How to Establish Secure Connections in Microcontroller Networks
FEB 25, 20269 MIN READ
Generate Your Research Report Instantly with AI Agent
Patsnap Eureka helps you evaluate technical feasibility & market potential.
Microcontroller Network Security Background and Objectives
Microcontroller networks have emerged as fundamental components of modern embedded systems, spanning applications from industrial automation and smart home devices to automotive systems and healthcare monitoring equipment. The proliferation of Internet of Things (IoT) devices has exponentially increased the deployment of interconnected microcontroller-based systems, creating vast networks of resource-constrained devices that communicate wirelessly or through wired connections. This technological evolution has transformed how we interact with our environment, enabling unprecedented levels of automation and data collection.
The historical development of microcontroller networking began with simple point-to-point communications in the 1980s, evolving through fieldbus systems in industrial applications during the 1990s, and culminating in today's complex mesh networks and IoT ecosystems. Early implementations focused primarily on functionality and cost optimization, with security considerations often relegated to secondary importance. However, the increasing connectivity and critical nature of applications have fundamentally shifted this paradigm.
Contemporary microcontroller networks face unprecedented security challenges due to their inherent resource limitations, including restricted processing power, limited memory capacity, and constrained energy budgets. These limitations create a complex security landscape where traditional cryptographic approaches may be impractical or impossible to implement effectively. The distributed nature of these networks, often spanning large geographical areas with minimal physical security, further compounds the vulnerability profile.
The primary objective of establishing secure connections in microcontroller networks is to ensure confidentiality, integrity, and authenticity of data transmission while maintaining system availability and performance within the constraints of resource-limited devices. This encompasses protecting against eavesdropping, data tampering, unauthorized access, and denial-of-service attacks. Additionally, secure connections must support device authentication, secure key management, and protection against both passive and active network attacks.
The technical goals extend beyond basic encryption to include lightweight authentication protocols, efficient key distribution mechanisms, and robust intrusion detection capabilities tailored for resource-constrained environments. These objectives must be achieved while preserving the real-time performance requirements critical to many microcontroller applications, ensuring that security implementations do not compromise the fundamental operational characteristics that make these systems viable for their intended applications.
The historical development of microcontroller networking began with simple point-to-point communications in the 1980s, evolving through fieldbus systems in industrial applications during the 1990s, and culminating in today's complex mesh networks and IoT ecosystems. Early implementations focused primarily on functionality and cost optimization, with security considerations often relegated to secondary importance. However, the increasing connectivity and critical nature of applications have fundamentally shifted this paradigm.
Contemporary microcontroller networks face unprecedented security challenges due to their inherent resource limitations, including restricted processing power, limited memory capacity, and constrained energy budgets. These limitations create a complex security landscape where traditional cryptographic approaches may be impractical or impossible to implement effectively. The distributed nature of these networks, often spanning large geographical areas with minimal physical security, further compounds the vulnerability profile.
The primary objective of establishing secure connections in microcontroller networks is to ensure confidentiality, integrity, and authenticity of data transmission while maintaining system availability and performance within the constraints of resource-limited devices. This encompasses protecting against eavesdropping, data tampering, unauthorized access, and denial-of-service attacks. Additionally, secure connections must support device authentication, secure key management, and protection against both passive and active network attacks.
The technical goals extend beyond basic encryption to include lightweight authentication protocols, efficient key distribution mechanisms, and robust intrusion detection capabilities tailored for resource-constrained environments. These objectives must be achieved while preserving the real-time performance requirements critical to many microcontroller applications, ensuring that security implementations do not compromise the fundamental operational characteristics that make these systems viable for their intended applications.
Market Demand for Secure MCU Network Solutions
The global microcontroller market is experiencing unprecedented growth driven by the proliferation of Internet of Things devices, industrial automation systems, and smart infrastructure deployments. This expansion has created substantial demand for secure networking solutions that can protect microcontroller-based systems from increasingly sophisticated cyber threats. Organizations across multiple sectors are recognizing that traditional security approaches are inadequate for resource-constrained microcontroller environments.
Industrial automation represents one of the largest market segments driving demand for secure MCU network solutions. Manufacturing facilities, power grids, and transportation systems rely heavily on microcontroller networks for critical operations. Security breaches in these environments can result in production downtime, safety hazards, and significant financial losses, creating strong incentives for robust security implementations.
The healthcare sector presents another high-growth market segment, particularly with the rise of connected medical devices and remote patient monitoring systems. Regulatory requirements such as HIPAA and FDA guidelines mandate stringent security measures for medical devices, driving healthcare organizations to seek comprehensive security solutions for their microcontroller-based equipment.
