How to Integrate Robust Security for Three Phase Electric Power
MAR 18, 20269 MIN READ
Generate Your Research Report Instantly with AI Agent
PatSnap Eureka helps you evaluate technical feasibility & market potential.
Three Phase Power Security Background and Objectives
Three-phase electric power systems form the backbone of global electrical infrastructure, delivering power from generation facilities to industrial, commercial, and residential consumers. These systems operate through three alternating current waveforms, each phase shifted by 120 degrees, providing efficient power transmission and balanced load distribution. However, the increasing digitization of power grids and the integration of smart technologies have introduced unprecedented security vulnerabilities that threaten the stability and reliability of electrical networks worldwide.
The evolution of power systems from purely mechanical and analog operations to digitally controlled smart grids has fundamentally transformed the security landscape. Traditional three-phase systems relied primarily on physical protection mechanisms such as circuit breakers, fuses, and mechanical relays. Today's power infrastructure incorporates sophisticated digital control systems, communication networks, and automated monitoring devices that, while enhancing operational efficiency, create multiple entry points for cyber threats and malicious attacks.
Recent incidents have demonstrated the critical importance of robust security integration in power systems. The 2015 Ukraine power grid attack, which left hundreds of thousands without electricity, highlighted how cybersecurity vulnerabilities in power infrastructure can have devastating real-world consequences. Similarly, the 2021 Colonial Pipeline ransomware attack underscored the interconnected nature of critical infrastructure and the cascading effects of security breaches on essential services.
The primary objective of integrating robust security into three-phase electric power systems is to establish comprehensive protection against both cyber and physical threats while maintaining operational efficiency and system reliability. This involves developing multi-layered security architectures that can detect, prevent, and respond to various attack vectors including unauthorized access, data manipulation, equipment tampering, and service disruption attempts.
Key security objectives include ensuring the confidentiality of operational data and control communications, maintaining the integrity of power system operations and measurements, and guaranteeing the availability of electrical services under various threat scenarios. Additionally, security integration must address the unique challenges of power systems, including real-time operational requirements, legacy equipment compatibility, and the need for seamless integration without compromising system performance or introducing operational delays that could affect power quality and stability.
The strategic importance of this security integration extends beyond individual utility companies to encompass national security, economic stability, and public safety considerations, making it a critical priority for governments, regulatory bodies, and industry stakeholders worldwide.
The evolution of power systems from purely mechanical and analog operations to digitally controlled smart grids has fundamentally transformed the security landscape. Traditional three-phase systems relied primarily on physical protection mechanisms such as circuit breakers, fuses, and mechanical relays. Today's power infrastructure incorporates sophisticated digital control systems, communication networks, and automated monitoring devices that, while enhancing operational efficiency, create multiple entry points for cyber threats and malicious attacks.
Recent incidents have demonstrated the critical importance of robust security integration in power systems. The 2015 Ukraine power grid attack, which left hundreds of thousands without electricity, highlighted how cybersecurity vulnerabilities in power infrastructure can have devastating real-world consequences. Similarly, the 2021 Colonial Pipeline ransomware attack underscored the interconnected nature of critical infrastructure and the cascading effects of security breaches on essential services.
The primary objective of integrating robust security into three-phase electric power systems is to establish comprehensive protection against both cyber and physical threats while maintaining operational efficiency and system reliability. This involves developing multi-layered security architectures that can detect, prevent, and respond to various attack vectors including unauthorized access, data manipulation, equipment tampering, and service disruption attempts.
Key security objectives include ensuring the confidentiality of operational data and control communications, maintaining the integrity of power system operations and measurements, and guaranteeing the availability of electrical services under various threat scenarios. Additionally, security integration must address the unique challenges of power systems, including real-time operational requirements, legacy equipment compatibility, and the need for seamless integration without compromising system performance or introducing operational delays that could affect power quality and stability.
