Optimizing Cyber Resilience Tools for Autonomous Vehicles
MAR 5, 20269 MIN READ
Generate Your Research Report Instantly with AI Agent
Patsnap Eureka helps you evaluate technical feasibility & market potential.
Autonomous Vehicle Cyber Resilience Background and Objectives
The evolution of autonomous vehicles represents one of the most significant technological transformations in modern transportation, fundamentally reshaping how we conceptualize mobility, safety, and connectivity. Since the early 2000s, autonomous vehicle technology has progressed from basic driver assistance systems to sophisticated self-driving capabilities, integrating advanced sensors, artificial intelligence, and real-time data processing. This technological advancement has created unprecedented opportunities for enhanced road safety, improved traffic efficiency, and increased accessibility for mobility-impaired individuals.
However, the increasing connectivity and automation of vehicles have simultaneously introduced complex cybersecurity vulnerabilities that pose substantial risks to both individual users and broader transportation infrastructure. Modern autonomous vehicles rely heavily on interconnected systems, including vehicle-to-vehicle communication, cloud-based services, over-the-air updates, and integration with smart city infrastructure. These dependencies create multiple attack vectors that malicious actors can exploit to compromise vehicle safety, steal sensitive data, or disrupt transportation networks.
The cyber threat landscape for autonomous vehicles encompasses various attack scenarios, ranging from remote vehicle hijacking and sensor manipulation to data breaches and denial-of-service attacks on critical transportation infrastructure. Recent security research has demonstrated the feasibility of exploiting vulnerabilities in vehicle communication protocols, infotainment systems, and sensor networks, highlighting the urgent need for robust cybersecurity measures.
Current cybersecurity approaches for autonomous vehicles often rely on traditional security frameworks that were not specifically designed for the unique challenges of mobile, real-time, safety-critical systems. These conventional solutions frequently struggle with the dynamic nature of vehicular environments, the need for ultra-low latency responses, and the requirement to maintain operational continuity even under cyber attack conditions.
The primary objective of optimizing cyber resilience tools for autonomous vehicles is to develop comprehensive security frameworks that can proactively detect, prevent, and respond to cyber threats while maintaining the operational integrity and safety of autonomous driving systems. This involves creating adaptive security mechanisms that can evolve with emerging threat patterns, implementing real-time threat intelligence systems, and establishing robust incident response protocols specifically tailored for vehicular environments.
Furthermore, the optimization effort aims to achieve seamless integration of cybersecurity measures without compromising the performance, reliability, or user experience of autonomous vehicle systems, ensuring that security enhancements support rather than hinder the advancement of autonomous driving technology.
However, the increasing connectivity and automation of vehicles have simultaneously introduced complex cybersecurity vulnerabilities that pose substantial risks to both individual users and broader transportation infrastructure. Modern autonomous vehicles rely heavily on interconnected systems, including vehicle-to-vehicle communication, cloud-based services, over-the-air updates, and integration with smart city infrastructure. These dependencies create multiple attack vectors that malicious actors can exploit to compromise vehicle safety, steal sensitive data, or disrupt transportation networks.
The cyber threat landscape for autonomous vehicles encompasses various attack scenarios, ranging from remote vehicle hijacking and sensor manipulation to data breaches and denial-of-service attacks on critical transportation infrastructure. Recent security research has demonstrated the feasibility of exploiting vulnerabilities in vehicle communication protocols, infotainment systems, and sensor networks, highlighting the urgent need for robust cybersecurity measures.
Current cybersecurity approaches for autonomous vehicles often rely on traditional security frameworks that were not specifically designed for the unique challenges of mobile, real-time, safety-critical systems. These conventional solutions frequently struggle with the dynamic nature of vehicular environments, the need for ultra-low latency responses, and the requirement to maintain operational continuity even under cyber attack conditions.
The primary objective of optimizing cyber resilience tools for autonomous vehicles is to develop comprehensive security frameworks that can proactively detect, prevent, and respond to cyber threats while maintaining the operational integrity and safety of autonomous driving systems. This involves creating adaptive security mechanisms that can evolve with emerging threat patterns, implementing real-time threat intelligence systems, and establishing robust incident response protocols specifically tailored for vehicular environments.
Furthermore, the optimization effort aims to achieve seamless integration of cybersecurity measures without compromising the performance, reliability, or user experience of autonomous vehicle systems, ensuring that security enhancements support rather than hinder the advancement of autonomous driving technology.
Market Demand for Secure Autonomous Vehicle Systems
The global autonomous vehicle market is experiencing unprecedented growth driven by increasing consumer demand for enhanced safety, convenience, and mobility solutions. As autonomous vehicles transition from experimental prototypes to commercial reality, the critical importance of cybersecurity has emerged as a primary concern for consumers, manufacturers, and regulatory bodies alike. This heightened awareness stems from the recognition that autonomous vehicles represent complex cyber-physical systems vulnerable to sophisticated attacks that could compromise passenger safety and public infrastructure.
