Smart Factory Data Privacy: Ensuring Compliance
MAR 19, 20269 MIN READ
Generate Your Research Report Instantly with AI Agent
PatSnap Eureka helps you evaluate technical feasibility & market potential.
Smart Factory Data Privacy Background and Compliance Goals
The evolution of smart manufacturing has fundamentally transformed industrial operations, creating interconnected ecosystems where operational technology converges with information technology. This digital transformation has enabled unprecedented levels of automation, real-time monitoring, and data-driven decision making across manufacturing processes. However, this technological advancement has simultaneously introduced complex data privacy challenges that require comprehensive regulatory compliance frameworks.
Smart factories generate vast quantities of sensitive data encompassing production parameters, quality metrics, supply chain information, employee performance data, and proprietary manufacturing processes. The interconnected nature of Industrial Internet of Things devices, edge computing systems, and cloud-based analytics platforms creates multiple data touchpoints that must be secured and managed in accordance with evolving privacy regulations.
The regulatory landscape governing industrial data privacy has become increasingly stringent, with frameworks such as the General Data Protection Regulation in Europe, the California Consumer Privacy Act in the United States, and emerging sector-specific regulations worldwide. These regulations impose strict requirements for data collection, processing, storage, and sharing, with significant financial penalties for non-compliance that can reach millions of dollars.
Manufacturing organizations face the dual challenge of maintaining operational efficiency while ensuring comprehensive data protection. The complexity increases when considering cross-border data transfers, third-party vendor relationships, and the integration of legacy systems with modern digital infrastructure. Traditional manufacturing environments were not designed with privacy-by-design principles, creating inherent vulnerabilities in data handling processes.
The primary compliance goals for smart factory data privacy encompass establishing robust data governance frameworks, implementing privacy-preserving technologies, ensuring transparent data processing practices, and maintaining continuous compliance monitoring. Organizations must develop comprehensive data mapping capabilities to understand information flows across their manufacturing ecosystems, from sensor data collection through analytics processing to long-term storage and eventual deletion.
Achieving compliance requires balancing operational requirements with privacy obligations, implementing technical safeguards such as encryption and access controls, establishing clear data retention policies, and ensuring employee training on privacy best practices. The ultimate objective is creating a manufacturing environment where data-driven innovation can flourish while maintaining the highest standards of privacy protection and regulatory compliance.
Smart factories generate vast quantities of sensitive data encompassing production parameters, quality metrics, supply chain information, employee performance data, and proprietary manufacturing processes. The interconnected nature of Industrial Internet of Things devices, edge computing systems, and cloud-based analytics platforms creates multiple data touchpoints that must be secured and managed in accordance with evolving privacy regulations.
The regulatory landscape governing industrial data privacy has become increasingly stringent, with frameworks such as the General Data Protection Regulation in Europe, the California Consumer Privacy Act in the United States, and emerging sector-specific regulations worldwide. These regulations impose strict requirements for data collection, processing, storage, and sharing, with significant financial penalties for non-compliance that can reach millions of dollars.
Manufacturing organizations face the dual challenge of maintaining operational efficiency while ensuring comprehensive data protection. The complexity increases when considering cross-border data transfers, third-party vendor relationships, and the integration of legacy systems with modern digital infrastructure. Traditional manufacturing environments were not designed with privacy-by-design principles, creating inherent vulnerabilities in data handling processes.
The primary compliance goals for smart factory data privacy encompass establishing robust data governance frameworks, implementing privacy-preserving technologies, ensuring transparent data processing practices, and maintaining continuous compliance monitoring. Organizations must develop comprehensive data mapping capabilities to understand information flows across their manufacturing ecosystems, from sensor data collection through analytics processing to long-term storage and eventual deletion.
Achieving compliance requires balancing operational requirements with privacy obligations, implementing technical safeguards such as encryption and access controls, establishing clear data retention policies, and ensuring employee training on privacy best practices. The ultimate objective is creating a manufacturing environment where data-driven innovation can flourish while maintaining the highest standards of privacy protection and regulatory compliance.
Market Demand for Secure Industrial Data Management
The global industrial sector is experiencing unprecedented digital transformation, driving substantial demand for secure industrial data management solutions. Manufacturing enterprises are increasingly adopting Industry 4.0 technologies, including IoT sensors, edge computing devices, and cloud-based analytics platforms, which generate massive volumes of sensitive operational data requiring robust protection mechanisms.
Regulatory compliance requirements are intensifying across major industrial markets. The European Union's General Data Protection Regulation (GDPR) and emerging cybersecurity frameworks in North America and Asia-Pacific regions mandate strict data handling protocols for industrial operations. These regulations create mandatory market demand for comprehensive data privacy solutions that can ensure continuous compliance while maintaining operational efficiency.
