Comparing PCM to Advanced Encryption Standards in Security
MAR 6, 20269 MIN READ
Generate Your Research Report Instantly with AI Agent
PatSnap Eureka helps you evaluate technical feasibility & market potential.
PCM vs AES Security Background and Objectives
The evolution of data security technologies has been fundamentally shaped by the perpetual arms race between protection mechanisms and attack methodologies. Traditional cryptographic approaches, exemplified by the Advanced Encryption Standard (AES), have dominated the security landscape for decades through mathematical complexity and computational barriers. However, emerging hardware-based security paradigms, particularly Phase Change Memory (PCM) technologies, are introducing novel approaches to data protection that challenge conventional encryption methodologies.
AES represents the culmination of symmetric encryption evolution, establishing itself as the global standard through rigorous cryptanalytic testing and widespread adoption across industries. Its mathematical foundation relies on substitution-permutation networks that transform plaintext through multiple rounds of complex operations, creating computational barriers that remain formidable against current attack vectors. The standard has demonstrated remarkable resilience, with its 128-bit, 192-bit, and 256-bit variants providing scalable security levels appropriate for diverse application requirements.
PCM technology introduces a fundamentally different security paradigm by leveraging physical properties of chalcogenide materials that can exist in crystalline and amorphous states. This hardware-based approach embeds security directly into the storage medium itself, creating inherent protection mechanisms that operate independently of software-layer encryption. The technology's unique characteristics include resistance to traditional memory forensics, inherent data volatility under specific conditions, and the ability to implement physical unclonable functions.
The convergence of these technologies represents a critical inflection point in security architecture design. While AES continues to provide robust mathematical security guarantees, PCM offers complementary physical security properties that address vulnerabilities in the hardware-software interface. Understanding the comparative strengths, limitations, and synergistic potential of these approaches becomes essential for developing next-generation security frameworks.
The primary objective of this comparative analysis centers on evaluating the security efficacy, implementation complexity, performance implications, and practical deployment considerations of PCM-based security mechanisms against established AES implementations. This evaluation encompasses threat model analysis, attack surface assessment, and the identification of optimal application scenarios where each technology demonstrates superior protective capabilities.
AES represents the culmination of symmetric encryption evolution, establishing itself as the global standard through rigorous cryptanalytic testing and widespread adoption across industries. Its mathematical foundation relies on substitution-permutation networks that transform plaintext through multiple rounds of complex operations, creating computational barriers that remain formidable against current attack vectors. The standard has demonstrated remarkable resilience, with its 128-bit, 192-bit, and 256-bit variants providing scalable security levels appropriate for diverse application requirements.
PCM technology introduces a fundamentally different security paradigm by leveraging physical properties of chalcogenide materials that can exist in crystalline and amorphous states. This hardware-based approach embeds security directly into the storage medium itself, creating inherent protection mechanisms that operate independently of software-layer encryption. The technology's unique characteristics include resistance to traditional memory forensics, inherent data volatility under specific conditions, and the ability to implement physical unclonable functions.
The convergence of these technologies represents a critical inflection point in security architecture design. While AES continues to provide robust mathematical security guarantees, PCM offers complementary physical security properties that address vulnerabilities in the hardware-software interface. Understanding the comparative strengths, limitations, and synergistic potential of these approaches becomes essential for developing next-generation security frameworks.
The primary objective of this comparative analysis centers on evaluating the security efficacy, implementation complexity, performance implications, and practical deployment considerations of PCM-based security mechanisms against established AES implementations. This evaluation encompasses threat model analysis, attack surface assessment, and the identification of optimal application scenarios where each technology demonstrates superior protective capabilities.
Market Demand for Advanced Cryptographic Solutions
The global cryptographic solutions market is experiencing unprecedented growth driven by escalating cybersecurity threats and stringent regulatory compliance requirements. Organizations across industries are increasingly recognizing the critical importance of robust encryption technologies to protect sensitive data, intellectual property, and customer information from sophisticated cyber attacks.
Financial services institutions represent the largest consumer segment for advanced cryptographic solutions, driven by regulatory mandates such as PCI DSS, GDPR, and emerging quantum-resistant encryption requirements. Banks and payment processors are actively seeking encryption technologies that can provide both current security assurance and future-proofing against quantum computing threats.