Smart city initiatives worldwide are generating substantial demand for secure microcontroller networking solutions. Traffic management systems, environmental monitoring networks, and public safety infrastructure require reliable security mechanisms to prevent malicious attacks that could disrupt essential services. Municipal governments are increasingly allocating budgets specifically for cybersecurity measures in their smart city deployments.
The automotive industry is experiencing rapid transformation with the integration of connected vehicle technologies and autonomous driving systems. Modern vehicles contain numerous microcontrollers managing everything from engine control to infotainment systems. The potential consequences of security vulnerabilities in automotive networks have created urgent demand for proven security solutions that can operate within the strict resource and real-time constraints of automotive microcontrollers.
Consumer electronics manufacturers are also driving market demand as they integrate networking capabilities into traditionally standalone devices. Smart home appliances, wearable devices, and personal electronics now require security measures to protect user privacy and prevent unauthorized access. The growing awareness of cybersecurity risks among consumers is pushing manufacturers to prioritize security features in their product development cycles.
Enterprise customers are increasingly seeking comprehensive security solutions that can scale across large deployments of microcontroller-based devices while maintaining centralized management capabilities. This demand is particularly strong in sectors such as retail, logistics, and building automation where organizations deploy thousands of connected devices across multiple locations.
Industrial automation represents one of the largest market segments driving demand for secure MCU network solutions. Manufacturing facilities, power grids, and transportation systems rely heavily on microcontroller networks for critical operations. Security breaches in these environments can result in production downtime, safety hazards, and significant financial losses, creating strong incentives for robust security implementations.
The healthcare sector presents another high-growth market segment, particularly with the rise of connected medical devices and remote patient monitoring systems. Regulatory requirements such as HIPAA and FDA guidelines mandate stringent security measures for medical devices, driving healthcare organizations to seek comprehensive security solutions for their microcontroller-based equipment.
Smart city initiatives worldwide are generating substantial demand for secure microcontroller networking solutions. Traffic management systems, environmental monitoring networks, and public safety infrastructure require reliable security mechanisms to prevent malicious attacks that could disrupt essential services. Municipal governments are increasingly allocating budgets specifically for cybersecurity measures in their smart city deployments.
The automotive industry is experiencing rapid transformation with the integration of connected vehicle technologies and autonomous driving systems. Modern vehicles contain numerous microcontrollers managing everything from engine control to infotainment systems. The potential consequences of security vulnerabilities in automotive networks have created urgent demand for proven security solutions that can operate within the strict resource and real-time constraints of automotive microcontrollers.
Consumer electronics manufacturers are also driving market demand as they integrate networking capabilities into traditionally standalone devices. Smart home appliances, wearable devices, and personal electronics now require security measures to protect user privacy and prevent unauthorized access. The growing awareness of cybersecurity risks among consumers is pushing manufacturers to prioritize security features in their product development cycles.
Enterprise customers are increasingly seeking comprehensive security solutions that can scale across large deployments of microcontroller-based devices while maintaining centralized management capabilities. This demand is particularly strong in sectors such as retail, logistics, and building automation where organizations deploy thousands of connected devices across multiple locations.
Current Security Challenges in Microcontroller Networks
Microcontroller networks face unprecedented security vulnerabilities due to their inherent resource constraints and widespread deployment across critical infrastructure. The limited computational power, memory capacity, and energy resources of microcontrollers create fundamental challenges in implementing robust security mechanisms that are standard in traditional computing environments.
Authentication and key management represent primary security bottlenecks in microcontroller networks. Traditional public key cryptography algorithms consume excessive computational resources, making real-time authentication difficult. The challenge intensifies when managing cryptographic keys across thousands of distributed nodes, where secure key distribution and periodic key rotation become operationally complex without centralized infrastructure.
Communication channel security poses another critical challenge, as microcontrollers often rely on wireless protocols that are inherently vulnerable to eavesdropping and man-in-the-middle attacks. The implementation of end-to-end encryption protocols must balance security strength with processing efficiency, often resulting in compromised security levels to maintain acceptable performance.
Device identity verification and trust establishment remain problematic in large-scale deployments. Microcontrollers frequently lack unique hardware identifiers or secure storage capabilities, making it difficult to establish device authenticity and prevent unauthorized nodes from joining the network. This vulnerability becomes particularly acute in IoT environments where physical access to devices may be unrestricted.
Firmware integrity and secure boot processes present additional security gaps. Many microcontrollers lack hardware-based security features such as secure boot mechanisms or trusted execution environments, leaving them vulnerable to firmware tampering and malicious code injection. The absence of secure update mechanisms further compounds these risks.
Power analysis and side-channel attacks exploit the physical characteristics of microcontroller operations. Limited resources prevent the implementation of comprehensive countermeasures against timing attacks, electromagnetic analysis, and power consumption monitoring, which can reveal cryptographic keys and sensitive operational data.