Smart factory implementations are proliferating across automotive, pharmaceutical, electronics, and chemical manufacturing sectors. These facilities generate critical intellectual property data, production parameters, quality metrics, and supply chain information that require sophisticated protection against both external cyber threats and internal data breaches. The convergence of operational technology and information technology networks amplifies security vulnerabilities, necessitating specialized industrial data management platforms.
Market drivers include increasing cyber attack frequency targeting industrial infrastructure, rising costs of data breaches in manufacturing environments, and growing awareness of competitive intelligence risks. Industrial espionage concerns are particularly acute in high-value manufacturing sectors where proprietary processes and product designs represent significant competitive advantages.
Enterprise buyers are seeking integrated solutions that combine real-time data encryption, access control mechanisms, audit trail capabilities, and automated compliance reporting features. The demand extends beyond basic cybersecurity to encompass comprehensive data governance frameworks that can adapt to evolving regulatory landscapes while supporting operational scalability.
Supply chain digitization initiatives further expand market opportunities, as manufacturers require secure data sharing capabilities with suppliers, distributors, and logistics partners. Cross-border manufacturing operations face complex multi-jurisdictional compliance requirements, creating demand for flexible data localization and sovereignty management solutions.
The market demonstrates strong growth momentum driven by mandatory regulatory compliance timelines, increasing insurance requirements for cybersecurity coverage, and competitive pressures to maintain customer trust through demonstrated data protection capabilities.
Regulatory compliance requirements are intensifying across major industrial markets. The European Union's General Data Protection Regulation (GDPR) and emerging cybersecurity frameworks in North America and Asia-Pacific regions mandate strict data handling protocols for industrial operations. These regulations create mandatory market demand for comprehensive data privacy solutions that can ensure continuous compliance while maintaining operational efficiency.
Smart factory implementations are proliferating across automotive, pharmaceutical, electronics, and chemical manufacturing sectors. These facilities generate critical intellectual property data, production parameters, quality metrics, and supply chain information that require sophisticated protection against both external cyber threats and internal data breaches. The convergence of operational technology and information technology networks amplifies security vulnerabilities, necessitating specialized industrial data management platforms.
Market drivers include increasing cyber attack frequency targeting industrial infrastructure, rising costs of data breaches in manufacturing environments, and growing awareness of competitive intelligence risks. Industrial espionage concerns are particularly acute in high-value manufacturing sectors where proprietary processes and product designs represent significant competitive advantages.
Enterprise buyers are seeking integrated solutions that combine real-time data encryption, access control mechanisms, audit trail capabilities, and automated compliance reporting features. The demand extends beyond basic cybersecurity to encompass comprehensive data governance frameworks that can adapt to evolving regulatory landscapes while supporting operational scalability.
Supply chain digitization initiatives further expand market opportunities, as manufacturers require secure data sharing capabilities with suppliers, distributors, and logistics partners. Cross-border manufacturing operations face complex multi-jurisdictional compliance requirements, creating demand for flexible data localization and sovereignty management solutions.
The market demonstrates strong growth momentum driven by mandatory regulatory compliance timelines, increasing insurance requirements for cybersecurity coverage, and competitive pressures to maintain customer trust through demonstrated data protection capabilities.
Current Privacy Challenges in Smart Manufacturing Systems
Smart manufacturing systems face unprecedented data privacy challenges as they integrate advanced IoT sensors, artificial intelligence, and cloud computing technologies. The interconnected nature of these systems creates multiple vulnerability points where sensitive manufacturing data, intellectual property, and operational information can be compromised. Traditional cybersecurity measures often prove inadequate against sophisticated attacks targeting industrial control systems and manufacturing execution systems.
Data collection and storage present significant privacy risks in smart factories. Manufacturing systems continuously generate vast amounts of data including production parameters, quality metrics, supply chain information, and employee performance data. This information often contains proprietary manufacturing processes, customer specifications, and competitive intelligence that requires stringent protection. The challenge intensifies when considering cross-border data transfers and varying international privacy regulations.
Regulatory compliance complexity represents another major challenge facing smart manufacturing organizations. The General Data Protection Regulation (GDPR) in Europe, California Consumer Privacy Act (CCPA), and emerging privacy laws in Asia create a complex web of requirements that manufacturers must navigate. These regulations often conflict with operational needs for real-time data sharing and analytics, forcing organizations to balance compliance requirements with manufacturing efficiency.
Third-party integration vulnerabilities pose substantial risks to manufacturing data privacy. Smart factories typically rely on multiple vendors for equipment, software, and services, creating numerous potential entry points for data breaches. Supplier networks, cloud service providers, and technology partners may have varying levels of security maturity, making it difficult to maintain consistent privacy protection across the entire manufacturing ecosystem.
