Optimize Network Redundancy for Cyber-Secure AV Systems
MAR 5, 20269 MIN READ
Generate Your Research Report Instantly with AI Agent
Patsnap Eureka helps you evaluate technical feasibility & market potential.
AV Network Security Background and Objectives
The evolution of autonomous vehicle (AV) systems has fundamentally transformed from isolated mechanical operations to highly interconnected, software-driven platforms that rely extensively on network communications. Modern AVs integrate multiple subsystems including perception sensors, navigation units, vehicle-to-everything (V2X) communication modules, and cloud connectivity interfaces. This interconnected architecture, while enabling advanced functionalities such as real-time traffic optimization and remote diagnostics, has simultaneously expanded the attack surface for potential cyber threats.
The proliferation of connected vehicles has introduced unprecedented cybersecurity challenges that extend beyond traditional automotive safety concerns. Unlike conventional vehicles, AVs continuously exchange critical data with external networks, infrastructure systems, and other vehicles. This constant connectivity creates multiple entry points for malicious actors who could potentially compromise vehicle operations, passenger safety, or broader transportation infrastructure. Recent incidents involving automotive cybersecurity breaches have demonstrated the real-world implications of inadequate network security measures.
Network redundancy in AV systems has emerged as a critical defense mechanism against both accidental failures and deliberate cyber attacks. Traditional redundancy approaches, primarily designed for hardware fault tolerance, prove insufficient when addressing sophisticated cyber threats that can simultaneously target multiple network pathways. The challenge lies in developing redundancy strategies that maintain operational continuity while preventing the propagation of security breaches across backup systems.
The primary objective of optimizing network redundancy for cyber-secure AV systems centers on establishing resilient communication architectures that can withstand coordinated cyber attacks without compromising vehicle functionality. This involves creating intelligent redundancy mechanisms that can dynamically isolate compromised network segments while maintaining essential vehicle operations through secure alternative pathways. The goal extends beyond simple backup systems to encompass adaptive security frameworks that can respond to emerging threats in real-time.
Furthermore, the optimization effort aims to balance security requirements with performance constraints inherent in automotive applications. AV systems demand ultra-low latency communications for safety-critical functions, making traditional security measures potentially incompatible with operational requirements. The objective includes developing lightweight security protocols and redundancy mechanisms that preserve real-time performance while providing robust protection against cyber threats.
The strategic importance of this optimization extends to ensuring regulatory compliance with emerging automotive cybersecurity standards while maintaining interoperability across diverse AV platforms and infrastructure systems. Success in this domain will enable the safe deployment of autonomous vehicles at scale while building public trust in connected transportation technologies.
The proliferation of connected vehicles has introduced unprecedented cybersecurity challenges that extend beyond traditional automotive safety concerns. Unlike conventional vehicles, AVs continuously exchange critical data with external networks, infrastructure systems, and other vehicles. This constant connectivity creates multiple entry points for malicious actors who could potentially compromise vehicle operations, passenger safety, or broader transportation infrastructure. Recent incidents involving automotive cybersecurity breaches have demonstrated the real-world implications of inadequate network security measures.
Network redundancy in AV systems has emerged as a critical defense mechanism against both accidental failures and deliberate cyber attacks. Traditional redundancy approaches, primarily designed for hardware fault tolerance, prove insufficient when addressing sophisticated cyber threats that can simultaneously target multiple network pathways. The challenge lies in developing redundancy strategies that maintain operational continuity while preventing the propagation of security breaches across backup systems.
The primary objective of optimizing network redundancy for cyber-secure AV systems centers on establishing resilient communication architectures that can withstand coordinated cyber attacks without compromising vehicle functionality. This involves creating intelligent redundancy mechanisms that can dynamically isolate compromised network segments while maintaining essential vehicle operations through secure alternative pathways. The goal extends beyond simple backup systems to encompass adaptive security frameworks that can respond to emerging threats in real-time.
Furthermore, the optimization effort aims to balance security requirements with performance constraints inherent in automotive applications. AV systems demand ultra-low latency communications for safety-critical functions, making traditional security measures potentially incompatible with operational requirements. The objective includes developing lightweight security protocols and redundancy mechanisms that preserve real-time performance while providing robust protection against cyber threats.
The strategic importance of this optimization extends to ensuring regulatory compliance with emerging automotive cybersecurity standards while maintaining interoperability across diverse AV platforms and infrastructure systems. Success in this domain will enable the safe deployment of autonomous vehicles at scale while building public trust in connected transportation technologies.
Market Demand for Cyber-Secure AV Network Solutions
The global audiovisual industry is experiencing unprecedented growth driven by digital transformation initiatives across enterprise, education, healthcare, and government sectors. Organizations increasingly rely on sophisticated AV systems for critical communications, remote collaboration, and operational continuity. This dependency has elevated AV infrastructure from convenience tools to mission-critical systems requiring enterprise-grade reliability and security.
