Frequency Shift Keying vs Time Division Multiple Access: Data Integrity
MAR 19, 20269 MIN READ
Generate Your Research Report Instantly with AI Agent
PatSnap Eureka helps you evaluate technical feasibility & market potential.
FSK vs TDMA Data Integrity Background and Objectives
The evolution of digital communication systems has been fundamentally shaped by the need to balance efficient data transmission with robust data integrity mechanisms. As wireless communication networks have expanded exponentially over the past decades, two critical technologies have emerged as cornerstone solutions: Frequency Shift Keying (FSK) modulation and Time Division Multiple Access (TDMA) protocols. These technologies address different layers of the communication stack yet share a common imperative to maintain data reliability in increasingly complex transmission environments.
FSK represents a fundamental digital modulation technique where binary data is encoded through discrete frequency variations of the carrier signal. This approach has demonstrated remarkable resilience in noisy environments, making it particularly valuable for applications requiring high data integrity. The technology's inherent error resistance stems from its ability to maintain signal distinction even under adverse channel conditions, establishing it as a preferred choice for critical communication systems.
TDMA operates at the multiple access layer, enabling multiple users to share the same frequency spectrum through temporal separation. This protocol divides transmission time into discrete slots, allowing systematic data exchange while minimizing interference between concurrent users. The structured nature of TDMA inherently supports data integrity through its organized approach to channel access and collision avoidance.
The intersection of FSK and TDMA technologies creates a compelling framework for examining data integrity challenges in modern communication systems. While FSK addresses signal-level reliability through robust modulation schemes, TDMA ensures system-level integrity through coordinated access protocols. However, the integration of these technologies introduces complex interactions that can either enhance or compromise overall data reliability.
Contemporary communication demands require unprecedented levels of data integrity across diverse application scenarios, from mission-critical industrial automation to high-volume consumer services. The primary objective of this technical investigation is to comprehensively evaluate how FSK and TDMA technologies individually and collectively address data integrity requirements. This analysis aims to identify optimal implementation strategies, quantify performance trade-offs, and establish guidelines for technology selection based on specific integrity requirements and operational constraints.
FSK represents a fundamental digital modulation technique where binary data is encoded through discrete frequency variations of the carrier signal. This approach has demonstrated remarkable resilience in noisy environments, making it particularly valuable for applications requiring high data integrity. The technology's inherent error resistance stems from its ability to maintain signal distinction even under adverse channel conditions, establishing it as a preferred choice for critical communication systems.
TDMA operates at the multiple access layer, enabling multiple users to share the same frequency spectrum through temporal separation. This protocol divides transmission time into discrete slots, allowing systematic data exchange while minimizing interference between concurrent users. The structured nature of TDMA inherently supports data integrity through its organized approach to channel access and collision avoidance.
The intersection of FSK and TDMA technologies creates a compelling framework for examining data integrity challenges in modern communication systems. While FSK addresses signal-level reliability through robust modulation schemes, TDMA ensures system-level integrity through coordinated access protocols. However, the integration of these technologies introduces complex interactions that can either enhance or compromise overall data reliability.
Contemporary communication demands require unprecedented levels of data integrity across diverse application scenarios, from mission-critical industrial automation to high-volume consumer services. The primary objective of this technical investigation is to comprehensively evaluate how FSK and TDMA technologies individually and collectively address data integrity requirements. This analysis aims to identify optimal implementation strategies, quantify performance trade-offs, and establish guidelines for technology selection based on specific integrity requirements and operational constraints.
Market Demand for Reliable Digital Communication Systems
The global digital communication market continues to experience unprecedented growth driven by the proliferation of connected devices, Internet of Things applications, and the increasing demand for real-time data transmission across various industries. Organizations across telecommunications, automotive, aerospace, industrial automation, and consumer electronics sectors require communication systems that can guarantee data integrity while maintaining efficient spectrum utilization and network capacity.
Mission-critical applications in sectors such as autonomous vehicles, medical devices, financial trading systems, and industrial control networks have elevated data integrity requirements beyond traditional performance metrics. These applications cannot tolerate data corruption, packet loss, or transmission errors that could result in system failures, safety hazards, or financial losses. The market increasingly demands communication protocols that can provide deterministic performance guarantees rather than best-effort delivery mechanisms.
The emergence of Industry 4.0 and smart manufacturing has created substantial demand for reliable communication systems that can support real-time control loops, predictive maintenance, and synchronized operations across distributed factory networks. Manufacturing environments require communication solutions that can maintain data integrity despite electromagnetic interference, physical obstacles, and high-density device deployments that characterize modern industrial facilities.
