Autonomous Database Security in Cloud Environments
MAR 17, 20269 MIN READ
Generate Your Research Report Instantly with AI Agent
PatSnap Eureka helps you evaluate technical feasibility & market potential.
Autonomous Database Security Background and Objectives
The evolution of database systems has undergone a transformative journey from traditional on-premises architectures to sophisticated cloud-native autonomous platforms. This progression represents a fundamental shift in how organizations manage, secure, and optimize their data infrastructure. Traditional database management required extensive manual intervention for tasks such as performance tuning, backup management, and security configuration, creating significant operational overhead and potential human error vulnerabilities.
The emergence of cloud computing has revolutionized database deployment models, offering unprecedented scalability, flexibility, and cost-effectiveness. However, this transition has introduced complex security challenges that extend beyond conventional database protection mechanisms. Cloud environments present unique attack vectors, shared responsibility models, and multi-tenancy concerns that demand innovative security approaches.
Autonomous databases represent the next evolutionary step, incorporating artificial intelligence and machine learning capabilities to self-manage, self-secure, and self-repair without human intervention. These systems promise to eliminate human error, reduce operational costs, and enhance security posture through continuous monitoring and automated threat response. The integration of autonomous capabilities with cloud infrastructure creates a powerful synergy that addresses many traditional database management challenges.
The primary objective of autonomous database security research in cloud environments centers on developing comprehensive protection frameworks that can adapt to dynamic threat landscapes while maintaining operational efficiency. This includes establishing automated threat detection mechanisms that can identify and respond to security incidents in real-time, without compromising system performance or availability.
Another critical objective involves creating robust access control systems that can intelligently manage user permissions, detect anomalous behavior patterns, and enforce security policies across distributed cloud architectures. The research aims to develop self-healing security mechanisms that can automatically remediate vulnerabilities and strengthen defenses based on emerging threat intelligence.
Furthermore, the research seeks to establish standardized security benchmarks and compliance frameworks specifically tailored for autonomous database systems in cloud environments. This includes developing automated audit capabilities, ensuring data privacy protection, and maintaining regulatory compliance across multiple jurisdictions and cloud service providers.
The emergence of cloud computing has revolutionized database deployment models, offering unprecedented scalability, flexibility, and cost-effectiveness. However, this transition has introduced complex security challenges that extend beyond conventional database protection mechanisms. Cloud environments present unique attack vectors, shared responsibility models, and multi-tenancy concerns that demand innovative security approaches.
Autonomous databases represent the next evolutionary step, incorporating artificial intelligence and machine learning capabilities to self-manage, self-secure, and self-repair without human intervention. These systems promise to eliminate human error, reduce operational costs, and enhance security posture through continuous monitoring and automated threat response. The integration of autonomous capabilities with cloud infrastructure creates a powerful synergy that addresses many traditional database management challenges.
The primary objective of autonomous database security research in cloud environments centers on developing comprehensive protection frameworks that can adapt to dynamic threat landscapes while maintaining operational efficiency. This includes establishing automated threat detection mechanisms that can identify and respond to security incidents in real-time, without compromising system performance or availability.
Another critical objective involves creating robust access control systems that can intelligently manage user permissions, detect anomalous behavior patterns, and enforce security policies across distributed cloud architectures. The research aims to develop self-healing security mechanisms that can automatically remediate vulnerabilities and strengthen defenses based on emerging threat intelligence.
Furthermore, the research seeks to establish standardized security benchmarks and compliance frameworks specifically tailored for autonomous database systems in cloud environments. This includes developing automated audit capabilities, ensuring data privacy protection, and maintaining regulatory compliance across multiple jurisdictions and cloud service providers.
Market Demand for Secure Cloud Database Solutions
The global cloud database market has experienced unprecedented growth as organizations accelerate their digital transformation initiatives. Enterprise adoption of cloud-native database solutions has surged, driven by the need for scalability, cost optimization, and operational efficiency. However, this migration has simultaneously amplified security concerns, creating a substantial demand for secure cloud database solutions that can protect sensitive data while maintaining performance and accessibility.
Financial services, healthcare, and government sectors represent the most security-conscious market segments, where regulatory compliance requirements such as GDPR, HIPAA, and SOX mandate stringent data protection measures. These industries are increasingly seeking autonomous database security solutions that can automatically detect, prevent, and respond to threats without human intervention. The demand is particularly acute for solutions that can provide real-time threat detection, automated patch management, and continuous compliance monitoring.
