretical framework, enabling more complex modulation schemes.
Current electromagnetic encryption approaches primarily focus on utilizing electromagnetic field properties such as frequency, phase, amplitude, and polarization as encryption parameters. These methods offer inherent advantages over traditional mathematical encryption by introducing physical layer security that is difficult to intercept or decode without precise knowledge of the electromagnetic characteristics used in the encryption process. The technology demonstrates particular promise in scenarios requiring real-time encryption with minimal computational overhead.
The primary technical objectives center on developing robust electromagnetic modulation techniques that can reliably encode and decode data while maintaining signal integrity across various transmission media. Key goals include achieving encryption strength comparable to or exceeding current AES standards, minimizing electromagnetic interference with existing communication systems, and ensuring compatibility with diverse hardware platforms. Additionally, the technology aims to provide quantum-resistant security features that remain effective against future computational threats.
Implementation objectives focus on creating scalable solutions suitable for both high-bandwidth data centers and resource-constrained IoT devices. The technology must demonstrate consistent performance across different electromagnetic environments while maintaining energy efficiency standards. Long-term goals include establishing standardized protocols for electromagnetic encryption deployment and developing automated systems capable of adaptive modulation based on real-time threat assessment and environmental conditions.
The historical development of electromagnetic encryption traces back to early radio communication security efforts during the mid-20th century, where researchers first explored using electromagnetic field variations for secure communications. However, significant advancement occurred only in recent decades with the availability of sophisticated electromagnetic field manipulation technologies and high-precision measurement instruments. The integration of quantum electromagnetic principles has further expanded the theoretical framework, enabling more complex modulation schemes.
Current electromagnetic encryption approaches primarily focus on utilizing electromagnetic field properties such as frequency, phase, amplitude, and polarization as encryption parameters. These methods offer inherent advantages over traditional mathematical encryption by introducing physical layer security that is difficult to intercept or decode without precise knowledge of the electromagnetic characteristics used in the encryption process. The technology demonstrates particular promise in scenarios requiring real-time encryption with minimal computational overhead.
The primary technical objectives center on developing robust electromagnetic modulation techniques that can reliably encode and decode data while maintaining signal integrity across various transmission media. Key goals include achieving encryption strength comparable to or exceeding current AES standards, minimizing electromagnetic interference with existing communication systems, and ensuring compatibility with diverse hardware platforms. Additionally, the technology aims to provide quantum-resistant security features that remain effective against future computational threats.
Implementation objectives focus on creating scalable solutions suitable for both high-bandwidth data centers and resource-constrained IoT devices. The technology must demonstrate consistent performance across different electromagnetic environments while maintaining energy efficiency standards. Long-term goals include establishing standardized protocols for electromagnetic encryption deployment and developing automated systems capable of adaptive modulation based on real-time threat assessment and environmental conditions.
Market Demand for Advanced Data Encryption Solutions
The global data encryption market is experiencing unprecedented growth driven by escalating cybersecurity threats and stringent regulatory requirements across industries. Organizations worldwide face mounting pressure to protect sensitive information from sophisticated cyber attacks, data breaches, and unauthorized access attempts that continue to evolve in complexity and frequency.
Financial services institutions represent the largest segment demanding advanced encryption solutions, as they handle vast amounts of sensitive financial data and face strict compliance requirements under regulations such as PCI DSS and Basel III. Healthcare organizations constitute another rapidly expanding market segment, driven by HIPAA compliance needs and the increasing digitization of medical records and patient data.
Government and defense sectors demonstrate substantial demand for next-generation encryption technologies, particularly solutions that can withstand quantum computing threats and provide enhanced security for classified communications. The growing adoption of cloud computing services across enterprises has created additional market pressure for encryption solutions that can secure data both in transit and at rest without compromising system performance.
The Internet of Things ecosystem presents a significant emerging market opportunity, as billions of connected devices require lightweight yet robust encryption mechanisms. Traditional encryption methods often prove inadequate for IoT applications due to computational limitations and power constraints, creating demand for innovative approaches like electromagnetic modulation-based encryption.
Regulatory frameworks such as GDPR in Europe and various data protection laws worldwide have intensified the need for comprehensive encryption strategies. Organizations face substantial financial penalties for data breaches, making investment in advanced encryption technologies a business imperative rather than merely a technical consideration.
The market increasingly seeks encryption solutions that offer improved performance characteristics, reduced computational overhead, and enhanced resistance to emerging attack vectors. Electromagnetic modulation-based encryption addresses these requirements by potentially offering faster processing speeds and novel security mechanisms that differ fundamentally from conventional cryptographic approaches, positioning it as a promising solution for next-generation data protection needs.
