Strengthen Autonomous System Defense with AI-Driven Analytics
MAR 5, 20269 MIN READ
Generate Your Research Report Instantly with AI Agent
Patsnap Eureka helps you evaluate technical feasibility & market potential.
AI-Driven Autonomous Defense Background and Objectives
The evolution of cybersecurity has reached a critical juncture where traditional defensive mechanisms are increasingly inadequate against sophisticated, rapidly evolving threats. Autonomous systems, spanning from industrial control networks to smart city infrastructures, face unprecedented challenges from advanced persistent threats, zero-day exploits, and AI-powered attacks. The exponential growth in connected devices and the complexity of modern cyber-physical systems have created an attack surface that exceeds human capacity for comprehensive monitoring and response.
Historical cybersecurity approaches relied heavily on signature-based detection, perimeter defenses, and reactive incident response protocols. However, the emergence of polymorphic malware, living-off-the-land techniques, and nation-state actors employing machine learning for offensive operations has fundamentally shifted the threat landscape. The average dwell time of advanced threats in enterprise networks continues to extend, often remaining undetected for months while exfiltrating sensitive data or establishing persistent footholds.
The integration of artificial intelligence and machine learning into cybersecurity represents a paradigm shift toward proactive, adaptive defense mechanisms. AI-driven analytics enable real-time behavioral analysis, anomaly detection at scale, and predictive threat modeling that can anticipate attack vectors before they materialize. This technological convergence addresses the fundamental asymmetry between attackers and defenders by providing automated threat hunting, intelligent response orchestration, and continuous learning capabilities.
The primary objective of strengthening autonomous system defense through AI-driven analytics encompasses multiple dimensions. First, achieving real-time threat detection and classification across heterogeneous network environments while minimizing false positive rates that plague traditional security tools. Second, developing adaptive defense mechanisms that can autonomously reconfigure security postures based on emerging threat intelligence and environmental changes.
Furthermore, the initiative aims to establish predictive security capabilities that leverage machine learning models to forecast potential attack scenarios and preemptively strengthen vulnerable system components. The integration of natural language processing for threat intelligence analysis and computer vision for network traffic pattern recognition represents additional technological objectives.
Ultimately, the goal extends beyond mere threat detection to encompass comprehensive security orchestration, where AI systems can coordinate multi-layered defensive responses, manage security tool integration, and provide actionable intelligence for strategic security planning while maintaining operational continuity in critical autonomous systems.
Historical cybersecurity approaches relied heavily on signature-based detection, perimeter defenses, and reactive incident response protocols. However, the emergence of polymorphic malware, living-off-the-land techniques, and nation-state actors employing machine learning for offensive operations has fundamentally shifted the threat landscape. The average dwell time of advanced threats in enterprise networks continues to extend, often remaining undetected for months while exfiltrating sensitive data or establishing persistent footholds.
The integration of artificial intelligence and machine learning into cybersecurity represents a paradigm shift toward proactive, adaptive defense mechanisms. AI-driven analytics enable real-time behavioral analysis, anomaly detection at scale, and predictive threat modeling that can anticipate attack vectors before they materialize. This technological convergence addresses the fundamental asymmetry between attackers and defenders by providing automated threat hunting, intelligent response orchestration, and continuous learning capabilities.
The primary objective of strengthening autonomous system defense through AI-driven analytics encompasses multiple dimensions. First, achieving real-time threat detection and classification across heterogeneous network environments while minimizing false positive rates that plague traditional security tools. Second, developing adaptive defense mechanisms that can autonomously reconfigure security postures based on emerging threat intelligence and environmental changes.
Furthermore, the initiative aims to establish predictive security capabilities that leverage machine learning models to forecast potential attack scenarios and preemptively strengthen vulnerable system components. The integration of natural language processing for threat intelligence analysis and computer vision for network traffic pattern recognition represents additional technological objectives.
Ultimately, the goal extends beyond mere threat detection to encompass comprehensive security orchestration, where AI systems can coordinate multi-layered defensive responses, manage security tool integration, and provide actionable intelligence for strategic security planning while maintaining operational continuity in critical autonomous systems.
Market Demand for AI-Enhanced Cybersecurity Solutions
The global cybersecurity market is experiencing unprecedented growth driven by escalating cyber threats and the increasing sophistication of attack vectors targeting autonomous systems. Organizations across industries are recognizing that traditional security approaches are insufficient to protect against advanced persistent threats, zero-day exploits, and AI-powered attacks that can adapt and evolve in real-time.
Enterprise demand for AI-enhanced cybersecurity solutions has surged as organizations seek proactive defense mechanisms capable of detecting anomalies and responding to threats at machine speed. The shift from reactive to predictive security models has become a strategic imperative, particularly for critical infrastructure operators, financial institutions, and technology companies managing autonomous systems.