Consumer acceptance of autonomous vehicles remains heavily contingent upon demonstrated security capabilities. Market research indicates that cybersecurity concerns rank among the top barriers to autonomous vehicle adoption, with potential buyers expressing significant apprehension about data privacy, system integrity, and protection against malicious attacks. This consumer sentiment directly translates into market demand for robust cyber resilience solutions that can provide comprehensive protection across all vehicle systems and communication channels.
The commercial vehicle sector, including logistics, delivery services, and ride-sharing platforms, represents a particularly strong market segment driving demand for secure autonomous systems. Fleet operators require assurance that their autonomous vehicles can maintain operational continuity while protecting valuable cargo and passenger data. The potential for coordinated attacks on multiple vehicles within a fleet amplifies the need for sophisticated cyber resilience tools capable of detecting, preventing, and responding to various threat vectors.
Regulatory frameworks worldwide are increasingly mandating cybersecurity standards for autonomous vehicles, creating additional market pressure for comprehensive security solutions. Government agencies and international standards organizations are developing stringent requirements for cyber resilience capabilities, including real-time threat detection, secure communication protocols, and incident response mechanisms. These regulatory developments are accelerating market demand as manufacturers must demonstrate compliance to achieve market access.
The insurance industry is also influencing market dynamics by requiring enhanced cybersecurity measures as prerequisites for coverage. Insurance providers are developing risk assessment models that heavily weight cybersecurity capabilities when determining premiums and coverage terms for autonomous vehicle deployments. This creates additional economic incentives for investing in advanced cyber resilience tools.
Emerging market segments, including smart city initiatives and connected infrastructure projects, are generating new demand patterns for integrated security solutions. These applications require autonomous vehicles to securely interact with complex urban ecosystems while maintaining protection against both targeted attacks and systemic vulnerabilities that could affect multiple interconnected systems simultaneously.
Consumer acceptance of autonomous vehicles remains heavily contingent upon demonstrated security capabilities. Market research indicates that cybersecurity concerns rank among the top barriers to autonomous vehicle adoption, with potential buyers expressing significant apprehension about data privacy, system integrity, and protection against malicious attacks. This consumer sentiment directly translates into market demand for robust cyber resilience solutions that can provide comprehensive protection across all vehicle systems and communication channels.
The commercial vehicle sector, including logistics, delivery services, and ride-sharing platforms, represents a particularly strong market segment driving demand for secure autonomous systems. Fleet operators require assurance that their autonomous vehicles can maintain operational continuity while protecting valuable cargo and passenger data. The potential for coordinated attacks on multiple vehicles within a fleet amplifies the need for sophisticated cyber resilience tools capable of detecting, preventing, and responding to various threat vectors.
Regulatory frameworks worldwide are increasingly mandating cybersecurity standards for autonomous vehicles, creating additional market pressure for comprehensive security solutions. Government agencies and international standards organizations are developing stringent requirements for cyber resilience capabilities, including real-time threat detection, secure communication protocols, and incident response mechanisms. These regulatory developments are accelerating market demand as manufacturers must demonstrate compliance to achieve market access.
The insurance industry is also influencing market dynamics by requiring enhanced cybersecurity measures as prerequisites for coverage. Insurance providers are developing risk assessment models that heavily weight cybersecurity capabilities when determining premiums and coverage terms for autonomous vehicle deployments. This creates additional economic incentives for investing in advanced cyber resilience tools.
Emerging market segments, including smart city initiatives and connected infrastructure projects, are generating new demand patterns for integrated security solutions. These applications require autonomous vehicles to securely interact with complex urban ecosystems while maintaining protection against both targeted attacks and systemic vulnerabilities that could affect multiple interconnected systems simultaneously.
Current Cybersecurity Challenges in Autonomous Vehicles
Autonomous vehicles face unprecedented cybersecurity challenges due to their complex interconnected systems and reliance on real-time data processing. The attack surface of modern autonomous vehicles encompasses multiple entry points, including vehicle-to-everything (V2X) communications, over-the-air (OTA) update mechanisms, sensor networks, and cloud connectivity interfaces. Each of these components presents unique vulnerabilities that malicious actors can exploit to compromise vehicle safety and passenger security.
The distributed nature of autonomous vehicle architectures creates significant security complexities. Modern self-driving cars integrate numerous electronic control units (ECUs), advanced driver assistance systems (ADAS), and artificial intelligence processing units that communicate through various protocols including CAN bus, Ethernet, and wireless networks. This interconnectedness means that a breach in one component can potentially cascade throughout the entire system, affecting critical safety functions.