Corporate environments demonstrate particularly strong demand for cyber-secure AV solutions as hybrid work models become permanent fixtures. Companies investing in boardroom technologies, digital signage networks, and campus-wide communication systems recognize that traditional AV security approaches are insufficient against modern cyber threats. The integration of AV systems with corporate networks creates potential attack vectors that malicious actors can exploit to access sensitive data or disrupt operations.
Educational institutions represent another significant market segment driving demand for secure AV network solutions. Universities and K-12 schools deploying distance learning technologies, lecture capture systems, and interactive classroom displays require robust security frameworks to protect student data and maintain educational continuity. Recent high-profile cyberattacks on educational networks have heightened awareness of AV system vulnerabilities.
Healthcare organizations face unique challenges requiring specialized cyber-secure AV solutions. Telemedicine platforms, surgical display systems, and patient communication networks must comply with strict regulatory requirements while maintaining operational reliability. The critical nature of healthcare communications makes network redundancy and cybersecurity paramount concerns for medical facility administrators.
Government and defense sectors exhibit growing demand for highly secure AV network architectures. Public safety communications, emergency management systems, and secure briefing facilities require solutions that meet stringent security clearance levels while providing failover capabilities during crisis situations.
The market demand extends beyond traditional AV applications to encompass emerging technologies such as digital twins, augmented reality training systems, and IoT-integrated smart building platforms. These advanced implementations require sophisticated network redundancy strategies to ensure continuous operation while maintaining cybersecurity postures against evolving threat landscapes.
Supply chain disruptions and geopolitical tensions have further intensified demand for domestically sourced, security-verified AV components. Organizations seek solutions that provide both technical redundancy and supply chain resilience to mitigate risks associated with foreign-manufactured equipment and potential backdoor vulnerabilities.
Corporate environments demonstrate particularly strong demand for cyber-secure AV solutions as hybrid work models become permanent fixtures. Companies investing in boardroom technologies, digital signage networks, and campus-wide communication systems recognize that traditional AV security approaches are insufficient against modern cyber threats. The integration of AV systems with corporate networks creates potential attack vectors that malicious actors can exploit to access sensitive data or disrupt operations.
Educational institutions represent another significant market segment driving demand for secure AV network solutions. Universities and K-12 schools deploying distance learning technologies, lecture capture systems, and interactive classroom displays require robust security frameworks to protect student data and maintain educational continuity. Recent high-profile cyberattacks on educational networks have heightened awareness of AV system vulnerabilities.
Healthcare organizations face unique challenges requiring specialized cyber-secure AV solutions. Telemedicine platforms, surgical display systems, and patient communication networks must comply with strict regulatory requirements while maintaining operational reliability. The critical nature of healthcare communications makes network redundancy and cybersecurity paramount concerns for medical facility administrators.
Government and defense sectors exhibit growing demand for highly secure AV network architectures. Public safety communications, emergency management systems, and secure briefing facilities require solutions that meet stringent security clearance levels while providing failover capabilities during crisis situations.
The market demand extends beyond traditional AV applications to encompass emerging technologies such as digital twins, augmented reality training systems, and IoT-integrated smart building platforms. These advanced implementations require sophisticated network redundancy strategies to ensure continuous operation while maintaining cybersecurity postures against evolving threat landscapes.
Supply chain disruptions and geopolitical tensions have further intensified demand for domestically sourced, security-verified AV components. Organizations seek solutions that provide both technical redundancy and supply chain resilience to mitigate risks associated with foreign-manufactured equipment and potential backdoor vulnerabilities.
Current AV Network Vulnerabilities and Security Challenges
Autonomous vehicle networks face unprecedented cybersecurity challenges as they integrate complex interconnected systems spanning vehicle-to-vehicle (V2V), vehicle-to-infrastructure (V2I), and vehicle-to-everything (V2X) communications. These networks operate across multiple communication protocols including 5G, Wi-Fi, Bluetooth, and dedicated short-range communications (DSRC), creating numerous attack vectors that malicious actors can exploit.
The distributed nature of AV systems presents significant vulnerabilities through their reliance on cloud connectivity for real-time data processing, mapping updates, and fleet management. Edge computing nodes, while reducing latency, introduce additional entry points where attackers can potentially compromise entire vehicle networks. The integration of third-party components and software creates supply chain vulnerabilities that are difficult to monitor and secure comprehensively.
Current AV architectures struggle with inadequate network segmentation, allowing lateral movement of threats across critical systems. Many implementations lack robust authentication mechanisms for inter-vehicle communications, making them susceptible to spoofing attacks where malicious entities can impersonate legitimate vehicles or infrastructure components. The high-speed nature of vehicular communications often prioritizes performance over security validation, creating windows of opportunity for real-time attacks.
