Compare Logic Chip Features for Cybersecurity Applications
APR 2, 20269 MIN READ
Generate Your Research Report Instantly with AI Agent
Patsnap Eureka helps you evaluate technical feasibility & market potential.
Logic Chip Cybersecurity Background and Objectives
The evolution of cybersecurity threats has fundamentally transformed the landscape of digital security, with attackers increasingly targeting hardware-level vulnerabilities that traditional software-based defenses cannot adequately address. Logic chips, serving as the foundational computing elements in critical infrastructure, IoT devices, and enterprise systems, have become prime targets for sophisticated attacks including hardware trojans, side-channel exploits, and supply chain compromises. This escalating threat environment necessitates a comprehensive evaluation of logic chip architectures specifically designed to counter these emerging cybersecurity challenges.
The historical development of cybersecurity-focused logic chips traces back to the early 2000s when trusted platform modules (TPMs) first introduced hardware-based security anchors. Subsequently, the industry witnessed the emergence of secure enclaves, hardware security modules (HSMs), and specialized cryptographic processors. Recent years have seen accelerated innovation in areas such as physically unclonable functions (PUFs), secure boot mechanisms, and real-time threat detection capabilities embedded directly into silicon architectures.
Current technological trends indicate a shift toward heterogeneous computing architectures that integrate security functions at the chip level rather than relying solely on software implementations. This paradigm encompasses the development of security-first processor designs, dedicated cryptographic acceleration units, and adaptive defense mechanisms capable of responding to dynamic threat landscapes. The integration of artificial intelligence and machine learning capabilities directly into security chips represents another significant evolutionary trajectory.
The primary technical objectives driving this comparative analysis include establishing comprehensive evaluation criteria for assessing logic chip security features, identifying optimal architectural approaches for different cybersecurity applications, and determining performance trade-offs between security robustness and computational efficiency. Additionally, the analysis aims to evaluate scalability considerations for enterprise deployments and compatibility requirements with existing security frameworks.
Strategic objectives encompass providing actionable insights for technology selection decisions, establishing benchmarks for security chip performance evaluation, and identifying emerging technological gaps that require further research and development investment. The analysis seeks to support informed decision-making processes for organizations implementing hardware-based cybersecurity solutions across diverse operational environments and threat models.
The historical development of cybersecurity-focused logic chips traces back to the early 2000s when trusted platform modules (TPMs) first introduced hardware-based security anchors. Subsequently, the industry witnessed the emergence of secure enclaves, hardware security modules (HSMs), and specialized cryptographic processors. Recent years have seen accelerated innovation in areas such as physically unclonable functions (PUFs), secure boot mechanisms, and real-time threat detection capabilities embedded directly into silicon architectures.
Current technological trends indicate a shift toward heterogeneous computing architectures that integrate security functions at the chip level rather than relying solely on software implementations. This paradigm encompasses the development of security-first processor designs, dedicated cryptographic acceleration units, and adaptive defense mechanisms capable of responding to dynamic threat landscapes. The integration of artificial intelligence and machine learning capabilities directly into security chips represents another significant evolutionary trajectory.
The primary technical objectives driving this comparative analysis include establishing comprehensive evaluation criteria for assessing logic chip security features, identifying optimal architectural approaches for different cybersecurity applications, and determining performance trade-offs between security robustness and computational efficiency. Additionally, the analysis aims to evaluate scalability considerations for enterprise deployments and compatibility requirements with existing security frameworks.
Strategic objectives encompass providing actionable insights for technology selection decisions, establishing benchmarks for security chip performance evaluation, and identifying emerging technological gaps that require further research and development investment. The analysis seeks to support informed decision-making processes for organizations implementing hardware-based cybersecurity solutions across diverse operational environments and threat models.
Market Demand for Secure Logic Chip Solutions
The cybersecurity landscape has witnessed unprecedented growth in demand for secure logic chip solutions, driven by escalating cyber threats and stringent regulatory requirements across multiple industries. Organizations worldwide are increasingly recognizing that traditional software-based security measures are insufficient against sophisticated attacks, creating substantial market opportunities for hardware-based security solutions.
Financial services sector represents one of the most significant demand drivers, as banks and payment processors require tamper-resistant hardware security modules and secure elements to protect sensitive transaction data. The proliferation of digital payment systems and cryptocurrency platforms has further amplified this demand, with institutions seeking logic chips that provide hardware-level encryption and authentication capabilities.
Critical infrastructure sectors including power grids, water systems, and transportation networks are experiencing heightened security requirements following numerous high-profile cyberattacks. These sectors demand logic chips with built-in security features such as secure boot mechanisms, hardware-based attestation, and real-time threat detection capabilities to protect operational technology environments.