Small and medium enterprises constitute a rapidly growing market segment for secure cloud database solutions. These organizations often lack dedicated security expertise and are attracted to autonomous security features that reduce operational complexity while providing enterprise-grade protection. The democratization of advanced security capabilities through cloud-based autonomous systems has made sophisticated database protection accessible to organizations with limited IT resources.
Multi-cloud and hybrid cloud deployments have created additional market demand for unified security solutions that can operate consistently across different cloud environments. Organizations require autonomous database security systems capable of maintaining consistent security policies and threat detection capabilities regardless of the underlying cloud infrastructure provider.
The market demand is further intensified by the increasing sophistication of cyber threats targeting cloud databases. Advanced persistent threats, insider attacks, and zero-day exploits have created an urgent need for proactive, intelligent security solutions that can adapt to evolving threat landscapes without requiring constant manual updates or configuration changes.
Emerging technologies such as artificial intelligence, machine learning, and blockchain are driving demand for specialized security solutions that can protect these new data types and processing patterns. Organizations implementing AI-driven applications require autonomous database security systems that can understand and protect complex data relationships while maintaining the performance requirements of real-time analytics and machine learning workloads.
Financial services, healthcare, and government sectors represent the most security-conscious market segments, where regulatory compliance requirements such as GDPR, HIPAA, and SOX mandate stringent data protection measures. These industries are increasingly seeking autonomous database security solutions that can automatically detect, prevent, and respond to threats without human intervention. The demand is particularly acute for solutions that can provide real-time threat detection, automated patch management, and continuous compliance monitoring.
Small and medium enterprises constitute a rapidly growing market segment for secure cloud database solutions. These organizations often lack dedicated security expertise and are attracted to autonomous security features that reduce operational complexity while providing enterprise-grade protection. The democratization of advanced security capabilities through cloud-based autonomous systems has made sophisticated database protection accessible to organizations with limited IT resources.
Multi-cloud and hybrid cloud deployments have created additional market demand for unified security solutions that can operate consistently across different cloud environments. Organizations require autonomous database security systems capable of maintaining consistent security policies and threat detection capabilities regardless of the underlying cloud infrastructure provider.
The market demand is further intensified by the increasing sophistication of cyber threats targeting cloud databases. Advanced persistent threats, insider attacks, and zero-day exploits have created an urgent need for proactive, intelligent security solutions that can adapt to evolving threat landscapes without requiring constant manual updates or configuration changes.
Emerging technologies such as artificial intelligence, machine learning, and blockchain are driving demand for specialized security solutions that can protect these new data types and processing patterns. Organizations implementing AI-driven applications require autonomous database security systems that can understand and protect complex data relationships while maintaining the performance requirements of real-time analytics and machine learning workloads.
Current Security Challenges in Cloud Autonomous Databases
Cloud autonomous databases face unprecedented security challenges as they operate in dynamic, multi-tenant environments with minimal human intervention. The convergence of cloud computing vulnerabilities and autonomous system complexities creates a unique threat landscape that traditional security measures struggle to address effectively.
Data protection remains the most critical challenge, as autonomous databases must secure sensitive information across distributed cloud infrastructures. Multi-tenancy introduces risks of data leakage between different customer environments, while automated data movement and replication processes can inadvertently expose confidential information. The challenge intensifies when considering compliance requirements such as GDPR, HIPAA, and SOX, which demand strict data governance controls that must be maintained autonomously.
Identity and access management presents significant complexity in autonomous environments. Traditional role-based access controls become insufficient when dealing with machine-to-machine authentication, automated privilege escalation, and dynamic resource allocation. The autonomous nature of these systems requires sophisticated authentication mechanisms that can adapt to changing workloads while maintaining security integrity without human oversight.
Network security vulnerabilities emerge from the distributed nature of cloud autonomous databases. Attack vectors include man-in-the-middle attacks during data synchronization, unauthorized access through misconfigured network policies, and lateral movement within cloud environments. The autonomous systems must continuously monitor and adapt network security configurations while maintaining optimal performance and availability.
Configuration drift and security policy enforcement pose ongoing challenges as autonomous databases self-optimize and scale. Automated configuration changes may inadvertently weaken security postures, while the rapid pace of autonomous adjustments makes it difficult to maintain consistent security baselines. Security policies must be embedded into the autonomous decision-making processes to ensure compliance is maintained during all operational changes.