Legacy automotive systems integration poses another critical challenge, as traditional vehicle components were not designed with cybersecurity as a primary consideration. The transition period where conventional and autonomous systems coexist creates hybrid vulnerabilities that are particularly difficult to address through standard security frameworks.
Data integrity and privacy concerns compound these challenges, as AV systems continuously collect and transmit sensitive location, behavioral, and operational data. Current encryption methods may prove insufficient against quantum computing threats, while key management across distributed vehicle fleets remains complex and resource-intensive.
The rapid evolution of AV technology often outpaces security standard development, resulting in implementations that rely on reactive rather than proactive security measures. This creates a persistent gap between emerging threats and available countermeasures, particularly in scenarios involving coordinated attacks on multiple vehicles or infrastructure systems simultaneously.
The distributed nature of AV systems presents significant vulnerabilities through their reliance on cloud connectivity for real-time data processing, mapping updates, and fleet management. Edge computing nodes, while reducing latency, introduce additional entry points where attackers can potentially compromise entire vehicle networks. The integration of third-party components and software creates supply chain vulnerabilities that are difficult to monitor and secure comprehensively.
Current AV architectures struggle with inadequate network segmentation, allowing lateral movement of threats across critical systems. Many implementations lack robust authentication mechanisms for inter-vehicle communications, making them susceptible to spoofing attacks where malicious entities can impersonate legitimate vehicles or infrastructure components. The high-speed nature of vehicular communications often prioritizes performance over security validation, creating windows of opportunity for real-time attacks.
Legacy automotive systems integration poses another critical challenge, as traditional vehicle components were not designed with cybersecurity as a primary consideration. The transition period where conventional and autonomous systems coexist creates hybrid vulnerabilities that are particularly difficult to address through standard security frameworks.
Data integrity and privacy concerns compound these challenges, as AV systems continuously collect and transmit sensitive location, behavioral, and operational data. Current encryption methods may prove insufficient against quantum computing threats, while key management across distributed vehicle fleets remains complex and resource-intensive.
The rapid evolution of AV technology often outpaces security standard development, resulting in implementations that rely on reactive rather than proactive security measures. This creates a persistent gap between emerging threats and available countermeasures, particularly in scenarios involving coordinated attacks on multiple vehicles or infrastructure systems simultaneously.
Existing Network Redundancy Solutions for AV Systems
01 Redundant network path configuration and failover mechanisms
Network redundancy can be achieved through the implementation of multiple network paths between nodes or devices. When a primary path fails, the system automatically switches to a backup path to maintain connectivity. This approach involves configuring redundant links, monitoring path availability, and implementing automatic failover protocols to ensure continuous network operation without service interruption.- Redundant network path configuration and failover mechanisms: Network redundancy can be achieved by establishing multiple communication paths between network nodes. When a primary path fails, the system automatically switches to a backup path to maintain network connectivity. This approach involves configuring redundant links, implementing path monitoring mechanisms, and enabling automatic failover protocols to ensure continuous network operation without service interruption.
- Redundant network device and component architecture: Implementing redundancy at the hardware level involves deploying duplicate network devices such as routers, switches, and controllers. These redundant components operate in active-standby or active-active configurations to provide continuous service availability. The architecture includes synchronization mechanisms between redundant devices and health monitoring systems to detect failures and trigger seamless transitions to backup components.
- Network topology redundancy and ring protection: Network redundancy can be implemented through specific topological designs such as ring, mesh, or dual-homed configurations. These topologies provide multiple physical paths for data transmission and incorporate protection switching mechanisms. When a link or node failure occurs, traffic is automatically rerouted through alternative paths within the topology to maintain network connectivity and minimize service disruption.
- Protocol-based redundancy and load balancing: Redundancy protocols enable intelligent traffic distribution and automatic failover across multiple network paths or devices. These protocols monitor network conditions, detect failures, and redistribute traffic to maintain optimal performance. The mechanisms include dynamic routing protocols, virtual router redundancy protocols, and link aggregation techniques that provide both redundancy and load balancing capabilities across the network infrastructure.
- Data synchronization and state replication for redundant systems: Maintaining consistency between redundant network elements requires sophisticated data synchronization and state replication mechanisms. These systems ensure that configuration data, routing tables, session information, and operational states are continuously synchronized across redundant components. This enables seamless failover without data loss or service interruption, as backup systems maintain current operational context and can immediately assume active roles when needed.