Real-time processing requirements impose additional constraints on cybersecurity implementations. Traditional security measures often introduce latency that can be incompatible with the millisecond response times required for autonomous driving decisions. This creates a fundamental tension between security robustness and operational performance, forcing engineers to balance comprehensive protection with system responsiveness.
External connectivity vulnerabilities represent another critical challenge area. Autonomous vehicles must maintain constant communication with infrastructure systems, other vehicles, and cloud-based services to function effectively. These communication channels create potential attack vectors for remote exploitation, including man-in-the-middle attacks, data interception, and unauthorized system access attempts.
The complexity of software supply chains in autonomous vehicles introduces additional risk factors. Modern autonomous systems integrate software components from multiple vendors, open-source libraries, and third-party service providers. Each component may contain undiscovered vulnerabilities or backdoors that could be exploited by sophisticated attackers seeking to compromise vehicle operations.
Data privacy and integrity concerns compound the cybersecurity challenge landscape. Autonomous vehicles collect vast amounts of sensitive information including location data, passenger behavior patterns, and environmental observations. Protecting this data from unauthorized access while ensuring its integrity for safety-critical decision-making processes requires sophisticated encryption and validation mechanisms that must operate within strict performance constraints.
The distributed nature of autonomous vehicle architectures creates significant security complexities. Modern self-driving cars integrate numerous electronic control units (ECUs), advanced driver assistance systems (ADAS), and artificial intelligence processing units that communicate through various protocols including CAN bus, Ethernet, and wireless networks. This interconnectedness means that a breach in one component can potentially cascade throughout the entire system, affecting critical safety functions.
Real-time processing requirements impose additional constraints on cybersecurity implementations. Traditional security measures often introduce latency that can be incompatible with the millisecond response times required for autonomous driving decisions. This creates a fundamental tension between security robustness and operational performance, forcing engineers to balance comprehensive protection with system responsiveness.
External connectivity vulnerabilities represent another critical challenge area. Autonomous vehicles must maintain constant communication with infrastructure systems, other vehicles, and cloud-based services to function effectively. These communication channels create potential attack vectors for remote exploitation, including man-in-the-middle attacks, data interception, and unauthorized system access attempts.
The complexity of software supply chains in autonomous vehicles introduces additional risk factors. Modern autonomous systems integrate software components from multiple vendors, open-source libraries, and third-party service providers. Each component may contain undiscovered vulnerabilities or backdoors that could be exploited by sophisticated attackers seeking to compromise vehicle operations.
Data privacy and integrity concerns compound the cybersecurity challenge landscape. Autonomous vehicles collect vast amounts of sensitive information including location data, passenger behavior patterns, and environmental observations. Protecting this data from unauthorized access while ensuring its integrity for safety-critical decision-making processes requires sophisticated encryption and validation mechanisms that must operate within strict performance constraints.
Existing Cyber Resilience Solutions for AVs
01 Automated threat detection and response systems
Cyber resilience tools incorporate automated systems that continuously monitor network traffic and system behavior to detect anomalies and potential security threats in real-time. These systems utilize machine learning algorithms and artificial intelligence to identify patterns indicative of cyber attacks, enabling rapid response and mitigation. The automation reduces response time and minimizes human error in threat detection, enhancing overall system resilience against various cyber threats including malware, ransomware, and unauthorized access attempts.- Automated threat detection and response systems: Cyber resilience tools incorporate automated systems that continuously monitor network traffic and system behavior to detect anomalies and potential security threats in real-time. These systems utilize machine learning algorithms and artificial intelligence to identify patterns indicative of cyber attacks, enabling rapid response and mitigation. The automation reduces response time and minimizes human error in threat detection, enhancing overall system resilience against various cyber threats including malware, ransomware, and unauthorized access attempts.
- Data backup and recovery mechanisms: Resilience tools implement comprehensive data backup and recovery solutions that ensure business continuity during and after cyber incidents. These mechanisms include redundant storage systems, incremental backup protocols, and rapid restoration capabilities. The systems are designed to maintain data integrity and availability even when primary systems are compromised, allowing organizations to quickly recover from ransomware attacks, data corruption, or system failures with minimal downtime and data loss.
- Security assessment and vulnerability management: Tools for cyber resilience include frameworks for continuous security assessment and vulnerability management that identify weaknesses in systems before they can be exploited. These solutions perform regular security audits, penetration testing simulations, and compliance checks to evaluate the security posture of an organization. The assessment results guide remediation efforts and help prioritize security investments based on risk levels, ensuring that critical vulnerabilities are addressed promptly.
- Identity and access management controls: Cyber resilience is enhanced through robust identity and access management systems that control and monitor user permissions and authentication processes. These tools implement multi-factor authentication, role-based access controls, and privileged access management to prevent unauthorized access to critical systems and data. The solutions maintain detailed audit trails of access activities and can automatically revoke or adjust permissions based on user behavior patterns or detected anomalies, reducing the risk of insider threats and credential compromise.