Threat detection and response capabilities must evolve to address sophisticated attacks targeting autonomous systems. Advanced persistent threats can exploit the predictable patterns of autonomous operations, while AI-powered attacks may attempt to manipulate the machine learning algorithms that drive autonomous decisions. Real-time anomaly detection becomes crucial but challenging when distinguishing between legitimate autonomous optimizations and malicious activities.
The integration of multiple cloud services and third-party components creates additional attack surfaces that autonomous databases must continuously monitor and secure. Supply chain security becomes paramount as autonomous systems rely on various external services and APIs that could introduce vulnerabilities or become compromise vectors for attackers seeking to infiltrate the database environment.
Data protection remains the most critical challenge, as autonomous databases must secure sensitive information across distributed cloud infrastructures. Multi-tenancy introduces risks of data leakage between different customer environments, while automated data movement and replication processes can inadvertently expose confidential information. The challenge intensifies when considering compliance requirements such as GDPR, HIPAA, and SOX, which demand strict data governance controls that must be maintained autonomously.
Identity and access management presents significant complexity in autonomous environments. Traditional role-based access controls become insufficient when dealing with machine-to-machine authentication, automated privilege escalation, and dynamic resource allocation. The autonomous nature of these systems requires sophisticated authentication mechanisms that can adapt to changing workloads while maintaining security integrity without human oversight.
Network security vulnerabilities emerge from the distributed nature of cloud autonomous databases. Attack vectors include man-in-the-middle attacks during data synchronization, unauthorized access through misconfigured network policies, and lateral movement within cloud environments. The autonomous systems must continuously monitor and adapt network security configurations while maintaining optimal performance and availability.
Configuration drift and security policy enforcement pose ongoing challenges as autonomous databases self-optimize and scale. Automated configuration changes may inadvertently weaken security postures, while the rapid pace of autonomous adjustments makes it difficult to maintain consistent security baselines. Security policies must be embedded into the autonomous decision-making processes to ensure compliance is maintained during all operational changes.
Threat detection and response capabilities must evolve to address sophisticated attacks targeting autonomous systems. Advanced persistent threats can exploit the predictable patterns of autonomous operations, while AI-powered attacks may attempt to manipulate the machine learning algorithms that drive autonomous decisions. Real-time anomaly detection becomes crucial but challenging when distinguishing between legitimate autonomous optimizations and malicious activities.
The integration of multiple cloud services and third-party components creates additional attack surfaces that autonomous databases must continuously monitor and secure. Supply chain security becomes paramount as autonomous systems rely on various external services and APIs that could introduce vulnerabilities or become compromise vectors for attackers seeking to infiltrate the database environment.
Existing Security Solutions for Autonomous Databases
01 Autonomous security policy management and enforcement
Database systems can implement autonomous security mechanisms that automatically manage and enforce security policies without manual intervention. These systems utilize machine learning algorithms and predefined rules to detect anomalies, assess risks, and apply appropriate security measures in real-time. The autonomous approach enables continuous monitoring and adaptive protection against evolving threats while reducing administrative overhead.- Autonomous security policy management and enforcement: Database systems can implement autonomous security mechanisms that automatically manage and enforce security policies without manual intervention. These systems utilize machine learning algorithms and predefined rules to detect anomalies, assess risks, and apply appropriate security measures in real-time. The autonomous approach enables continuous monitoring and adaptive protection against evolving threats while reducing administrative overhead.
- Access control and authentication mechanisms: Advanced access control systems provide multi-layered authentication and authorization for database security. These mechanisms include role-based access control, attribute-based policies, and dynamic credential management. The systems can automatically verify user identities, validate permissions, and restrict unauthorized access to sensitive data through intelligent authentication protocols and token-based verification methods.
- Encryption and data protection techniques: Database security implementations incorporate sophisticated encryption methods to protect data at rest and in transit. These techniques include transparent data encryption, column-level encryption, and key management systems that operate autonomously. The encryption mechanisms can automatically identify sensitive data, apply appropriate encryption algorithms, and manage cryptographic keys without requiring constant manual oversight.
- Threat detection and intrusion prevention: Autonomous database security systems employ advanced threat detection capabilities that identify and respond to potential security breaches. These systems utilize behavioral analysis, pattern recognition, and anomaly detection to identify suspicious activities. The intrusion prevention mechanisms can automatically block malicious queries, isolate compromised components, and trigger alerts while maintaining database availability and performance.