Healthcare organizations constitute another rapidly expanding market segment, particularly following the acceleration of digital health initiatives and telemedicine adoption. The need to secure patient data while maintaining interoperability between systems creates substantial demand for flexible encryption solutions that can balance security with operational efficiency.
Government and defense sectors continue to drive innovation in cryptographic technologies, with increasing focus on post-quantum cryptography and hardware-based security modules. These sectors often serve as early adopters for emerging encryption standards before they gain broader commercial acceptance.
The enterprise software market is witnessing growing demand for encryption solutions that can seamlessly integrate with cloud infrastructure and hybrid environments. Organizations are prioritizing solutions that offer centralized key management, automated encryption processes, and minimal performance impact on business operations.
Emerging technologies such as Internet of Things devices, autonomous vehicles, and industrial control systems are creating new market opportunities for lightweight cryptographic solutions. These applications require encryption methods that can operate within constrained computational environments while maintaining strong security guarantees.
The comparison between PCM and Advanced Encryption Standards reflects broader market trends toward evaluating encryption technologies based on performance, security strength, implementation complexity, and long-term viability. Market demand increasingly favors solutions that demonstrate clear advantages in specific use cases rather than one-size-fits-all approaches.
Financial services institutions represent the largest consumer segment for advanced cryptographic solutions, driven by regulatory mandates such as PCI DSS, GDPR, and emerging quantum-resistant encryption requirements. Banks and payment processors are actively seeking encryption technologies that can provide both current security assurance and future-proofing against quantum computing threats.
Healthcare organizations constitute another rapidly expanding market segment, particularly following the acceleration of digital health initiatives and telemedicine adoption. The need to secure patient data while maintaining interoperability between systems creates substantial demand for flexible encryption solutions that can balance security with operational efficiency.
Government and defense sectors continue to drive innovation in cryptographic technologies, with increasing focus on post-quantum cryptography and hardware-based security modules. These sectors often serve as early adopters for emerging encryption standards before they gain broader commercial acceptance.
The enterprise software market is witnessing growing demand for encryption solutions that can seamlessly integrate with cloud infrastructure and hybrid environments. Organizations are prioritizing solutions that offer centralized key management, automated encryption processes, and minimal performance impact on business operations.
Emerging technologies such as Internet of Things devices, autonomous vehicles, and industrial control systems are creating new market opportunities for lightweight cryptographic solutions. These applications require encryption methods that can operate within constrained computational environments while maintaining strong security guarantees.
The comparison between PCM and Advanced Encryption Standards reflects broader market trends toward evaluating encryption technologies based on performance, security strength, implementation complexity, and long-term viability. Market demand increasingly favors solutions that demonstrate clear advantages in specific use cases rather than one-size-fits-all approaches.
Current State of PCM and AES Implementation Challenges
Physical Unclonable Functions (PUFs) and Process Control Memory (PCM) technologies currently face significant implementation challenges in security applications when compared to established Advanced Encryption Standard (AES) protocols. The primary obstacle lies in the inherent variability and reliability issues of PCM-based security systems, which struggle to maintain consistent performance across different environmental conditions and manufacturing processes.
Contemporary PCM implementations suffer from temperature sensitivity and aging effects that can compromise cryptographic key generation and storage reliability. Unlike AES systems that operate on deterministic algorithms, PCM-based security relies on physical properties that naturally drift over time, creating authentication and encryption inconsistencies. Current error correction mechanisms add substantial overhead, often negating the performance advantages that PCM theoretically offers.
Manufacturing scalability represents another critical challenge for PCM security implementations. While AES can be deployed uniformly across diverse hardware platforms, PCM devices exhibit unique characteristics that require individual calibration and testing procedures. This variability increases production costs and complicates quality assurance processes, particularly when attempting to achieve the security certification levels required for enterprise and government applications.
Power consumption and thermal management issues further constrain PCM deployment in security-critical environments. Current PCM technologies require higher operating voltages and generate more heat during write operations compared to conventional AES implementations. These characteristics limit their applicability in mobile devices and embedded systems where energy efficiency is paramount.
Integration complexity with existing security infrastructures poses additional implementation barriers. Most current security frameworks are optimized for software-based AES implementations, requiring significant architectural modifications to accommodate PCM-based hardware security modules. The lack of standardized interfaces and protocols for PCM security devices creates interoperability challenges that slow enterprise adoption.