The Internet of Things market expansion has created massive demand for secure logic chips in connected devices. Smart home systems, industrial IoT sensors, and automotive electronics require embedded security features to prevent unauthorized access and data breaches. Manufacturers are increasingly seeking cost-effective secure logic solutions that can be integrated into resource-constrained devices without compromising performance.
Government and defense applications continue to drive demand for high-assurance secure logic chips meeting stringent certification requirements. Military communications systems, classified data processing equipment, and national security infrastructure require chips with advanced features such as side-channel attack resistance and secure key management capabilities.
Healthcare digitization has emerged as another significant market driver, with medical device manufacturers requiring secure logic chips to protect patient data and ensure device integrity. Regulatory compliance requirements such as HIPAA and medical device cybersecurity guidelines are pushing healthcare organizations toward hardware-based security solutions.
The enterprise market shows growing adoption of secure logic chips for data center security, cloud computing infrastructure, and endpoint protection. Organizations are investing in hardware security modules and trusted platform modules to establish hardware roots of trust and protect against advanced persistent threats targeting their digital assets.
Financial services sector represents one of the most significant demand drivers, as banks and payment processors require tamper-resistant hardware security modules and secure elements to protect sensitive transaction data. The proliferation of digital payment systems and cryptocurrency platforms has further amplified this demand, with institutions seeking logic chips that provide hardware-level encryption and authentication capabilities.
Critical infrastructure sectors including power grids, water systems, and transportation networks are experiencing heightened security requirements following numerous high-profile cyberattacks. These sectors demand logic chips with built-in security features such as secure boot mechanisms, hardware-based attestation, and real-time threat detection capabilities to protect operational technology environments.
The Internet of Things market expansion has created massive demand for secure logic chips in connected devices. Smart home systems, industrial IoT sensors, and automotive electronics require embedded security features to prevent unauthorized access and data breaches. Manufacturers are increasingly seeking cost-effective secure logic solutions that can be integrated into resource-constrained devices without compromising performance.
Government and defense applications continue to drive demand for high-assurance secure logic chips meeting stringent certification requirements. Military communications systems, classified data processing equipment, and national security infrastructure require chips with advanced features such as side-channel attack resistance and secure key management capabilities.
Healthcare digitization has emerged as another significant market driver, with medical device manufacturers requiring secure logic chips to protect patient data and ensure device integrity. Regulatory compliance requirements such as HIPAA and medical device cybersecurity guidelines are pushing healthcare organizations toward hardware-based security solutions.
The enterprise market shows growing adoption of secure logic chips for data center security, cloud computing infrastructure, and endpoint protection. Organizations are investing in hardware security modules and trusted platform modules to establish hardware roots of trust and protect against advanced persistent threats targeting their digital assets.
Current State of Logic Chip Security Features
The contemporary landscape of logic chip security features reflects a multi-layered approach to addressing evolving cybersecurity threats. Modern processors incorporate hardware-based security mechanisms that operate at the foundational level, providing protection that software-based solutions cannot easily compromise. These features have become essential components in enterprise, government, and consumer applications where data integrity and system security are paramount.
Trusted Platform Modules (TPMs) represent one of the most widely deployed security features in current logic chips. These dedicated cryptographic processors provide hardware-based key generation, storage, and cryptographic operations. TPM 2.0 specifications have standardized implementations across major chip manufacturers, enabling secure boot processes, device attestation, and encrypted storage capabilities. The integration of TPM functionality directly into system-on-chip designs has reduced costs while improving security posture.
Hardware Security Modules (HSMs) embedded within logic chips offer enhanced cryptographic processing capabilities beyond traditional TPMs. These modules provide dedicated secure enclaves for executing sensitive operations, including digital signature generation, certificate management, and secure key exchange protocols. Current implementations support multiple cryptographic algorithms simultaneously, enabling flexible security architectures that can adapt to different threat models and compliance requirements.
Memory protection features have evolved significantly, with current logic chips implementing advanced techniques such as Control Flow Integrity (CFI) and Pointer Authentication. These mechanisms prevent common attack vectors including buffer overflows, return-oriented programming, and code injection attacks. Intel's Control-flow Enforcement Technology (CET) and ARM's Pointer Authentication represent leading implementations that provide runtime protection against memory corruption vulnerabilities.
Secure enclaves and trusted execution environments constitute another critical category of current security features. Intel's Software Guard Extensions (SGX), AMD's Secure Memory Encryption (SME), and ARM's TrustZone technology create isolated execution environments that protect sensitive code and data from privileged software attacks. These technologies enable confidential computing scenarios where applications can process sensitive data without exposing it to the underlying operating system or hypervisor.
Random number generation capabilities have become standard security features in modern logic chips. True Random Number Generators (TRNGs) leverage physical phenomena such as thermal noise or quantum effects to produce cryptographically secure random values. These hardware-based entropy sources are essential for key generation, nonce creation, and other cryptographic operations that require high-quality randomness.