The autonomous vehicle industry represents a significant market driver, with manufacturers requiring robust cybersecurity frameworks to protect vehicle-to-everything communication systems, over-the-air update mechanisms, and safety-critical control systems. Similar demand patterns emerge in industrial automation, where smart manufacturing facilities need protection for interconnected operational technology networks and autonomous production systems.
Cloud service providers and data center operators are increasingly investing in AI-driven security analytics to protect their infrastructure and customer workloads. The complexity of modern cloud environments, combined with the dynamic nature of containerized applications and microservices architectures, creates substantial demand for intelligent security solutions that can adapt to rapidly changing threat landscapes.
Financial services organizations face regulatory pressure to implement advanced cybersecurity measures, driving adoption of AI-enhanced solutions for fraud detection, transaction monitoring, and network security. The integration of artificial intelligence into financial systems has created new attack surfaces that require sophisticated defense mechanisms.
Healthcare organizations managing connected medical devices and patient data systems represent another growing market segment. The proliferation of Internet of Medical Things devices and telemedicine platforms has expanded the attack surface, creating urgent demand for AI-powered security solutions capable of protecting patient safety and privacy.
Government agencies and defense contractors require advanced cybersecurity capabilities to protect national security systems and classified information. The increasing use of autonomous systems in military applications has created specialized demand for AI-driven security analytics capable of operating in contested environments.
Enterprise demand for AI-enhanced cybersecurity solutions has surged as organizations seek proactive defense mechanisms capable of detecting anomalies and responding to threats at machine speed. The shift from reactive to predictive security models has become a strategic imperative, particularly for critical infrastructure operators, financial institutions, and technology companies managing autonomous systems.
The autonomous vehicle industry represents a significant market driver, with manufacturers requiring robust cybersecurity frameworks to protect vehicle-to-everything communication systems, over-the-air update mechanisms, and safety-critical control systems. Similar demand patterns emerge in industrial automation, where smart manufacturing facilities need protection for interconnected operational technology networks and autonomous production systems.
Cloud service providers and data center operators are increasingly investing in AI-driven security analytics to protect their infrastructure and customer workloads. The complexity of modern cloud environments, combined with the dynamic nature of containerized applications and microservices architectures, creates substantial demand for intelligent security solutions that can adapt to rapidly changing threat landscapes.
Financial services organizations face regulatory pressure to implement advanced cybersecurity measures, driving adoption of AI-enhanced solutions for fraud detection, transaction monitoring, and network security. The integration of artificial intelligence into financial systems has created new attack surfaces that require sophisticated defense mechanisms.
Healthcare organizations managing connected medical devices and patient data systems represent another growing market segment. The proliferation of Internet of Medical Things devices and telemedicine platforms has expanded the attack surface, creating urgent demand for AI-powered security solutions capable of protecting patient safety and privacy.
Government agencies and defense contractors require advanced cybersecurity capabilities to protect national security systems and classified information. The increasing use of autonomous systems in military applications has created specialized demand for AI-driven security analytics capable of operating in contested environments.
Current State of Autonomous Defense System Challenges
Autonomous defense systems currently face significant cybersecurity vulnerabilities that expose critical infrastructure to sophisticated threat actors. Traditional signature-based detection methods prove inadequate against advanced persistent threats (APTs) and zero-day exploits that specifically target industrial control systems, autonomous vehicles, and unmanned aerial systems. The increasing complexity of these systems creates expanded attack surfaces that conventional security frameworks struggle to monitor effectively.
The integration of legacy systems with modern autonomous technologies presents substantial compatibility challenges. Many autonomous systems operate on hybrid architectures that combine decades-old industrial protocols with cutting-edge AI algorithms, creating security gaps at integration points. These legacy components often lack built-in security features and cannot be easily updated, making them persistent weak links in the overall defense posture.
Real-time threat detection and response capabilities remain severely limited in current autonomous defense implementations. Most existing systems rely on periodic security scans and manual threat analysis, which introduce dangerous delays in threat identification and mitigation. The time-sensitive nature of autonomous operations demands instantaneous security responses that current technologies cannot consistently deliver.
Scalability represents another critical challenge as autonomous systems proliferate across industries. Current defense mechanisms struggle to maintain consistent security coverage across distributed autonomous networks, particularly in scenarios involving thousands of interconnected devices. The computational overhead of traditional security monitoring becomes prohibitive when applied to large-scale autonomous deployments.