- Incident response orchestration and coordination: Advanced cyber resilience tools provide orchestration platforms that coordinate incident response activities across multiple security systems and teams. These platforms automate workflow processes, facilitate communication between stakeholders, and integrate with various security tools to provide a unified response capability. The orchestration ensures that incident response procedures are executed consistently and efficiently, reducing the time to contain and remediate security incidents while maintaining comprehensive documentation for post-incident analysis and compliance requirements.
02 Data backup and recovery mechanisms
Resilience tools implement comprehensive data backup and recovery solutions that ensure business continuity during and after cyber incidents. These mechanisms include redundant storage systems, incremental backup protocols, and rapid restoration capabilities. The systems are designed to maintain data integrity and availability even when primary systems are compromised, allowing organizations to quickly recover from ransomware attacks, data corruption, or system failures with minimal downtime and data loss.Expand Specific Solutions03 Security assessment and vulnerability management
Cyber resilience platforms provide tools for continuous security assessment and vulnerability scanning across network infrastructure and applications. These tools identify weaknesses in system configurations, outdated software components, and potential entry points for attackers. The assessment capabilities include penetration testing simulations, compliance checking, and risk scoring mechanisms that help organizations prioritize remediation efforts and strengthen their security posture proactively.Expand Specific Solutions04 Incident response orchestration and coordination
Advanced resilience tools feature orchestration capabilities that coordinate multiple security systems and response teams during cyber incidents. These platforms automate workflow processes, facilitate communication between stakeholders, and provide centralized dashboards for incident management. The orchestration functionality ensures that response actions are executed in proper sequence, resources are allocated efficiently, and all relevant parties are informed throughout the incident lifecycle, reducing overall impact and recovery time.Expand Specific Solutions05 Resilience testing and simulation frameworks
Cyber resilience tools include frameworks for testing and simulating various attack scenarios to evaluate organizational preparedness and system robustness. These frameworks enable controlled testing of disaster recovery plans, incident response procedures, and system failover mechanisms without disrupting production environments. The simulation capabilities help identify gaps in resilience strategies, validate recovery time objectives, and train personnel in handling cyber incidents effectively.Expand Specific Solutions
Key Players in Autonomous Vehicle Security Industry
The autonomous vehicle cyber resilience market is experiencing rapid evolution as the industry transitions from early development to commercial deployment phases. With the global autonomous vehicle market projected to reach significant scale by 2030, cybersecurity has emerged as a critical enabler for widespread adoption. The competitive landscape spans traditional automotive suppliers like DENSO Corp., Robert Bosch GmbH, and Continental Teves AG, technology giants including LG Electronics and Panasonic Automotive Systems, pure-play autonomous vehicle companies such as Aurora Operations and Motional AD LLC, and cybersecurity specialists like Darktrace Ltd. Technology maturity varies significantly across players, with established automotive suppliers leveraging decades of safety-critical systems experience, while newer entrants like May Mobility focus on integrated autonomous solutions with built-in security frameworks, creating a dynamic ecosystem where collaboration and competition coexist.
DENSO Corp.
Technical Solution: DENSO has developed advanced cybersecurity solutions tailored for autonomous vehicle architectures, focusing on secure ECU design and network protection. Their approach includes implementing secure gateways that monitor and filter communications between different vehicle domains, preventing lateral movement of potential threats. The company's cybersecurity framework incorporates machine learning algorithms to detect anomalous patterns in vehicle sensor data and communication protocols. DENSO's solution features hardware-based security anchors in critical control units, providing tamper-resistant protection for autonomous driving functions. Their platform includes secure key management systems for vehicle-to-everything (V2X) communications and supports real-time threat intelligence updates. The technology integrates with existing automotive safety systems to ensure that cybersecurity measures do not compromise functional safety requirements.
Strengths: Strong automotive supplier relationships, integrated safety-security approach, proven manufacturing scalability. Weaknesses: Limited experience with advanced AI-based threat detection compared to pure cybersecurity companies.
Darktrace Ltd.
Technical Solution: Darktrace develops AI-powered cyber defense solutions specifically designed for autonomous vehicle ecosystems. Their Enterprise Immune System technology uses unsupervised machine learning to detect anomalous behavior in real-time across vehicle networks, including CAN bus communications, V2X protocols, and cloud connectivity interfaces. The platform creates a dynamic baseline of normal vehicle behavior and identifies deviations that could indicate cyber attacks, malware infiltration, or system compromises. Their Antigena technology provides autonomous response capabilities that can isolate compromised vehicle systems while maintaining critical safety functions. The solution integrates with existing automotive cybersecurity frameworks and provides continuous monitoring of both in-vehicle networks and external communication channels.