- Audit logging and compliance monitoring: Comprehensive audit logging systems automatically track and record all database activities for security analysis and compliance purposes. These mechanisms capture user actions, data modifications, and system events in tamper-proof logs. The autonomous monitoring capabilities can analyze audit trails, generate compliance reports, and identify policy violations without manual review, ensuring adherence to regulatory requirements and security standards.
02 Access control and authentication mechanisms
Advanced access control systems provide multi-layered authentication and authorization for database security. These mechanisms include role-based access control, attribute-based policies, and dynamic permission management that adapts to user behavior and context. The systems can automatically verify user identities, validate credentials, and grant appropriate access levels based on predefined security rules and real-time risk assessment.Expand Specific Solutions03 Encryption and data protection techniques
Database security implementations incorporate comprehensive encryption methods to protect data at rest and in transit. These techniques include transparent data encryption, column-level encryption, and key management systems that operate autonomously. The encryption mechanisms can automatically identify sensitive data, apply appropriate encryption algorithms, and manage cryptographic keys throughout their lifecycle to ensure data confidentiality and integrity.Expand Specific Solutions04 Threat detection and anomaly monitoring
Autonomous database security systems employ sophisticated threat detection capabilities that continuously monitor database activities for suspicious patterns and potential security breaches. These systems utilize behavioral analysis, pattern recognition, and artificial intelligence to identify unauthorized access attempts, data exfiltration, and other malicious activities. The monitoring mechanisms can automatically trigger alerts and initiate protective responses when threats are detected.Expand Specific Solutions05 Audit logging and compliance management
Comprehensive audit logging systems automatically track and record all database operations, access attempts, and security events for compliance and forensic purposes. These systems maintain detailed logs of user activities, configuration changes, and security incidents while ensuring log integrity and tamper-proof storage. The autonomous logging mechanisms can generate compliance reports, facilitate security audits, and provide evidence for incident investigation without requiring manual intervention.Expand Specific Solutions
Key Players in Cloud Database Security Market
The autonomous database security in cloud environments represents a rapidly evolving market segment currently in its growth phase, driven by increasing cloud adoption and stringent data protection regulations. The market demonstrates substantial expansion potential as organizations migrate critical workloads to cloud platforms, necessitating advanced automated security solutions. Technology maturity varies significantly across market participants, with established leaders like IBM, Oracle, and Microsoft leveraging decades of database expertise to develop sophisticated autonomous security capabilities, while specialized security firms such as Imperva, Cyera, and Proofpoint focus on targeted cloud-native protection solutions. Emerging players including Chinese technology companies like Inspur and Tianyi Cloud are rapidly advancing their autonomous database security offerings, alongside academic institutions such as Beihang University and Xiamen University contributing foundational research. The competitive landscape reflects a mix of mature enterprise solutions and innovative startups, indicating a dynamic market with significant technological advancement opportunities.
International Business Machines Corp.
Technical Solution: IBM's approach to autonomous database security in cloud environments centers on IBM Db2 on Cloud and Watson-powered AI security analytics. The solution incorporates automated threat detection using cognitive computing to identify unusual database access patterns and potential security breaches. IBM implements multi-layered encryption, automated backup and recovery with point-in-time restoration capabilities, and compliance management for various regulatory standards. The system features IBM Security Guardium for database activity monitoring, vulnerability assessment, and automated policy enforcement. Watson AI continuously learns from security events to improve threat detection accuracy and reduce false positives. The platform provides automated security configuration management and real-time alerting for suspicious activities across hybrid cloud deployments.
Strengths: Strong AI-driven security analytics, extensive compliance support, and robust hybrid cloud capabilities. Weaknesses: Complex implementation process and higher total cost of ownership compared to cloud-native solutions.
Oracle International Corp.
Technical Solution: Oracle's Autonomous Database implements comprehensive security through multiple layers including automatic encryption at rest and in transit, advanced threat detection using machine learning algorithms, and automated security patching without downtime. The system features Oracle Data Safe for unified security management, providing data discovery, classification, masking, and activity monitoring. Oracle's approach integrates Zero Trust security principles with continuous monitoring and automated response mechanisms. The database automatically applies security updates and patches vulnerabilities while maintaining high availability. Advanced features include database vault for privileged user access control, transparent data encryption, and real-time security analytics that can detect anomalous patterns and potential threats across cloud environments.
Strengths: Market-leading autonomous capabilities with proven enterprise-grade security, comprehensive built-in security tools, and seamless cloud integration. Weaknesses: High licensing costs and vendor lock-in concerns, complex migration from existing systems.
