Network Anomaly Detection through Adaptive Network Control
MAR 18, 20269 MIN READ
Generate Your Research Report Instantly with AI Agent
PatSnap Eureka helps you evaluate technical feasibility & market potential.
Adaptive Network Control Background and Objectives
Adaptive network control has emerged as a critical paradigm in modern network management, evolving from traditional static network configurations to dynamic, intelligent systems capable of real-time optimization. This technological evolution stems from the increasing complexity of network infrastructures, the proliferation of connected devices, and the growing demand for reliable, high-performance network services across diverse applications ranging from enterprise communications to IoT deployments.
The historical development of adaptive network control can be traced back to early quality of service (QoS) mechanisms in the 1990s, which provided basic traffic prioritization capabilities. However, these systems lacked the sophistication to handle complex, multi-dimensional network optimization challenges. The advent of software-defined networking (SDN) in the 2000s marked a pivotal milestone, introducing programmable network control planes that enabled centralized management and dynamic policy enforcement.
Contemporary adaptive network control systems leverage machine learning algorithms, artificial intelligence, and advanced analytics to continuously monitor network conditions and automatically adjust parameters such as routing paths, bandwidth allocation, traffic shaping policies, and security configurations. These systems represent a fundamental shift from reactive network management to proactive, predictive control mechanisms that can anticipate and mitigate potential issues before they impact network performance.
The primary objective of integrating adaptive network control with anomaly detection is to create self-healing network infrastructures that can identify, isolate, and respond to security threats and performance degradations in real-time. This integration aims to minimize human intervention while maximizing network reliability, security, and efficiency. Key technical goals include achieving sub-second response times to detected anomalies, maintaining network performance during adaptive control actions, and ensuring scalability across diverse network topologies.
Modern adaptive control systems target several critical objectives: enhancing network resilience against both malicious attacks and benign failures, optimizing resource utilization through intelligent traffic engineering, reducing operational costs through automation, and improving user experience through consistent service quality. These objectives align with the broader industry trend toward autonomous network operations, where networks can self-configure, self-optimize, self-heal, and self-protect with minimal human oversight.
The historical development of adaptive network control can be traced back to early quality of service (QoS) mechanisms in the 1990s, which provided basic traffic prioritization capabilities. However, these systems lacked the sophistication to handle complex, multi-dimensional network optimization challenges. The advent of software-defined networking (SDN) in the 2000s marked a pivotal milestone, introducing programmable network control planes that enabled centralized management and dynamic policy enforcement.
Contemporary adaptive network control systems leverage machine learning algorithms, artificial intelligence, and advanced analytics to continuously monitor network conditions and automatically adjust parameters such as routing paths, bandwidth allocation, traffic shaping policies, and security configurations. These systems represent a fundamental shift from reactive network management to proactive, predictive control mechanisms that can anticipate and mitigate potential issues before they impact network performance.
The primary objective of integrating adaptive network control with anomaly detection is to create self-healing network infrastructures that can identify, isolate, and respond to security threats and performance degradations in real-time. This integration aims to minimize human intervention while maximizing network reliability, security, and efficiency. Key technical goals include achieving sub-second response times to detected anomalies, maintaining network performance during adaptive control actions, and ensuring scalability across diverse network topologies.
Modern adaptive control systems target several critical objectives: enhancing network resilience against both malicious attacks and benign failures, optimizing resource utilization through intelligent traffic engineering, reducing operational costs through automation, and improving user experience through consistent service quality. These objectives align with the broader industry trend toward autonomous network operations, where networks can self-configure, self-optimize, self-heal, and self-protect with minimal human oversight.
Market Demand for Network Anomaly Detection Solutions
The global network security landscape has experienced unprecedented transformation driven by the exponential growth of digital infrastructure and the increasing sophistication of cyber threats. Organizations across industries are grappling with complex network environments that span cloud platforms, edge computing nodes, and traditional on-premises systems, creating vast attack surfaces that require continuous monitoring and protection.
Enterprise demand for network anomaly detection solutions has surged as traditional perimeter-based security models prove inadequate against advanced persistent threats and zero-day attacks. The shift toward remote work paradigms and distributed computing architectures has further amplified the need for intelligent systems capable of identifying subtle behavioral deviations that may indicate security breaches or operational failures.
Financial services institutions represent a particularly lucrative market segment, driven by stringent regulatory compliance requirements and the high-value nature of their digital assets. These organizations demand solutions that can detect fraudulent transactions, unauthorized access attempts, and data exfiltration activities in real-time while minimizing false positives that could disrupt critical business operations.
Healthcare organizations constitute another rapidly expanding market vertical, where network anomaly detection systems must protect sensitive patient data while ensuring uninterrupted access to life-critical systems. The integration of Internet of Medical Things devices has created complex network topologies that require sophisticated monitoring capabilities to identify potential security vulnerabilities or device malfunctions.