Current logic chips also incorporate side-channel attack mitigation features, addressing vulnerabilities that exploit timing variations, power consumption patterns, or electromagnetic emissions. Techniques such as constant-time execution, power analysis resistance, and electromagnetic shielding are increasingly integrated at the hardware level to prevent information leakage through these indirect channels.
Trusted Platform Modules (TPMs) represent one of the most widely deployed security features in current logic chips. These dedicated cryptographic processors provide hardware-based key generation, storage, and cryptographic operations. TPM 2.0 specifications have standardized implementations across major chip manufacturers, enabling secure boot processes, device attestation, and encrypted storage capabilities. The integration of TPM functionality directly into system-on-chip designs has reduced costs while improving security posture.
Hardware Security Modules (HSMs) embedded within logic chips offer enhanced cryptographic processing capabilities beyond traditional TPMs. These modules provide dedicated secure enclaves for executing sensitive operations, including digital signature generation, certificate management, and secure key exchange protocols. Current implementations support multiple cryptographic algorithms simultaneously, enabling flexible security architectures that can adapt to different threat models and compliance requirements.
Memory protection features have evolved significantly, with current logic chips implementing advanced techniques such as Control Flow Integrity (CFI) and Pointer Authentication. These mechanisms prevent common attack vectors including buffer overflows, return-oriented programming, and code injection attacks. Intel's Control-flow Enforcement Technology (CET) and ARM's Pointer Authentication represent leading implementations that provide runtime protection against memory corruption vulnerabilities.
Secure enclaves and trusted execution environments constitute another critical category of current security features. Intel's Software Guard Extensions (SGX), AMD's Secure Memory Encryption (SME), and ARM's TrustZone technology create isolated execution environments that protect sensitive code and data from privileged software attacks. These technologies enable confidential computing scenarios where applications can process sensitive data without exposing it to the underlying operating system or hypervisor.
Random number generation capabilities have become standard security features in modern logic chips. True Random Number Generators (TRNGs) leverage physical phenomena such as thermal noise or quantum effects to produce cryptographically secure random values. These hardware-based entropy sources are essential for key generation, nonce creation, and other cryptographic operations that require high-quality randomness.
Current logic chips also incorporate side-channel attack mitigation features, addressing vulnerabilities that exploit timing variations, power consumption patterns, or electromagnetic emissions. Techniques such as constant-time execution, power analysis resistance, and electromagnetic shielding are increasingly integrated at the hardware level to prevent information leakage through these indirect channels.
Existing Logic Chip Security Architectures
01 Advanced logic gate architectures and configurations
Logic chips incorporate various gate architectures including multi-input logic gates, configurable logic blocks, and specialized gate arrangements to optimize performance and functionality. These architectures enable efficient signal processing and computational operations through innovative gate designs and interconnection schemes that enhance processing capabilities while reducing power consumption and chip area.- Advanced logic gate architectures and configurations: Logic chips incorporate various gate architectures including multi-input logic gates, configurable logic blocks, and specialized gate arrangements to optimize performance and functionality. These architectures enable efficient Boolean operations and complex logical functions through innovative transistor arrangements and interconnection schemes. The designs focus on reducing propagation delay, minimizing power consumption, and maximizing integration density.
- Programmable and reconfigurable logic structures: Logic chips feature programmable elements that allow dynamic reconfiguration of logic functions after manufacturing. These structures include field-programmable gate arrays, lookup tables, and programmable interconnects that enable users to customize chip functionality for specific applications. The reconfigurability provides flexibility in implementing various logic functions without requiring new chip fabrication.
- Low-power and energy-efficient logic design: Logic chips implement power management techniques including voltage scaling, clock gating, and sleep modes to reduce energy consumption. These features incorporate specialized transistor designs, power domains, and dynamic voltage-frequency scaling mechanisms. The implementations focus on maintaining performance while minimizing static and dynamic power dissipation across various operating conditions.
- High-speed signal processing and timing control: Logic chips incorporate advanced timing circuits, clock distribution networks, and signal synchronization mechanisms to enable high-speed operations. These features include phase-locked loops, delay-locked loops, and precision timing generators that ensure reliable signal propagation and synchronization across the chip. The designs address signal integrity, skew reduction, and jitter minimization for improved performance.
- Integrated testing and fault detection capabilities: Logic chips include built-in self-test circuits, scan chains, and diagnostic features for detecting manufacturing defects and operational faults. These capabilities enable comprehensive testing of logic functions, identification of faulty components, and verification of chip functionality. The integrated testing structures facilitate quality assurance and reliability assessment throughout the chip lifecycle.