02 Redundant network device and component architecture
Implementing redundancy at the hardware level involves deploying duplicate network devices such as routers, switches, and controllers. These redundant components operate in active-standby or active-active configurations, where backup devices can immediately take over operations when primary devices fail. This architecture ensures high availability and minimizes single points of failure in network infrastructure.Expand Specific Solutions03 Network topology redundancy and ring configurations
Redundancy can be achieved through specific network topologies such as ring, mesh, or dual-homed configurations. These topologies provide multiple physical connections between network segments, allowing traffic to be rerouted automatically when a link or node fails. Ring-based redundancy protocols enable rapid recovery and maintain network integrity even during component failures.Expand Specific Solutions04 Protocol-based redundancy and load balancing
Network redundancy can be implemented through specialized protocols that manage traffic distribution and failover across multiple paths or devices. These protocols enable load balancing during normal operations and provide seamless transition to backup resources during failures. The approach includes dynamic routing protocols, virtual router redundancy protocols, and link aggregation techniques that optimize network utilization while maintaining high availability.Expand Specific Solutions05 Data center and cloud network redundancy
In data center and cloud environments, redundancy is implemented through distributed architectures that span multiple physical locations and availability zones. This includes redundant power supplies, network connections, and server clusters that work together to provide fault tolerance. The system ensures that services remain available even when entire data center components or facilities experience outages, utilizing geographic distribution and resource replication strategies.Expand Specific Solutions
Key Players in AV Network Security Industry
The competitive landscape for optimizing network redundancy in cyber-secure AV systems is characterized by a mature market with established infrastructure giants competing alongside specialized technology providers. The industry has reached an advanced development stage, driven by increasing cybersecurity threats and autonomous vehicle deployment demands. Market leaders like Siemens AG, Cisco Technology, Huawei Technologies, and ABB Ltd. leverage their extensive networking and automation expertise to deliver comprehensive solutions. Technology maturity varies significantly across players - while telecommunications veterans like Ericsson, NTT, and Nokia Solutions & Networks bring proven network resilience capabilities, emerging companies like Kyland Technology and specialized firms such as Shanghai Advanced Avionics focus on niche applications. The convergence of traditional networking companies with automotive and aerospace players like Volkswagen Group and Airbus Operations indicates growing cross-industry collaboration in developing robust, redundant systems for mission-critical AV applications.
Siemens AG
Technical Solution: Siemens implements industrial-grade network redundancy solutions adapted for automotive applications, featuring their PROFINET and Industrial Ethernet technologies modified for vehicle environments. Their approach utilizes redundant ring topologies with sub-millisecond failover times, ensuring continuous communication between critical vehicle systems. The solution incorporates deep packet inspection and anomaly detection algorithms specifically tuned for automotive communication patterns. Siemens' technology includes hardware-based security modules that provide cryptographic protection while maintaining deterministic network behavior essential for safety-critical autonomous vehicle functions. Their system supports hot-swappable network components and automatic network reconfiguration to maintain operational continuity during maintenance or security incidents.
Strengths: Proven industrial automation experience and deterministic network performance. Weaknesses: Traditional industrial focus may require adaptation for modern automotive connectivity requirements.
Cisco Technology, Inc.
Technical Solution: Cisco implements Software-Defined Networking (SDN) architecture with redundant network paths and real-time failover mechanisms for autonomous vehicle systems. Their solution features distributed network controllers that maintain multiple communication channels between vehicle components, ensuring continuous connectivity even when primary paths are compromised. The system employs advanced encryption protocols and intrusion detection systems specifically designed for vehicular networks. Cisco's approach includes network segmentation to isolate critical safety functions from infotainment systems, reducing attack surfaces while maintaining operational redundancy through dynamic routing protocols that automatically reroute traffic when security threats are detected.
Strengths: Industry-leading network security expertise and proven SDN solutions. Weaknesses: Higher complexity in implementation and potential latency in dynamic routing decisions.