Core Security Innovations in Autonomous Database Systems
Assessing data security of a managed database deployed in the cloud using a secured sandbox environment
PatentActiveUS20230025740A1
Innovation
- Creating a secure sandbox environment within the cloud, where a snapshot of the database is loaded and assessed using scanner code that runs without network access to the public internet, allowing for deep database scans without affecting production data.
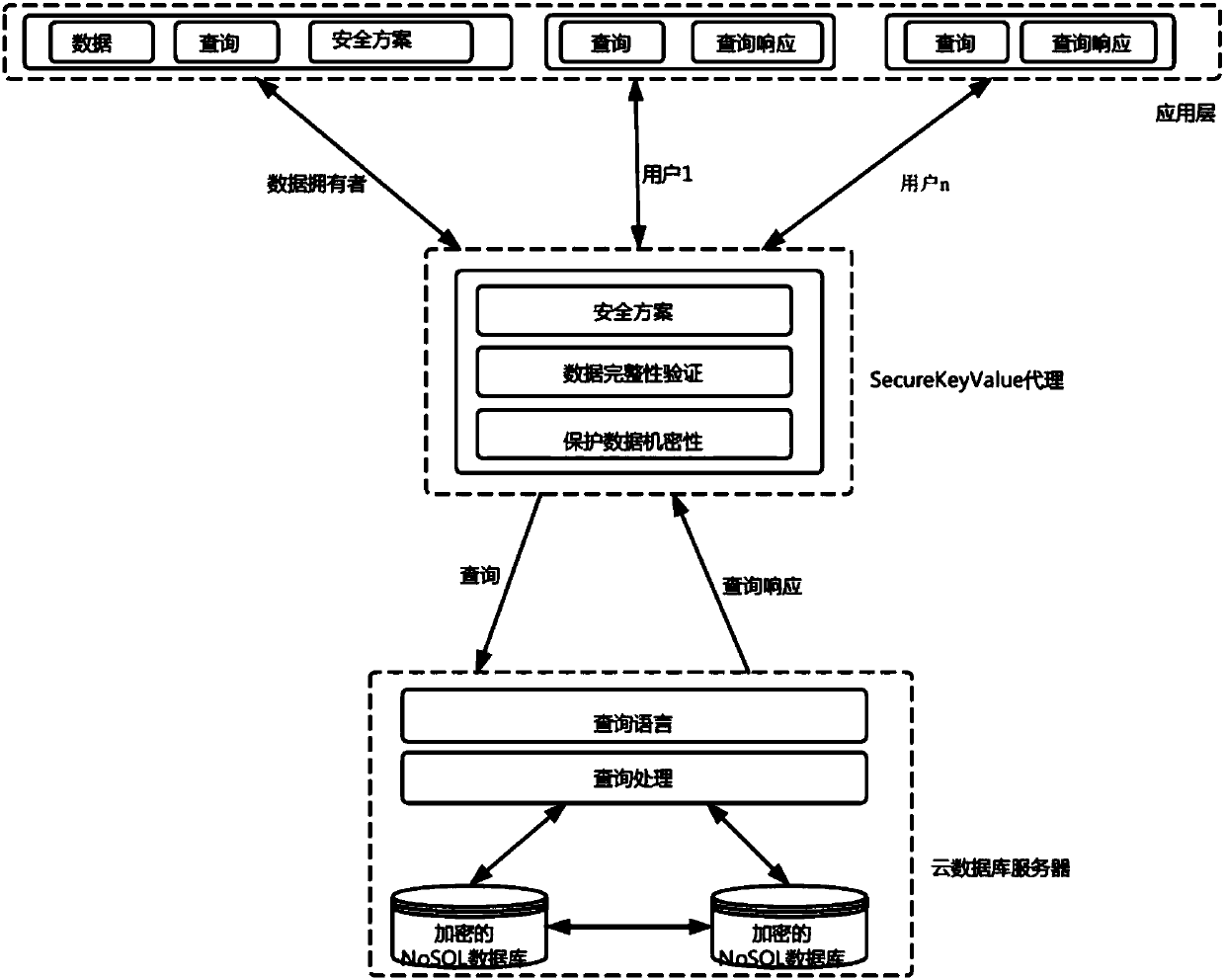
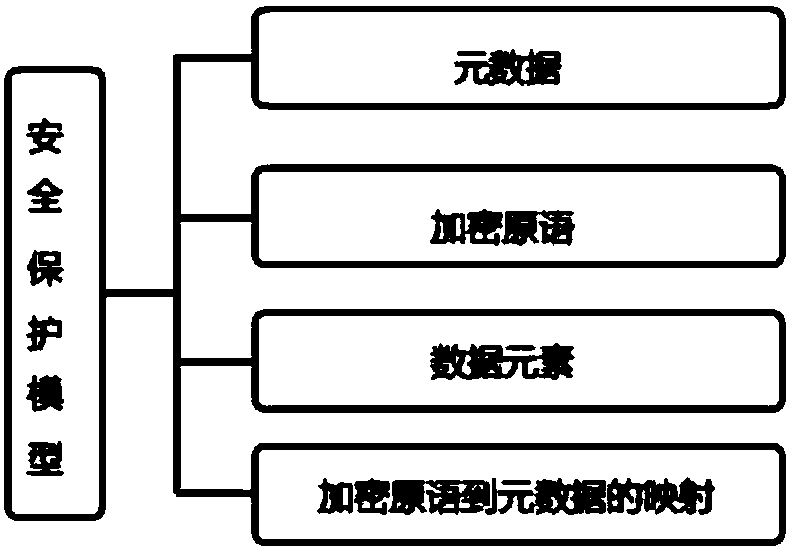
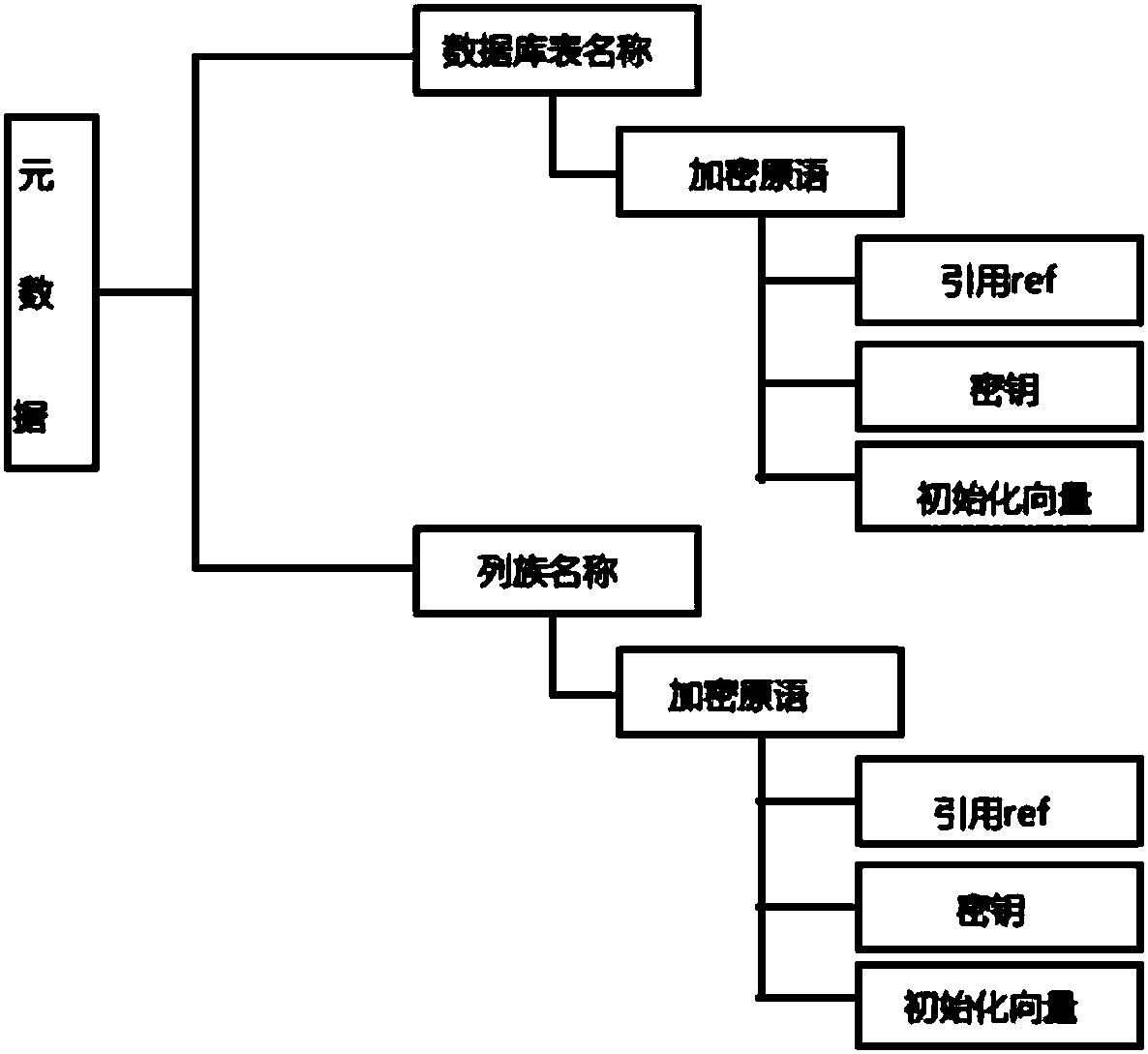
Method for Key-Value database encryption and security query in shared cloud
PatentInactiveCN108170753A
Innovation
- Adopt a multi-level self-describing Key-Value database security protection model, customize the security solution through the security protection model description language in JSON format, and design the security agent secureKeyValue, which is responsible for data encryption, decryption, query processing and data integrity verification to ensure that data is transmitted and remain encrypted during storage, providing confidentiality and integrity protection.