The shortage of specialized cybersecurity expertise for autonomous systems compounds these technical challenges. Security professionals often lack deep understanding of autonomous system architectures, while autonomous system engineers frequently have limited cybersecurity knowledge. This skills gap results in inadequate security implementations and delayed incident response capabilities.
Regulatory compliance adds another layer of complexity, as existing cybersecurity frameworks were not designed for autonomous systems. Current standards fail to address the unique security requirements of self-operating systems, creating uncertainty about compliance obligations and acceptable risk levels. The lack of standardized security metrics for autonomous systems makes it difficult to establish baseline security requirements and measure improvement over time.
The integration of legacy systems with modern autonomous technologies presents substantial compatibility challenges. Many autonomous systems operate on hybrid architectures that combine decades-old industrial protocols with cutting-edge AI algorithms, creating security gaps at integration points. These legacy components often lack built-in security features and cannot be easily updated, making them persistent weak links in the overall defense posture.
Real-time threat detection and response capabilities remain severely limited in current autonomous defense implementations. Most existing systems rely on periodic security scans and manual threat analysis, which introduce dangerous delays in threat identification and mitigation. The time-sensitive nature of autonomous operations demands instantaneous security responses that current technologies cannot consistently deliver.
Scalability represents another critical challenge as autonomous systems proliferate across industries. Current defense mechanisms struggle to maintain consistent security coverage across distributed autonomous networks, particularly in scenarios involving thousands of interconnected devices. The computational overhead of traditional security monitoring becomes prohibitive when applied to large-scale autonomous deployments.
The shortage of specialized cybersecurity expertise for autonomous systems compounds these technical challenges. Security professionals often lack deep understanding of autonomous system architectures, while autonomous system engineers frequently have limited cybersecurity knowledge. This skills gap results in inadequate security implementations and delayed incident response capabilities.
Regulatory compliance adds another layer of complexity, as existing cybersecurity frameworks were not designed for autonomous systems. Current standards fail to address the unique security requirements of self-operating systems, creating uncertainty about compliance obligations and acceptable risk levels. The lack of standardized security metrics for autonomous systems makes it difficult to establish baseline security requirements and measure improvement over time.
Existing AI-Driven Autonomous Defense Solutions
01 AI-powered threat detection and anomaly identification
Advanced artificial intelligence algorithms are employed to detect and identify anomalous patterns in network traffic and system behavior. Machine learning models are trained to recognize deviations from normal operational baselines, enabling early detection of potential security threats. These systems continuously analyze data streams to identify suspicious activities and potential attack vectors in real-time.- AI-powered threat detection and anomaly identification: Advanced artificial intelligence algorithms are employed to detect and identify anomalous patterns in network traffic, user behavior, and system activities. Machine learning models are trained to recognize deviations from normal operational baselines, enabling early detection of potential security threats. These systems continuously analyze data streams to identify suspicious activities and potential vulnerabilities in real-time, providing proactive defense mechanisms against cyber attacks.
- Automated security response and incident management: Intelligent systems are designed to automatically respond to detected security incidents by implementing predefined countermeasures and mitigation strategies. These solutions integrate automated workflows that can isolate compromised systems, block malicious traffic, and initiate remediation procedures without human intervention. The automation reduces response time and minimizes the impact of security breaches through rapid containment and recovery actions.
- Predictive analytics for vulnerability assessment: Predictive modeling techniques are utilized to forecast potential security vulnerabilities and attack vectors before they can be exploited. These systems analyze historical data, threat intelligence feeds, and system configurations to identify weaknesses and predict future attack scenarios. Risk scoring mechanisms prioritize vulnerabilities based on likelihood and potential impact, enabling organizations to allocate resources effectively for preventive measures.
- Behavioral analytics and user activity monitoring: Sophisticated monitoring systems track and analyze user behaviors, access patterns, and interaction sequences to establish behavioral baselines and detect insider threats. These solutions employ statistical analysis and pattern recognition to identify unusual activities that may indicate compromised credentials, privilege abuse, or malicious intent. Continuous monitoring enables the detection of subtle deviations that traditional security measures might miss.
- Integrated threat intelligence and data correlation: Comprehensive platforms aggregate and correlate data from multiple sources including network logs, endpoint sensors, and external threat intelligence feeds to provide holistic security visibility. Advanced analytics engines process vast amounts of security data to identify relationships between seemingly unrelated events and construct complete attack narratives. This integrated approach enables security teams to understand the full scope of threats and make informed decisions based on contextualized intelligence.