Despite these challenges, recent advances in PCM materials science and circuit design show promise for addressing reliability concerns. Emerging hybrid approaches that combine PCM's inherent randomness with AES's algorithmic stability are being explored to leverage the strengths of both technologies while mitigating individual weaknesses.
Contemporary PCM implementations suffer from temperature sensitivity and aging effects that can compromise cryptographic key generation and storage reliability. Unlike AES systems that operate on deterministic algorithms, PCM-based security relies on physical properties that naturally drift over time, creating authentication and encryption inconsistencies. Current error correction mechanisms add substantial overhead, often negating the performance advantages that PCM theoretically offers.
Manufacturing scalability represents another critical challenge for PCM security implementations. While AES can be deployed uniformly across diverse hardware platforms, PCM devices exhibit unique characteristics that require individual calibration and testing procedures. This variability increases production costs and complicates quality assurance processes, particularly when attempting to achieve the security certification levels required for enterprise and government applications.
Power consumption and thermal management issues further constrain PCM deployment in security-critical environments. Current PCM technologies require higher operating voltages and generate more heat during write operations compared to conventional AES implementations. These characteristics limit their applicability in mobile devices and embedded systems where energy efficiency is paramount.
Integration complexity with existing security infrastructures poses additional implementation barriers. Most current security frameworks are optimized for software-based AES implementations, requiring significant architectural modifications to accommodate PCM-based hardware security modules. The lack of standardized interfaces and protocols for PCM security devices creates interoperability challenges that slow enterprise adoption.
Despite these challenges, recent advances in PCM materials science and circuit design show promise for addressing reliability concerns. Emerging hybrid approaches that combine PCM's inherent randomness with AES's algorithmic stability are being explored to leverage the strengths of both technologies while mitigating individual weaknesses.
Existing PCM and AES Security Implementation Solutions
01 AES encryption implementation in hardware security modules
Advanced Encryption Standard (AES) can be implemented in dedicated hardware security modules to provide robust encryption capabilities. These implementations focus on optimizing the encryption and decryption processes through specialized circuitry, ensuring high-speed data protection while maintaining security standards. Hardware-based AES implementations offer resistance against various attack vectors and provide efficient cryptographic operations for secure data storage and transmission.- AES encryption implementation in hardware security modules: Advanced Encryption Standard (AES) can be implemented in dedicated hardware security modules to provide robust encryption capabilities. These implementations focus on optimizing the encryption and decryption processes through specialized circuitry, ensuring high-speed data protection while maintaining security standards. Hardware-based AES implementations offer resistance against various attack vectors and provide efficient cryptographic operations for secure data storage and transmission.
- PCM-based secure storage and encryption key management: Phase Change Memory (PCM) technology can be utilized for secure storage of encryption keys and sensitive data. The unique physical properties of PCM enable the creation of secure storage solutions that are resistant to unauthorized access. This approach combines the non-volatile characteristics of PCM with encryption mechanisms to protect cryptographic keys and confidential information, providing enhanced security for data at rest.
- Cryptographic authentication and access control systems: Security systems can implement cryptographic authentication mechanisms combined with access control protocols to ensure authorized access to protected resources. These systems utilize encryption standards to verify user identities and manage permissions, creating multiple layers of security. The integration of authentication protocols with encryption technologies provides comprehensive protection against unauthorized access attempts and ensures data integrity.
- Secure data transmission with AES encryption protocols: Data transmission security can be enhanced through the implementation of encryption protocols based on advanced encryption standards. These protocols ensure that data remains protected during transfer across networks by applying strong encryption algorithms. The systems incorporate mechanisms for secure key exchange and encrypted communication channels, protecting against interception and tampering during data transmission.
- Integrated security architectures combining PCM and encryption: Comprehensive security architectures can integrate phase change memory technology with advanced encryption standards to create robust protection systems. These integrated solutions leverage the benefits of both technologies to provide secure storage, processing, and transmission of sensitive information. The architectures implement multiple security layers, combining hardware-based security features with cryptographic algorithms to defend against various security threats.