The strategic importance of this security integration extends beyond individual utility companies to encompass national security, economic stability, and public safety considerations, making it a critical priority for governments, regulatory bodies, and industry stakeholders worldwide.
Market Demand for Secure Three Phase Power Systems
The global demand for secure three-phase power systems has experienced unprecedented growth driven by the increasing digitization of industrial operations and the critical need for uninterrupted power supply across manufacturing, healthcare, data centers, and smart grid infrastructure. Traditional three-phase power systems, while efficient for power distribution, face mounting security vulnerabilities as they become increasingly interconnected with digital control systems and IoT devices.
Industrial sectors represent the largest market segment for secure three-phase power solutions, with manufacturing facilities requiring robust protection against both physical tampering and cyber intrusions. The automotive industry, semiconductor fabrication plants, and chemical processing facilities demand continuous power availability with integrated security monitoring to prevent production disruptions that could result in significant financial losses.
Healthcare institutions constitute another rapidly expanding market segment, where secure three-phase power systems are essential for operating critical medical equipment, surgical suites, and life support systems. The integration of security features ensures protection against malicious attacks while maintaining the reliability standards required for patient safety and regulatory compliance.
Data centers and cloud computing facilities drive substantial demand for secure power infrastructure, as these facilities require not only reliable three-phase power distribution but also comprehensive security measures to protect against sophisticated cyber threats targeting power management systems. The growing adoption of edge computing and distributed data processing further amplifies this demand.
Smart grid modernization initiatives across developed and emerging economies create significant market opportunities for secure three-phase power systems. Utility companies are increasingly investing in power infrastructure that incorporates advanced security protocols to protect against grid-scale attacks and ensure system resilience.
The renewable energy sector presents emerging demand patterns, particularly in wind farms and solar installations where three-phase power systems must integrate security features to protect against unauthorized access and ensure stable grid integration. Energy storage systems and electric vehicle charging infrastructure also contribute to expanding market requirements for secure power solutions.
Regulatory frameworks and compliance standards across different regions are driving mandatory adoption of security-enhanced power systems, creating sustained market demand beyond voluntary technology upgrades.
Industrial sectors represent the largest market segment for secure three-phase power solutions, with manufacturing facilities requiring robust protection against both physical tampering and cyber intrusions. The automotive industry, semiconductor fabrication plants, and chemical processing facilities demand continuous power availability with integrated security monitoring to prevent production disruptions that could result in significant financial losses.
Healthcare institutions constitute another rapidly expanding market segment, where secure three-phase power systems are essential for operating critical medical equipment, surgical suites, and life support systems. The integration of security features ensures protection against malicious attacks while maintaining the reliability standards required for patient safety and regulatory compliance.
Data centers and cloud computing facilities drive substantial demand for secure power infrastructure, as these facilities require not only reliable three-phase power distribution but also comprehensive security measures to protect against sophisticated cyber threats targeting power management systems. The growing adoption of edge computing and distributed data processing further amplifies this demand.
Smart grid modernization initiatives across developed and emerging economies create significant market opportunities for secure three-phase power systems. Utility companies are increasingly investing in power infrastructure that incorporates advanced security protocols to protect against grid-scale attacks and ensure system resilience.
The renewable energy sector presents emerging demand patterns, particularly in wind farms and solar installations where three-phase power systems must integrate security features to protect against unauthorized access and ensure stable grid integration. Energy storage systems and electric vehicle charging infrastructure also contribute to expanding market requirements for secure power solutions.
Regulatory frameworks and compliance standards across different regions are driving mandatory adoption of security-enhanced power systems, creating sustained market demand beyond voluntary technology upgrades.
Current Security Vulnerabilities in Three Phase Power Infrastructure
Three-phase electric power infrastructure faces numerous security vulnerabilities that pose significant risks to grid stability and operational continuity. These vulnerabilities span across physical, cyber, and operational domains, creating multiple attack vectors that malicious actors can exploit to disrupt power delivery systems.