02 Programmable and reconfigurable logic structures
Logic chips feature programmable logic elements that allow for dynamic reconfiguration and customization of logic functions. These structures include field-programmable components, lookup tables, and reconfigurable interconnects that enable the chip to adapt to different applications and requirements. The programmability provides flexibility in implementing various logic functions without requiring hardware modifications.Expand Specific Solutions03 Integration of memory elements with logic circuits
Logic chips incorporate integrated memory components such as registers, latches, and embedded memory blocks that work in conjunction with logic circuits. This integration enables efficient data storage and retrieval during logic operations, reducing latency and improving overall chip performance. The memory-logic integration facilitates complex sequential logic operations and state management.Expand Specific Solutions04 Clock distribution and timing control mechanisms
Logic chips employ sophisticated clock distribution networks and timing control systems to ensure synchronized operation across all logic elements. These mechanisms include clock tree structures, phase-locked loops, and delay management circuits that maintain precise timing relationships. The timing control features enable high-speed operation while minimizing timing violations and ensuring reliable data processing.Expand Specific Solutions05 Power management and optimization features
Logic chips incorporate power management capabilities including voltage scaling, power gating, and dynamic power optimization techniques. These features enable selective activation and deactivation of logic blocks based on operational requirements, reducing overall power consumption. The power management systems monitor and control energy usage across different chip regions to balance performance with energy efficiency.Expand Specific Solutions
Major Players in Secure Logic Chip Industry
The cybersecurity logic chip market represents a rapidly evolving sector driven by escalating cyber threats and digital transformation demands. The industry is transitioning from growth to maturity phase, with market size expanding significantly due to increased enterprise security investments and regulatory compliance requirements. Technology maturity varies considerably across market participants. Established semiconductor giants like Intel Corp., Texas Instruments, and Infineon Technologies demonstrate advanced capabilities in secure processing architectures and hardware-based security features. Chinese companies including Huawei Technologies, Beijing Watchdata, and Beijing Smartchip Microelectronics are aggressively developing indigenous security chip solutions, while specialized players like Marvell Israel focus on data infrastructure security. Academic institutions such as Xidian University and Drexel University contribute foundational research in cryptographic hardware implementations. The competitive landscape shows consolidation around key technologies including trusted platform modules, secure enclaves, and AI-enhanced threat detection capabilities, with differentiation increasingly centered on power efficiency, integration complexity, and specialized application optimization.
Intel Corp.
Technical Solution: Intel develops specialized security processors including the Intel Security Engine (Intel SE) and Trust Domain Extensions (TDX) for cybersecurity applications. Their logic chips feature hardware-based security foundations with cryptographic acceleration units, secure boot capabilities, and memory protection extensions. The processors integrate Advanced Encryption Standard New Instructions (AES-NI) for high-performance encryption operations and Intel Software Guard Extensions (SGX) for creating secure enclaves. These chips provide real-time threat detection capabilities through integrated machine learning accelerators and support for virtualization-based security isolation. Intel's cybersecurity logic chips are designed with tamper-resistant hardware security modules and support multiple cryptographic algorithms including RSA, ECC, and post-quantum cryptography standards.
Strengths: Market-leading performance in cryptographic operations, extensive ecosystem support, proven enterprise reliability. Weaknesses: Higher power consumption, premium pricing, complex integration requirements for specialized applications.
Infineon Technologies AG
Technical Solution: Infineon specializes in security controller chips and Trusted Platform Modules (TPM) for cybersecurity applications. Their OPTIGA series provides hardware-based security solutions with integrated cryptographic processors, secure key storage, and authentication capabilities. The chips feature dedicated security processors with tamper detection mechanisms, secure boot loaders, and hardware random number generators. Infineon's logic chips support various security protocols including TLS/SSL acceleration, certificate-based authentication, and secure communication channels. Their security controllers integrate advanced side-channel attack protection and fault injection countermeasures. The chips are designed for IoT security, automotive cybersecurity, and industrial control system protection with low-power consumption and compact form factors suitable for embedded applications.
Strengths: Specialized security expertise, robust tamper protection, optimized for embedded systems, strong automotive market presence. Weaknesses: Limited general-purpose computing capabilities, smaller ecosystem compared to major CPU vendors.