Strengths: Industry-leading AI detection capabilities, real-time threat response, proven enterprise security track record. Weaknesses: High computational requirements, potential for false positives in complex vehicle environments.
Core Innovations in AV Cybersecurity Patents
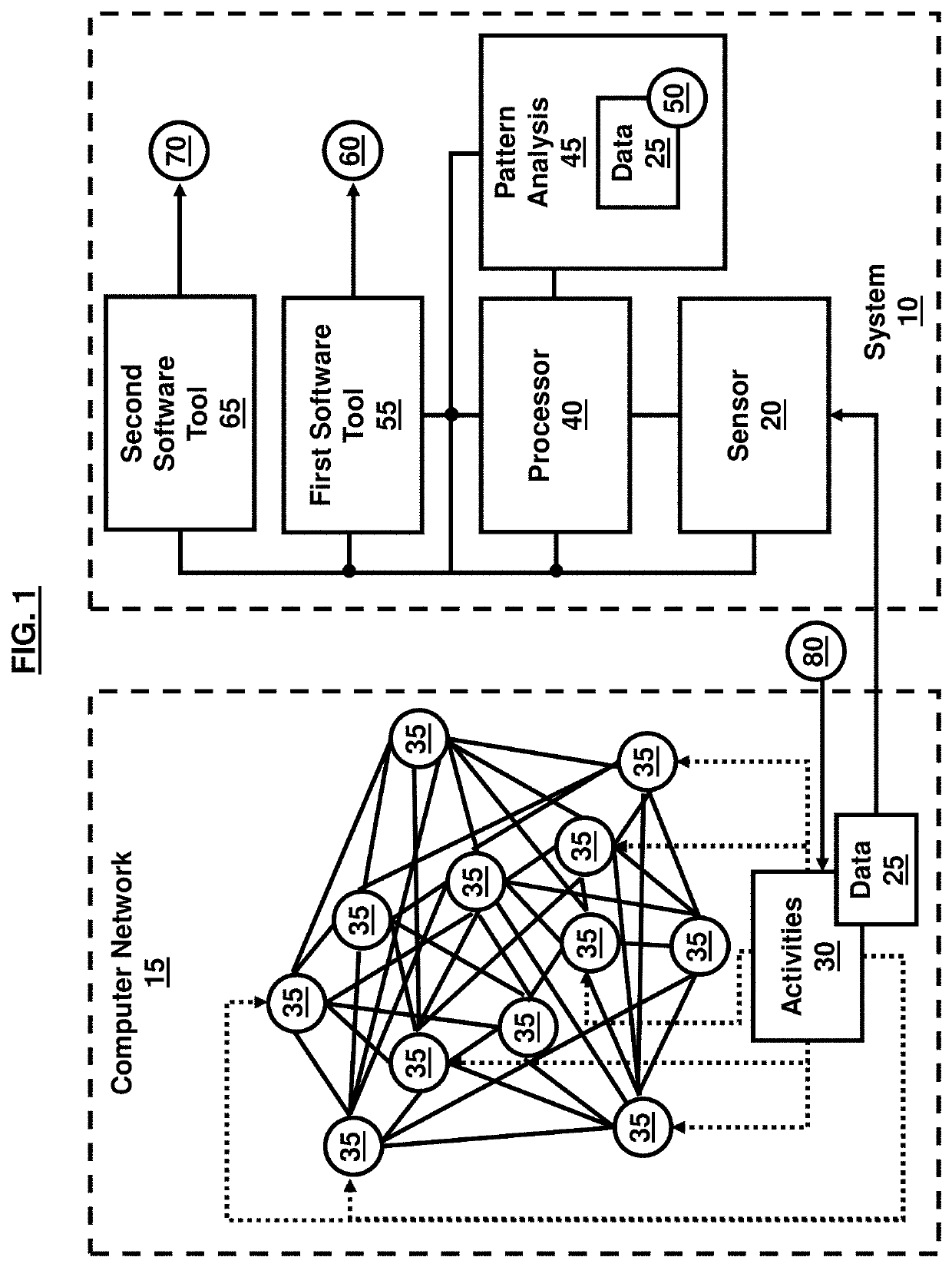
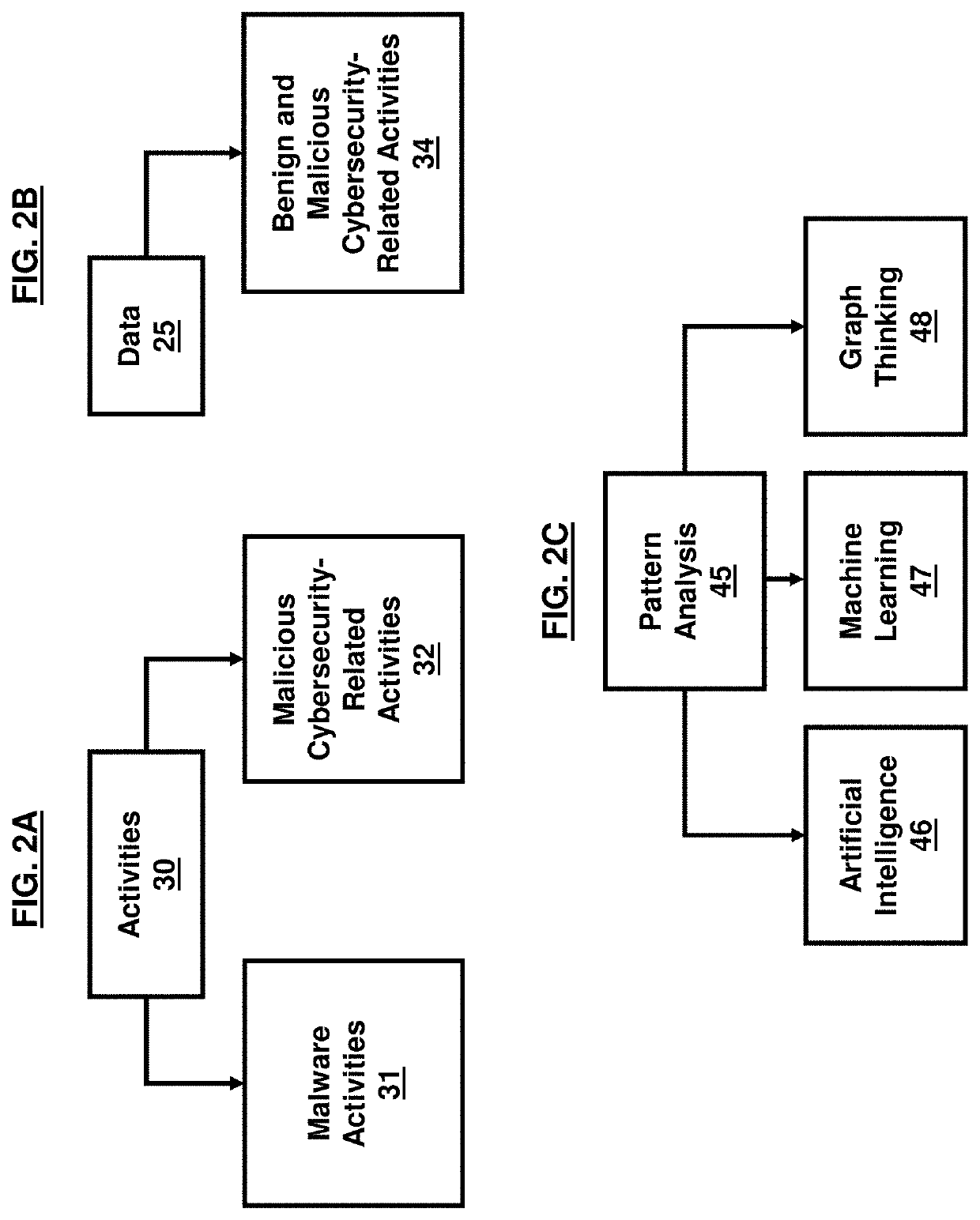
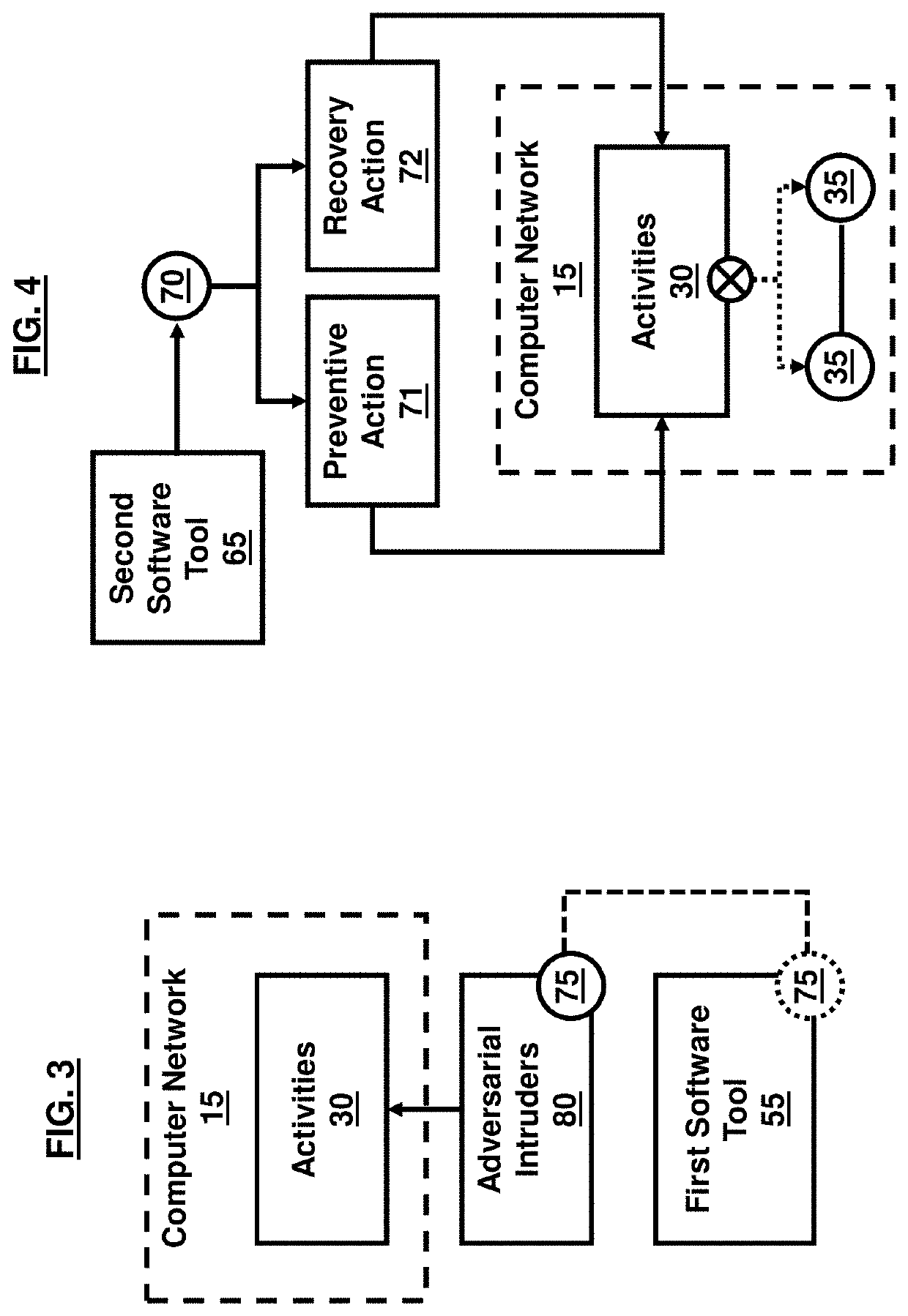
Cybersecurity resilience by integrating adversary and defender actions, deep learning, and graph thinking
PatentActiveUS20210352095A1
Innovation
- A system utilizing sensors to collect data on adversarial activities, a processor for pattern analysis, and machine learning techniques to predict adversary actions and intentions, as well as identify mitigation and recovery actions, creating a graphical representation of data paths to identify vulnerable nodes and predict malware infection propagation.
Regulatory Framework for Autonomous Vehicle Security
The regulatory landscape for autonomous vehicle security is rapidly evolving as governments worldwide recognize the critical importance of cybersecurity in ensuring public safety and consumer confidence. Current regulatory frameworks vary significantly across jurisdictions, with the European Union leading through comprehensive