Telecommunications infrastructure providers face mounting pressure to deliver enhanced data reliability while managing spectrum scarcity and increasing user density. The transition toward software-defined networks and network function virtualization has created opportunities for implementing advanced modulation schemes and multiple access techniques that can adapt to varying channel conditions and traffic patterns while preserving data integrity.
Consumer applications including streaming services, online gaming, video conferencing, and cloud computing have established user expectations for seamless, error-free data transmission. Service providers must balance the competing requirements of throughput, latency, and reliability while managing network resources efficiently across diverse user populations and usage patterns.
The growing adoption of edge computing and distributed processing architectures has intensified the need for communication systems that can maintain data consistency across geographically dispersed nodes. These applications require protocols that can detect and correct transmission errors while minimizing retransmission overhead that could impact overall system performance and user experience.
Regulatory frameworks across various industries increasingly mandate specific data integrity standards for communication systems, particularly in healthcare, finance, and transportation sectors. Compliance requirements drive market demand for communication solutions that can provide auditable data transmission records and demonstrate adherence to established reliability standards.
Mission-critical applications in sectors such as autonomous vehicles, medical devices, financial trading systems, and industrial control networks have elevated data integrity requirements beyond traditional performance metrics. These applications cannot tolerate data corruption, packet loss, or transmission errors that could result in system failures, safety hazards, or financial losses. The market increasingly demands communication protocols that can provide deterministic performance guarantees rather than best-effort delivery mechanisms.
The emergence of Industry 4.0 and smart manufacturing has created substantial demand for reliable communication systems that can support real-time control loops, predictive maintenance, and synchronized operations across distributed factory networks. Manufacturing environments require communication solutions that can maintain data integrity despite electromagnetic interference, physical obstacles, and high-density device deployments that characterize modern industrial facilities.
Telecommunications infrastructure providers face mounting pressure to deliver enhanced data reliability while managing spectrum scarcity and increasing user density. The transition toward software-defined networks and network function virtualization has created opportunities for implementing advanced modulation schemes and multiple access techniques that can adapt to varying channel conditions and traffic patterns while preserving data integrity.
Consumer applications including streaming services, online gaming, video conferencing, and cloud computing have established user expectations for seamless, error-free data transmission. Service providers must balance the competing requirements of throughput, latency, and reliability while managing network resources efficiently across diverse user populations and usage patterns.
The growing adoption of edge computing and distributed processing architectures has intensified the need for communication systems that can maintain data consistency across geographically dispersed nodes. These applications require protocols that can detect and correct transmission errors while minimizing retransmission overhead that could impact overall system performance and user experience.
Regulatory frameworks across various industries increasingly mandate specific data integrity standards for communication systems, particularly in healthcare, finance, and transportation sectors. Compliance requirements drive market demand for communication solutions that can provide auditable data transmission records and demonstrate adherence to established reliability standards.
Current FSK and TDMA Data Integrity Challenges
Frequency Shift Keying (FSK) modulation faces significant data integrity challenges in contemporary communication systems. The primary concern stems from frequency drift and phase noise, which can cause bit errors when the receiver incorrectly interprets frequency shifts. Environmental factors such as temperature variations and Doppler effects further exacerbate these issues, particularly in mobile communication scenarios. Additionally, FSK systems are susceptible to adjacent channel interference, where signals from neighboring frequency bands can corrupt the intended data transmission.
The coherent detection methods commonly employed in FSK systems require precise frequency synchronization between transmitter and receiver. Any deviation in this synchronization leads to increased bit error rates, especially in high-data-rate applications. Non-coherent detection, while more robust against synchronization issues, inherently suffers from higher error rates compared to coherent methods, creating a fundamental trade-off between system complexity and data integrity.
Time Division Multiple Access (TDMA) systems encounter distinct data integrity challenges primarily related to timing synchronization and slot management. Guard time optimization presents a critical challenge, as insufficient guard intervals lead to inter-slot interference, while excessive guard times reduce overall system efficiency. The synchronization overhead required to maintain precise timing across multiple users significantly impacts the effective data throughput and introduces potential points of failure.
Burst transmission characteristics inherent in TDMA systems create additional complications for error correction mechanisms. Traditional forward error correction (FEC) schemes must be adapted to handle the discontinuous nature of TDMA transmissions, often resulting in increased overhead and reduced coding efficiency. The time-sensitive nature of slot allocation also limits the implementation of automatic repeat request (ARQ) protocols, as retransmission delays can disrupt the entire frame structure.