Network scalability introduces security management complexity as the number of connected devices grows exponentially. Traditional security protocols designed for smaller networks become inefficient and may create single points of failure when applied to massive microcontroller deployments spanning diverse geographical locations and operational environments.
Authentication and key management represent primary security bottlenecks in microcontroller networks. Traditional public key cryptography algorithms consume excessive computational resources, making real-time authentication difficult. The challenge intensifies when managing cryptographic keys across thousands of distributed nodes, where secure key distribution and periodic key rotation become operationally complex without centralized infrastructure.
Communication channel security poses another critical challenge, as microcontrollers often rely on wireless protocols that are inherently vulnerable to eavesdropping and man-in-the-middle attacks. The implementation of end-to-end encryption protocols must balance security strength with processing efficiency, often resulting in compromised security levels to maintain acceptable performance.
Device identity verification and trust establishment remain problematic in large-scale deployments. Microcontrollers frequently lack unique hardware identifiers or secure storage capabilities, making it difficult to establish device authenticity and prevent unauthorized nodes from joining the network. This vulnerability becomes particularly acute in IoT environments where physical access to devices may be unrestricted.
Firmware integrity and secure boot processes present additional security gaps. Many microcontrollers lack hardware-based security features such as secure boot mechanisms or trusted execution environments, leaving them vulnerable to firmware tampering and malicious code injection. The absence of secure update mechanisms further compounds these risks.
Power analysis and side-channel attacks exploit the physical characteristics of microcontroller operations. Limited resources prevent the implementation of comprehensive countermeasures against timing attacks, electromagnetic analysis, and power consumption monitoring, which can reveal cryptographic keys and sensitive operational data.
Network scalability introduces security management complexity as the number of connected devices grows exponentially. Traditional security protocols designed for smaller networks become inefficient and may create single points of failure when applied to massive microcontroller deployments spanning diverse geographical locations and operational environments.
Existing Secure Connection Solutions for MCU Networks
01 Cryptographic authentication protocols for microcontroller networks
Secure connections in microcontroller networks can be established through cryptographic authentication protocols that verify the identity of devices before allowing communication. These protocols utilize encryption algorithms, digital signatures, and certificate-based authentication to ensure that only authorized microcontrollers can join the network and exchange data. The authentication process typically involves challenge-response mechanisms and secure key exchange methods to prevent unauthorized access and man-in-the-middle attacks.- Cryptographic authentication protocols for microcontroller networks: Secure connections in microcontroller networks can be established through cryptographic authentication protocols that verify the identity of devices before allowing communication. These protocols utilize encryption algorithms, digital signatures, and certificate-based authentication to ensure that only authorized microcontrollers can join the network and exchange data. The authentication process may involve challenge-response mechanisms, public key infrastructure, or symmetric key exchanges to prevent unauthorized access and man-in-the-middle attacks.
- Secure boot and firmware verification mechanisms: Microcontroller networks can implement secure boot processes that verify the integrity and authenticity of firmware before execution. This approach uses cryptographic hash functions and digital signatures to ensure that only trusted code runs on the microcontroller. The verification mechanism checks the firmware against stored signatures or certificates during the boot sequence, preventing the execution of malicious or tampered code. This security layer protects the entire network by ensuring each node operates with verified and trusted software.
- Encrypted communication channels and data transmission: Establishing encrypted communication channels between microcontrollers ensures that data transmitted across the network remains confidential and protected from eavesdropping. Encryption techniques such as symmetric and asymmetric cryptography are applied to data packets before transmission. The microcontrollers negotiate encryption keys through secure key exchange protocols, and all subsequent communications are encrypted using these keys. This approach protects sensitive information from interception and unauthorized access during transmission across the network.
- Network access control and device authorization: Microcontroller networks implement access control mechanisms that regulate which devices can connect and communicate within the network. These systems use authentication credentials, access tokens, or hardware-based identifiers to verify device legitimacy. Authorization policies define the level of access and permissions granted to each microcontroller based on its role and security clearance. The access control framework may include dynamic authorization updates, revocation capabilities, and monitoring systems to detect and prevent unauthorized connection attempts.
- Intrusion detection and security monitoring systems: Security monitoring systems for microcontroller networks continuously analyze network traffic and device behavior to detect potential security threats and intrusions. These systems employ anomaly detection algorithms, pattern recognition, and behavioral analysis to identify suspicious activities such as unauthorized access attempts, unusual data flows, or compromised devices. When threats are detected, the monitoring system can trigger alerts, isolate affected devices, or implement countermeasures to maintain network security. The monitoring framework provides real-time visibility into network security status and enables rapid response to security incidents.