Legacy system integration challenges compound privacy risks in smart manufacturing environments. Many factories operate hybrid systems combining modern IoT devices with decades-old industrial equipment that lacks built-in security features. These legacy systems often cannot support modern encryption protocols or access controls, creating weak links in the overall privacy protection framework.
Real-time operational requirements conflict with privacy protection measures in many manufacturing scenarios. Production systems demand immediate data access and processing to maintain efficiency and quality standards. However, implementing comprehensive privacy controls, data anonymization, and access restrictions can introduce latency that disrupts critical manufacturing processes, forcing organizations to make difficult trade-offs between privacy and operational performance.
Data collection and storage present significant privacy risks in smart factories. Manufacturing systems continuously generate vast amounts of data including production parameters, quality metrics, supply chain information, and employee performance data. This information often contains proprietary manufacturing processes, customer specifications, and competitive intelligence that requires stringent protection. The challenge intensifies when considering cross-border data transfers and varying international privacy regulations.
Regulatory compliance complexity represents another major challenge facing smart manufacturing organizations. The General Data Protection Regulation (GDPR) in Europe, California Consumer Privacy Act (CCPA), and emerging privacy laws in Asia create a complex web of requirements that manufacturers must navigate. These regulations often conflict with operational needs for real-time data sharing and analytics, forcing organizations to balance compliance requirements with manufacturing efficiency.
Third-party integration vulnerabilities pose substantial risks to manufacturing data privacy. Smart factories typically rely on multiple vendors for equipment, software, and services, creating numerous potential entry points for data breaches. Supplier networks, cloud service providers, and technology partners may have varying levels of security maturity, making it difficult to maintain consistent privacy protection across the entire manufacturing ecosystem.
Legacy system integration challenges compound privacy risks in smart manufacturing environments. Many factories operate hybrid systems combining modern IoT devices with decades-old industrial equipment that lacks built-in security features. These legacy systems often cannot support modern encryption protocols or access controls, creating weak links in the overall privacy protection framework.
Real-time operational requirements conflict with privacy protection measures in many manufacturing scenarios. Production systems demand immediate data access and processing to maintain efficiency and quality standards. However, implementing comprehensive privacy controls, data anonymization, and access restrictions can introduce latency that disrupts critical manufacturing processes, forcing organizations to make difficult trade-offs between privacy and operational performance.
Existing Data Privacy Protection Frameworks
01 Data encryption and secure communication protocols in smart factories
Implementation of encryption technologies and secure communication protocols to protect sensitive manufacturing data during transmission and storage. This includes end-to-end encryption, secure data channels, and cryptographic methods to ensure data confidentiality and integrity in industrial IoT environments. These technologies prevent unauthorized access and data breaches while maintaining compliance with privacy regulations.- Data encryption and secure communication protocols in smart factories: Implementation of encryption technologies and secure communication protocols to protect sensitive manufacturing data during transmission and storage within smart factory environments. These methods ensure that data exchanged between machines, sensors, and control systems remains confidential and protected from unauthorized access. Advanced cryptographic techniques are employed to safeguard industrial data against cyber threats while maintaining operational efficiency.
- Access control and authentication systems for industrial data: Deployment of robust access control mechanisms and multi-factor authentication systems to regulate who can access sensitive manufacturing data and operational systems. These solutions implement role-based permissions, user verification protocols, and identity management systems specifically designed for industrial environments. The technologies ensure that only authorized personnel can access critical production data and control systems.
- Privacy-preserving data analytics and anonymization techniques: Application of data anonymization and privacy-preserving analytics methods that allow smart factories to derive insights from operational data while protecting individual privacy and proprietary information. These techniques enable statistical analysis and machine learning applications without exposing sensitive details. Methods include differential privacy, data masking, and aggregation strategies tailored for industrial datasets.
- Compliance monitoring and audit trail systems: Implementation of automated compliance monitoring systems that track data handling practices and maintain comprehensive audit trails for regulatory purposes. These systems continuously monitor data flows, access patterns, and processing activities to ensure adherence to privacy regulations. They generate detailed logs and reports that demonstrate compliance with data protection standards and facilitate regulatory audits.
- Data governance frameworks and policy enforcement: Establishment of comprehensive data governance frameworks that define policies, procedures, and technical controls for managing sensitive information throughout its lifecycle in smart factory environments. These frameworks include automated policy enforcement mechanisms, data classification systems, and retention management tools. They ensure consistent application of privacy principles across all manufacturing operations and data processing activities.