Core Innovations in Cyber-Secure AV Redundancy
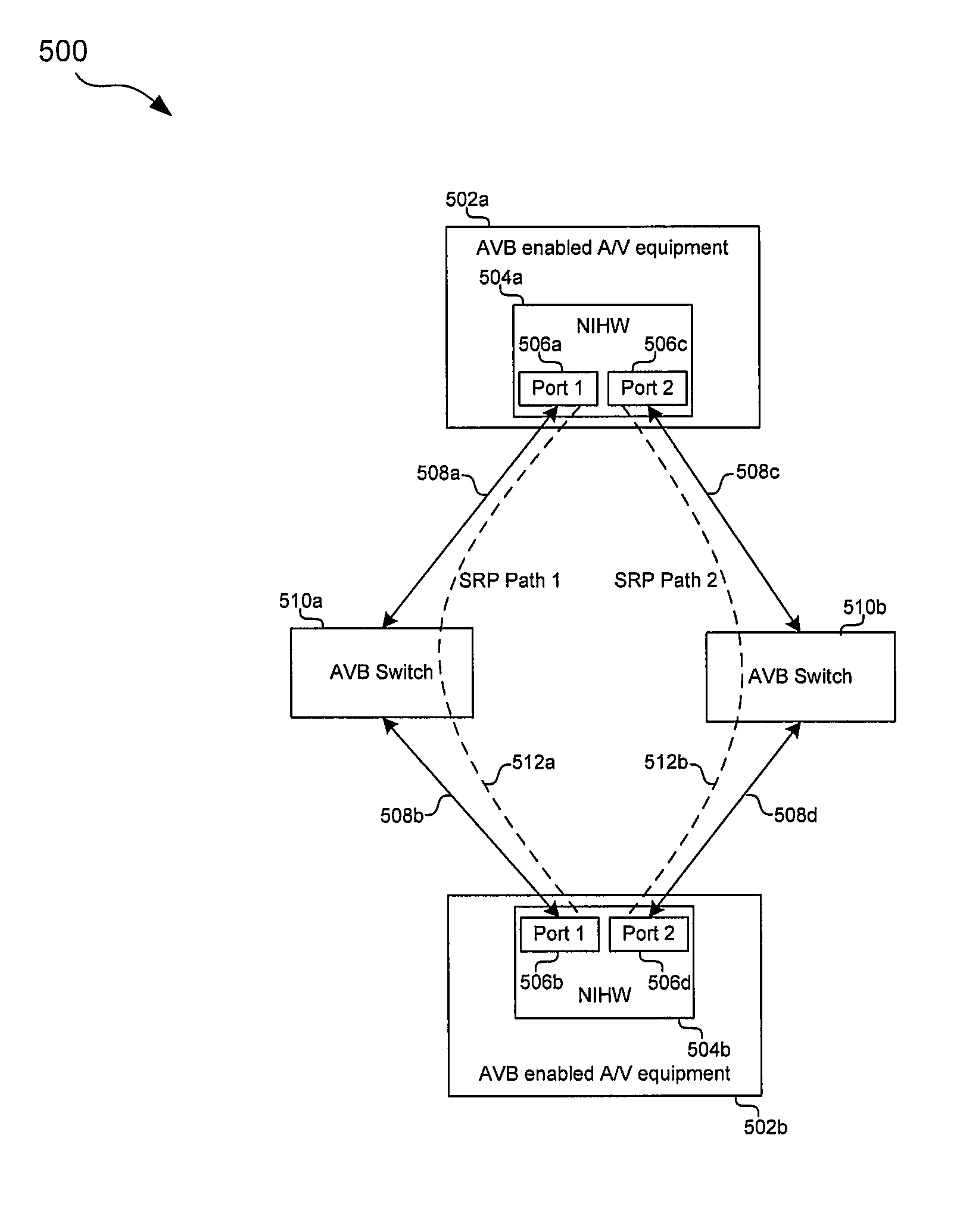
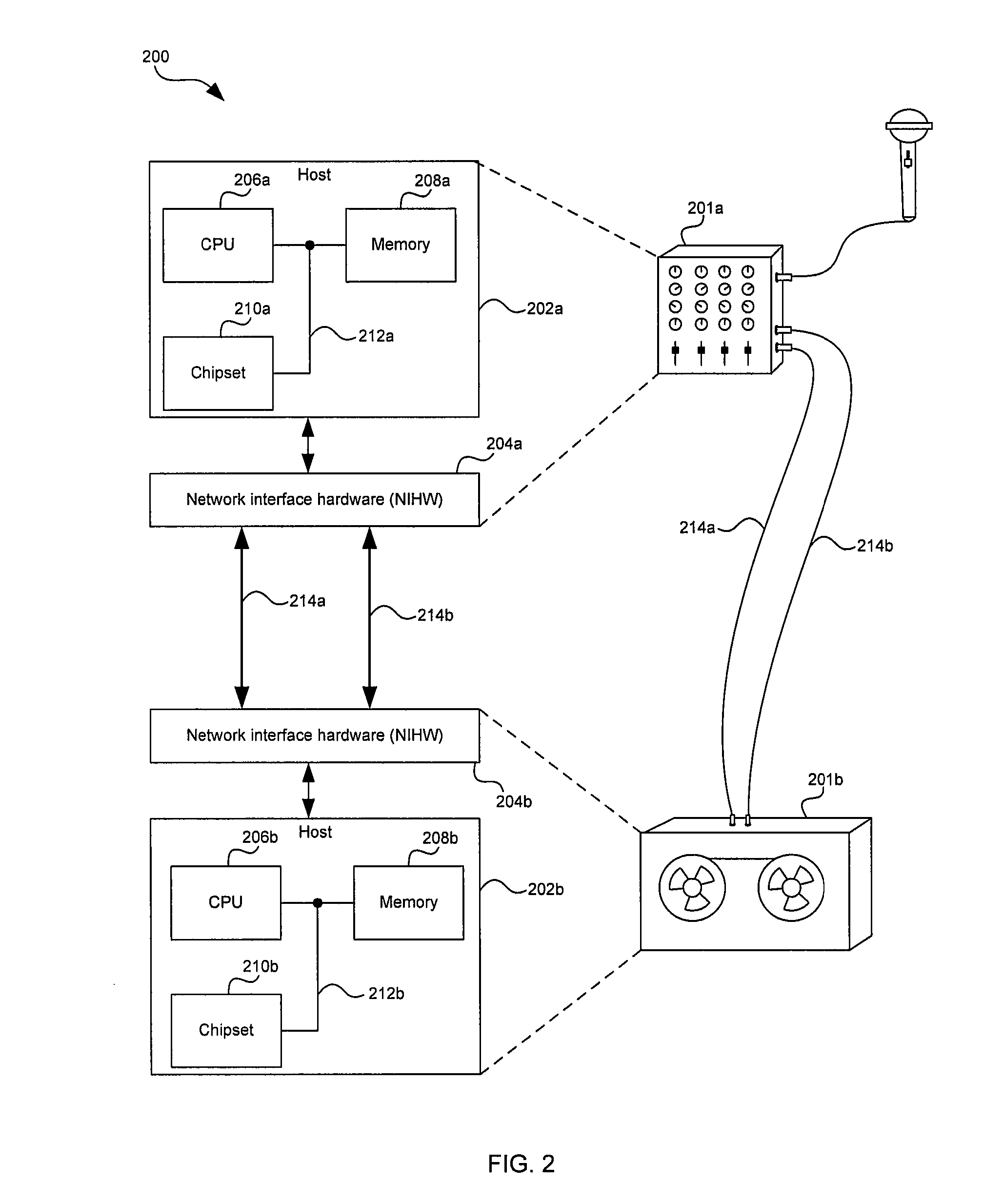
Method and system for implementing redundancy for streaming data in audio video bridging networks
PatentInactiveUS8254248B2
Innovation
- Implementing redundancy through the use of redundant network interface hardware devices and redundant network ports, as well as link aggregation protocols, to transmit and receive multiple data streams where one or more streams comprise redundant data, ensuring that packet losses and hardware failures have minimal impact on the user experience.
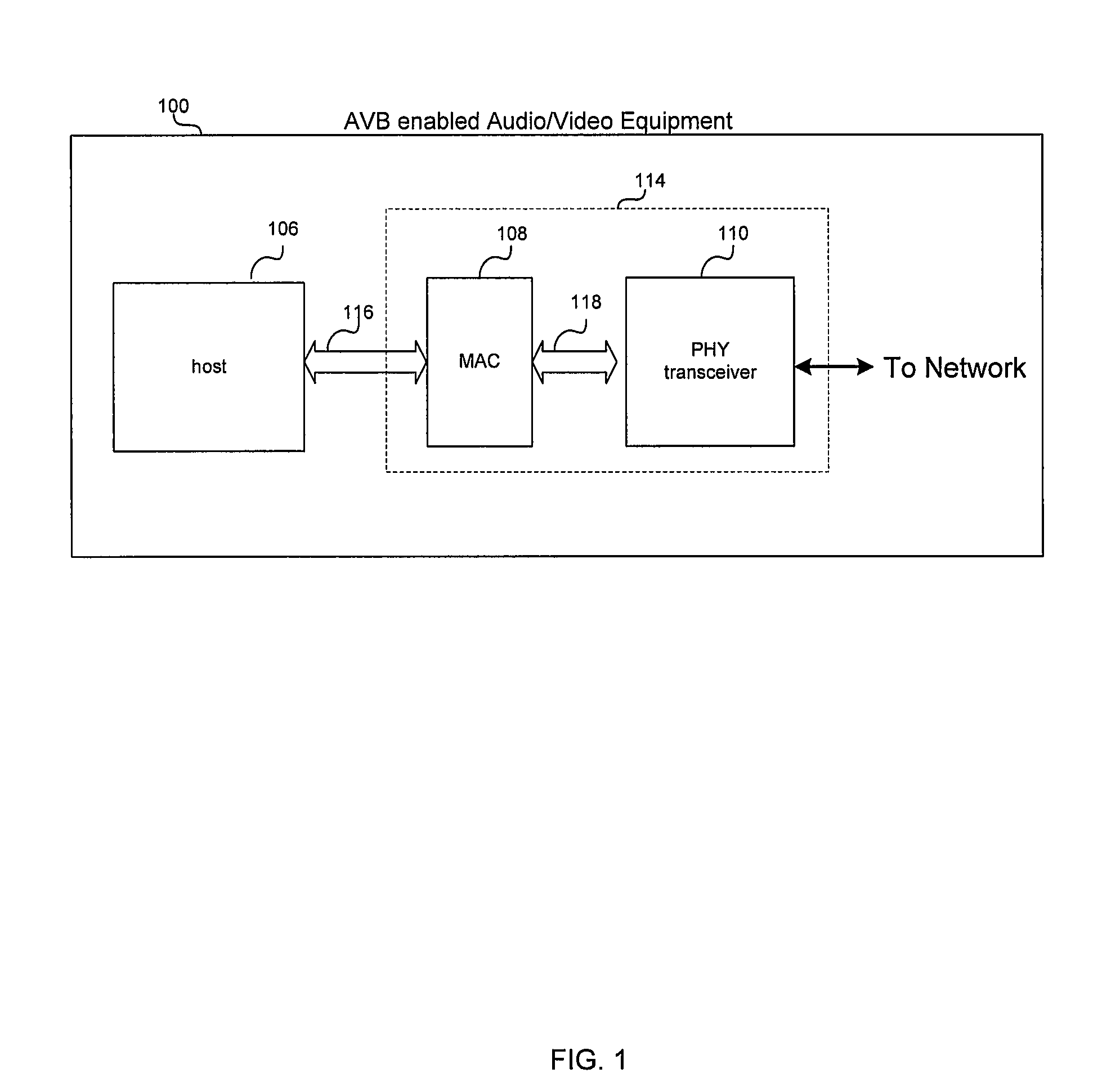
System and method for network redundancy
PatentInactiveUS20040165525A1
Innovation
- The implementation of a redundant Ethernet network architecture using multiple IEEE 802.3 MAC PHYs with an additional data link driver between the network stack and the IEEE 802.3 MAC PHY, allowing for automatic and transparent network access redundancy and end-to-end error detection, independent of employed network redundancy methods, without requiring changes to higher-layer protocols or applications.
Cybersecurity Compliance Standards for AV Systems
Cybersecurity compliance standards for AV systems represent a critical framework that governs the security requirements and operational protocols necessary for protecting audiovisual infrastructure from cyber threats. These standards establish mandatory guidelines that organizations must follow to ensure their AV systems meet regulatory requirements while maintaining operational integrity and data protection.