02 PCM-based secure storage and encryption key management
Phase Change Memory (PCM) technology can be utilized for secure storage of encryption keys and sensitive data. The unique physical properties of PCM enable the creation of secure storage solutions that are resistant to unauthorized access. This approach combines the non-volatile characteristics of PCM with encryption mechanisms to provide enhanced security for cryptographic key storage and management, offering protection against physical and logical attacks.Expand Specific Solutions03 Cryptographic authentication and access control systems
Security systems can implement cryptographic authentication mechanisms using encryption standards to control access to protected resources. These systems employ various authentication protocols and encryption algorithms to verify user identities and establish secure communication channels. The integration of encryption standards with authentication frameworks provides multi-layered security for preventing unauthorized access and ensuring data integrity.Expand Specific Solutions04 Secure data transmission with encryption protocols
Encryption standards can be applied to secure data transmission across various communication channels. These implementations focus on protecting data in transit through the application of robust encryption algorithms and secure communication protocols. The systems ensure confidentiality and integrity of transmitted data by employing standardized encryption methods that prevent interception and tampering during transmission.Expand Specific Solutions05 Integrated encryption solutions for memory protection
Memory protection systems can incorporate encryption standards to safeguard stored data against unauthorized access and tampering. These solutions integrate encryption capabilities directly into memory architectures, providing transparent encryption and decryption operations. The approach ensures that sensitive information remains protected even if physical access to the memory is compromised, combining memory technology with cryptographic security measures.Expand Specific Solutions
Key Players in Cryptographic Hardware and Software Industry
The security comparison between PCM and Advanced Encryption Standards represents a rapidly evolving sector within the broader cybersecurity market, which has reached multi-billion dollar valuations globally. The industry is currently in a transitional phase, moving from traditional encryption methods toward more sophisticated security architectures. Technology maturity varies significantly across market participants, with established players like IBM, Microsoft Technology Licensing LLC, and Huawei Technologies demonstrating advanced capabilities in both hardware and software security implementations. Semiconductor specialists including STMicroelectronics and Macronix International provide foundational hardware security components, while companies like DigiCert focus on certificate-based security solutions. Chinese entities such as Feiteng Information Technology and Beijing Smartchip Microelectronics are developing indigenous security technologies, particularly in processor-level security features. The competitive landscape shows a clear division between mature Western technology providers and emerging Asian manufacturers, with academic institutions like Beijing University of Technology and Huazhong University of Science & Technology contributing fundamental research that bridges traditional PCM applications with modern encryption standards.
Huawei Technologies Co., Ltd.
Technical Solution: Huawei has implemented PCM technology in their storage solutions with integrated security frameworks that compare favorably to AES standards. Their approach focuses on combining PCM's non-volatile characteristics with encryption algorithms optimized for memory operations. The company has developed proprietary security protocols that leverage PCM's unique properties, such as its ability to maintain data integrity without power while providing encryption key storage directly in the memory cells. Their solution includes multi-layer security architecture that encompasses both software-based AES encryption and hardware-based PCM security features, targeting telecommunications and data center applications.
Strengths: Telecommunications expertise, integrated hardware-software security, cost-effective solutions. Weaknesses: Limited global market presence due to regulatory restrictions, newer technology compared to established players.
International Business Machines Corp.
Technical Solution: IBM has developed comprehensive PCM (Phase Change Memory) solutions that integrate advanced encryption capabilities at the hardware level. Their PCM technology utilizes chalcogenide materials that can switch between crystalline and amorphous states to store data, while implementing AES-256 encryption directly within the memory controller. This approach provides both the speed advantages of PCM with sub-microsecond access times and robust security through hardware-accelerated encryption. IBM's solution includes secure key management systems and tamper-resistant features that make it suitable for enterprise applications requiring both high performance and security compliance.
Strengths: Hardware-level encryption integration, enterprise-grade security features, proven scalability. Weaknesses: Higher cost compared to traditional solutions, complex implementation requirements.
Core Technical Innovations in PCM Security Applications
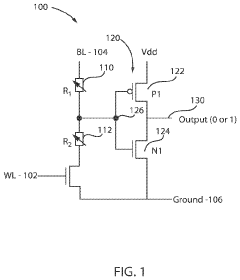
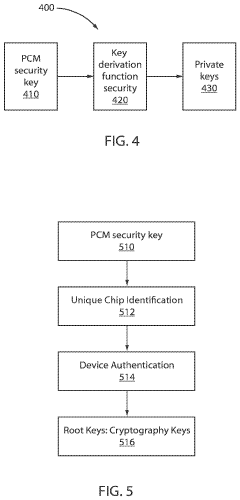
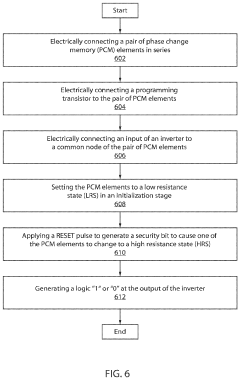
On-chip security key with phase change memory
PatentActiveUS11081172B1
Innovation
- The method involves forming on-chip security keys using a pair of phase change memory (PCM) elements connected in series with a programming transistor and a CMOS inverter, where PCM elements are set to a low resistance state and a RESET pulse is applied to generate a security bit, allowing for dynamic key generation and erasure, preventing key theft.