Core Security Features in Modern Logic Chips
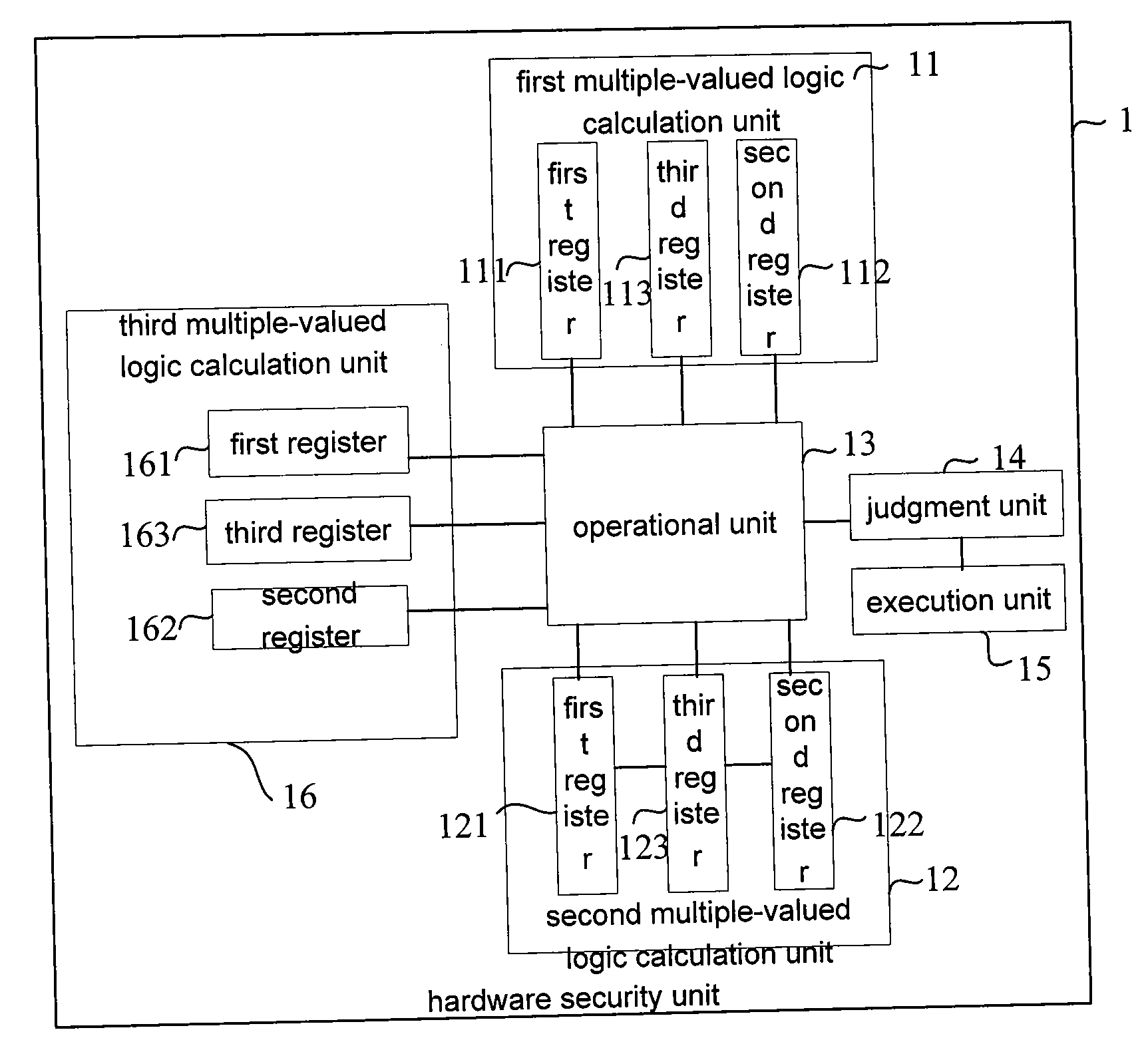
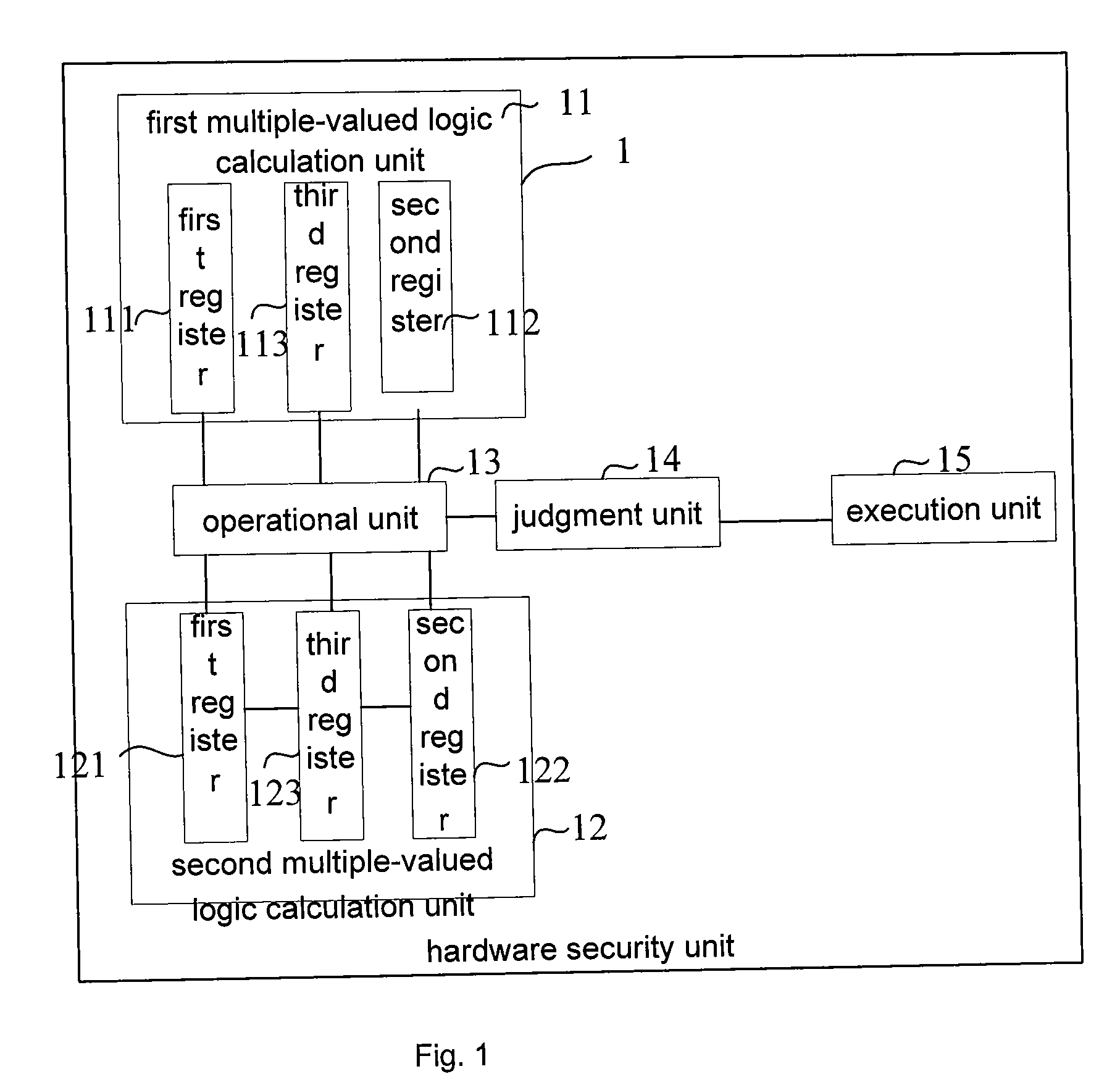
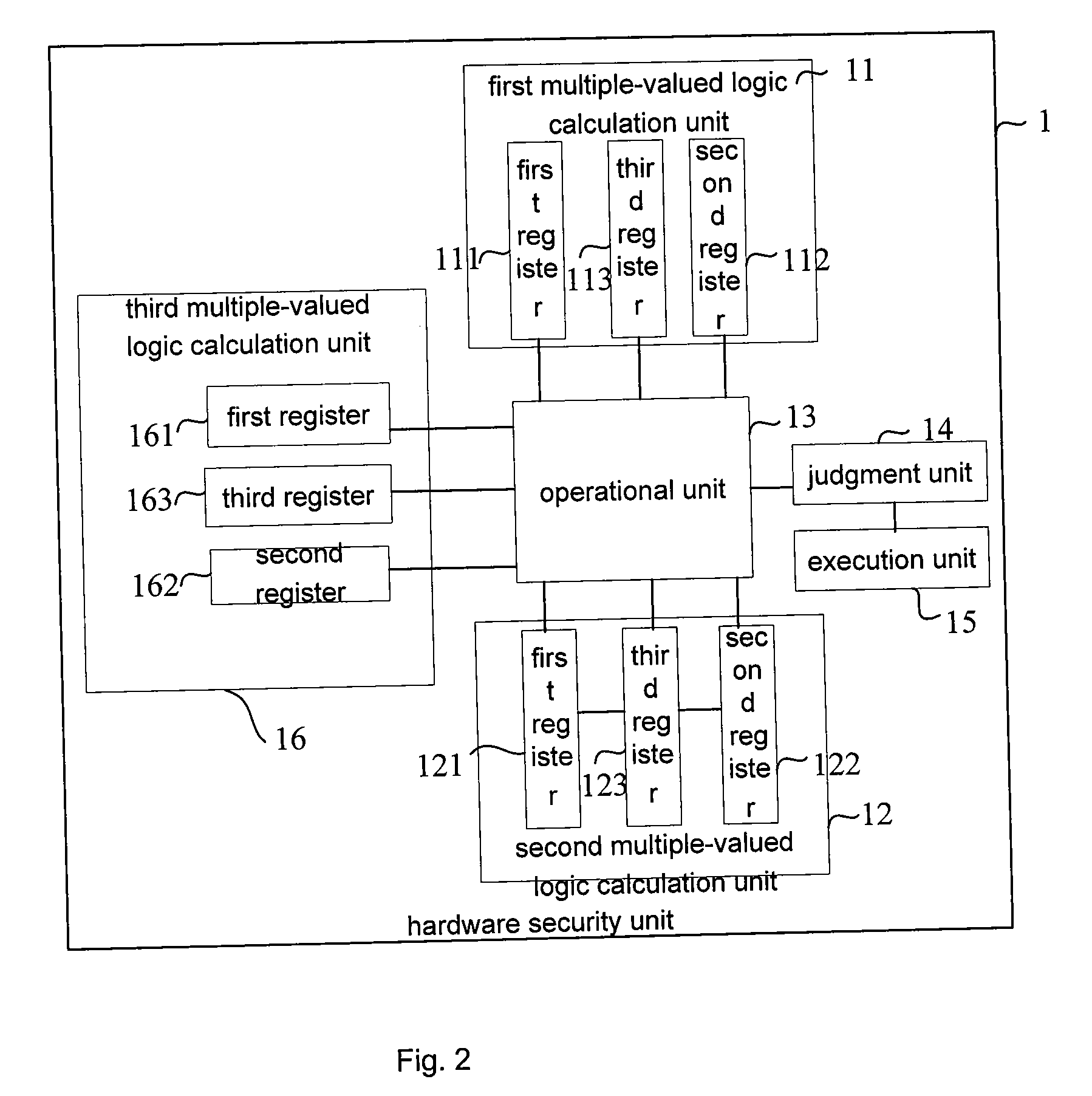
Hardware security unit and multiple-valued logic operational method thereof
PatentInactiveUS20090177616A1
Innovation
- A hardware security unit employing multiple-valued logic calculation units with registers for expected and current logical states and operators, allowing for flexible logic operations and user-defined settings, judgments, and executions to accommodate different security levels and environments.
Secure access to memory in an integrated circuit
PatentWO2025056971A1
Innovation
- An integrated circuit (IC) chip architecture that provides a processor external to the IC chip with both unsecured access to first memories and secured access to second memories via a single communication interface. The IC chip includes embedded hardware security circuitry that authenticates the processor and selectively provides secure access to the second memories, which store sensitive information such as security keys.
Security Standards and Certification Requirements
Logic chips designed for cybersecurity applications must adhere to stringent security standards and certification requirements that ensure their reliability, integrity, and resistance to various attack vectors. These requirements form the foundation for evaluating and comparing different chip solutions in the cybersecurity domain.