Physical security vulnerabilities represent the most direct threat to three-phase power systems. Substations, transmission lines, and distribution equipment are often located in remote or poorly monitored areas, making them susceptible to sabotage, theft, and vandalism. Critical components such as transformers, switchgear, and protective relays can be physically damaged or tampered with, leading to cascading failures across the power grid. The lack of comprehensive perimeter security and inadequate surveillance systems further exacerbate these risks.
Cyber security threats have emerged as increasingly sophisticated challenges for modern power infrastructure. Legacy SCADA systems and industrial control networks were originally designed without robust cybersecurity considerations, leaving them vulnerable to remote attacks. Weak authentication protocols, unencrypted communications, and outdated software create entry points for cybercriminals and state-sponsored actors. The integration of smart grid technologies and IoT devices has expanded the attack surface, introducing new vulnerabilities through interconnected systems.
Communication network vulnerabilities pose additional risks to three-phase power systems. Many power utilities rely on aging communication infrastructure that lacks proper encryption and authentication mechanisms. Wireless communication links used for remote monitoring and control can be intercepted or jammed, compromising system visibility and operational control. The increasing dependence on internet-based communication protocols introduces additional exposure to network-based attacks.
Operational vulnerabilities stem from inadequate security procedures and insufficient personnel training. Many power system operators lack comprehensive cybersecurity awareness, making them susceptible to social engineering attacks and phishing attempts. Inadequate access control policies and poor credential management practices create opportunities for unauthorized system access. The complexity of modern power systems often results in configuration errors and security misconfigurations that can be exploited by attackers.
Supply chain vulnerabilities represent an emerging threat vector that affects the integrity of power system components. Compromised hardware or software introduced during manufacturing or installation can create backdoors for future attacks. The global nature of power equipment supply chains makes it difficult to ensure the security and authenticity of critical components throughout their lifecycle.
Physical security vulnerabilities represent the most direct threat to three-phase power systems. Substations, transmission lines, and distribution equipment are often located in remote or poorly monitored areas, making them susceptible to sabotage, theft, and vandalism. Critical components such as transformers, switchgear, and protective relays can be physically damaged or tampered with, leading to cascading failures across the power grid. The lack of comprehensive perimeter security and inadequate surveillance systems further exacerbate these risks.
Cyber security threats have emerged as increasingly sophisticated challenges for modern power infrastructure. Legacy SCADA systems and industrial control networks were originally designed without robust cybersecurity considerations, leaving them vulnerable to remote attacks. Weak authentication protocols, unencrypted communications, and outdated software create entry points for cybercriminals and state-sponsored actors. The integration of smart grid technologies and IoT devices has expanded the attack surface, introducing new vulnerabilities through interconnected systems.
Communication network vulnerabilities pose additional risks to three-phase power systems. Many power utilities rely on aging communication infrastructure that lacks proper encryption and authentication mechanisms. Wireless communication links used for remote monitoring and control can be intercepted or jammed, compromising system visibility and operational control. The increasing dependence on internet-based communication protocols introduces additional exposure to network-based attacks.
Operational vulnerabilities stem from inadequate security procedures and insufficient personnel training. Many power system operators lack comprehensive cybersecurity awareness, making them susceptible to social engineering attacks and phishing attempts. Inadequate access control policies and poor credential management practices create opportunities for unauthorized system access. The complexity of modern power systems often results in configuration errors and security misconfigurations that can be exploited by attackers.
Supply chain vulnerabilities represent an emerging threat vector that affects the integrity of power system components. Compromised hardware or software introduced during manufacturing or installation can create backdoors for future attacks. The global nature of power equipment supply chains makes it difficult to ensure the security and authenticity of critical components throughout their lifecycle.