02 Secure boot and firmware verification mechanisms
Microcontroller networks can implement secure boot processes that verify the integrity and authenticity of firmware before execution. This approach uses cryptographic hash functions and digital signatures to ensure that only trusted code runs on the microcontroller. The verification mechanism checks the firmware against stored signatures or certificates during the boot sequence, preventing the execution of malicious or tampered code. This security layer protects the entire network by ensuring each node operates with verified and trusted software.Expand Specific Solutions03 Encrypted communication channels and secure data transmission
Establishing encrypted communication channels between microcontrollers ensures that data transmitted across the network remains confidential and protected from eavesdropping. Various encryption standards and protocols can be implemented to secure the data packets exchanged between nodes. The encryption methods include symmetric and asymmetric key algorithms that protect sensitive information during transmission. Additionally, secure session establishment protocols ensure that communication channels are properly authenticated before data exchange begins.Expand Specific Solutions04 Hardware-based security modules and trusted execution environments
Microcontroller networks can incorporate dedicated hardware security modules that provide isolated execution environments for critical security operations. These modules store cryptographic keys in tamper-resistant memory and perform sensitive operations in a protected domain separate from the main processor. The hardware-based approach offers enhanced protection against physical attacks and software vulnerabilities. Trusted execution environments ensure that security-critical code and data remain isolated from potentially compromised system components.Expand Specific Solutions05 Network access control and device authorization frameworks
Secure microcontroller networks implement access control mechanisms that manage which devices can connect and what resources they can access. These frameworks use authorization policies, access tokens, and permission management systems to enforce security boundaries within the network. The control systems can dynamically grant or revoke access based on device credentials, security posture, and network policies. Multi-level authorization schemes ensure that different microcontrollers have appropriate access rights based on their roles and trust levels within the network.Expand Specific Solutions
Key Players in Microcontroller Security Industry
The microcontroller network security landscape is experiencing rapid growth driven by IoT expansion and increasing cybersecurity threats. The market demonstrates significant scale with diverse players spanning telecommunications giants like Qualcomm, Huawei, ZTE, and Ericsson providing foundational wireless technologies, while specialized security firms such as Thales DIS France and China Iwncomm focus on encryption solutions. Technology maturity varies considerably across segments - established companies like Keysight Technologies and Rockwell Automation offer mature testing and industrial automation solutions, whereas emerging players like Shanghai Huahong Integrated Circuit and New H3C Information Security Technology represent evolving semiconductor and network security capabilities. The competitive landscape shows strong representation from Chinese state-backed entities including State Grid Corporation subsidiaries, indicating strategic national investment in secure infrastructure technologies alongside established Western technology leaders.
QUALCOMM, Inc.
Technical Solution: QUALCOMM implements comprehensive security frameworks for microcontroller networks through their Snapdragon platforms, featuring hardware-based security elements including ARM TrustZone technology, secure boot processes, and cryptographic accelerators. Their solution incorporates TLS 1.3 protocol support with hardware-accelerated encryption/decryption capabilities, enabling secure communication channels between microcontrollers. The platform provides integrated security services including device authentication, secure key management, and over-the-air update mechanisms. QUALCOMM's approach emphasizes low-power security implementations suitable for IoT and embedded systems, with dedicated security processors that handle cryptographic operations without impacting main system performance.
Strengths: Industry-leading hardware security integration, extensive ecosystem support, proven scalability across diverse applications. Weaknesses: Higher cost compared to basic solutions, complexity may be excessive for simple microcontroller applications.
ZTE Corp.
Technical Solution: ZTE develops secure microcontroller network solutions through their uSmart platform, incorporating lightweight security protocols and hardware security modules tailored for industrial IoT applications. Their implementation features secure boot mechanisms, encrypted communication channels using optimized TLS variants, and distributed key management systems. The solution supports multiple authentication methods including certificate-based and token-based approaches, with emphasis on maintaining security while minimizing computational overhead. ZTE's approach includes secure firmware update capabilities and network segmentation techniques to isolate critical microcontroller clusters, ensuring robust protection against both external and internal threats in complex network topologies.
Strengths: Strong focus on industrial applications, competitive pricing with good performance balance. Weaknesses: Limited global market presence compared to major competitors, fewer third-party integrations available.