Financial services institutions represent the largest segment demanding advanced encryption solutions, as they handle vast amounts of sensitive financial data and face strict compliance requirements under regulations such as PCI DSS and Basel III. Healthcare organizations constitute another rapidly expanding market segment, driven by HIPAA compliance needs and the increasing digitization of medical records and patient data.
Government and defense sectors demonstrate substantial demand for next-generation encryption technologies, particularly solutions that can withstand quantum computing threats and provide enhanced security for classified communications. The growing adoption of cloud computing services across enterprises has created additional market pressure for encryption solutions that can secure data both in transit and at rest without compromising system performance.
The Internet of Things ecosystem presents a significant emerging market opportunity, as billions of connected devices require lightweight yet robust encryption mechanisms. Traditional encryption methods often prove inadequate for IoT applications due to computational limitations and power constraints, creating demand for innovative approaches like electromagnetic modulation-based encryption.
Regulatory frameworks such as GDPR in Europe and various data protection laws worldwide have intensified the need for comprehensive encryption strategies. Organizations face substantial financial penalties for data breaches, making investment in advanced encryption technologies a business imperative rather than merely a technical consideration.
The market increasingly seeks encryption solutions that offer improved performance characteristics, reduced computational overhead, and enhanced resistance to emerging attack vectors. Electromagnetic modulation-based encryption addresses these requirements by potentially offering faster processing speeds and novel security mechanisms that differ fundamentally from conventional cryptographic approaches, positioning it as a promising solution for next-generation data protection needs.
Current State of EM-Based Encryption Technologies
Electromagnetic-based encryption technologies represent an emerging paradigm that leverages the unique properties of electromagnetic fields to enhance data security. Current implementations primarily focus on utilizing electromagnetic interference patterns, field modulation techniques, and radio frequency characteristics to create additional layers of cryptographic protection beyond traditional mathematical algorithms.
The foundational approach in contemporary EM-based encryption involves modulating data signals through controlled electromagnetic field variations. Research institutions and technology companies have developed systems that embed encrypted information within electromagnetic carrier waves, making data extraction significantly more challenging without proper field detection equipment. These systems typically operate across various frequency spectrums, from low-frequency magnetic fields to high-frequency radio waves.
Physical layer security represents the most mature application area within EM-based encryption. Current technologies exploit the inherent randomness of electromagnetic propagation channels to generate cryptographic keys. Channel reciprocity principles enable legitimate communication parties to derive identical encryption keys from shared electromagnetic channel characteristics, while potential eavesdroppers cannot replicate these conditions due to spatial decorrelation properties.
Near-field communication security has advanced considerably through electromagnetic modulation techniques. Modern implementations utilize magnetic field coupling variations to create dynamic encryption parameters that change based on device proximity and orientation. These systems demonstrate particular effectiveness in contactless payment systems and secure device pairing applications, where electromagnetic field strength and pattern recognition serve as authentication factors.
Industrial applications have emerged in secure wireless sensor networks, where electromagnetic signature-based encryption provides robust protection against signal interception. Current deployments utilize ambient electromagnetic noise as entropy sources for key generation, creating location-specific and time-variant encryption parameters that enhance overall system security.
However, existing EM-based encryption technologies face significant implementation challenges. Power consumption requirements for electromagnetic field generation and detection often exceed conventional encryption methods. Signal processing complexity increases substantially when incorporating electromagnetic modulation parameters, requiring specialized hardware components and advanced signal processing algorithms.
Standardization efforts remain fragmented across different application domains. While some protocols exist for specific use cases like RFID security and wireless sensor networks, comprehensive standards for general-purpose EM-based encryption are still under development. This fragmentation limits interoperability and widespread adoption across diverse technological platforms.
Current research directions focus on hybrid approaches that combine traditional cryptographic methods with electromagnetic modulation techniques. These systems aim to leverage the computational efficiency of established algorithms while incorporating the physical security advantages of electromagnetic field manipulation, creating more robust and practical encryption solutions for real-world deployment scenarios.
The foundational approach in contemporary EM-based encryption involves modulating data signals through controlled electromagnetic field variations. Research institutions and technology companies have developed systems that embed encrypted information within electromagnetic carrier waves, making data extraction significantly more challenging without proper field detection equipment. These systems typically operate across various frequency spectrums, from low-frequency magnetic fields to high-frequency radio waves.
Physical layer security represents the most mature application area within EM-based encryption. Current technologies exploit the inherent randomness of electromagnetic propagation channels to generate cryptographic keys. Channel reciprocity principles enable legitimate communication parties to derive identical encryption keys from shared electromagnetic channel characteristics, while potential eavesdroppers cannot replicate these conditions due to spatial decorrelation properties.