The International Organization for Standardization (ISO) 27001 serves as the foundational framework for information security management systems in AV environments. This standard requires organizations to implement comprehensive risk assessment procedures, establish security controls, and maintain continuous monitoring of their AV network infrastructure. Additionally, the NIST Cybersecurity Framework provides specific guidelines for identifying, protecting, detecting, responding to, and recovering from cybersecurity incidents affecting AV systems.
Industry-specific compliance requirements vary significantly across sectors. Healthcare organizations must adhere to HIPAA regulations when implementing AV systems that handle patient information, while financial institutions must comply with SOX and PCI-DSS standards. Educational institutions face FERPA compliance requirements, and government agencies must meet FISMA and FedRAMP standards for their AV deployments.
The Common Criteria (CC) evaluation framework establishes security evaluation standards specifically applicable to AV system components. This framework requires manufacturers to demonstrate that their products meet specific security functional requirements and undergo rigorous testing procedures. Products achieving CC certification provide organizations with validated security assurance levels that support compliance objectives.
Emerging compliance frameworks address cloud-based AV systems and hybrid deployments. The Cloud Security Alliance (CSA) has developed specific guidelines for securing cloud-connected AV infrastructure, while the Industrial Internet Consortium (IIC) provides standards for IoT-enabled AV devices. These frameworks emphasize zero-trust architecture principles, requiring continuous authentication and authorization for all system components.
Regular compliance auditing and assessment procedures ensure ongoing adherence to established standards. Organizations must implement automated compliance monitoring tools, conduct periodic security assessments, and maintain detailed documentation of their security controls and incident response procedures to demonstrate regulatory compliance.
The International Organization for Standardization (ISO) 27001 serves as the foundational framework for information security management systems in AV environments. This standard requires organizations to implement comprehensive risk assessment procedures, establish security controls, and maintain continuous monitoring of their AV network infrastructure. Additionally, the NIST Cybersecurity Framework provides specific guidelines for identifying, protecting, detecting, responding to, and recovering from cybersecurity incidents affecting AV systems.
Industry-specific compliance requirements vary significantly across sectors. Healthcare organizations must adhere to HIPAA regulations when implementing AV systems that handle patient information, while financial institutions must comply with SOX and PCI-DSS standards. Educational institutions face FERPA compliance requirements, and government agencies must meet FISMA and FedRAMP standards for their AV deployments.