02 Automated security response and mitigation systems
Intelligent automation frameworks are implemented to provide rapid response to detected security incidents. These systems can automatically execute predefined countermeasures and mitigation strategies when threats are identified. The automated response mechanisms reduce response time and minimize human intervention requirements during critical security events.Expand Specific Solutions03 Behavioral analytics and user activity monitoring
Comprehensive monitoring solutions track and analyze user behavior patterns across systems and applications. Advanced analytics engines establish baseline behavioral profiles and detect deviations that may indicate compromised accounts or insider threats. These systems employ sophisticated algorithms to correlate user activities with potential security risks.Expand Specific Solutions04 Predictive security intelligence and risk assessment
Predictive analytics capabilities leverage historical data and threat intelligence to forecast potential security vulnerabilities and attack scenarios. Risk assessment frameworks evaluate system configurations and identify weaknesses before they can be exploited. These proactive approaches enable organizations to strengthen defenses based on anticipated threat landscapes.Expand Specific Solutions05 Integrated defense orchestration and incident management
Unified platforms coordinate multiple security tools and technologies to provide comprehensive defense coverage. Incident management systems integrate data from various sources to provide holistic visibility into security events. These orchestration solutions enable coordinated response across different security layers and facilitate efficient incident resolution workflows.Expand Specific Solutions
Key Players in AI Cybersecurity and Defense Industry
The AI-driven autonomous system defense market is experiencing rapid growth, transitioning from early adoption to mainstream deployment across critical infrastructure sectors. The market demonstrates substantial expansion potential, driven by escalating cyber threats and increasing digitalization of industrial systems. Technology maturity varies significantly among market participants, with established cybersecurity leaders like Darktrace Ltd. and IBM offering sophisticated AI-powered threat detection platforms, while specialized firms such as Deep Sentinel Corp. focus on specific applications like property security using deep learning. Infrastructure operators including State Grid Corp. of China and Guangdong Power Grid Co., Ltd. represent major end-users implementing these technologies to protect critical energy systems. The competitive landscape spans from mature enterprise solutions providers like Salesforce and Harman International to emerging specialized vendors, indicating a market in transition toward standardized AI-driven defense capabilities across autonomous systems.
Deep Sentinel Corp.
Technical Solution: Deep Sentinel combines AI-powered video analytics with human intelligence to create autonomous security systems for physical infrastructure protection. Their platform uses deep learning algorithms for real-time threat detection through computer vision and behavioral analysis, automatically identifying suspicious activities and potential security breaches. The system integrates machine learning models trained on extensive security datasets to distinguish between normal and anomalous behaviors in autonomous environments. Their solution provides automated alert generation and response coordination, strengthening perimeter defense and access control for critical autonomous systems through intelligent surveillance and predictive threat assessment capabilities.
Strengths: Innovative combination of AI automation with human oversight for enhanced accuracy. Weaknesses: Limited to physical security applications and requires extensive camera infrastructure deployment.
Darktrace Ltd.
Technical Solution: Darktrace employs Enterprise Immune System technology that uses unsupervised machine learning to detect and respond to cyber threats in real-time across autonomous systems. Their AI-driven platform creates a dynamic understanding of normal behavior patterns within network infrastructure and automatically identifies deviations that could indicate security breaches. The system provides autonomous response capabilities through Antigena technology, which can take precise actions to neutralize threats while maintaining business continuity. Their solution integrates behavioral analytics with threat intelligence to strengthen defense mechanisms against advanced persistent threats and zero-day attacks in autonomous environments.
Strengths: Industry-leading behavioral analytics and real-time autonomous response capabilities. Weaknesses: High implementation costs and potential for false positives in complex environments.