Near-field communication security has advanced considerably through electromagnetic modulation techniques. Modern implementations utilize magnetic field coupling variations to create dynamic encryption parameters that change based on device proximity and orientation. These systems demonstrate particular effectiveness in contactless payment systems and secure device pairing applications, where electromagnetic field strength and pattern recognition serve as authentication factors.
Industrial applications have emerged in secure wireless sensor networks, where electromagnetic signature-based encryption provides robust protection against signal interception. Current deployments utilize ambient electromagnetic noise as entropy sources for key generation, creating location-specific and time-variant encryption parameters that enhance overall system security.
However, existing EM-based encryption technologies face significant implementation challenges. Power consumption requirements for electromagnetic field generation and detection often exceed conventional encryption methods. Signal processing complexity increases substantially when incorporating electromagnetic modulation parameters, requiring specialized hardware components and advanced signal processing algorithms.
Standardization efforts remain fragmented across different application domains. While some protocols exist for specific use cases like RFID security and wireless sensor networks, comprehensive standards for general-purpose EM-based encryption are still under development. This fragmentation limits interoperability and widespread adoption across diverse technological platforms.
Current research directions focus on hybrid approaches that combine traditional cryptographic methods with electromagnetic modulation techniques. These systems aim to leverage the computational efficiency of established algorithms while incorporating the physical security advantages of electromagnetic field manipulation, creating more robust and practical encryption solutions for real-world deployment scenarios.
Existing EM Modulation Encryption Approaches
01 Advanced encryption algorithms and key management
Implementation of sophisticated encryption algorithms such as AES, RSA, and elliptic curve cryptography to enhance data security. These methods focus on improving key generation, distribution, and management processes to ensure robust protection against unauthorized access. The effectiveness is measured by the computational complexity required to break the encryption and the resistance to various cryptographic attacks.- Advanced encryption algorithms and key management: Implementation of sophisticated encryption algorithms such as AES, RSA, and elliptic curve cryptography to enhance data security. These methods focus on improving key generation, distribution, and management processes to ensure robust protection against unauthorized access. The effectiveness is measured by the computational complexity required to break the encryption and the resistance to various cryptographic attacks.
- Multi-layer encryption and hybrid cryptographic systems: Utilization of multiple encryption layers and hybrid approaches that combine symmetric and asymmetric encryption techniques to maximize security effectiveness. These systems provide enhanced protection by applying different encryption methods at various stages of data transmission and storage, making it significantly more difficult for attackers to compromise the encrypted data.
- Performance optimization in encryption processes: Techniques for improving the speed and efficiency of encryption and decryption operations without compromising security. This includes hardware acceleration, parallel processing, and optimized algorithm implementations that reduce computational overhead while maintaining high levels of data protection. The focus is on balancing security strength with system performance requirements.
- Encryption effectiveness evaluation and testing methodologies: Methods and systems for assessing the strength and reliability of encryption implementations through various testing approaches. This includes vulnerability analysis, penetration testing, and statistical evaluation of encrypted data to verify that encryption meets security standards and effectively protects against known attack vectors. These evaluation frameworks help ensure that encryption systems maintain their intended security levels.
- Context-aware and adaptive encryption mechanisms: Dynamic encryption systems that adjust encryption parameters and methods based on data sensitivity, threat levels, and operational contexts. These adaptive approaches optimize encryption effectiveness by applying appropriate security measures according to real-time risk assessment and data classification, ensuring efficient resource utilization while maintaining necessary protection levels for different types of information.