The Common Criteria (CC) evaluation framework establishes security evaluation standards specifically applicable to AV system components. This framework requires manufacturers to demonstrate that their products meet specific security functional requirements and undergo rigorous testing procedures. Products achieving CC certification provide organizations with validated security assurance levels that support compliance objectives.
Emerging compliance frameworks address cloud-based AV systems and hybrid deployments. The Cloud Security Alliance (CSA) has developed specific guidelines for securing cloud-connected AV infrastructure, while the Industrial Internet Consortium (IIC) provides standards for IoT-enabled AV devices. These frameworks emphasize zero-trust architecture principles, requiring continuous authentication and authorization for all system components.
Regular compliance auditing and assessment procedures ensure ongoing adherence to established standards. Organizations must implement automated compliance monitoring tools, conduct periodic security assessments, and maintain detailed documentation of their security controls and incident response procedures to demonstrate regulatory compliance.
Risk Assessment Framework for AV Network Infrastructure
A comprehensive risk assessment framework for autonomous vehicle network infrastructure requires systematic evaluation of vulnerabilities across multiple layers of connectivity and communication systems. The framework must address both traditional cybersecurity threats and emerging risks specific to vehicular networks, including vehicle-to-vehicle (V2V), vehicle-to-infrastructure (V2I), and vehicle-to-everything (V2X) communications.
The assessment methodology should begin with asset identification and classification, mapping all network components including onboard computing units, communication modules, sensors, and external connectivity interfaces. Each component requires evaluation based on criticality levels, with safety-critical systems receiving the highest priority for protection measures.
Threat modeling forms the core of the framework, encompassing attack vectors such as man-in-the-middle attacks, denial-of-service attempts, data injection, and unauthorized access to vehicle control systems. The framework must consider both direct attacks on individual vehicles and coordinated attacks targeting fleet-wide vulnerabilities or infrastructure dependencies.
Vulnerability assessment protocols should incorporate both automated scanning tools and manual penetration testing specifically designed for automotive environments. This includes evaluation of wireless communication protocols, encryption implementations, authentication mechanisms, and network segmentation effectiveness across different operational scenarios.
Risk quantification requires establishing probability matrices that account for the dynamic nature of vehicular networks, where vehicles continuously join and leave network clusters. The framework must evaluate risks during various operational states including parking, urban driving, highway operations, and charging or maintenance periods.
Impact analysis extends beyond traditional data security concerns to encompass physical safety implications, regulatory compliance requirements, and potential cascading effects on transportation infrastructure. The framework should establish clear risk tolerance thresholds and escalation procedures for different threat levels.
Continuous monitoring capabilities must be integrated into the framework, enabling real-time threat detection and response across distributed vehicle fleets. This includes establishing baseline behavioral patterns for network traffic and implementing anomaly detection systems capable of identifying potential security incidents while minimizing false positives that could disrupt normal operations.
The assessment methodology should begin with asset identification and classification, mapping all network components including onboard computing units, communication modules, sensors, and external connectivity interfaces. Each component requires evaluation based on criticality levels, with safety-critical systems receiving the highest priority for protection measures.
Threat modeling forms the core of the framework, encompassing attack vectors such as man-in-the-middle attacks, denial-of-service attempts, data injection, and unauthorized access to vehicle control systems. The framework must consider both direct attacks on individual vehicles and coordinated attacks targeting fleet-wide vulnerabilities or infrastructure dependencies.
Vulnerability assessment protocols should incorporate both automated scanning tools and manual penetration testing specifically designed for automotive environments. This includes evaluation of wireless communication protocols, encryption implementations, authentication mechanisms, and network segmentation effectiveness across different operational scenarios.
Risk quantification requires establishing probability matrices that account for the dynamic nature of vehicular networks, where vehicles continuously join and leave network clusters. The framework must evaluate risks during various operational states including parking, urban driving, highway operations, and charging or maintenance periods.
Impact analysis extends beyond traditional data security concerns to encompass physical safety implications, regulatory compliance requirements, and potential cascading effects on transportation infrastructure. The framework should establish clear risk tolerance thresholds and escalation procedures for different threat levels.
Continuous monitoring capabilities must be integrated into the framework, enabling real-time threat detection and response across distributed vehicle fleets. This includes establishing baseline behavioral patterns for network traffic and implementing anomaly detection systems capable of identifying potential security incidents while minimizing false positives that could disrupt normal operations.
Unlock deeper insights with Patsnap Eureka Quick Research — get a full tech report to explore trends and direct your research. Try now!
Generate Your Research Report Instantly with AI Agent
Supercharge your innovation with Patsnap Eureka AI Agent Platform!