Core Security Technologies for Microcontroller Communications
Microcontroller
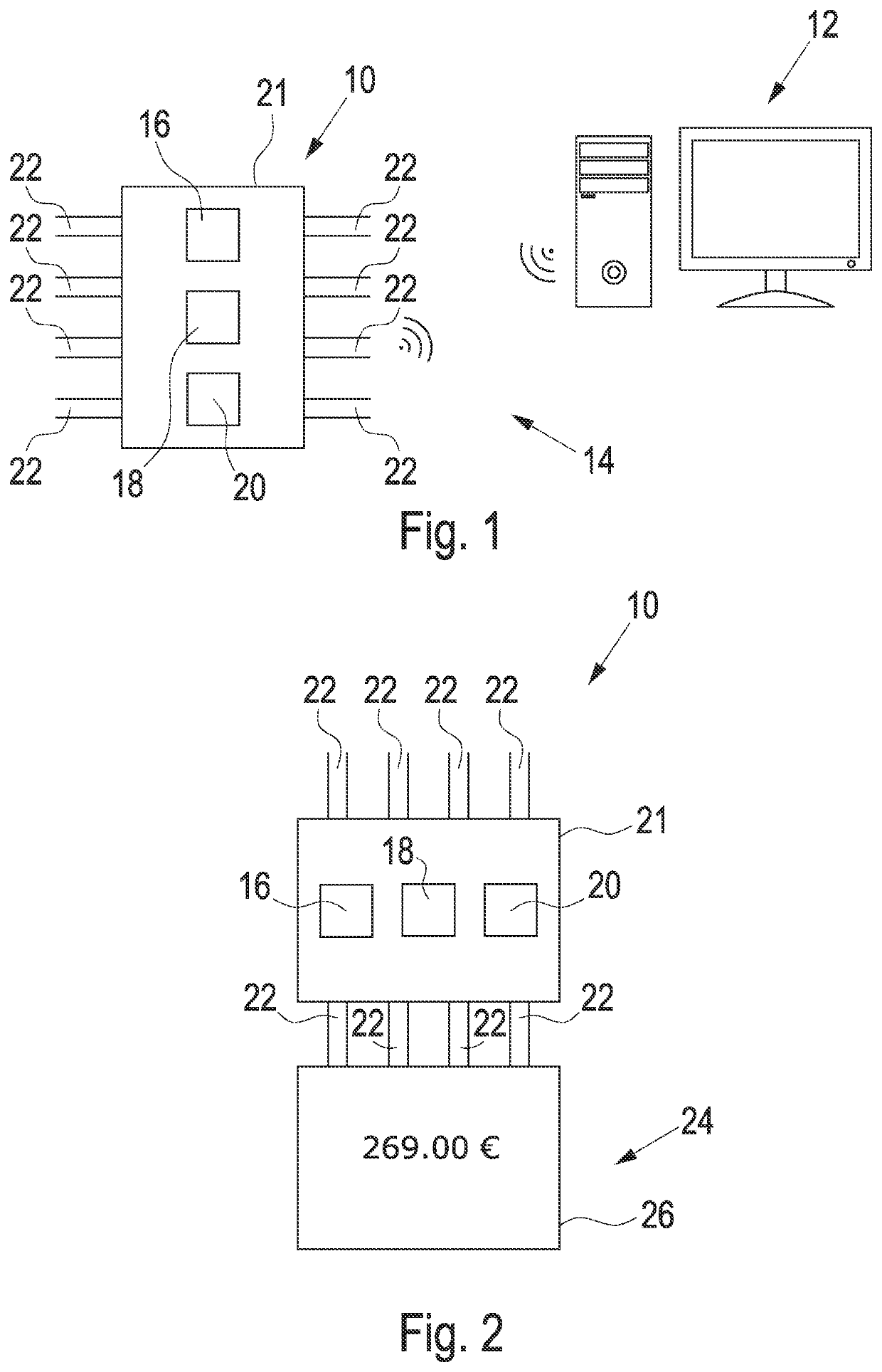
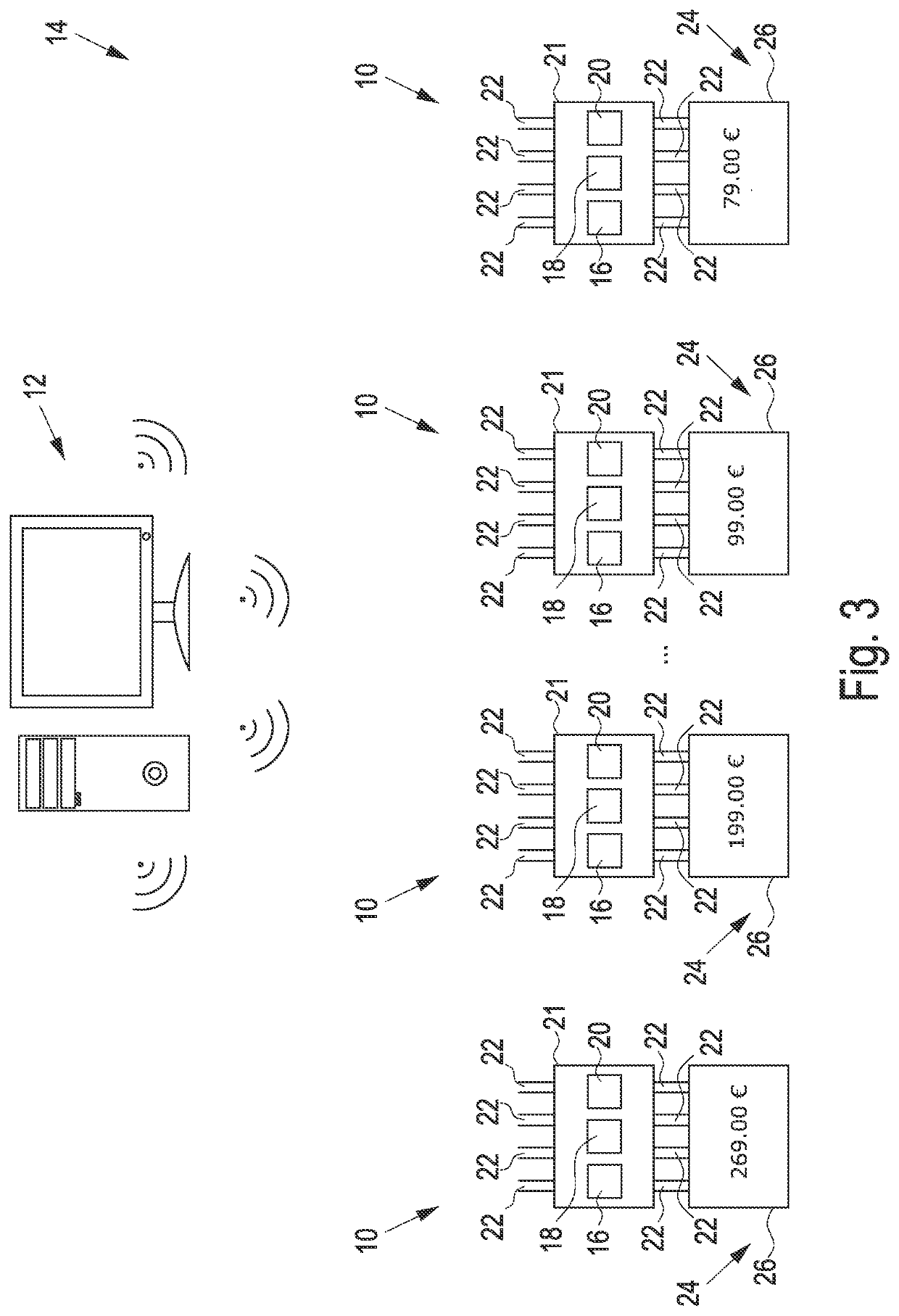
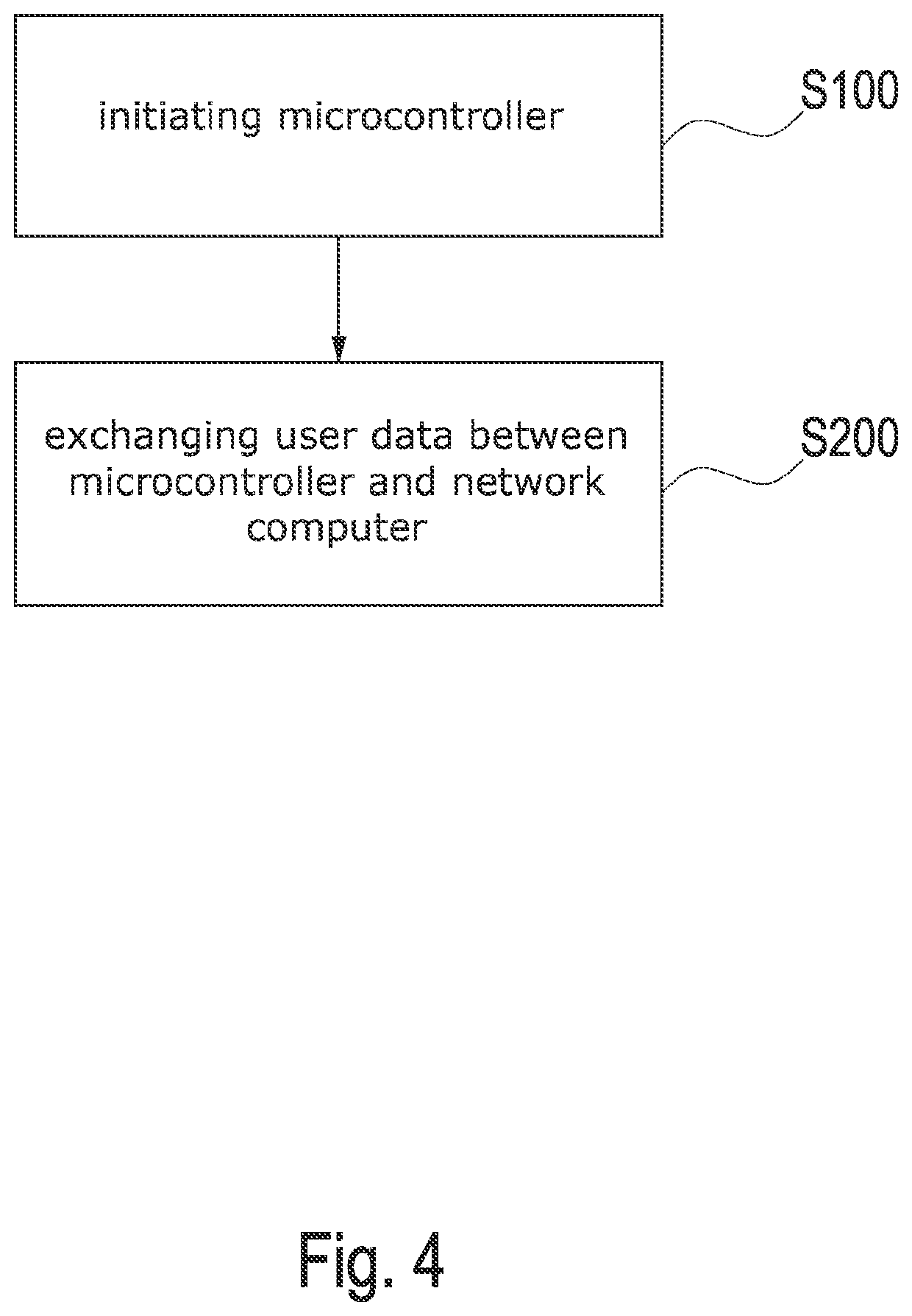
PatentActiveUS20220116384A1
Innovation
- A microcontroller with a network module that establishes a connection with a network computer to request, receive, and store a digital certificate, allowing for secure and efficient issuance without the manufacturer having access to the certificate or authentication key, using protocols like SRP for secure communication.
Methods for facilitating secure connections for an operating system kernel and devices thereof
PatentActiveUS11025728B2
Innovation
- A method utilizing a proxy application in user space to handle the handshake phase of secure protocols, allowing the kernel to manage data exchange securely without the need for complex cryptographic negotiations, thereby reducing resource strain and latency.
Cybersecurity Standards for Embedded Systems
The cybersecurity landscape for embedded systems has evolved significantly with the proliferation of Internet of Things devices and microcontroller networks. Establishing comprehensive security standards has become paramount as these systems increasingly handle sensitive data and control critical infrastructure. The development of robust cybersecurity frameworks specifically tailored for resource-constrained embedded environments represents a fundamental shift from traditional IT security approaches.