Cross-system interference represents a growing concern when FSK and TDMA technologies coexist in shared spectrum environments. The frequency agility of FSK systems can inadvertently interfere with TDMA time slots operating in adjacent frequency bands, while TDMA burst transmissions can create transient interference affecting FSK frequency detection algorithms.
Power control mechanisms in both systems present ongoing challenges for maintaining data integrity. FSK systems require consistent power levels to ensure reliable frequency discrimination, while TDMA systems must manage power ramping during slot transitions to minimize interference with adjacent time slots. These power management requirements become increasingly complex in multi-user environments where dynamic channel conditions demand real-time adaptation.
The coherent detection methods commonly employed in FSK systems require precise frequency synchronization between transmitter and receiver. Any deviation in this synchronization leads to increased bit error rates, especially in high-data-rate applications. Non-coherent detection, while more robust against synchronization issues, inherently suffers from higher error rates compared to coherent methods, creating a fundamental trade-off between system complexity and data integrity.
Time Division Multiple Access (TDMA) systems encounter distinct data integrity challenges primarily related to timing synchronization and slot management. Guard time optimization presents a critical challenge, as insufficient guard intervals lead to inter-slot interference, while excessive guard times reduce overall system efficiency. The synchronization overhead required to maintain precise timing across multiple users significantly impacts the effective data throughput and introduces potential points of failure.
Burst transmission characteristics inherent in TDMA systems create additional complications for error correction mechanisms. Traditional forward error correction (FEC) schemes must be adapted to handle the discontinuous nature of TDMA transmissions, often resulting in increased overhead and reduced coding efficiency. The time-sensitive nature of slot allocation also limits the implementation of automatic repeat request (ARQ) protocols, as retransmission delays can disrupt the entire frame structure.
Cross-system interference represents a growing concern when FSK and TDMA technologies coexist in shared spectrum environments. The frequency agility of FSK systems can inadvertently interfere with TDMA time slots operating in adjacent frequency bands, while TDMA burst transmissions can create transient interference affecting FSK frequency detection algorithms.
Power control mechanisms in both systems present ongoing challenges for maintaining data integrity. FSK systems require consistent power levels to ensure reliable frequency discrimination, while TDMA systems must manage power ramping during slot transitions to minimize interference with adjacent time slots. These power management requirements become increasingly complex in multi-user environments where dynamic channel conditions demand real-time adaptation.
Existing FSK and TDMA Data Protection Solutions
01 Error detection and correction in FSK-TDMA systems
Implementation of error detection and correction mechanisms to ensure data integrity in frequency shift keying and time division multiple access communication systems. These techniques include cyclic redundancy check (CRC), forward error correction (FEC), and parity checking to detect and correct transmission errors. The methods help maintain reliable data transmission by identifying corrupted bits and recovering original data through redundancy coding schemes.- Error detection and correction in FSK-TDMA systems: Implementation of error detection and correction mechanisms to ensure data integrity in frequency shift keying and time division multiple access communication systems. These techniques include the use of cyclic redundancy checks, forward error correction codes, and interleaving methods to detect and correct transmission errors that may occur during data transmission over wireless channels.
- Synchronization and timing control for TDMA data transmission: Methods for maintaining synchronization and precise timing control in time division multiple access systems to preserve data integrity. This includes frame synchronization techniques, slot timing alignment, and guard time management to prevent data collision and ensure accurate reception of transmitted information across multiple access channels.
- Authentication and encryption for secure FSK communication: Security mechanisms incorporating authentication protocols and encryption algorithms to protect data integrity in frequency shift keying transmission systems. These methods prevent unauthorized access and data tampering through cryptographic techniques, digital signatures, and secure key exchange protocols specifically designed for wireless communication environments.
- Channel coding and modulation optimization: Advanced channel coding schemes and modulation optimization techniques to enhance data integrity in combined FSK and TDMA systems. This includes adaptive modulation, convolutional coding, turbo coding, and bit interleaving strategies that improve signal quality and reduce bit error rates under varying channel conditions.
- Protocol design for reliable data transmission: Communication protocol architectures specifically designed to ensure reliable data transmission and integrity verification in FSK-TDMA networks. These protocols incorporate acknowledgment mechanisms, retransmission strategies, packet sequencing, and checksum validation to guarantee successful delivery and verification of transmitted data packets.