Phase-change memory device with reduced programming voltage
PatentWO2022189300A1
Innovation
- The use of a bridge cell architecture with workfunction altering materials, where at least one electrode is coated to increase the difference in workfunction between electrodes, reduces the threshold programming voltage and minimizes the amount of phase-change material needed in the amorphous state, thereby reducing power consumption and enhancing data retention.
Cryptographic Standards and Compliance Requirements
Cryptographic standards and compliance requirements form the regulatory backbone that governs the implementation and deployment of encryption technologies across various industries and government sectors. These frameworks establish mandatory security baselines, certification processes, and operational guidelines that organizations must adhere to when selecting and implementing cryptographic solutions.
The Federal Information Processing Standards (FIPS) 140-2 and its successor FIPS 140-3 represent cornerstone compliance frameworks in the United States, defining security requirements for cryptographic modules used in federal systems. These standards mandate rigorous testing and validation procedures for encryption implementations, including both hardware and software components. Advanced Encryption Standard (AES) has achieved FIPS validation across multiple security levels, establishing its credibility for government and enterprise applications.
Common Criteria (CC) evaluations provide internationally recognized security certifications that assess cryptographic products against standardized protection profiles. AES implementations frequently undergo CC evaluations to demonstrate compliance with security functional requirements and assurance levels. These certifications enable cross-border acceptance and facilitate international procurement processes for security-critical applications.
Industry-specific compliance frameworks impose additional cryptographic requirements tailored to sector-specific risks and regulatory environments. The Payment Card Industry Data Security Standard (PCI DSS) mandates strong encryption for cardholder data protection, while healthcare organizations must comply with HIPAA encryption requirements for protected health information. Financial services face stringent regulatory oversight through frameworks like SOX and Basel III, which specify cryptographic controls for data integrity and confidentiality.
Privacy regulations such as GDPR and CCPA introduce data protection requirements that directly impact cryptographic implementation strategies. These frameworks emphasize encryption as a technical safeguard for personal data processing and establish legal obligations for organizations to implement appropriate cryptographic measures based on risk assessments and data sensitivity classifications.
The compliance landscape for emerging technologies like PCM presents unique challenges due to the absence of established certification pathways and standardized evaluation criteria. Unlike mature encryption standards with well-defined compliance frameworks, novel cryptographic approaches must navigate uncertain regulatory environments while demonstrating equivalent or superior security properties to gain acceptance in regulated industries.
The Federal Information Processing Standards (FIPS) 140-2 and its successor FIPS 140-3 represent cornerstone compliance frameworks in the United States, defining security requirements for cryptographic modules used in federal systems. These standards mandate rigorous testing and validation procedures for encryption implementations, including both hardware and software components. Advanced Encryption Standard (AES) has achieved FIPS validation across multiple security levels, establishing its credibility for government and enterprise applications.
Common Criteria (CC) evaluations provide internationally recognized security certifications that assess cryptographic products against standardized protection profiles. AES implementations frequently undergo CC evaluations to demonstrate compliance with security functional requirements and assurance levels. These certifications enable cross-border acceptance and facilitate international procurement processes for security-critical applications.
Industry-specific compliance frameworks impose additional cryptographic requirements tailored to sector-specific risks and regulatory environments. The Payment Card Industry Data Security Standard (PCI DSS) mandates strong encryption for cardholder data protection, while healthcare organizations must comply with HIPAA encryption requirements for protected health information. Financial services face stringent regulatory oversight through frameworks like SOX and Basel III, which specify cryptographic controls for data integrity and confidentiality.
Privacy regulations such as GDPR and CCPA introduce data protection requirements that directly impact cryptographic implementation strategies. These frameworks emphasize encryption as a technical safeguard for personal data processing and establish legal obligations for organizations to implement appropriate cryptographic measures based on risk assessments and data sensitivity classifications.