Existing Security Solutions for Three Phase Power Systems
01 Protection and monitoring systems for three-phase power networks
Advanced protection systems are designed to monitor three-phase electrical power networks and detect abnormal conditions such as voltage imbalances, phase failures, and overcurrent situations. These systems employ sophisticated algorithms and sensors to continuously assess the health of the power system and trigger protective actions when necessary. The monitoring capabilities include real-time analysis of voltage, current, and frequency parameters across all three phases to ensure system stability and prevent equipment damage.- Three-phase power monitoring and protection systems: Advanced monitoring systems are designed to continuously track three-phase electrical parameters including voltage, current, and frequency. These systems incorporate protective mechanisms that can detect abnormalities such as phase imbalances, overcurrent conditions, and voltage fluctuations. When anomalies are detected, the systems can automatically trigger protective actions such as circuit disconnection or alarm notifications to prevent equipment damage and ensure operational safety.
- Phase sequence detection and correction devices: Specialized devices are employed to detect and verify the correct phase sequence in three-phase power systems. These devices can identify incorrect phase connections that could lead to motor rotation in the wrong direction or equipment malfunction. Some advanced systems include automatic correction capabilities that can adjust phase sequences without manual intervention, ensuring proper system operation and preventing potential damage to connected equipment.
- Fault detection and isolation mechanisms: Comprehensive fault detection systems are integrated into three-phase power networks to identify various types of electrical faults including short circuits, ground faults, and phase-to-phase faults. These mechanisms utilize sophisticated algorithms and sensor networks to quickly locate and isolate faulty sections, minimizing downtime and preventing cascading failures. The systems can differentiate between temporary and permanent faults, enabling appropriate response strategies.
- Load balancing and power quality management: Technologies for managing load distribution across three phases ensure optimal power utilization and prevent overloading of individual phases. These systems monitor real-time load conditions and can dynamically redistribute loads to maintain balance. Additionally, power quality management features address issues such as harmonics, power factor correction, and voltage regulation to ensure stable and efficient power delivery while protecting sensitive equipment from power quality disturbances.
- Cybersecurity and communication protection for power systems: Modern three-phase power systems incorporate cybersecurity measures to protect against digital threats and unauthorized access. These include encrypted communication protocols, secure authentication mechanisms, and intrusion detection systems. The protection extends to supervisory control and data acquisition systems, ensuring that remote monitoring and control functions remain secure. These measures prevent cyber attacks that could compromise power system integrity and operational continuity.
02 Fault detection and isolation mechanisms
Specialized fault detection technologies are implemented to identify and isolate faults in three-phase power systems. These mechanisms can quickly detect short circuits, ground faults, and phase-to-phase faults, enabling rapid isolation of affected sections to minimize downtime and prevent cascading failures. The systems utilize advanced signal processing techniques and intelligent switching devices to automatically disconnect faulty segments while maintaining power supply to unaffected areas.Expand Specific Solutions03 Power quality management and harmonic filtering
Power quality enhancement solutions address issues related to harmonics, voltage fluctuations, and power factor correction in three-phase systems. These technologies employ active and passive filtering techniques to eliminate harmonic distortions that can damage sensitive equipment and reduce system efficiency. The systems also include voltage regulation capabilities to maintain stable power supply despite load variations and grid disturbances.Expand Specific Solutions04 Load balancing and phase management
Load balancing technologies ensure equal distribution of electrical load across all three phases to prevent overloading of individual phases and optimize system performance. These solutions include automatic phase switching mechanisms and intelligent load distribution algorithms that dynamically adjust power allocation based on real-time demand. The systems help reduce energy losses, prevent equipment overheating, and extend the lifespan of electrical infrastructure.Expand Specific Solutions05 Cybersecurity and communication protection for power systems
Security measures are implemented to protect three-phase power systems from cyber threats and unauthorized access. These solutions include encrypted communication protocols, secure data transmission methods, and authentication mechanisms for remote monitoring and control systems. The technologies also incorporate intrusion detection systems and firewalls specifically designed for industrial control systems to prevent malicious attacks that could compromise power system operations.Expand Specific Solutions
Key Players in Power Security and Grid Protection Industry
The three-phase electric power security market is experiencing rapid growth driven by increasing cybersecurity threats and grid modernization initiatives. The industry is in a mature expansion phase, with market size projected to reach significant scale as utilities prioritize infrastructure protection. Technology maturity varies across segments, with established players like Siemens AG, IBM, and Hitachi Energy leading through comprehensive security platforms integrating AI-driven threat detection and real-time monitoring. Regional specialists such as Delta Electronics and Chinese state grid companies are advancing localized solutions, while emerging innovators like IONATE Ltd are developing next-generation hybrid intelligent transformers with embedded security features. The competitive landscape shows convergence between traditional power equipment manufacturers and cybersecurity specialists, creating integrated hardware-software solutions that address both operational technology and information technology security requirements for modern three-phase power systems.