02 Synchronization and timing control for TDMA slot allocation
Techniques for maintaining precise synchronization and timing control in time division multiple access systems to prevent data collision and ensure integrity. Methods include frame synchronization, slot timing adjustment, and guard time implementation to separate user transmissions. Proper synchronization prevents overlapping transmissions and maintains the integrity of data packets transmitted in assigned time slots.Expand Specific Solutions03 Authentication and encryption for secure FSK transmission
Security mechanisms including authentication protocols and encryption algorithms applied to frequency shift keying transmissions to protect data integrity. These methods prevent unauthorized access and tampering of transmitted data through cryptographic techniques. Implementation of message authentication codes and digital signatures ensures that received data has not been modified during transmission.Expand Specific Solutions04 Interference mitigation and signal quality enhancement
Techniques for reducing interference and improving signal quality in FSK-TDMA systems to maintain data integrity. Methods include adaptive filtering, frequency hopping, power control, and diversity reception to combat channel impairments. These approaches minimize bit errors caused by noise, fading, and co-channel interference, thereby preserving the accuracy of transmitted information.Expand Specific Solutions05 Retransmission protocols and acknowledgment mechanisms
Implementation of automatic repeat request (ARQ) protocols and acknowledgment schemes to ensure reliable data delivery in FSK-TDMA networks. These mechanisms detect missing or corrupted packets and trigger retransmission to recover lost data. Positive and negative acknowledgment systems combined with timeout mechanisms guarantee that all transmitted data is successfully received and verified by the intended recipient.Expand Specific Solutions
Key Players in Digital Communication Technology
The competitive landscape for Frequency Shift Keying versus Time Division Multiple Access data integrity technologies reflects a mature telecommunications sector experiencing rapid evolution toward 5G and beyond. The market demonstrates substantial scale, driven by global connectivity demands and IoT proliferation. Technology maturity varies significantly across players, with established telecommunications giants like Huawei Technologies, Qualcomm, Ericsson, and Nokia Technologies leading advanced modulation and multiple access implementations. Traditional infrastructure providers including Siemens AG and Cisco Technology maintain strong positions in network equipment, while semiconductor specialists like MediaTek and Spreadtrum focus on chipset-level optimizations. Research institutions such as Xidian University contribute foundational innovations, while patent holders like InterDigital Technology Corp. influence industry standards. The competitive dynamics show convergence toward hybrid approaches combining FSK robustness with TDMA efficiency for enhanced data integrity.
Huawei Technologies Co., Ltd.
Technical Solution: Huawei's approach combines FSK with advanced forward error correction (FEC) techniques, implementing Reed-Solomon coding and convolutional coding to enhance data integrity. Their TDMA solutions feature intelligent time slot allocation algorithms that adapt to network traffic patterns while maintaining synchronization accuracy within microsecond precision. The company's base station equipment incorporates machine learning algorithms to predict and compensate for signal degradation, automatically switching between FSK and higher-order modulation schemes based on link quality metrics. Their proprietary interference cancellation technology significantly improves data integrity in dense deployment scenarios.
Strengths: Comprehensive end-to-end solutions, strong R&D capabilities, cost-effective implementations. Weaknesses: Geopolitical restrictions limiting market access, concerns over technology transfer and security.
InterDigital Technology Corp.
Technical Solution: InterDigital develops advanced FSK techniques with non-coherent detection algorithms optimized for low-power IoT applications while maintaining high data integrity through sophisticated error correction coding. Their TDMA research focuses on cognitive radio approaches that dynamically optimize time slot utilization based on spectrum sensing and interference analysis. The company's patent portfolio includes innovations in adaptive frequency hopping combined with FSK modulation to enhance security and reliability. Their solutions incorporate machine learning-based channel prediction algorithms that proactively adjust transmission parameters to maintain data integrity under varying propagation conditions.
Strengths: Strong intellectual property portfolio, innovative research capabilities, focus on next-generation wireless technologies. Weaknesses: Limited manufacturing capabilities, dependency on licensing revenue model, smaller market presence compared to major equipment vendors.