Core AI Analytics Innovations for System Defense
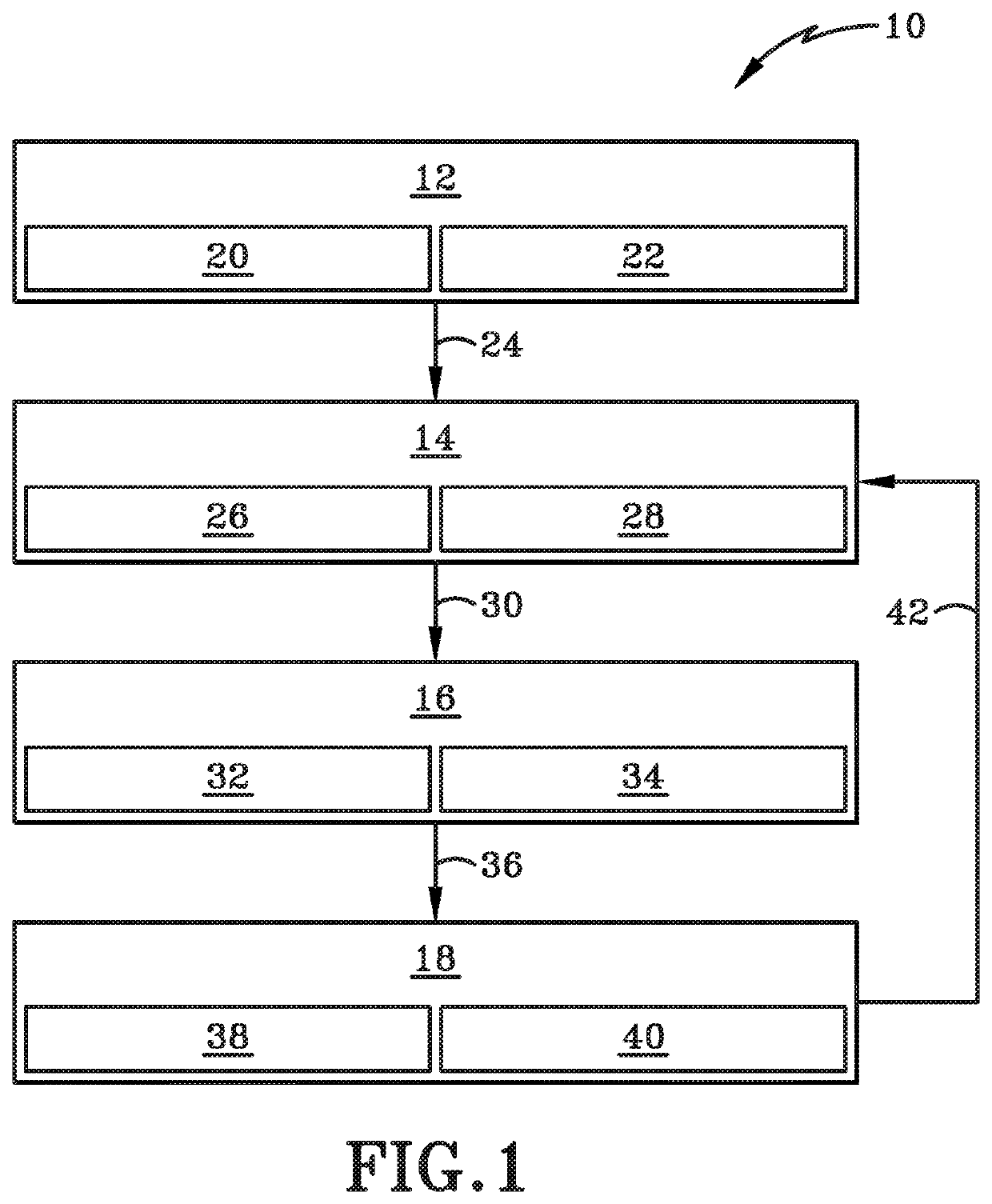
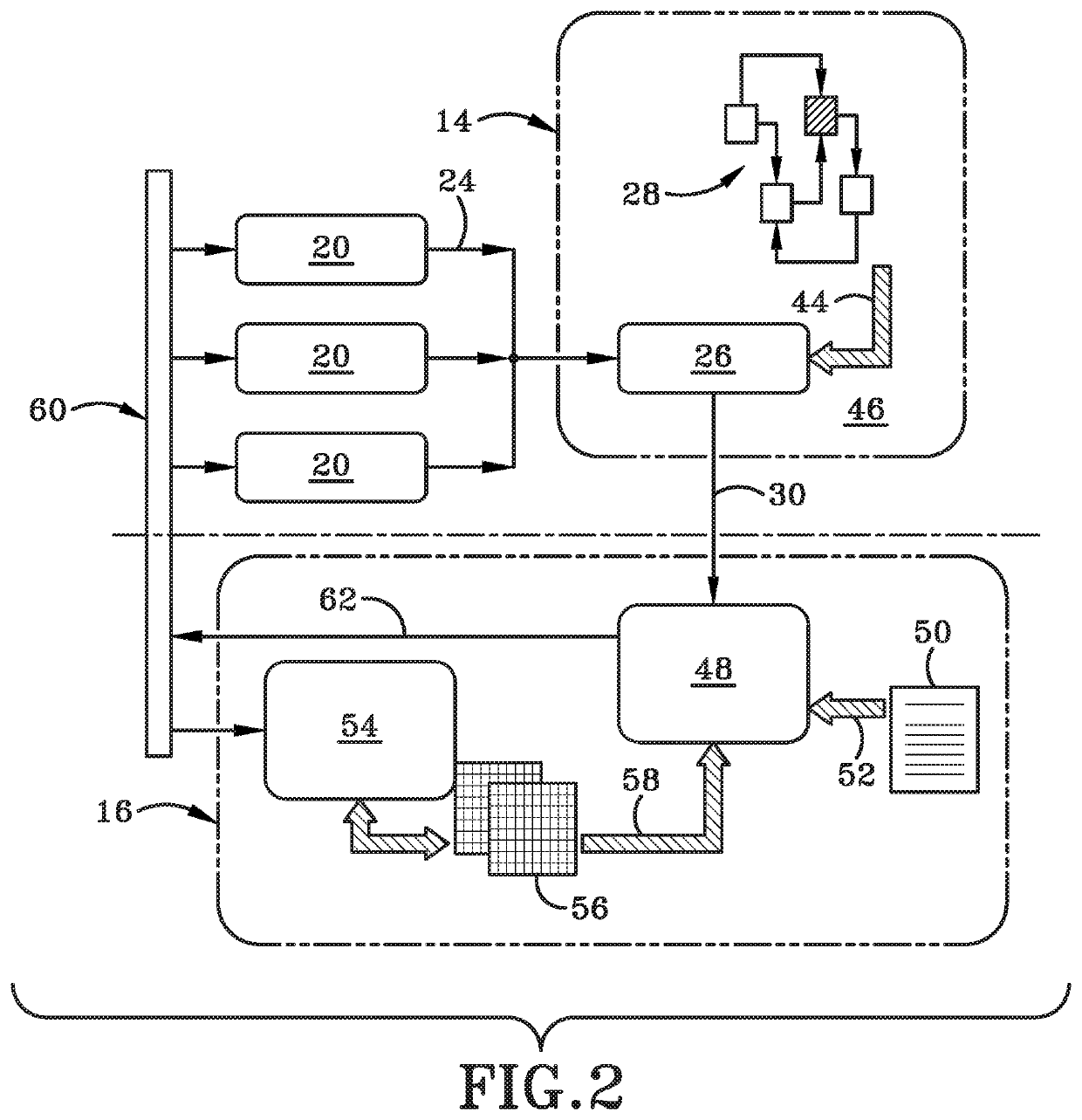
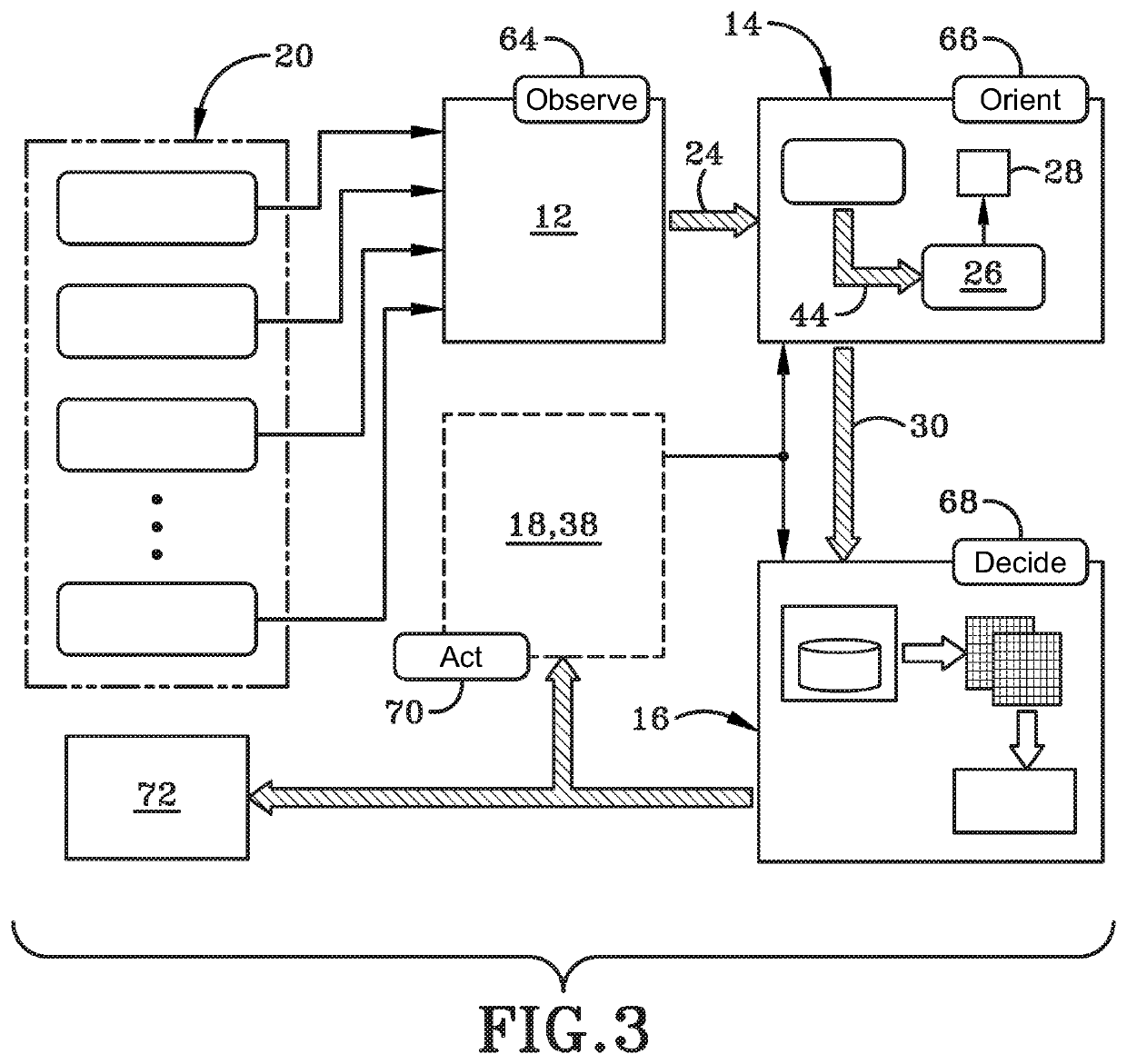
Network defense system and method thereof
PatentInactiveUS20200045069A1
Innovation
- An integrated autonomic network defense system utilizing machine learning and simulation-based risk assessment, which includes a sensor alert ingestion framework, network analyzer, course of action simulator, and training unit to analyze anomalies, generate decision lists with confidence measures, and predict future network impacts, enabling automated and proactive defense strategies.
AI-driven defensive cybersecurity strategy analysis and recommendation system
PatentActiveUS11792229B2
Innovation
- A system and method utilizing machine learning algorithms to simulate attack and defense strategies on a model of the network created using a directed graph, allowing for predictive analysis and cost-benefit-based recommendations for cybersecurity improvements.
Cybersecurity Regulatory Framework for AI Systems
The regulatory landscape for AI-driven cybersecurity systems is rapidly evolving as governments and international organizations recognize the critical need to establish comprehensive frameworks that address both the opportunities and risks associated with autonomous defense technologies. Current regulatory approaches vary significantly across jurisdictions, with the European Union leading through the AI Act, which establishes risk-based classifications for AI systems used in critical infrastructure protection.