Current cybersecurity standards for embedded systems encompass multiple layers of protection, addressing both hardware and software vulnerabilities. The ISO/IEC 27001 framework provides foundational security management principles, while IEC 62443 specifically targets industrial automation and control systems. These standards emphasize the importance of secure boot processes, cryptographic key management, and secure communication protocols tailored for microcontroller architectures with limited computational resources.
The Common Criteria evaluation framework has been adapted for embedded systems, providing standardized security evaluation methodologies. This framework enables manufacturers to demonstrate compliance with specific security assurance levels, particularly relevant for microcontroller networks handling sensitive operations. The evaluation process considers threat modeling, security functional requirements, and assurance requirements specific to embedded environments.
Industry-specific standards have emerged to address unique security challenges in different sectors. The automotive industry has developed ISO/SAE 21434 for cybersecurity engineering, while medical device manufacturers follow IEC 62304 and FDA cybersecurity guidelines. These sector-specific standards recognize that microcontroller networks in different applications face distinct threat landscapes and operational constraints.
Emerging standards focus on lightweight cryptographic implementations suitable for microcontroller environments. The NIST Lightweight Cryptography initiative has established standards for authenticated encryption and hashing algorithms optimized for resource-constrained devices. These standards ensure that security measures do not compromise system performance or battery life in embedded applications.
The integration of hardware security modules and trusted platform modules into embedded systems standards reflects the growing emphasis on hardware-based security foundations. Standards now mandate secure element integration for critical applications, ensuring that cryptographic operations and key storage occur within tamper-resistant hardware components, providing robust protection against physical and logical attacks in microcontroller networks.
Current cybersecurity standards for embedded systems encompass multiple layers of protection, addressing both hardware and software vulnerabilities. The ISO/IEC 27001 framework provides foundational security management principles, while IEC 62443 specifically targets industrial automation and control systems. These standards emphasize the importance of secure boot processes, cryptographic key management, and secure communication protocols tailored for microcontroller architectures with limited computational resources.