02 Access control and authentication systems for industrial data
Advanced access control mechanisms and multi-factor authentication systems designed specifically for smart factory environments. These systems manage user permissions, role-based access controls, and identity verification to ensure only authorized personnel can access sensitive manufacturing data. The solutions include biometric authentication, token-based systems, and hierarchical access management to maintain data privacy compliance.Expand Specific Solutions03 Privacy-preserving data analytics and monitoring
Technologies that enable data analysis and monitoring in smart factories while preserving privacy through anonymization, pseudonymization, and differential privacy techniques. These methods allow manufacturers to extract valuable insights from operational data without exposing personally identifiable information or proprietary manufacturing processes, ensuring compliance with data protection regulations.Expand Specific Solutions04 Compliance management and audit trail systems
Automated compliance management frameworks and comprehensive audit trail systems that track data access, modifications, and usage patterns in smart factory environments. These systems provide real-time monitoring, automated reporting, and documentation capabilities to demonstrate adherence to privacy regulations. They include logging mechanisms, compliance dashboards, and automated alert systems for potential violations.Expand Specific Solutions05 Data governance and policy enforcement frameworks
Comprehensive data governance frameworks that establish policies, procedures, and technical controls for managing data privacy in smart manufacturing environments. These frameworks include automated policy enforcement, data classification systems, retention management, and consent management mechanisms. They ensure consistent application of privacy rules across distributed factory systems and provide mechanisms for data subject rights management.Expand Specific Solutions
Key Players in Smart Factory Security Solutions
The smart factory data privacy compliance landscape represents a rapidly evolving market driven by increasing regulatory requirements and digital transformation initiatives. The industry is in a growth phase, with market expansion fueled by GDPR, CCPA, and emerging data protection regulations. Technology maturity varies significantly across segments, with established players like IBM, Salesforce, and Thales offering comprehensive enterprise solutions, while specialized privacy-focused companies such as OneTrust and TerraTrue provide targeted compliance platforms. Industrial automation leaders including Mitsubishi Electric, Baker Hughes, and Rosemount integrate privacy-by-design into manufacturing systems. The competitive landscape spans traditional tech giants, emerging privacy specialists, and industrial equipment manufacturers, indicating a fragmented but rapidly consolidating market where cross-industry collaboration is essential for comprehensive smart factory data protection solutions.
OneTrust LLC
Technical Solution: OneTrust provides a comprehensive privacy management platform specifically designed for smart factory environments. Their solution includes automated data discovery and classification capabilities that can identify and categorize sensitive manufacturing data across IoT devices, sensors, and production systems. The platform offers real-time privacy impact assessments for smart factory operations, ensuring GDPR, CCPA, and industry-specific compliance requirements are met. Their technology features automated consent management for worker data collection, third-party vendor privacy risk assessments, and incident response workflows tailored for manufacturing environments. The solution integrates with existing manufacturing execution systems (MES) and enterprise resource planning (ERP) systems to provide seamless privacy governance without disrupting production workflows.
Strengths: Market-leading privacy management platform with extensive compliance framework coverage and strong integration capabilities. Weaknesses: High implementation costs and complexity may challenge smaller manufacturing operations.
International Business Machines Corp.
Technical Solution: IBM offers Watson IoT Platform with integrated privacy and security features specifically designed for smart manufacturing environments. Their solution combines artificial intelligence-driven data classification with blockchain-based data provenance tracking to ensure manufacturing data privacy and compliance. The platform includes automated privacy policy enforcement, real-time monitoring of data flows across factory networks, and intelligent anonymization techniques for sensitive production data. IBM's approach leverages federated learning capabilities to enable collaborative manufacturing insights while maintaining data locality and privacy. Their solution provides comprehensive audit trails, automated compliance reporting, and integration with major industrial protocols like OPC-UA and MQTT while ensuring end-to-end encryption and access controls.
Strengths: Robust AI-powered privacy solutions with strong enterprise integration and comprehensive audit capabilities. Weaknesses: Complex implementation requiring significant technical expertise and substantial infrastructure investment.
Core Innovations in Industrial Data Encryption
Integrity and Privacy-Preserving Federated Learning in a Smart Factory Using Smart Contracts and Merkle Tree-Based Key Management
PatentPendingUS20250062896A1
Innovation
- The integration of smart contracts in blockchain and Merkle Tree-based key management operations provides a system for ensuring integrity and privacy-preserving communication in smart factories. This system encrypts data before transmission, splits keys into parts for secure sharing, and uses blockchain to validate transactions, ensuring that no single point of failure can compromise the system.