In the United States, the National Institute of Standards and Technology (NIST) has developed the AI Risk Management Framework, specifically addressing AI systems deployed in cybersecurity contexts. This framework emphasizes the importance of explainability, accountability, and human oversight in AI-driven security analytics. The framework requires organizations to maintain detailed documentation of AI decision-making processes, particularly when these systems autonomously respond to perceived threats.
The challenge of regulating AI-powered autonomous defense systems lies in balancing innovation with security and privacy concerns. Regulatory bodies must address issues such as algorithmic transparency, data governance, and the potential for AI systems to make critical security decisions without human intervention. Cross-border data sharing requirements further complicate compliance, as cybersecurity analytics often require real-time threat intelligence from multiple international sources.
Emerging regulatory trends indicate a shift toward mandatory AI system auditing and certification processes. Organizations deploying AI-driven cybersecurity solutions must demonstrate compliance with data protection regulations while ensuring their systems can adapt to evolving threat landscapes. The regulatory framework increasingly emphasizes the need for continuous monitoring and validation of AI model performance in cybersecurity applications.
Future regulatory developments are expected to focus on establishing international standards for AI-powered cybersecurity systems, addressing liability issues when autonomous systems make incorrect threat assessments, and creating mechanisms for rapid regulatory adaptation to emerging AI technologies in the cybersecurity domain.
In the United States, the National Institute of Standards and Technology (NIST) has developed the AI Risk Management Framework, specifically addressing AI systems deployed in cybersecurity contexts. This framework emphasizes the importance of explainability, accountability, and human oversight in AI-driven security analytics. The framework requires organizations to maintain detailed documentation of AI decision-making processes, particularly when these systems autonomously respond to perceived threats.
The challenge of regulating AI-powered autonomous defense systems lies in balancing innovation with security and privacy concerns. Regulatory bodies must address issues such as algorithmic transparency, data governance, and the potential for AI systems to make critical security decisions without human intervention. Cross-border data sharing requirements further complicate compliance, as cybersecurity analytics often require real-time threat intelligence from multiple international sources.
Emerging regulatory trends indicate a shift toward mandatory AI system auditing and certification processes. Organizations deploying AI-driven cybersecurity solutions must demonstrate compliance with data protection regulations while ensuring their systems can adapt to evolving threat landscapes. The regulatory framework increasingly emphasizes the need for continuous monitoring and validation of AI model performance in cybersecurity applications.