02 Multi-layer encryption and hybrid cryptographic systems
Utilization of multiple encryption layers and hybrid approaches that combine symmetric and asymmetric encryption techniques to maximize security effectiveness. These systems provide enhanced protection by applying different encryption methods at various stages of data transmission and storage, making it significantly more difficult for attackers to compromise the entire system.Expand Specific Solutions03 Performance optimization in encryption processes
Techniques for improving the speed and efficiency of encryption and decryption operations without compromising security. This includes hardware acceleration, parallel processing, and optimized algorithm implementations that reduce computational overhead while maintaining high levels of data protection. The focus is on balancing security strength with system performance requirements.Expand Specific Solutions04 Encryption effectiveness evaluation and testing methodologies
Methods and systems for assessing the strength and reliability of encryption implementations through various testing approaches. This includes vulnerability analysis, penetration testing, and statistical evaluation of encrypted data to verify that encryption meets security standards and effectively protects against known attack vectors.Expand Specific Solutions05 Adaptive and context-aware encryption mechanisms
Dynamic encryption systems that adjust security parameters based on data sensitivity, threat levels, and operational context. These intelligent approaches optimize encryption effectiveness by applying appropriate security measures according to real-time risk assessment, ensuring efficient resource utilization while maintaining necessary protection levels for different types of data and usage scenarios.Expand Specific Solutions
Key Players in EM Encryption and Security Industry