Cloud Data Protection Regulatory Compliance Framework
The regulatory landscape for cloud data protection has become increasingly complex as organizations migrate autonomous database systems to cloud environments. Multiple jurisdictions have established comprehensive frameworks that directly impact how sensitive data must be handled, stored, and processed in cloud-based autonomous database deployments.
The General Data Protection Regulation (GDPR) in the European Union sets stringent requirements for data protection, mandating explicit consent mechanisms, data minimization principles, and the right to erasure. For autonomous databases operating in cloud environments, these requirements necessitate sophisticated automated compliance monitoring systems that can track data lineage, implement privacy-by-design principles, and ensure real-time compliance verification across distributed cloud infrastructures.
In the United States, sector-specific regulations create a complex compliance matrix. The Health Insurance Portability and Accountability Act (HIPAA) governs healthcare data protection, requiring robust encryption, access controls, and audit trails for autonomous databases handling protected health information. The Gramm-Leach-Bliley Act (GLBA) imposes similar requirements for financial institutions, while the California Consumer Privacy Act (CCPA) introduces consumer rights that autonomous systems must automatically enforce.
Cross-border data transfer regulations present particular challenges for cloud-deployed autonomous databases. The EU-US Data Privacy Framework, Schrems II decision implications, and various adequacy decisions create a patchwork of requirements that autonomous systems must navigate. These frameworks require dynamic policy enforcement capabilities that can adapt to changing regulatory interpretations and geographic data residency requirements.
Emerging regulations in Asia-Pacific regions, including China's Personal Information Protection Law (PIPL) and India's proposed Data Protection Bill, introduce additional compliance layers. These regulations often emphasize data localization requirements and government access provisions that autonomous database systems must accommodate through intelligent data placement and sovereignty controls.
The convergence of these regulatory frameworks demands autonomous databases implement comprehensive compliance orchestration capabilities, including automated policy translation, real-time regulatory change detection, and adaptive security posture management to maintain continuous compliance across multiple jurisdictions simultaneously.
The General Data Protection Regulation (GDPR) in the European Union sets stringent requirements for data protection, mandating explicit consent mechanisms, data minimization principles, and the right to erasure. For autonomous databases operating in cloud environments, these requirements necessitate sophisticated automated compliance monitoring systems that can track data lineage, implement privacy-by-design principles, and ensure real-time compliance verification across distributed cloud infrastructures.
In the United States, sector-specific regulations create a complex compliance matrix. The Health Insurance Portability and Accountability Act (HIPAA) governs healthcare data protection, requiring robust encryption, access controls, and audit trails for autonomous databases handling protected health information. The Gramm-Leach-Bliley Act (GLBA) imposes similar requirements for financial institutions, while the California Consumer Privacy Act (CCPA) introduces consumer rights that autonomous systems must automatically enforce.
Cross-border data transfer regulations present particular challenges for cloud-deployed autonomous databases. The EU-US Data Privacy Framework, Schrems II decision implications, and various adequacy decisions create a patchwork of requirements that autonomous systems must navigate. These frameworks require dynamic policy enforcement capabilities that can adapt to changing regulatory interpretations and geographic data residency requirements.