legislation such as the UN-ECE WP.29 regulations, which mandate cybersecurity management systems throughout vehicle lifecycles. The United States follows a more fragmented approach, with NHTSA providing voluntary guidance while individual states develop their own autonomous vehicle testing and deployment requirements.
International standardization efforts are gaining momentum through organizations like ISO and SAE International, which have established foundational standards including ISO/SAE 21434 for cybersecurity engineering and ISO 26262 for functional safety. These standards provide essential frameworks for implementing cyber resilience tools, requiring manufacturers to demonstrate robust security measures from design through decommissioning phases.
Regulatory compliance presents unique challenges for cyber resilience optimization, as traditional automotive safety regulations were not designed to address dynamic cybersecurity threats. Current frameworks emphasize risk assessment methodologies, incident response protocols, and continuous monitoring requirements that directly impact how cyber resilience tools must be architected and deployed.
Emerging regulatory trends indicate increasing focus on real-time threat detection capabilities, mandatory security update mechanisms, and cross-border information sharing protocols. The European Cyber Resilience Act and similar initiatives in Asia-Pacific regions are establishing new requirements for vulnerability disclosure, security testing, and supply chain security that will fundamentally reshape how autonomous vehicle manufacturers approach cyber resilience tool integration.
Future regulatory developments are expected to mandate specific performance metrics for cyber resilience systems, including response time requirements for threat mitigation, minimum security update frequencies, and standardized incident reporting formats. These evolving requirements will drive innovation in automated compliance monitoring tools and adaptive security architectures that can dynamically adjust to changing regulatory landscapes while maintaining operational effectiveness.
International standardization efforts are gaining momentum through organizations like ISO and SAE International, which have established foundational standards including ISO/SAE 21434 for cybersecurity engineering and ISO 26262 for functional safety. These standards provide essential frameworks for implementing cyber resilience tools, requiring manufacturers to demonstrate robust security measures from design through decommissioning phases.