Future regulatory developments are expected to focus on establishing international standards for AI-powered cybersecurity systems, addressing liability issues when autonomous systems make incorrect threat assessments, and creating mechanisms for rapid regulatory adaptation to emerging AI technologies in the cybersecurity domain.
Ethical AI Considerations in Autonomous Defense
The integration of AI-driven analytics into autonomous defense systems raises profound ethical considerations that must be carefully addressed to ensure responsible deployment and operation. These considerations span multiple dimensions, from decision-making transparency to accountability frameworks, and require comprehensive evaluation before implementation.
Algorithmic bias represents a critical concern in autonomous defense applications. AI systems trained on historical data may perpetuate existing biases or develop new ones that could lead to discriminatory targeting or threat assessment. This is particularly problematic in defense contexts where biased algorithms might disproportionately flag certain populations or regions as threats based on incomplete or skewed training data. Establishing rigorous bias detection and mitigation protocols becomes essential to prevent systematic discrimination.
The principle of human oversight and meaningful control emerges as another fundamental ethical requirement. While autonomous systems offer speed and efficiency advantages, maintaining human authority over critical defense decisions remains paramount. This involves designing systems with appropriate human-in-the-loop mechanisms, ensuring that humans retain ultimate decision-making authority for actions with significant consequences, and establishing clear protocols for human intervention when necessary.
Transparency and explainability pose significant challenges in AI-driven defense analytics. Military personnel and decision-makers must understand how AI systems reach their conclusions to make informed judgments about system recommendations. However, the black-box nature of many advanced AI algorithms conflicts with this requirement, necessitating the development of explainable AI techniques specifically tailored for defense applications.
Privacy and data protection considerations become complex in defense contexts where national security interests may conflict with individual privacy rights. AI-driven analytics systems often require extensive data collection and analysis, raising questions about the scope of surveillance, data retention policies, and protection of civilian information. Establishing clear boundaries and oversight mechanisms for data usage becomes crucial.
Accountability frameworks must address the challenge of responsibility attribution when autonomous systems make errors or cause unintended consequences. This includes defining legal and operational responsibility chains, establishing liability frameworks for AI-driven decisions, and creating mechanisms for redress when systems fail or cause harm.
International humanitarian law compliance represents another critical dimension, ensuring that autonomous defense systems operate within established legal frameworks governing armed conflict. This includes adherence to principles of distinction, proportionality, and precaution in attack, which must be programmed into AI systems and continuously validated.
Algorithmic bias represents a critical concern in autonomous defense applications. AI systems trained on historical data may perpetuate existing biases or develop new ones that could lead to discriminatory targeting or threat assessment. This is particularly problematic in defense contexts where biased algorithms might disproportionately flag certain populations or regions as threats based on incomplete or skewed training data. Establishing rigorous bias detection and mitigation protocols becomes essential to prevent systematic discrimination.
The principle of human oversight and meaningful control emerges as another fundamental ethical requirement. While autonomous systems offer speed and efficiency advantages, maintaining human authority over critical defense decisions remains paramount. This involves designing systems with appropriate human-in-the-loop mechanisms, ensuring that humans retain ultimate decision-making authority for actions with significant consequences, and establishing clear protocols for human intervention when necessary.
Transparency and explainability pose significant challenges in AI-driven defense analytics. Military personnel and decision-makers must understand how AI systems reach their conclusions to make informed judgments about system recommendations. However, the black-box nature of many advanced AI algorithms conflicts with this requirement, necessitating the development of explainable AI techniques specifically tailored for defense applications.
Privacy and data protection considerations become complex in defense contexts where national security interests may conflict with individual privacy rights. AI-driven analytics systems often require extensive data collection and analysis, raising questions about the scope of surveillance, data retention policies, and protection of civilian information. Establishing clear boundaries and oversight mechanisms for data usage becomes crucial.
Accountability frameworks must address the challenge of responsibility attribution when autonomous systems make errors or cause unintended consequences. This includes defining legal and operational responsibility chains, establishing liability frameworks for AI-driven decisions, and creating mechanisms for redress when systems fail or cause harm.
International humanitarian law compliance represents another critical dimension, ensuring that autonomous defense systems operate within established legal frameworks governing armed conflict. This includes adherence to principles of distinction, proportionality, and precaution in attack, which must be programmed into AI systems and continuously validated.
Unlock deeper insights with Patsnap Eureka Quick Research — get a full tech report to explore trends and direct your research. Try now!
Generate Your Research Report Instantly with AI Agent
Supercharge your innovation with Patsnap Eureka AI Agent Platform!