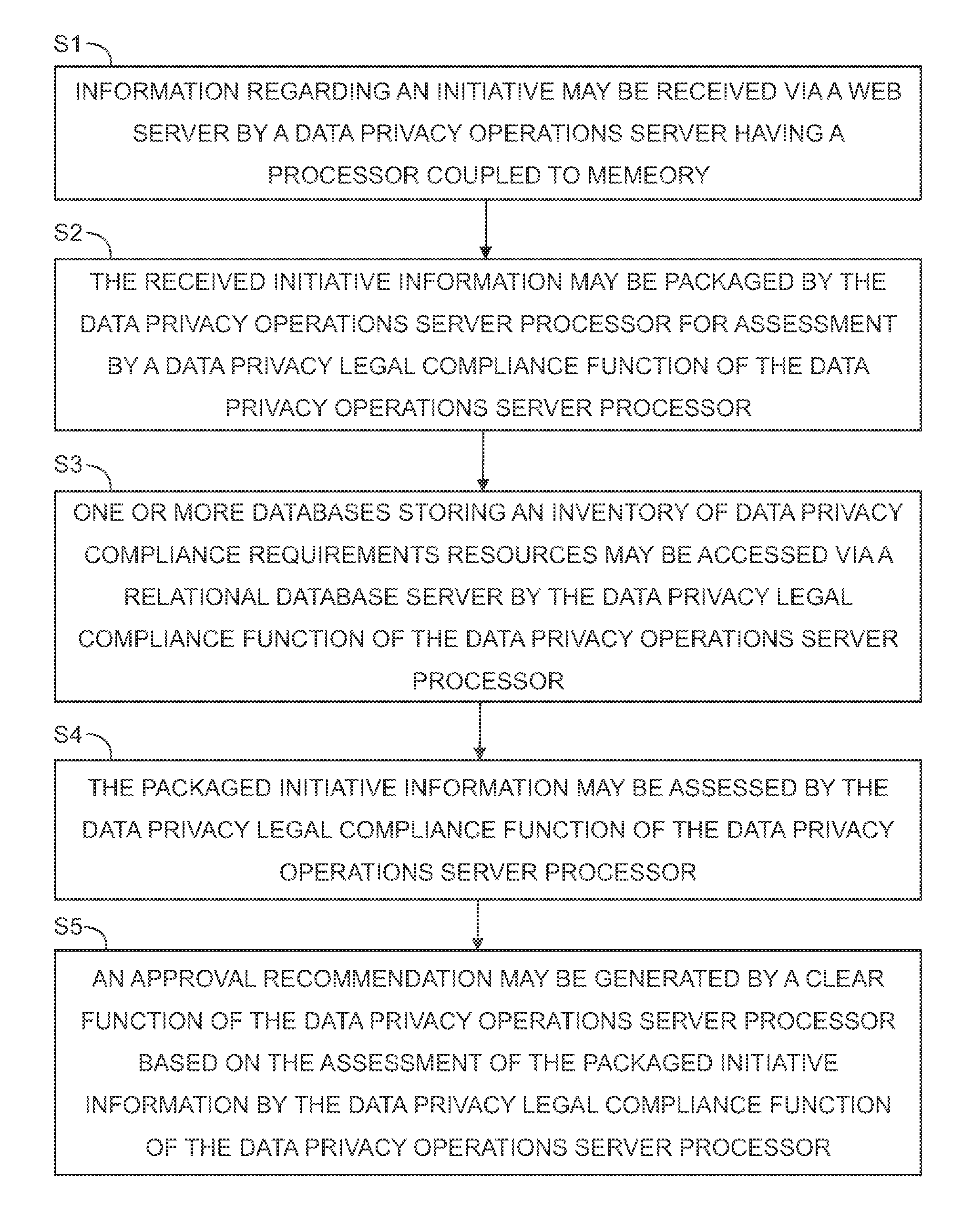
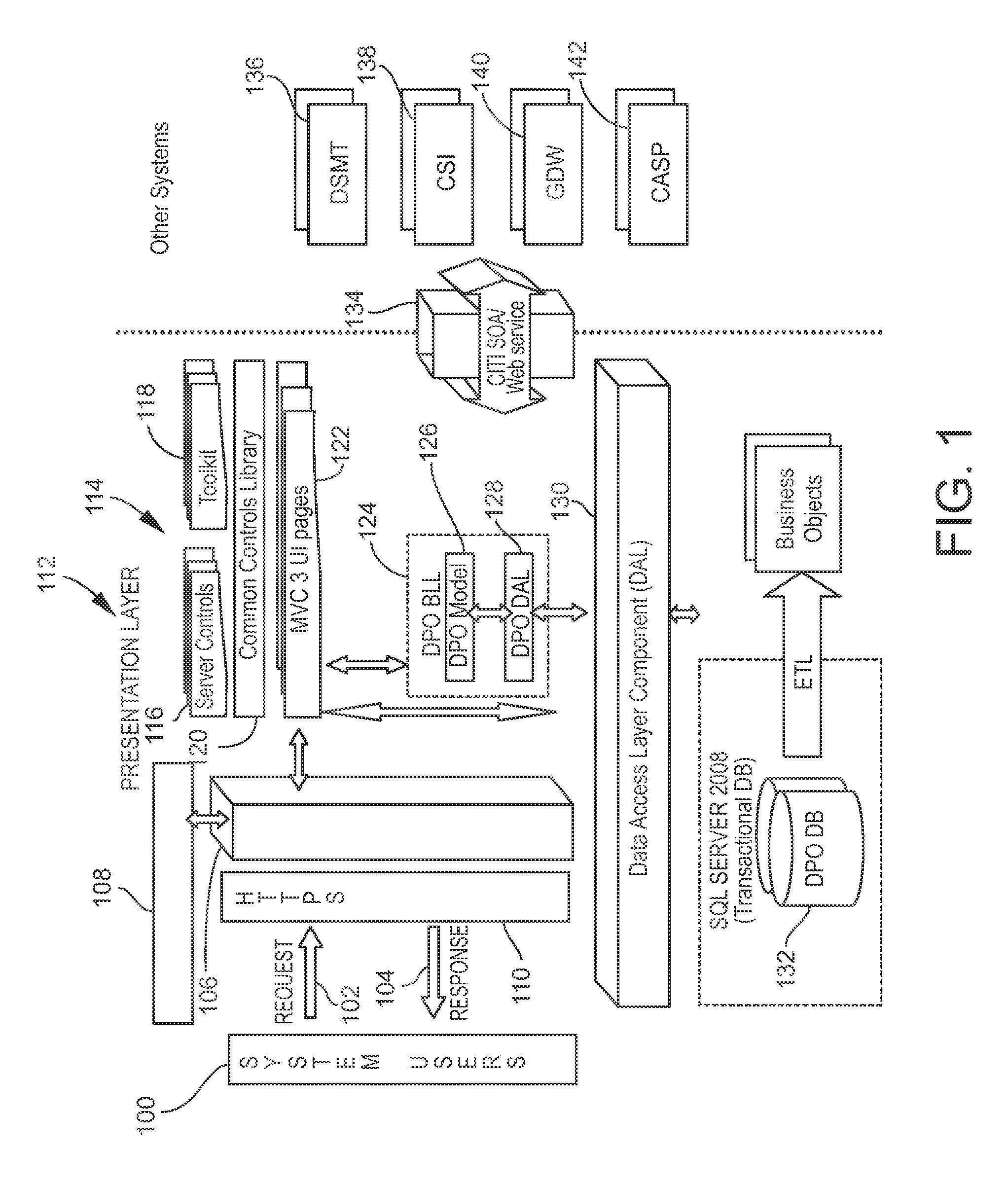
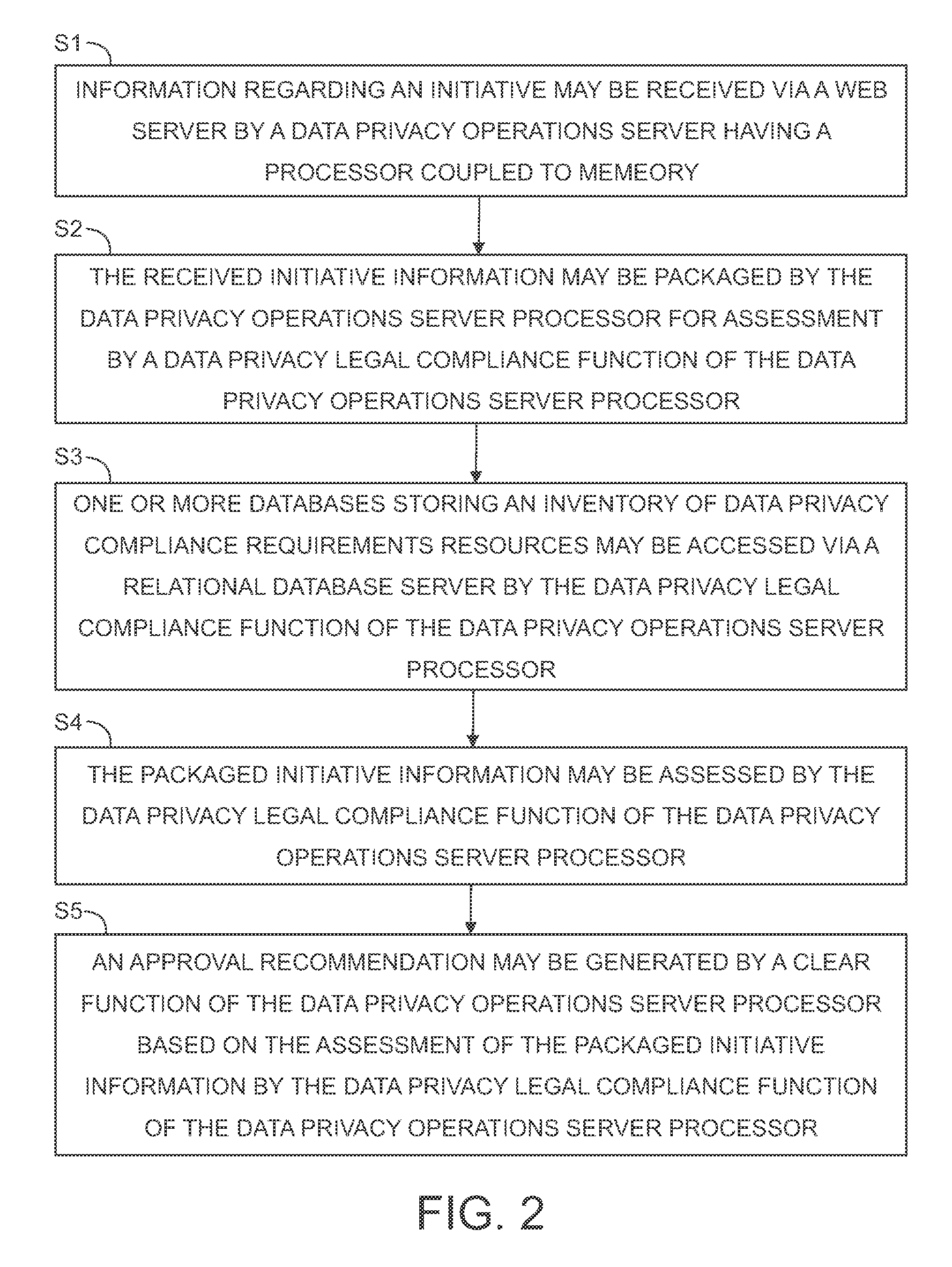
Systems and methods for automated data privacy compliance
PatentActiveUS9507960B2
Innovation
- A system utilizing a data privacy operations server with a processor and memory, coupled with a user interface and database, assesses compliance requirements for multiple countries, generating approval recommendations through a workflow engine and relational database access, ensuring adherence to data privacy laws.
Regulatory Framework for Industrial Data Compliance
The regulatory framework for industrial data compliance in smart factories operates within a complex multi-jurisdictional environment where various data protection laws intersect with industrial standards. The European Union's General Data Protection Regulation (GDPR) serves as the foundational framework, establishing strict requirements for personal data processing, consent mechanisms, and breach notification protocols. This regulation significantly impacts smart factory operations that collect worker biometric data, location tracking information, and behavioral analytics.