Manufacturing and industrial sectors are increasingly adopting network anomaly detection solutions to protect operational technology environments and industrial control systems. The convergence of information technology and operational technology networks has created new security challenges that require specialized detection capabilities tailored to industrial protocols and real-time operational requirements.
The telecommunications industry faces unique challenges in securing massive network infrastructures that serve millions of users while maintaining service quality and availability. Network operators require scalable anomaly detection platforms capable of processing enormous volumes of network traffic data to identify potential security threats, service degradation, or infrastructure failures.
Government and defense organizations represent a critical market segment with specialized requirements for protecting classified information and critical infrastructure. These entities demand highly sophisticated detection capabilities that can identify nation-state attacks and advanced threat actors while operating within strict security and compliance frameworks.
Enterprise demand for network anomaly detection solutions has surged as traditional perimeter-based security models prove inadequate against advanced persistent threats and zero-day attacks. The shift toward remote work paradigms and distributed computing architectures has further amplified the need for intelligent systems capable of identifying subtle behavioral deviations that may indicate security breaches or operational failures.
Financial services institutions represent a particularly lucrative market segment, driven by stringent regulatory compliance requirements and the high-value nature of their digital assets. These organizations demand solutions that can detect fraudulent transactions, unauthorized access attempts, and data exfiltration activities in real-time while minimizing false positives that could disrupt critical business operations.
Healthcare organizations constitute another rapidly expanding market vertical, where network anomaly detection systems must protect sensitive patient data while ensuring uninterrupted access to life-critical systems. The integration of Internet of Medical Things devices has created complex network topologies that require sophisticated monitoring capabilities to identify potential security vulnerabilities or device malfunctions.
Manufacturing and industrial sectors are increasingly adopting network anomaly detection solutions to protect operational technology environments and industrial control systems. The convergence of information technology and operational technology networks has created new security challenges that require specialized detection capabilities tailored to industrial protocols and real-time operational requirements.
The telecommunications industry faces unique challenges in securing massive network infrastructures that serve millions of users while maintaining service quality and availability. Network operators require scalable anomaly detection platforms capable of processing enormous volumes of network traffic data to identify potential security threats, service degradation, or infrastructure failures.
Government and defense organizations represent a critical market segment with specialized requirements for protecting classified information and critical infrastructure. These entities demand highly sophisticated detection capabilities that can identify nation-state attacks and advanced threat actors while operating within strict security and compliance frameworks.
Current State of Adaptive Network Control Technologies
Adaptive network control technologies have evolved significantly over the past decade, driven by the increasing complexity of modern network infrastructures and the growing sophistication of cyber threats. Current implementations primarily focus on dynamic traffic management, automated resource allocation, and real-time network optimization to maintain optimal performance while detecting and mitigating anomalous behaviors.
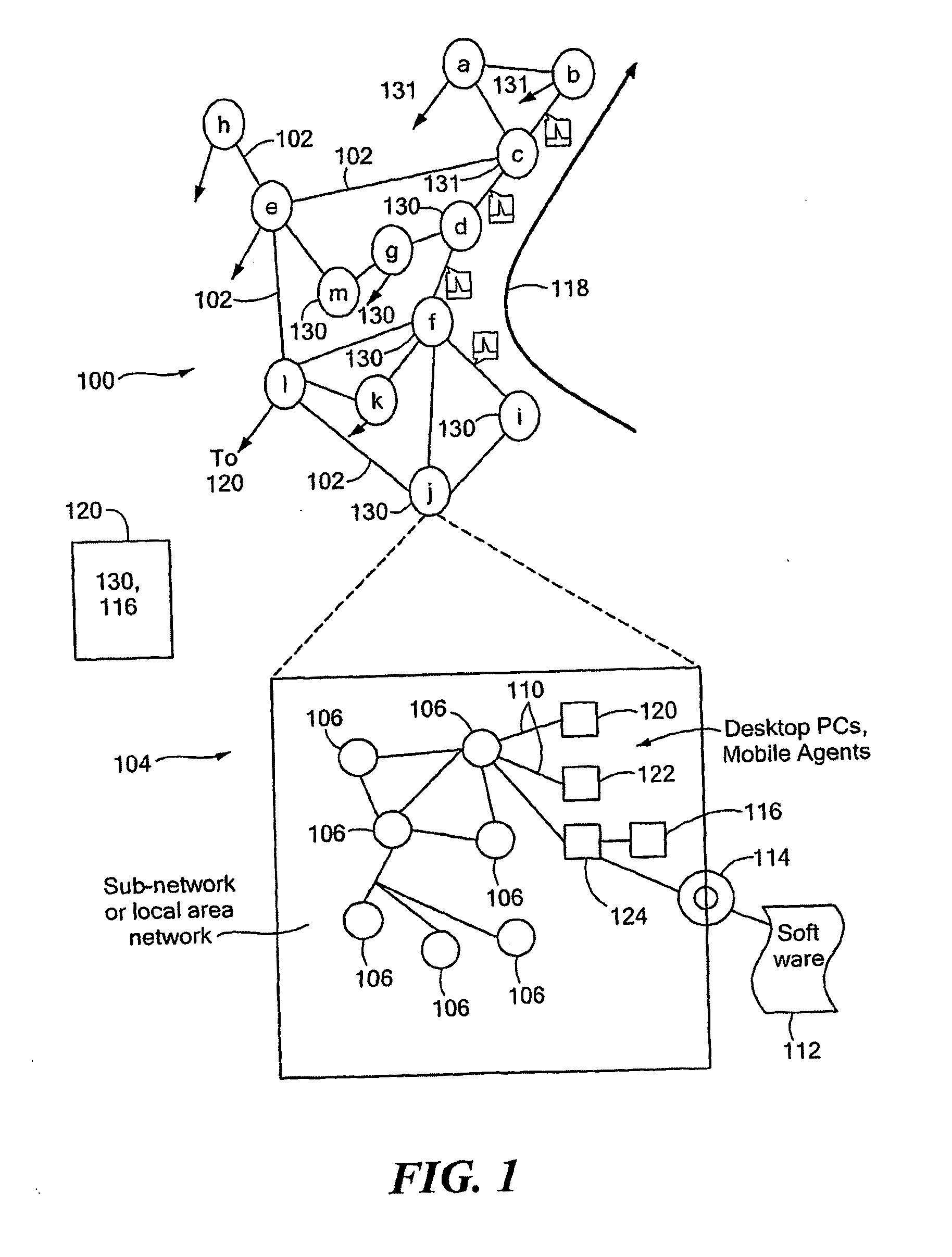