Siemens AG
Technical Solution: Siemens provides comprehensive cybersecurity solutions for three-phase electric power systems through their SICAM GridEdge platform and DIGSI 5 protection software. Their approach integrates IEC 62351 security standards with advanced encryption protocols for SCADA communications. The system employs multi-layered security architecture including secure authentication, encrypted data transmission, and real-time threat detection capabilities. Their solutions feature hardware security modules (HSMs) for cryptographic key management and support role-based access control with digital certificates. The platform includes intrusion detection systems specifically designed for power grid environments and provides secure remote access capabilities for maintenance operations while maintaining operational technology (OT) network isolation.
Strengths: Industry-leading compliance with IEC 62351 standards, extensive experience in critical infrastructure protection, comprehensive end-to-end security solutions. Weaknesses: High implementation costs, complex integration requirements, potential vendor lock-in scenarios.
International Business Machines Corp.
Technical Solution: IBM provides security solutions for three-phase electric power systems through their IBM Security QRadar SIEM platform and Watson IoT for Energy. Their approach leverages artificial intelligence and machine learning for predictive threat analysis and automated incident response in power grid environments. The system integrates with existing SCADA and DCS systems to provide real-time security monitoring and threat intelligence. Their solution includes advanced analytics for detecting sophisticated persistent threats, encrypted communication channels, and blockchain-based authentication mechanisms. The platform supports compliance with multiple regulatory frameworks and provides comprehensive security orchestration capabilities with automated remediation workflows specifically designed for critical power infrastructure operations.
Strengths: Advanced AI and machine learning capabilities, extensive cybersecurity expertise, strong enterprise-grade security solutions. Weaknesses: High complexity requiring significant IT resources, potentially over-engineered for smaller power systems.
Core Innovations in Three Phase Power Cybersecurity
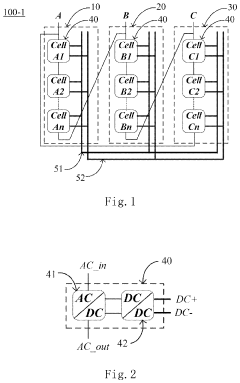
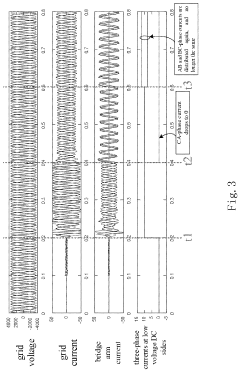
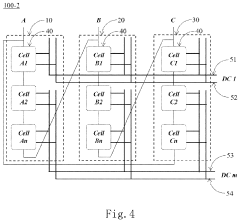
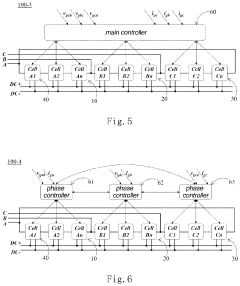
Three-phase power supply system and power supply method
PatentActiveUS20210391724A1
Innovation
- A three-phase power supply system with a delta connection architecture, where each phase branch comprises multiple power conversion cells connected in parallel, allowing for regulation of active and reactive powers to maintain three-phase current balance without injecting negative-sequence or reactive currents, enabling four-quadrant operation even when one phase branch fails.