Regulatory compliance presents unique challenges for cyber resilience optimization, as traditional automotive safety regulations were not designed to address dynamic cybersecurity threats. Current frameworks emphasize risk assessment methodologies, incident response protocols, and continuous monitoring requirements that directly impact how cyber resilience tools must be architected and deployed.
Emerging regulatory trends indicate increasing focus on real-time threat detection capabilities, mandatory security update mechanisms, and cross-border information sharing protocols. The European Cyber Resilience Act and similar initiatives in Asia-Pacific regions are establishing new requirements for vulnerability disclosure, security testing, and supply chain security that will fundamentally reshape how autonomous vehicle manufacturers approach cyber resilience tool integration.
Future regulatory developments are expected to mandate specific performance metrics for cyber resilience systems, including response time requirements for threat mitigation, minimum security update frequencies, and standardized incident reporting formats. These evolving requirements will drive innovation in automated compliance monitoring tools and adaptive security architectures that can dynamically adjust to changing regulatory landscapes while maintaining operational effectiveness.
Safety-Security Integration in Autonomous Systems
The convergence of safety and security in autonomous vehicle systems represents a fundamental paradigm shift from traditional automotive engineering approaches. Historically, functional safety and cybersecurity have been addressed as separate domains, with safety focusing on preventing random hardware failures and security concentrating on protecting against malicious attacks. However, the interconnected nature of autonomous systems necessitates a holistic integration approach where safety and security mechanisms work synergistically rather than in isolation.
Modern autonomous vehicles operate through complex networks of sensors, processors, and communication systems that create multiple attack vectors while simultaneously requiring ultra-high reliability for safe operation. This dual requirement has led to the development of integrated safety-security frameworks that consider both accidental failures and intentional threats as potential sources of system compromise. The integration approach recognizes that security vulnerabilities can directly impact safety performance, while safety mechanisms can inadvertently create security weaknesses.
The technical foundation for safety-security integration relies on shared risk assessment methodologies that evaluate both probabilistic safety hazards and deterministic security threats within a unified framework. This involves developing common taxonomies for failure modes, establishing cross-domain impact analysis procedures, and creating integrated monitoring systems that can detect both safety-critical deviations and security anomalies. Advanced autonomous systems now implement defense-in-depth strategies that incorporate redundant safety mechanisms with multi-layered security controls.
Emerging integration architectures utilize secure-by-design principles combined with fail-safe operational modes to ensure that security measures do not compromise safety performance under any circumstances. These systems employ real-time threat assessment engines that continuously evaluate the security posture while maintaining safety-critical functions, enabling dynamic adaptation of both safety and security parameters based on current operational conditions and threat landscapes.
The implementation of integrated safety-security frameworks requires sophisticated coordination mechanisms that can manage trade-offs between security overhead and safety response times. This includes developing optimized cryptographic protocols for safety-critical communications, implementing secure update mechanisms for safety-related software components, and establishing trusted execution environments that can maintain both safety integrity levels and security assurance requirements simultaneously.
Modern autonomous vehicles operate through complex networks of sensors, processors, and communication systems that create multiple attack vectors while simultaneously requiring ultra-high reliability for safe operation. This dual requirement has led to the development of integrated safety-security frameworks that consider both accidental failures and intentional threats as potential sources of system compromise. The integration approach recognizes that security vulnerabilities can directly impact safety performance, while safety mechanisms can inadvertently create security weaknesses.
The technical foundation for safety-security integration relies on shared risk assessment methodologies that evaluate both probabilistic safety hazards and deterministic security threats within a unified framework. This involves developing common taxonomies for failure modes, establishing cross-domain impact analysis procedures, and creating integrated monitoring systems that can detect both safety-critical deviations and security anomalies. Advanced autonomous systems now implement defense-in-depth strategies that incorporate redundant safety mechanisms with multi-layered security controls.
Emerging integration architectures utilize secure-by-design principles combined with fail-safe operational modes to ensure that security measures do not compromise safety performance under any circumstances. These systems employ real-time threat assessment engines that continuously evaluate the security posture while maintaining safety-critical functions, enabling dynamic adaptation of both safety and security parameters based on current operational conditions and threat landscapes.
The implementation of integrated safety-security frameworks requires sophisticated coordination mechanisms that can manage trade-offs between security overhead and safety response times. This includes developing optimized cryptographic protocols for safety-critical communications, implementing secure update mechanisms for safety-related software components, and establishing trusted execution environments that can maintain both safety integrity levels and security assurance requirements simultaneously.
Unlock deeper insights with Patsnap Eureka Quick Research — get a full tech report to explore trends and direct your research. Try now!
Generate Your Research Report Instantly with AI Agent
Supercharge your innovation with Patsnap Eureka AI Agent Platform!