The Common Criteria evaluation framework has been adapted for embedded systems, providing standardized security evaluation methodologies. This framework enables manufacturers to demonstrate compliance with specific security assurance levels, particularly relevant for microcontroller networks handling sensitive operations. The evaluation process considers threat modeling, security functional requirements, and assurance requirements specific to embedded environments.
Industry-specific standards have emerged to address unique security challenges in different sectors. The automotive industry has developed ISO/SAE 21434 for cybersecurity engineering, while medical device manufacturers follow IEC 62304 and FDA cybersecurity guidelines. These sector-specific standards recognize that microcontroller networks in different applications face distinct threat landscapes and operational constraints.
Emerging standards focus on lightweight cryptographic implementations suitable for microcontroller environments. The NIST Lightweight Cryptography initiative has established standards for authenticated encryption and hashing algorithms optimized for resource-constrained devices. These standards ensure that security measures do not compromise system performance or battery life in embedded applications.
The integration of hardware security modules and trusted platform modules into embedded systems standards reflects the growing emphasis on hardware-based security foundations. Standards now mandate secure element integration for critical applications, ensuring that cryptographic operations and key storage occur within tamper-resistant hardware components, providing robust protection against physical and logical attacks in microcontroller networks.
Resource Optimization in Secure MCU Implementations
Resource optimization in secure microcontroller implementations represents a critical balance between maintaining robust security protocols and operating within the stringent constraints of embedded systems. Modern MCUs typically feature limited processing power, memory capacity, and energy resources, making efficient resource utilization paramount for practical deployment of security mechanisms.
Memory optimization strategies focus on minimizing the footprint of cryptographic libraries and security protocols. Lightweight cryptographic algorithms such as ChaCha20-Poly1305 and AES-128 in counter mode offer reduced memory requirements compared to traditional implementations while maintaining adequate security levels. Code optimization techniques, including function inlining and dead code elimination, can reduce program memory usage by 15-30% in typical secure MCU applications.
Processing power optimization involves selecting appropriate cryptographic algorithms that balance security strength with computational efficiency. Elliptic curve cryptography using curves like Curve25519 provides equivalent security to RSA with significantly lower computational overhead. Hardware acceleration features, when available, should be leveraged to offload intensive operations such as AES encryption and hash computations from the main processor.
Energy consumption optimization is crucial for battery-powered IoT devices. Dynamic frequency scaling allows MCUs to reduce clock speeds during cryptographic operations that are not time-critical. Sleep mode management between secure communications can extend battery life by up to 80% in intermittent communication scenarios. Efficient key management protocols that minimize the frequency of computationally expensive key exchange operations contribute significantly to energy conservation.
Buffer management and memory allocation strategies play vital roles in resource optimization. Static memory allocation for cryptographic operations prevents memory fragmentation and reduces overhead. Ring buffers for secure communication queues optimize memory usage while maintaining data integrity. Careful management of temporary variables and intermediate cryptographic values prevents memory leaks and reduces peak memory consumption during security operations.
Memory optimization strategies focus on minimizing the footprint of cryptographic libraries and security protocols. Lightweight cryptographic algorithms such as ChaCha20-Poly1305 and AES-128 in counter mode offer reduced memory requirements compared to traditional implementations while maintaining adequate security levels. Code optimization techniques, including function inlining and dead code elimination, can reduce program memory usage by 15-30% in typical secure MCU applications.
Processing power optimization involves selecting appropriate cryptographic algorithms that balance security strength with computational efficiency. Elliptic curve cryptography using curves like Curve25519 provides equivalent security to RSA with significantly lower computational overhead. Hardware acceleration features, when available, should be leveraged to offload intensive operations such as AES encryption and hash computations from the main processor.
Energy consumption optimization is crucial for battery-powered IoT devices. Dynamic frequency scaling allows MCUs to reduce clock speeds during cryptographic operations that are not time-critical. Sleep mode management between secure communications can extend battery life by up to 80% in intermittent communication scenarios. Efficient key management protocols that minimize the frequency of computationally expensive key exchange operations contribute significantly to energy conservation.
Buffer management and memory allocation strategies play vital roles in resource optimization. Static memory allocation for cryptographic operations prevents memory fragmentation and reduces overhead. Ring buffers for secure communication queues optimize memory usage while maintaining data integrity. Careful management of temporary variables and intermediate cryptographic values prevents memory leaks and reduces peak memory consumption during security operations.
Unlock deeper insights with Patsnap Eureka Quick Research — get a full tech report to explore trends and direct your research. Try now!
Generate Your Research Report Instantly with AI Agent
Supercharge your innovation with Patsnap Eureka AI Agent Platform!