In the United States, the regulatory landscape is more fragmented, with sector-specific regulations such as the Health Insurance Portability and Accountability Act (HIPAA) for health-related data and the California Consumer Privacy Act (CCPA) providing state-level protection. The Federal Trade Commission (FTC) also plays a crucial role in enforcing data security standards through its authority over unfair and deceptive practices in commerce.
Industrial-specific regulations add another layer of complexity to compliance requirements. The International Organization for Standardization (ISO) 27001 standard provides a comprehensive framework for information security management systems, while IEC 62443 specifically addresses cybersecurity for industrial automation and control systems. These standards establish technical safeguards and operational procedures that smart factories must implement to protect sensitive industrial data.
Emerging regulations are increasingly focusing on cross-border data transfers and data localization requirements. China's Cybersecurity Law and Data Security Law impose strict controls on data processing and cross-border transfers, requiring companies to conduct security assessments and obtain regulatory approval for certain data transfers. Similarly, Russia's data localization laws mandate that personal data of Russian citizens be stored within the country's borders.
The regulatory framework also encompasses industry-specific compliance requirements such as the Sarbanes-Oxley Act for publicly traded companies, which mandates strict internal controls over financial reporting systems. For smart factories in regulated industries like pharmaceuticals or aerospace, additional compliance frameworks such as FDA 21 CFR Part 11 or ITAR regulations may apply, creating overlapping compliance obligations that require careful coordination and comprehensive data governance strategies.
In the United States, the regulatory landscape is more fragmented, with sector-specific regulations such as the Health Insurance Portability and Accountability Act (HIPAA) for health-related data and the California Consumer Privacy Act (CCPA) providing state-level protection. The Federal Trade Commission (FTC) also plays a crucial role in enforcing data security standards through its authority over unfair and deceptive practices in commerce.
Industrial-specific regulations add another layer of complexity to compliance requirements. The International Organization for Standardization (ISO) 27001 standard provides a comprehensive framework for information security management systems, while IEC 62443 specifically addresses cybersecurity for industrial automation and control systems. These standards establish technical safeguards and operational procedures that smart factories must implement to protect sensitive industrial data.