The compliance landscape for emerging technologies like PCM presents unique challenges due to the absence of established certification pathways and standardized evaluation criteria. Unlike mature encryption standards with well-defined compliance frameworks, novel cryptographic approaches must navigate uncertain regulatory environments while demonstrating equivalent or superior security properties to gain acceptance in regulated industries.
Performance vs Security Trade-offs Analysis
The performance versus security trade-off analysis between Physical Cryptographic Modules (PCM) and Advanced Encryption Standards (AES) reveals fundamental differences in computational overhead, implementation complexity, and security assurance levels. PCM systems typically demonstrate superior security characteristics through hardware-based entropy generation and tamper-resistant properties, but these advantages come at the cost of increased latency and higher power consumption compared to software-implemented AES solutions.
Performance metrics indicate that AES implementations, particularly AES-128 and AES-256, achieve significantly higher throughput rates in software environments, often exceeding 1 GB/s on modern processors with dedicated cryptographic instruction sets. The symmetric nature of AES allows for efficient parallel processing and optimized implementations across various hardware platforms. However, this performance advantage diminishes when considering the complete security ecosystem requirements, including key management, secure storage, and authentication protocols.
PCM solutions introduce additional latency due to hardware-based random number generation and cryptographic processing within dedicated security chips. Typical PCM implementations exhibit throughput rates ranging from 10-100 MB/s, depending on the specific hardware configuration and cryptographic operations performed. This performance penalty is offset by enhanced security features, including physical tamper detection, secure key storage in hardware security modules, and resistance to side-channel attacks.
The security-performance trade-off becomes particularly evident in real-time applications where latency constraints are critical. AES implementations can achieve sub-microsecond encryption times for small data blocks, making them suitable for high-frequency trading systems and real-time communications. Conversely, PCM systems may require several milliseconds for equivalent operations due to hardware-based verification processes and secure boot sequences.
Energy consumption analysis reveals that PCM implementations generally require 2-5 times more power than optimized AES software solutions, primarily due to dedicated cryptographic hardware and continuous security monitoring functions. This energy overhead must be balanced against the enhanced security posture provided by hardware-based implementations, particularly in scenarios where cryptographic key compromise could result in significant financial or operational consequences.
The scalability implications further highlight the performance-security trade-off, as PCM solutions face limitations in concurrent processing capabilities due to hardware constraints, while AES implementations can leverage multi-core processors and distributed computing architectures to achieve linear performance scaling with increased computational resources.
Performance metrics indicate that AES implementations, particularly AES-128 and AES-256, achieve significantly higher throughput rates in software environments, often exceeding 1 GB/s on modern processors with dedicated cryptographic instruction sets. The symmetric nature of AES allows for efficient parallel processing and optimized implementations across various hardware platforms. However, this performance advantage diminishes when considering the complete security ecosystem requirements, including key management, secure storage, and authentication protocols.
PCM solutions introduce additional latency due to hardware-based random number generation and cryptographic processing within dedicated security chips. Typical PCM implementations exhibit throughput rates ranging from 10-100 MB/s, depending on the specific hardware configuration and cryptographic operations performed. This performance penalty is offset by enhanced security features, including physical tamper detection, secure key storage in hardware security modules, and resistance to side-channel attacks.
The security-performance trade-off becomes particularly evident in real-time applications where latency constraints are critical. AES implementations can achieve sub-microsecond encryption times for small data blocks, making them suitable for high-frequency trading systems and real-time communications. Conversely, PCM systems may require several milliseconds for equivalent operations due to hardware-based verification processes and secure boot sequences.
Energy consumption analysis reveals that PCM implementations generally require 2-5 times more power than optimized AES software solutions, primarily due to dedicated cryptographic hardware and continuous security monitoring functions. This energy overhead must be balanced against the enhanced security posture provided by hardware-based implementations, particularly in scenarios where cryptographic key compromise could result in significant financial or operational consequences.
The scalability implications further highlight the performance-security trade-off, as PCM solutions face limitations in concurrent processing capabilities due to hardware constraints, while AES implementations can leverage multi-core processors and distributed computing architectures to achieve linear performance scaling with increased computational resources.
Unlock deeper insights with PatSnap Eureka Quick Research — get a full tech report to explore trends and direct your research. Try now!
Generate Your Research Report Instantly with AI Agent
Supercharge your innovation with PatSnap Eureka AI Agent Platform!