Emerging regulations in Asia-Pacific regions, including China's Personal Information Protection Law (PIPL) and India's proposed Data Protection Bill, introduce additional compliance layers. These regulations often emphasize data localization requirements and government access provisions that autonomous database systems must accommodate through intelligent data placement and sovereignty controls.
The convergence of these regulatory frameworks demands autonomous databases implement comprehensive compliance orchestration capabilities, including automated policy translation, real-time regulatory change detection, and adaptive security posture management to maintain continuous compliance across multiple jurisdictions simultaneously.
Privacy and Trust Considerations in Autonomous Systems
Privacy considerations in autonomous database systems operating within cloud environments represent a fundamental challenge that extends beyond traditional data protection mechanisms. The autonomous nature of these systems introduces unique privacy risks, as machine learning algorithms continuously analyze data patterns, user behaviors, and system performance metrics to optimize operations. This constant data processing creates potential exposure points where sensitive information could be inadvertently accessed, analyzed, or retained longer than necessary for operational purposes.
The multi-tenancy architecture inherent in cloud environments amplifies privacy concerns for autonomous databases. While logical separation mechanisms exist, the shared infrastructure model means that tenant data may reside on the same physical hardware, creating potential cross-contamination risks. Autonomous systems must implement sophisticated privacy-preserving techniques such as differential privacy, homomorphic encryption, and secure multi-party computation to ensure that optimization algorithms can function effectively without compromising individual data privacy or revealing sensitive patterns across tenant boundaries.
Trust establishment in autonomous database systems requires a paradigm shift from traditional security models that rely heavily on human oversight and intervention. Users must develop confidence in automated decision-making processes that govern data access, query optimization, and security policy enforcement. This trust framework necessitates transparent algorithmic governance, where the decision-making logic of autonomous systems can be audited and validated without exposing proprietary optimization techniques or creating security vulnerabilities.
The dynamic nature of autonomous systems presents ongoing trust challenges, as these systems continuously evolve their behavior based on learned patterns and environmental changes. Establishing verifiable trust requires implementing immutable audit trails, behavioral consistency monitoring, and explainable AI mechanisms that can provide clear justifications for autonomous decisions. Additionally, trust models must account for the distributed nature of cloud environments, where autonomous database components may span multiple geographic regions with varying regulatory requirements and security standards.
Regulatory compliance adds another layer of complexity to privacy and trust considerations, as autonomous systems must navigate evolving data protection regulations while maintaining operational efficiency. The systems must be capable of automatically adapting to new privacy requirements, implementing data residency controls, and providing granular consent management capabilities that align with regional privacy laws without requiring constant human intervention.
The multi-tenancy architecture inherent in cloud environments amplifies privacy concerns for autonomous databases. While logical separation mechanisms exist, the shared infrastructure model means that tenant data may reside on the same physical hardware, creating potential cross-contamination risks. Autonomous systems must implement sophisticated privacy-preserving techniques such as differential privacy, homomorphic encryption, and secure multi-party computation to ensure that optimization algorithms can function effectively without compromising individual data privacy or revealing sensitive patterns across tenant boundaries.
Trust establishment in autonomous database systems requires a paradigm shift from traditional security models that rely heavily on human oversight and intervention. Users must develop confidence in automated decision-making processes that govern data access, query optimization, and security policy enforcement. This trust framework necessitates transparent algorithmic governance, where the decision-making logic of autonomous systems can be audited and validated without exposing proprietary optimization techniques or creating security vulnerabilities.
The dynamic nature of autonomous systems presents ongoing trust challenges, as these systems continuously evolve their behavior based on learned patterns and environmental changes. Establishing verifiable trust requires implementing immutable audit trails, behavioral consistency monitoring, and explainable AI mechanisms that can provide clear justifications for autonomous decisions. Additionally, trust models must account for the distributed nature of cloud environments, where autonomous database components may span multiple geographic regions with varying regulatory requirements and security standards.
Regulatory compliance adds another layer of complexity to privacy and trust considerations, as autonomous systems must navigate evolving data protection regulations while maintaining operational efficiency. The systems must be capable of automatically adapting to new privacy requirements, implementing data residency controls, and providing granular consent management capabilities that align with regional privacy laws without requiring constant human intervention.
Unlock deeper insights with PatSnap Eureka Quick Research — get a full tech report to explore trends and direct your research. Try now!
Generate Your Research Report Instantly with AI Agent
Supercharge your innovation with PatSnap Eureka AI Agent Platform!