Emerging regulations are increasingly focusing on cross-border data transfers and data localization requirements. China's Cybersecurity Law and Data Security Law impose strict controls on data processing and cross-border transfers, requiring companies to conduct security assessments and obtain regulatory approval for certain data transfers. Similarly, Russia's data localization laws mandate that personal data of Russian citizens be stored within the country's borders.
The regulatory framework also encompasses industry-specific compliance requirements such as the Sarbanes-Oxley Act for publicly traded companies, which mandates strict internal controls over financial reporting systems. For smart factories in regulated industries like pharmaceuticals or aerospace, additional compliance frameworks such as FDA 21 CFR Part 11 or ITAR regulations may apply, creating overlapping compliance obligations that require careful coordination and comprehensive data governance strategies.
Risk Assessment in Smart Factory Data Governance
Risk assessment in smart factory data governance represents a critical systematic process for identifying, evaluating, and mitigating potential threats to data privacy and regulatory compliance. This comprehensive approach encompasses multiple risk categories including data breach vulnerabilities, unauthorized access scenarios, regulatory non-compliance penalties, and operational disruptions stemming from privacy violations.
The primary risk vectors in smart factory environments stem from the interconnected nature of Industrial Internet of Things (IIoT) devices, which create numerous potential entry points for malicious actors. Network segmentation failures, inadequate encryption protocols, and insufficient access controls constitute the most prevalent technical risks. Additionally, human factors such as inadequate training, social engineering attacks, and insider threats significantly amplify the overall risk profile.
Regulatory compliance risks vary substantially across different jurisdictions, with GDPR in Europe, CCPA in California, and emerging data protection laws in Asia creating complex compliance matrices. Non-compliance penalties can reach up to 4% of annual global turnover under GDPR, making regulatory risk assessment a business-critical function. The dynamic nature of regulatory landscapes requires continuous monitoring and adaptive risk assessment methodologies.
Operational risks include production line disruptions caused by security incidents, intellectual property theft, and supply chain vulnerabilities. Smart factories often integrate third-party systems and cloud services, introducing additional risk dimensions that require careful evaluation. Data residency requirements and cross-border data transfer restrictions further complicate the risk landscape.
Risk assessment frameworks typically employ quantitative and qualitative methodologies, utilizing risk matrices that consider probability and impact factors. Advanced approaches incorporate machine learning algorithms to identify anomalous patterns and predict potential risk scenarios. Regular penetration testing, vulnerability assessments, and compliance audits form essential components of comprehensive risk evaluation strategies.
The assessment process must account for emerging threats such as AI-powered attacks, quantum computing implications for current encryption standards, and evolving regulatory requirements. Continuous risk monitoring systems enable real-time threat detection and automated response mechanisms, ensuring that risk mitigation strategies remain effective against evolving threat landscapes in smart factory environments.
The primary risk vectors in smart factory environments stem from the interconnected nature of Industrial Internet of Things (IIoT) devices, which create numerous potential entry points for malicious actors. Network segmentation failures, inadequate encryption protocols, and insufficient access controls constitute the most prevalent technical risks. Additionally, human factors such as inadequate training, social engineering attacks, and insider threats significantly amplify the overall risk profile.
Regulatory compliance risks vary substantially across different jurisdictions, with GDPR in Europe, CCPA in California, and emerging data protection laws in Asia creating complex compliance matrices. Non-compliance penalties can reach up to 4% of annual global turnover under GDPR, making regulatory risk assessment a business-critical function. The dynamic nature of regulatory landscapes requires continuous monitoring and adaptive risk assessment methodologies.
Operational risks include production line disruptions caused by security incidents, intellectual property theft, and supply chain vulnerabilities. Smart factories often integrate third-party systems and cloud services, introducing additional risk dimensions that require careful evaluation. Data residency requirements and cross-border data transfer restrictions further complicate the risk landscape.
Risk assessment frameworks typically employ quantitative and qualitative methodologies, utilizing risk matrices that consider probability and impact factors. Advanced approaches incorporate machine learning algorithms to identify anomalous patterns and predict potential risk scenarios. Regular penetration testing, vulnerability assessments, and compliance audits form essential components of comprehensive risk evaluation strategies.
The assessment process must account for emerging threats such as AI-powered attacks, quantum computing implications for current encryption standards, and evolving regulatory requirements. Continuous risk monitoring systems enable real-time threat detection and automated response mechanisms, ensuring that risk mitigation strategies remain effective against evolving threat landscapes in smart factory environments.
Unlock deeper insights with PatSnap Eureka Quick Research — get a full tech report to explore trends and direct your research. Try now!
Generate Your Research Report Instantly with AI Agent
Supercharge your innovation with PatSnap Eureka AI Agent Platform!