The data encryption using electromagnetic modulation field represents an emerging technology sector in its early development stage, characterized by significant growth potential and evolving market dynamics. The market remains relatively nascent with substantial opportunities for expansion as cybersecurity demands intensify globally. Technology maturity varies considerably across market participants, with established semiconductor giants like Intel Corp., Fujitsu Ltd., Toshiba Corp., and STMicroelectronics demonstrating advanced capabilities in hardware-based encryption solutions. Specialized security firms such as Cryptography Research Inc., Vaultree Ltd., and Rampart Communications Inc. are pioneering innovative approaches to electromagnetic-based encryption methodologies. Academic institutions including Tsinghua University, Harbin Institute of Technology, and Northwestern University contribute foundational research driving technological advancement. The competitive landscape features a mix of mature technology corporations leveraging existing infrastructure, emerging specialized companies focusing on novel encryption techniques, and research institutions providing theoretical foundations, creating a dynamic ecosystem poised for significant technological breakthroughs and market expansion.
Toshiba Corp.
Technical Solution: Toshiba has developed quantum key distribution systems that utilize electromagnetic modulation for ultra-secure communications, particularly in their quantum cryptography solutions. Their technology combines quantum mechanics principles with electromagnetic field manipulation to create theoretically unbreakable encryption systems. Toshiba's approach focuses on using controlled electromagnetic pulses and photonic systems to establish secure key exchange protocols that can detect any attempt at eavesdropping through electromagnetic signature analysis and quantum state measurement.