Three-phase power supply conversion circuit for household appliance, household appliance, and power-on control method
PatentPendingUS20250132663A1
Innovation
- A three-phase power conversion circuit with a three-level active Power Factor Correction (PFC) unit and power-on units that include controllable switch modules. The control unit manages the switching of these modules to buffer devices during power-on, preventing overvoltage damage.
Regulatory Framework for Critical Power Infrastructure Security
The regulatory framework governing critical power infrastructure security has evolved significantly in response to growing cybersecurity threats and the increasing digitization of electrical grid systems. In the United States, the North American Electric Reliability Corporation (NERC) Critical Infrastructure Protection (CIP) standards serve as the primary regulatory foundation, establishing mandatory cybersecurity requirements for bulk electric system operators. These standards specifically address three-phase power system security through comprehensive asset identification, security controls, and incident response protocols.
The Federal Energy Regulatory Commission (FERC) provides oversight authority, ensuring compliance with NERC CIP standards while adapting regulations to address emerging threats. Recent regulatory updates have expanded the scope of critical cyber assets to include distributed energy resources and advanced metering infrastructure that interact with three-phase power systems. The Department of Energy's Cybersecurity, Energy Security, and Emergency Response (CESER) office coordinates national-level policy initiatives and provides additional guidance for critical infrastructure protection.
International regulatory frameworks demonstrate varying approaches to three-phase power security. The European Union's Network and Information Systems (NIS) Directive establishes security requirements for essential services, including electricity supply operators. The directive emphasizes risk management approaches and incident notification requirements that directly impact three-phase power infrastructure security implementations.
Regulatory compliance requirements increasingly mandate specific technical controls for three-phase power systems, including network segmentation, access controls, and continuous monitoring capabilities. The NERC CIP-007 standard specifically requires system security management for cyber assets associated with bulk electric system operations, encompassing patch management, malware prevention, and security event monitoring for three-phase power control systems.
Emerging regulatory trends indicate a shift toward performance-based standards rather than prescriptive technical requirements. This evolution allows utilities greater flexibility in implementing security measures while maintaining accountability for protecting three-phase power infrastructure against sophisticated cyber threats and ensuring grid reliability.
The Federal Energy Regulatory Commission (FERC) provides oversight authority, ensuring compliance with NERC CIP standards while adapting regulations to address emerging threats. Recent regulatory updates have expanded the scope of critical cyber assets to include distributed energy resources and advanced metering infrastructure that interact with three-phase power systems. The Department of Energy's Cybersecurity, Energy Security, and Emergency Response (CESER) office coordinates national-level policy initiatives and provides additional guidance for critical infrastructure protection.
International regulatory frameworks demonstrate varying approaches to three-phase power security. The European Union's Network and Information Systems (NIS) Directive establishes security requirements for essential services, including electricity supply operators. The directive emphasizes risk management approaches and incident notification requirements that directly impact three-phase power infrastructure security implementations.
Regulatory compliance requirements increasingly mandate specific technical controls for three-phase power systems, including network segmentation, access controls, and continuous monitoring capabilities. The NERC CIP-007 standard specifically requires system security management for cyber assets associated with bulk electric system operations, encompassing patch management, malware prevention, and security event monitoring for three-phase power control systems.
Emerging regulatory trends indicate a shift toward performance-based standards rather than prescriptive technical requirements. This evolution allows utilities greater flexibility in implementing security measures while maintaining accountability for protecting three-phase power infrastructure against sophisticated cyber threats and ensuring grid reliability.
Risk Assessment and Threat Modeling for Power Systems
Risk assessment and threat modeling represent fundamental pillars in establishing comprehensive security frameworks for three-phase electric power systems. These methodologies provide systematic approaches to identify, analyze, and prioritize potential vulnerabilities across the entire power infrastructure ecosystem. The complexity of modern power grids, with their interconnected generation, transmission, and distribution networks, necessitates sophisticated assessment techniques that can capture both traditional operational risks and emerging cybersecurity threats.