Core Patents in FSK-TDMA Data Integrity Enhancement
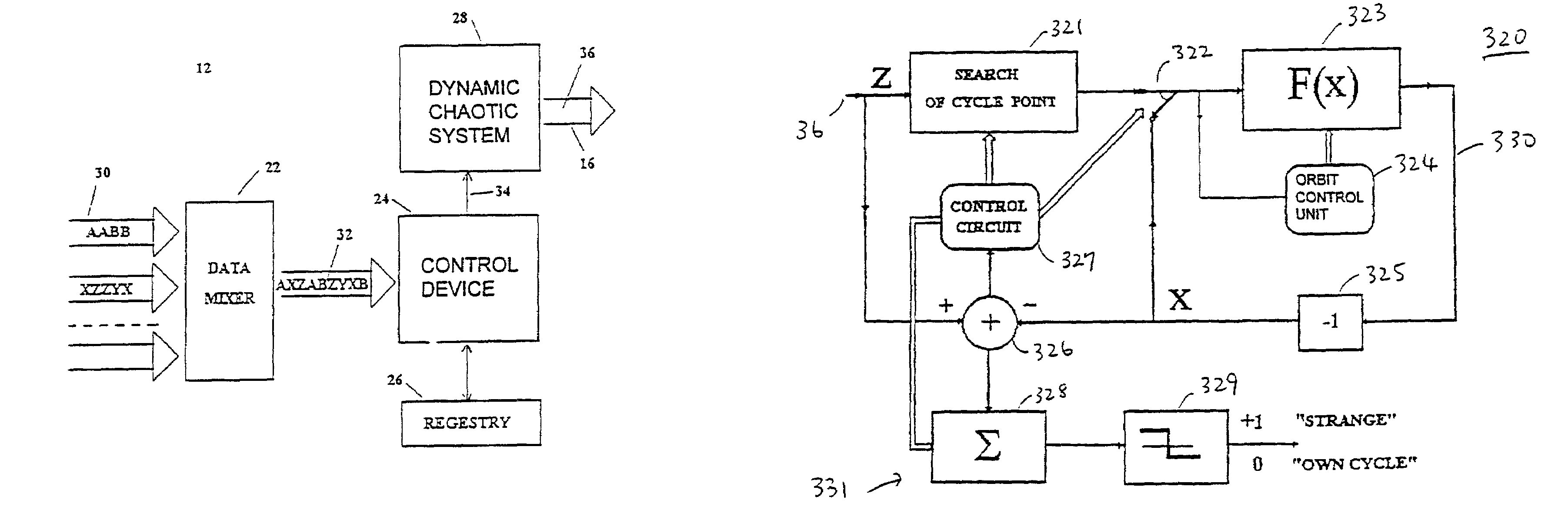
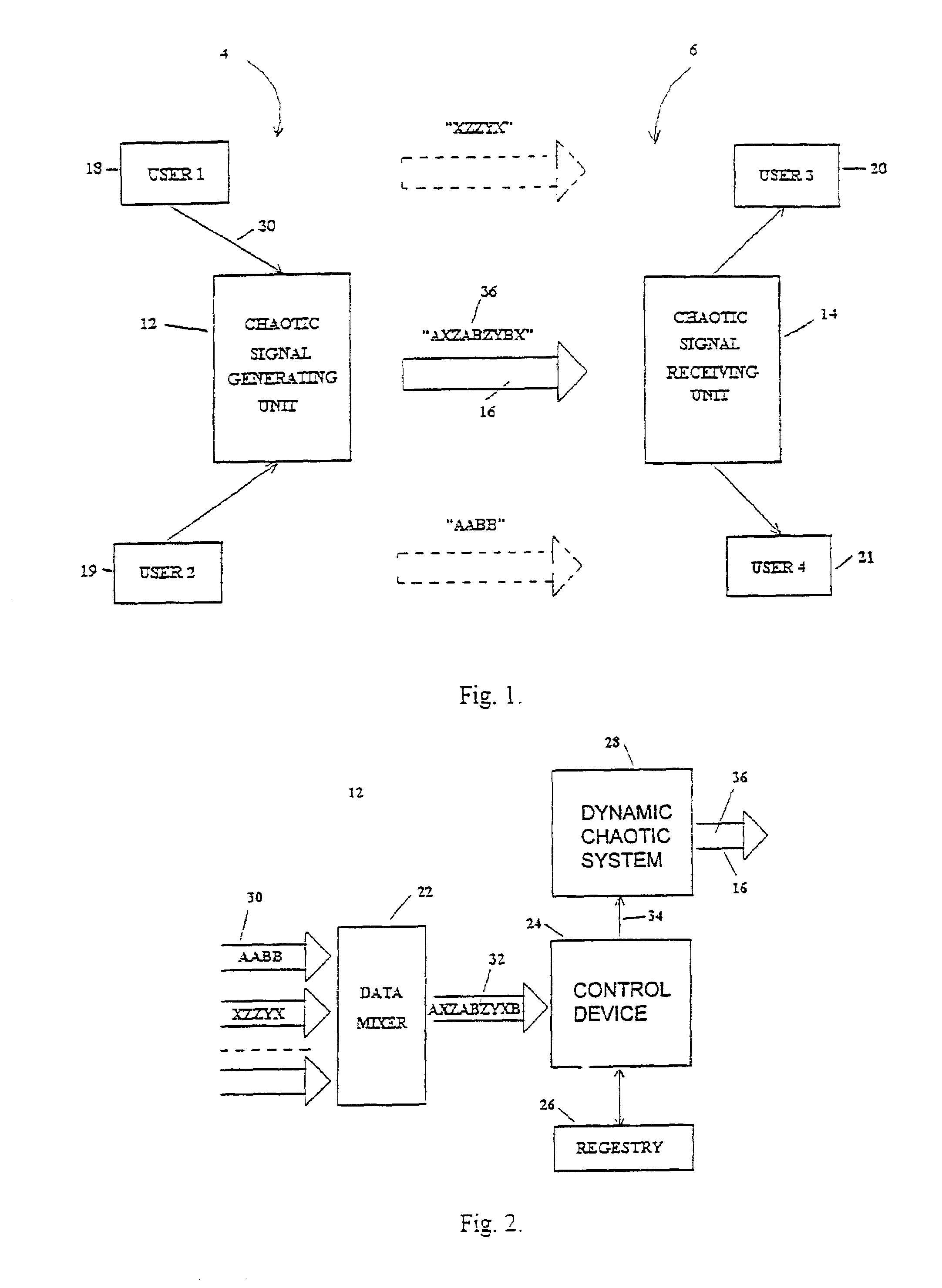
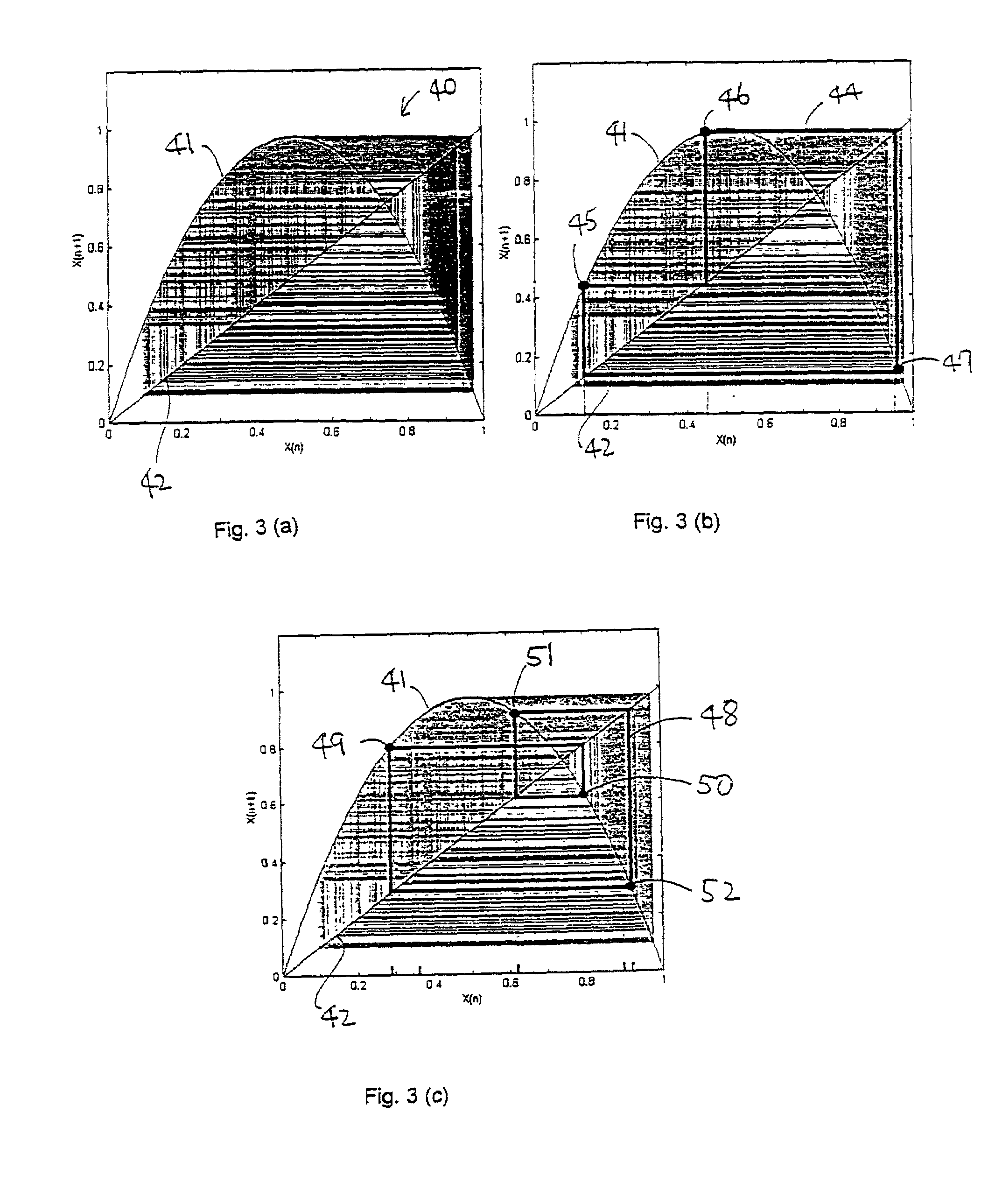
Multiple access communication system using chaotic signals and method for generating and extracting chaotic signals
PatentInactiveUS6999445B1
Innovation
- A multiple access communication system utilizing a chaotic signal generating unit with a dynamic chaotic system having a strange attractor and unstable periodic orbits, where each sender-recipient pair is assigned a set of characters matched to specific unstable orbits, and a selecting dynamic chaotic system at the receiving end extracts intended chaotic signals through iterative processes.
Time division multiple access communication system, signal receiving method in time division multiple access communication system, and center unit for use in time division multiple access communication system
PatentInactiveUS6347092B1
Innovation
- A time division multiple access communication system where the center unit receives varying channel signals during the fixed channel receive period, allowing for a prolonged variation allowable period without affecting the fixed channel receive period, enabling extended distance coverage.
Spectrum Regulation and Communication Standards