Strengths: Advanced quantum technology capabilities, strong research foundation in photonics and electromagnetic systems. Weaknesses: High implementation costs, limited to specialized applications requiring maximum security levels.
Huawei Technologies Co., Ltd.
Technical Solution: Huawei has developed advanced electromagnetic modulation techniques for secure communications, implementing quantum-resistant encryption algorithms combined with electromagnetic field manipulation for enhanced data protection. Their approach utilizes controlled electromagnetic interference patterns to create additional encryption layers, making intercepted signals extremely difficult to decode. The company has integrated these technologies into their 5G infrastructure and networking equipment, providing multi-layered security through electromagnetic signal obfuscation and advanced cryptographic protocols that can adapt to various threat scenarios.
Strengths: Strong R&D capabilities in telecommunications security, extensive patent portfolio in electromagnetic technologies. Weaknesses: Limited market access in some regions due to geopolitical concerns.
Core Patents in Electromagnetic Cryptographic Methods
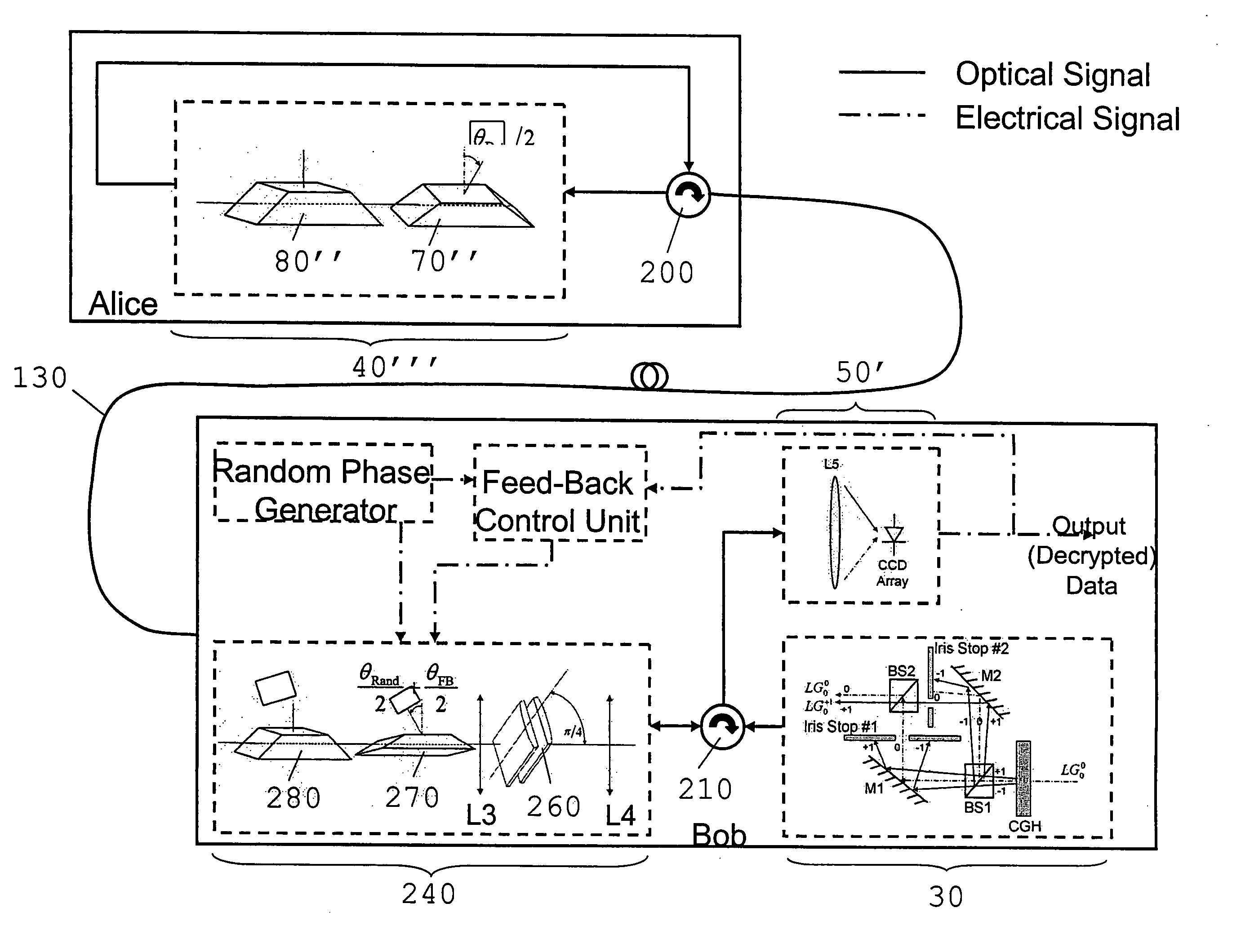
A method and apparatus relating to secure communication
PatentInactiveEP2019497B1
Innovation
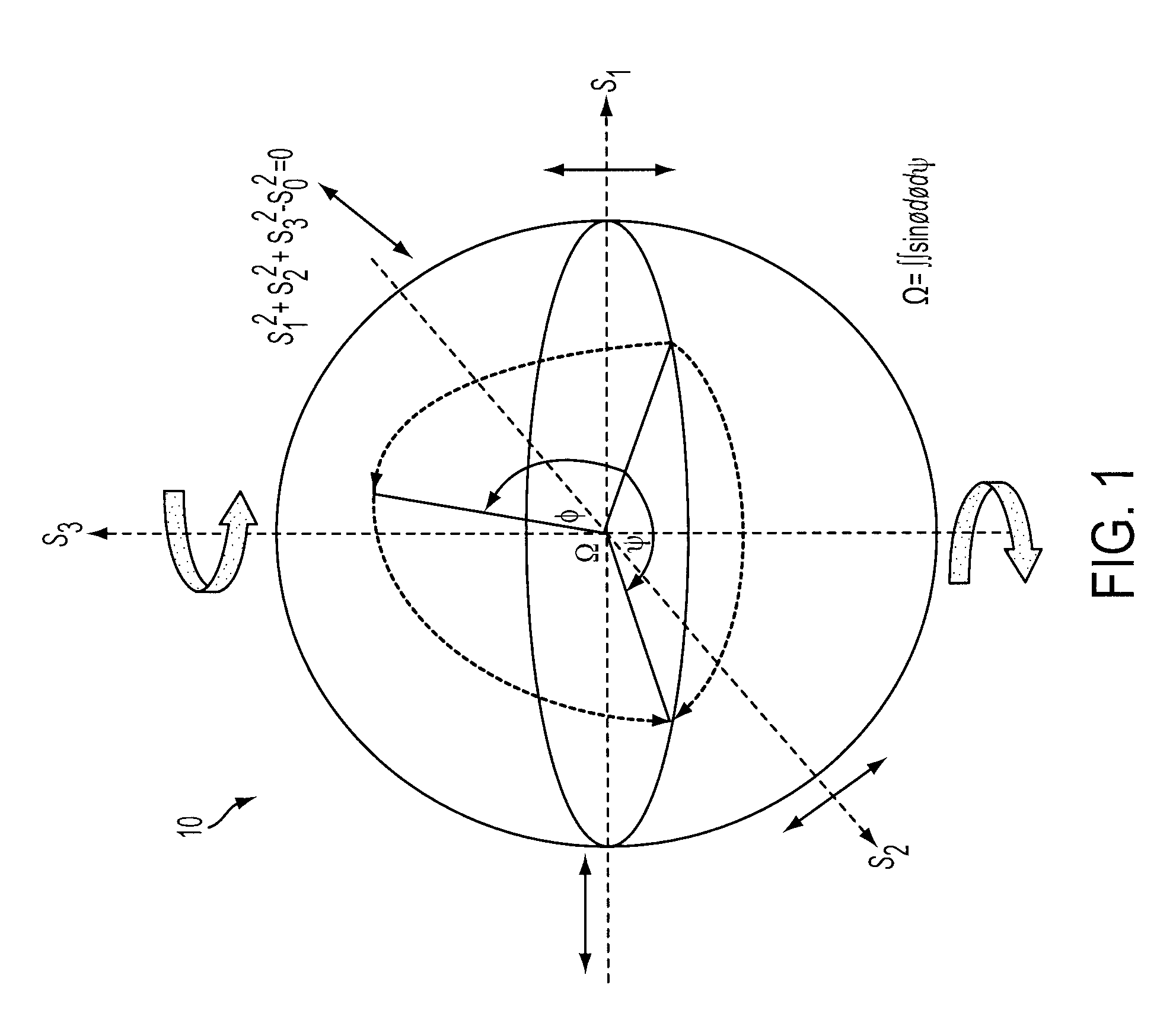
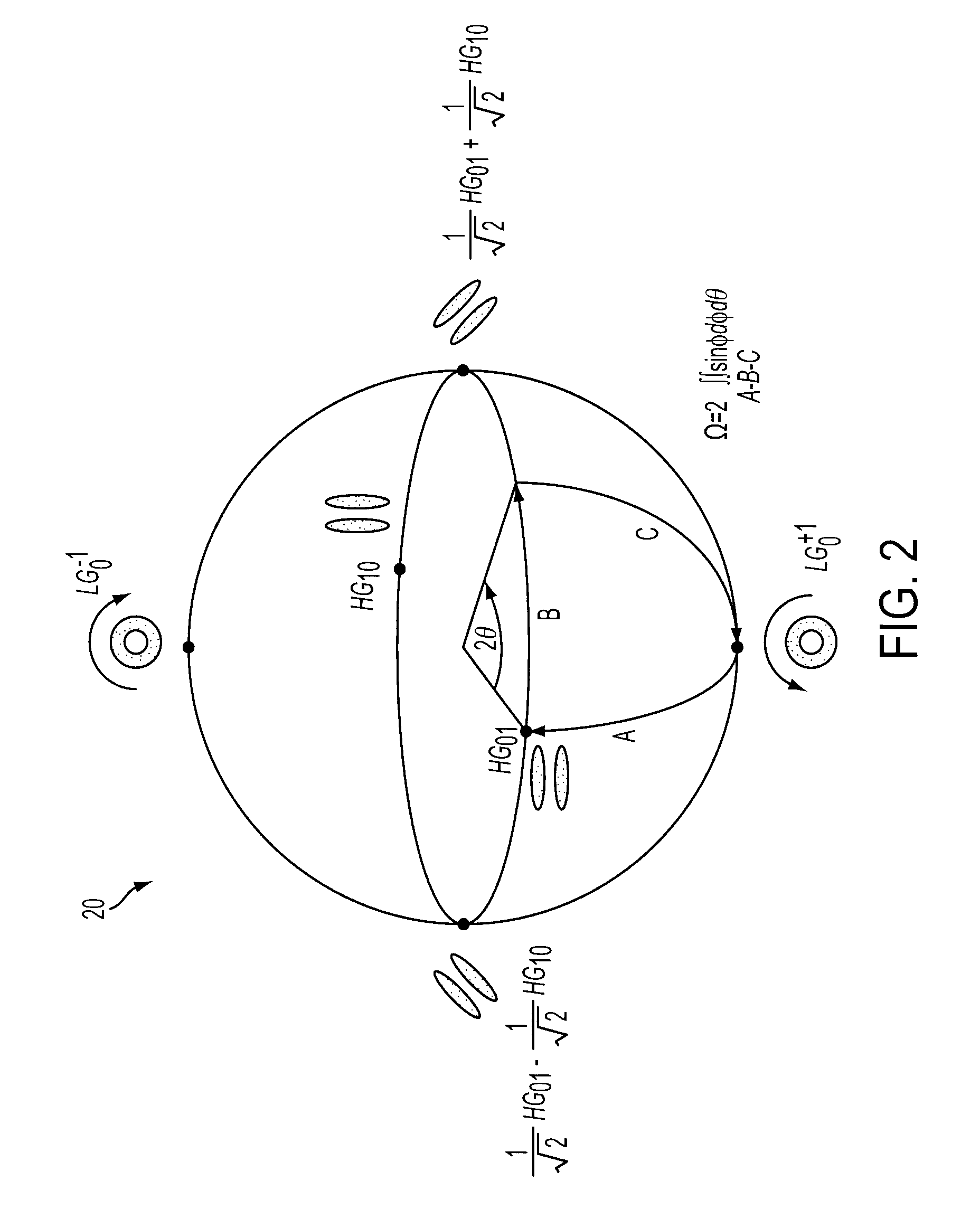
- The method involves encrypting data onto an electromagnetic beam by accumulating and modulating geometric phase through transformations of its orbital-angular-momentum modal states, using a combination of optical elements like cylindrical lenses and Dove prisms to generate and manipulate orbital-angular-momentum modes, allowing for secure key exchange and encryption.