Contemporary risk assessment frameworks for power systems typically employ multi-layered analytical approaches that examine threats across physical, cyber, and operational domains. Physical threats encompass natural disasters, equipment failures, and deliberate sabotage targeting critical infrastructure components such as transformers, substations, and transmission lines. Cyber threats have evolved significantly, ranging from advanced persistent threats targeting SCADA systems to sophisticated attacks on smart grid communications protocols and industrial control systems.
Threat modeling methodologies specifically designed for power systems utilize structured frameworks such as STRIDE, PASTA, and OCTAVE, adapted to address the unique characteristics of electrical infrastructure. These models systematically decompose power system architectures into discrete components, analyzing potential attack vectors, threat actors, and impact scenarios. The modeling process considers various threat actors, including nation-state adversaries, cybercriminal organizations, insider threats, and terrorist groups, each with distinct motivations, capabilities, and preferred attack methodologies.
Quantitative risk assessment techniques increasingly incorporate probabilistic models and Monte Carlo simulations to evaluate the likelihood and potential impact of various threat scenarios. These assessments consider cascading failure mechanisms, where initial security breaches or physical attacks can propagate throughout interconnected power networks, potentially causing widespread blackouts or system instability. Advanced modeling approaches integrate real-time operational data, historical incident patterns, and threat intelligence feeds to provide dynamic risk assessments that adapt to changing threat landscapes.
The integration of artificial intelligence and machine learning technologies has enhanced threat detection capabilities, enabling predictive risk assessment models that can identify anomalous patterns indicative of potential security breaches. These systems analyze vast datasets from multiple sources, including network traffic, operational parameters, and external threat intelligence, to provide early warning capabilities and support proactive security measures for three-phase power system protection.
Contemporary risk assessment frameworks for power systems typically employ multi-layered analytical approaches that examine threats across physical, cyber, and operational domains. Physical threats encompass natural disasters, equipment failures, and deliberate sabotage targeting critical infrastructure components such as transformers, substations, and transmission lines. Cyber threats have evolved significantly, ranging from advanced persistent threats targeting SCADA systems to sophisticated attacks on smart grid communications protocols and industrial control systems.
Threat modeling methodologies specifically designed for power systems utilize structured frameworks such as STRIDE, PASTA, and OCTAVE, adapted to address the unique characteristics of electrical infrastructure. These models systematically decompose power system architectures into discrete components, analyzing potential attack vectors, threat actors, and impact scenarios. The modeling process considers various threat actors, including nation-state adversaries, cybercriminal organizations, insider threats, and terrorist groups, each with distinct motivations, capabilities, and preferred attack methodologies.
Quantitative risk assessment techniques increasingly incorporate probabilistic models and Monte Carlo simulations to evaluate the likelihood and potential impact of various threat scenarios. These assessments consider cascading failure mechanisms, where initial security breaches or physical attacks can propagate throughout interconnected power networks, potentially causing widespread blackouts or system instability. Advanced modeling approaches integrate real-time operational data, historical incident patterns, and threat intelligence feeds to provide dynamic risk assessments that adapt to changing threat landscapes.
The integration of artificial intelligence and machine learning technologies has enhanced threat detection capabilities, enabling predictive risk assessment models that can identify anomalous patterns indicative of potential security breaches. These systems analyze vast datasets from multiple sources, including network traffic, operational parameters, and external threat intelligence, to provide early warning capabilities and support proactive security measures for three-phase power system protection.
Unlock deeper insights with PatSnap Eureka Quick Research — get a full tech report to explore trends and direct your research. Try now!
Generate Your Research Report Instantly with AI Agent
Supercharge your innovation with PatSnap Eureka AI Agent Platform!