The regulatory landscape governing spectrum allocation and communication standards plays a crucial role in determining the viability and implementation of both Frequency Shift Keying (FSK) and Time Division Multiple Access (TDMA) technologies. International bodies such as the International Telecommunication Union (ITU) establish fundamental frameworks for spectrum management, while regional authorities like the Federal Communications Commission (FCC) in the United States and the European Telecommunications Standards Institute (ETSI) provide specific implementation guidelines that directly impact data integrity requirements.
FSK modulation techniques operate within strictly regulated frequency bands, where spectrum efficiency and interference mitigation are paramount concerns. Regulatory standards mandate specific parameters for frequency deviation, symbol rates, and spectral masks to ensure coexistence with adjacent channel users. These constraints directly influence data integrity performance, as tighter spectral limitations may require reduced deviation ratios, potentially compromising noise immunity and error rates.
TDMA systems face distinct regulatory challenges related to synchronization accuracy and time slot coordination. Standards such as GSM specifications define precise timing requirements, guard intervals, and power ramping characteristics that are essential for maintaining data integrity across multiple users. Regulatory compliance often necessitates sophisticated synchronization mechanisms and error correction protocols to meet stringent bit error rate thresholds.
Emerging spectrum sharing paradigms, including dynamic spectrum access and cognitive radio technologies, are reshaping traditional regulatory approaches. These developments particularly impact FSK implementations in unlicensed bands, where adaptive power control and interference avoidance mechanisms become critical for maintaining data integrity. TDMA systems benefit from more predictable interference patterns but must adapt to increasingly complex coexistence scenarios.
The convergence toward software-defined radio architectures has prompted regulatory bodies to develop more flexible certification processes. This evolution enables more sophisticated implementations of both FSK and TDMA that can dynamically optimize data integrity parameters while maintaining compliance with evolving standards. Future regulatory trends indicate increased emphasis on interference mitigation capabilities and adaptive transmission strategies.
FSK modulation techniques operate within strictly regulated frequency bands, where spectrum efficiency and interference mitigation are paramount concerns. Regulatory standards mandate specific parameters for frequency deviation, symbol rates, and spectral masks to ensure coexistence with adjacent channel users. These constraints directly influence data integrity performance, as tighter spectral limitations may require reduced deviation ratios, potentially compromising noise immunity and error rates.