The Common Criteria (CC) framework represents one of the most widely recognized international standards for security evaluation, providing Evaluation Assurance Levels (EAL1 through EAL7) that define the depth and rigor of security testing. Logic chips targeting high-security applications typically require EAL4 or higher certification, which involves comprehensive vulnerability assessments, penetration testing, and formal security model verification.
FIPS 140-2 and its successor FIPS 140-3 establish critical benchmarks for cryptographic modules, defining four security levels that address physical security, cryptographic key management, and tamper resistance. Level 3 and Level 4 certifications are particularly relevant for cybersecurity logic chips, requiring advanced tamper detection mechanisms and environmental failure protection capabilities.
Industry-specific standards further shape certification requirements. The Trusted Computing Group (TCG) specifications define Trusted Platform Module (TPM) requirements for hardware-based security anchors. ISO/IEC 15408 provides additional evaluation criteria for information technology security, while NIST cybersecurity frameworks offer comprehensive guidelines for risk management and security controls implementation.
Certification processes typically involve extensive third-party testing laboratories that conduct side-channel analysis, fault injection testing, and electromagnetic compatibility assessments. These evaluations examine power consumption patterns, timing variations, and electromagnetic emissions that could potentially leak sensitive information or create vulnerabilities.
Compliance with these standards significantly impacts chip design decisions, manufacturing processes, and supply chain management. Manufacturers must implement robust quality assurance programs, maintain detailed documentation throughout the development lifecycle, and establish secure manufacturing environments to meet certification requirements. The certification timeline often extends 12-18 months, requiring early integration into product development schedules and substantial financial investment for comprehensive testing and validation procedures.
The Common Criteria (CC) framework represents one of the most widely recognized international standards for security evaluation, providing Evaluation Assurance Levels (EAL1 through EAL7) that define the depth and rigor of security testing. Logic chips targeting high-security applications typically require EAL4 or higher certification, which involves comprehensive vulnerability assessments, penetration testing, and formal security model verification.
FIPS 140-2 and its successor FIPS 140-3 establish critical benchmarks for cryptographic modules, defining four security levels that address physical security, cryptographic key management, and tamper resistance. Level 3 and Level 4 certifications are particularly relevant for cybersecurity logic chips, requiring advanced tamper detection mechanisms and environmental failure protection capabilities.