Method and apparatus relating to secure communication
PatentInactiveUS20090028332A1
Innovation
- The method involves encrypting data onto an electromagnetic beam by accumulating geometric phase through transformation of its modal state, using a signal component and a reference component, where the signal component undergoes transformations on a Poincaré Sphere to modulate the geometric phase with data, providing a secure communication channel resistant to eavesdropping.
Cybersecurity Regulations for EM Encryption Systems
The regulatory landscape for electromagnetic encryption systems is rapidly evolving as governments and international bodies recognize the unique challenges posed by this emerging technology. Current cybersecurity frameworks, primarily designed for conventional digital encryption methods, are being reassessed to accommodate the distinct characteristics of electromagnetic modulation-based encryption systems.
The United States leads regulatory development through NIST's post-quantum cryptography standards initiative, which now includes preliminary guidelines for electromagnetic encryption validation. The Federal Information Processing Standards (FIPS) 140-3 framework is undergoing revisions to incorporate electromagnetic interference testing and shielding requirements specific to EM encryption devices. Similarly, the European Union's Cybersecurity Act and the upcoming NIS2 Directive are establishing certification schemes that address electromagnetic encryption systems' unique vulnerabilities and operational requirements.
International standardization efforts are coordinated through ISO/IEC 27001 amendments and ITU-T recommendations, focusing on electromagnetic compatibility standards for cryptographic equipment. These standards emphasize the need for rigorous testing protocols to ensure EM encryption systems maintain security integrity under various electromagnetic environments while preventing unintended signal leakage that could compromise encrypted data.
Compliance challenges emerge from the dual-use nature of electromagnetic encryption technology, which intersects with export control regulations such as the Wassenaar Arrangement and national ITAR restrictions. Organizations developing EM encryption systems must navigate complex licensing requirements while ensuring their products meet both cybersecurity standards and electromagnetic compatibility regulations.
The regulatory framework also addresses spectrum allocation concerns, as EM encryption systems require specific frequency bands for optimal operation. Coordination with telecommunications regulators becomes essential to prevent interference with existing communication infrastructure while maintaining the security benefits of electromagnetic modulation techniques.
Future regulatory developments are expected to establish mandatory security assessment protocols specifically tailored to electromagnetic encryption systems, including standardized penetration testing methodologies and continuous monitoring requirements for deployed systems.
The United States leads regulatory development through NIST's post-quantum cryptography standards initiative, which now includes preliminary guidelines for electromagnetic encryption validation. The Federal Information Processing Standards (FIPS) 140-3 framework is undergoing revisions to incorporate electromagnetic interference testing and shielding requirements specific to EM encryption devices. Similarly, the European Union's Cybersecurity Act and the upcoming NIS2 Directive are establishing certification schemes that address electromagnetic encryption systems' unique vulnerabilities and operational requirements.
International standardization efforts are coordinated through ISO/IEC 27001 amendments and ITU-T recommendations, focusing on electromagnetic compatibility standards for cryptographic equipment. These standards emphasize the need for rigorous testing protocols to ensure EM encryption systems maintain security integrity under various electromagnetic environments while preventing unintended signal leakage that could compromise encrypted data.
Compliance challenges emerge from the dual-use nature of electromagnetic encryption technology, which intersects with export control regulations such as the Wassenaar Arrangement and national ITAR restrictions. Organizations developing EM encryption systems must navigate complex licensing requirements while ensuring their products meet both cybersecurity standards and electromagnetic compatibility regulations.