TDMA systems face distinct regulatory challenges related to synchronization accuracy and time slot coordination. Standards such as GSM specifications define precise timing requirements, guard intervals, and power ramping characteristics that are essential for maintaining data integrity across multiple users. Regulatory compliance often necessitates sophisticated synchronization mechanisms and error correction protocols to meet stringent bit error rate thresholds.
Emerging spectrum sharing paradigms, including dynamic spectrum access and cognitive radio technologies, are reshaping traditional regulatory approaches. These developments particularly impact FSK implementations in unlicensed bands, where adaptive power control and interference avoidance mechanisms become critical for maintaining data integrity. TDMA systems benefit from more predictable interference patterns but must adapt to increasingly complex coexistence scenarios.
The convergence toward software-defined radio architectures has prompted regulatory bodies to develop more flexible certification processes. This evolution enables more sophisticated implementations of both FSK and TDMA that can dynamically optimize data integrity parameters while maintaining compliance with evolving standards. Future regulatory trends indicate increased emphasis on interference mitigation capabilities and adaptive transmission strategies.
Security Framework for FSK-TDMA Systems
The security framework for FSK-TDMA systems represents a comprehensive approach to addressing data integrity challenges inherent in frequency shift keying combined with time division multiple access architectures. This framework encompasses multiple layers of protection mechanisms designed to mitigate vulnerabilities that arise from the intersection of frequency-based modulation and time-slotted channel access methods.
At the foundational level, the security framework establishes cryptographic protocols specifically tailored for FSK-TDMA environments. These protocols account for the unique timing constraints imposed by TDMA slot allocations while maintaining the frequency stability requirements of FSK modulation. The framework incorporates adaptive encryption algorithms that can dynamically adjust their computational complexity based on available time slot durations and frequency channel conditions.
Authentication mechanisms within the framework utilize frequency-hopping patterns as additional security parameters, creating multi-dimensional authentication vectors that combine temporal slot assignments with frequency signatures. This approach significantly enhances resistance against spoofing attacks while maintaining system efficiency. The framework also implements real-time integrity verification protocols that operate within TDMA time constraints.
Error detection and correction capabilities are integrated through redundant frequency channels and temporal diversity techniques. The framework employs cross-layer security monitoring that correlates frequency domain anomalies with time slot irregularities to identify potential security breaches or data corruption events. Advanced signal processing algorithms continuously analyze frequency deviation patterns and timing synchronization metrics to detect unauthorized access attempts.
The framework addresses interference mitigation through adaptive frequency selection algorithms that consider both security requirements and signal quality metrics. It incorporates machine learning-based threat detection systems capable of identifying sophisticated attacks that exploit the interaction between FSK modulation characteristics and TDMA scheduling vulnerabilities. Recovery mechanisms ensure rapid restoration of secure communications following detected security incidents while maintaining system availability and performance standards.
At the foundational level, the security framework establishes cryptographic protocols specifically tailored for FSK-TDMA environments. These protocols account for the unique timing constraints imposed by TDMA slot allocations while maintaining the frequency stability requirements of FSK modulation. The framework incorporates adaptive encryption algorithms that can dynamically adjust their computational complexity based on available time slot durations and frequency channel conditions.
Authentication mechanisms within the framework utilize frequency-hopping patterns as additional security parameters, creating multi-dimensional authentication vectors that combine temporal slot assignments with frequency signatures. This approach significantly enhances resistance against spoofing attacks while maintaining system efficiency. The framework also implements real-time integrity verification protocols that operate within TDMA time constraints.
Error detection and correction capabilities are integrated through redundant frequency channels and temporal diversity techniques. The framework employs cross-layer security monitoring that correlates frequency domain anomalies with time slot irregularities to identify potential security breaches or data corruption events. Advanced signal processing algorithms continuously analyze frequency deviation patterns and timing synchronization metrics to detect unauthorized access attempts.
The framework addresses interference mitigation through adaptive frequency selection algorithms that consider both security requirements and signal quality metrics. It incorporates machine learning-based threat detection systems capable of identifying sophisticated attacks that exploit the interaction between FSK modulation characteristics and TDMA scheduling vulnerabilities. Recovery mechanisms ensure rapid restoration of secure communications following detected security incidents while maintaining system availability and performance standards.
Unlock deeper insights with PatSnap Eureka Quick Research — get a full tech report to explore trends and direct your research. Try now!
Generate Your Research Report Instantly with AI Agent
Supercharge your innovation with PatSnap Eureka AI Agent Platform!