Industry-specific standards further shape certification requirements. The Trusted Computing Group (TCG) specifications define Trusted Platform Module (TPM) requirements for hardware-based security anchors. ISO/IEC 15408 provides additional evaluation criteria for information technology security, while NIST cybersecurity frameworks offer comprehensive guidelines for risk management and security controls implementation.
Certification processes typically involve extensive third-party testing laboratories that conduct side-channel analysis, fault injection testing, and electromagnetic compatibility assessments. These evaluations examine power consumption patterns, timing variations, and electromagnetic emissions that could potentially leak sensitive information or create vulnerabilities.
Compliance with these standards significantly impacts chip design decisions, manufacturing processes, and supply chain management. Manufacturers must implement robust quality assurance programs, maintain detailed documentation throughout the development lifecycle, and establish secure manufacturing environments to meet certification requirements. The certification timeline often extends 12-18 months, requiring early integration into product development schedules and substantial financial investment for comprehensive testing and validation procedures.
Supply Chain Security for Logic Chip Manufacturing
Supply chain security in logic chip manufacturing represents a critical vulnerability vector that directly impacts cybersecurity applications. The complexity of modern semiconductor supply chains, spanning multiple countries and involving numerous suppliers, creates extensive attack surfaces where malicious actors can introduce hardware trojans, counterfeit components, or compromised firmware during various manufacturing stages.
The geographic distribution of chip manufacturing facilities across different geopolitical regions introduces significant security risks. Major foundries located in Taiwan, South Korea, and China handle production for chips destined for critical cybersecurity infrastructure, creating dependencies that can be exploited through state-sponsored attacks or industrial espionage. This geographical concentration means that a single compromised facility could affect thousands of cybersecurity products globally.
Third-party intellectual property integration poses another substantial risk factor. Logic chips for cybersecurity applications often incorporate IP blocks from multiple vendors, creating blind spots where malicious code or hardware modifications can be embedded without detection. The lack of comprehensive visibility into these third-party components makes it extremely difficult to verify the integrity of the final product.
Manufacturing process vulnerabilities extend beyond intentional attacks to include unintentional security weaknesses. Inadequate quality control, insufficient testing protocols, and limited traceability systems can result in chips with exploitable flaws reaching cybersecurity applications. These vulnerabilities may remain dormant until activated by specific triggers or discovered by adversaries.
The verification and validation challenges in supply chain security are particularly acute for cybersecurity logic chips. Traditional testing methods often fail to detect sophisticated hardware trojans designed to activate only under specific conditions. Advanced persistent threats targeting the supply chain require new detection methodologies, including machine learning-based anomaly detection and comprehensive behavioral analysis of manufactured chips.
Regulatory frameworks and industry standards are evolving to address these challenges, with initiatives like the NIST Cybersecurity Framework and emerging supply chain security requirements. However, implementation remains inconsistent across the industry, creating gaps that adversaries can exploit to compromise cybersecurity applications through supply chain infiltration.
The geographic distribution of chip manufacturing facilities across different geopolitical regions introduces significant security risks. Major foundries located in Taiwan, South Korea, and China handle production for chips destined for critical cybersecurity infrastructure, creating dependencies that can be exploited through state-sponsored attacks or industrial espionage. This geographical concentration means that a single compromised facility could affect thousands of cybersecurity products globally.
Third-party intellectual property integration poses another substantial risk factor. Logic chips for cybersecurity applications often incorporate IP blocks from multiple vendors, creating blind spots where malicious code or hardware modifications can be embedded without detection. The lack of comprehensive visibility into these third-party components makes it extremely difficult to verify the integrity of the final product.
Manufacturing process vulnerabilities extend beyond intentional attacks to include unintentional security weaknesses. Inadequate quality control, insufficient testing protocols, and limited traceability systems can result in chips with exploitable flaws reaching cybersecurity applications. These vulnerabilities may remain dormant until activated by specific triggers or discovered by adversaries.
The verification and validation challenges in supply chain security are particularly acute for cybersecurity logic chips. Traditional testing methods often fail to detect sophisticated hardware trojans designed to activate only under specific conditions. Advanced persistent threats targeting the supply chain require new detection methodologies, including machine learning-based anomaly detection and comprehensive behavioral analysis of manufactured chips.
Regulatory frameworks and industry standards are evolving to address these challenges, with initiatives like the NIST Cybersecurity Framework and emerging supply chain security requirements. However, implementation remains inconsistent across the industry, creating gaps that adversaries can exploit to compromise cybersecurity applications through supply chain infiltration.
Unlock deeper insights with Patsnap Eureka Quick Research — get a full tech report to explore trends and direct your research. Try now!
Generate Your Research Report Instantly with AI Agent
Supercharge your innovation with Patsnap Eureka AI Agent Platform!