The regulatory framework also addresses spectrum allocation concerns, as EM encryption systems require specific frequency bands for optimal operation. Coordination with telecommunications regulators becomes essential to prevent interference with existing communication infrastructure while maintaining the security benefits of electromagnetic modulation techniques.
Future regulatory developments are expected to establish mandatory security assessment protocols specifically tailored to electromagnetic encryption systems, including standardized penetration testing methodologies and continuous monitoring requirements for deployed systems.
Hardware Security Considerations for EM Implementation
Electromagnetic modulation-based encryption systems introduce unique hardware security challenges that require comprehensive evaluation across multiple attack vectors. The physical nature of electromagnetic signals creates vulnerabilities that traditional software-based encryption methods do not face, necessitating specialized hardware protection mechanisms.
Side-channel attacks represent the most significant threat to EM-based encryption implementations. Electromagnetic emissions from processing units can leak sensitive information about encryption keys and algorithms through power analysis, timing analysis, and electromagnetic emanation monitoring. Hardware designers must implement robust shielding techniques, including Faraday cage enclosures and electromagnetic interference filters, to prevent unauthorized signal interception. Additionally, randomization techniques in power consumption patterns and processing timing can effectively mitigate differential power analysis attacks.
Physical tampering poses another critical security concern for EM encryption hardware. Attackers may attempt to modify antenna configurations, inject malicious signals, or alter circuit components to compromise encryption integrity. Tamper-evident packaging, secure boot mechanisms, and hardware security modules provide essential protection layers. Implementation of real-time integrity monitoring systems can detect unauthorized hardware modifications and trigger automatic security responses.
Signal integrity and interference management become paramount in EM encryption systems. External electromagnetic interference can potentially corrupt encryption processes or create exploitable vulnerabilities. Hardware implementations must incorporate adaptive filtering mechanisms, error correction protocols, and signal validation systems to maintain encryption reliability under adverse electromagnetic conditions.
Key management hardware requires specialized security considerations for EM implementations. Secure key storage elements must be electromagnetically isolated to prevent key extraction through signal analysis. Hardware security modules with dedicated cryptographic processors and secure memory elements provide robust key protection. Implementation of secure key derivation functions and hardware-based random number generators ensures cryptographic key quality and unpredictability.
Manufacturing security presents unique challenges for EM encryption hardware. Supply chain integrity verification, secure manufacturing processes, and post-production security testing become critical to prevent hardware trojans and malicious modifications. Implementing hardware fingerprinting techniques and secure provisioning processes helps establish trusted hardware foundations for EM encryption systems.
Side-channel attacks represent the most significant threat to EM-based encryption implementations. Electromagnetic emissions from processing units can leak sensitive information about encryption keys and algorithms through power analysis, timing analysis, and electromagnetic emanation monitoring. Hardware designers must implement robust shielding techniques, including Faraday cage enclosures and electromagnetic interference filters, to prevent unauthorized signal interception. Additionally, randomization techniques in power consumption patterns and processing timing can effectively mitigate differential power analysis attacks.
Physical tampering poses another critical security concern for EM encryption hardware. Attackers may attempt to modify antenna configurations, inject malicious signals, or alter circuit components to compromise encryption integrity. Tamper-evident packaging, secure boot mechanisms, and hardware security modules provide essential protection layers. Implementation of real-time integrity monitoring systems can detect unauthorized hardware modifications and trigger automatic security responses.
Signal integrity and interference management become paramount in EM encryption systems. External electromagnetic interference can potentially corrupt encryption processes or create exploitable vulnerabilities. Hardware implementations must incorporate adaptive filtering mechanisms, error correction protocols, and signal validation systems to maintain encryption reliability under adverse electromagnetic conditions.
Key management hardware requires specialized security considerations for EM implementations. Secure key storage elements must be electromagnetically isolated to prevent key extraction through signal analysis. Hardware security modules with dedicated cryptographic processors and secure memory elements provide robust key protection. Implementation of secure key derivation functions and hardware-based random number generators ensures cryptographic key quality and unpredictability.
Manufacturing security presents unique challenges for EM encryption hardware. Supply chain integrity verification, secure manufacturing processes, and post-production security testing become critical to prevent hardware trojans and malicious modifications. Implementing hardware fingerprinting techniques and secure provisioning processes helps establish trusted hardware foundations for EM encryption systems.
Unlock deeper insights with PatSnap Eureka Quick Research — get a full tech report to explore trends and direct your research. Try now!
Generate Your Research Report Instantly with AI Agent
Supercharge your innovation with PatSnap Eureka AI Agent Platform!