Software-Defined Networking (SDN) represents the foundational technology enabling adaptive network control, providing centralized network management through programmable interfaces. Major SDN controllers like OpenDaylight, ONOS, and Floodlight offer APIs for dynamic flow rule modification and network topology management. These platforms enable real-time network reconfiguration based on traffic patterns and security events, forming the backbone of modern adaptive control systems.
Machine learning integration has become increasingly prevalent in adaptive network control implementations. Current systems employ supervised learning algorithms for traffic classification, unsupervised clustering for anomaly detection, and reinforcement learning for automated decision-making. Deep learning models, particularly recurrent neural networks and autoencoders, are being deployed to identify complex network behavior patterns and predict potential security threats.
Intent-based networking (IBN) has emerged as a significant advancement, allowing network administrators to define high-level policies that are automatically translated into network configurations. Cisco's DNA Center, Juniper's Contrail, and VMware's NSX platforms incorporate IBN principles to enable self-healing networks that can adapt to changing conditions without manual intervention.
Network function virtualization (NFV) complements adaptive control by enabling dynamic deployment of security functions such as firewalls, intrusion detection systems, and load balancers. Current NFV orchestrators can automatically scale and relocate virtual network functions based on traffic demands and threat intelligence, providing flexible response mechanisms for anomaly detection scenarios.
Despite these advances, current adaptive network control technologies face several technical constraints. Latency requirements for real-time decision-making often conflict with the computational complexity of advanced analytics. Scalability remains challenging in large enterprise networks with thousands of endpoints. Additionally, the integration of legacy network equipment with modern adaptive control systems presents ongoing compatibility issues that limit full deployment potential.
Software-Defined Networking (SDN) represents the foundational technology enabling adaptive network control, providing centralized network management through programmable interfaces. Major SDN controllers like OpenDaylight, ONOS, and Floodlight offer APIs for dynamic flow rule modification and network topology management. These platforms enable real-time network reconfiguration based on traffic patterns and security events, forming the backbone of modern adaptive control systems.
Machine learning integration has become increasingly prevalent in adaptive network control implementations. Current systems employ supervised learning algorithms for traffic classification, unsupervised clustering for anomaly detection, and reinforcement learning for automated decision-making. Deep learning models, particularly recurrent neural networks and autoencoders, are being deployed to identify complex network behavior patterns and predict potential security threats.
Intent-based networking (IBN) has emerged as a significant advancement, allowing network administrators to define high-level policies that are automatically translated into network configurations. Cisco's DNA Center, Juniper's Contrail, and VMware's NSX platforms incorporate IBN principles to enable self-healing networks that can adapt to changing conditions without manual intervention.
Network function virtualization (NFV) complements adaptive control by enabling dynamic deployment of security functions such as firewalls, intrusion detection systems, and load balancers. Current NFV orchestrators can automatically scale and relocate virtual network functions based on traffic demands and threat intelligence, providing flexible response mechanisms for anomaly detection scenarios.
Despite these advances, current adaptive network control technologies face several technical constraints. Latency requirements for real-time decision-making often conflict with the computational complexity of advanced analytics. Scalability remains challenging in large enterprise networks with thousands of endpoints. Additionally, the integration of legacy network equipment with modern adaptive control systems presents ongoing compatibility issues that limit full deployment potential.
Existing Adaptive Control Solutions for Anomaly Detection
01 Machine learning-based anomaly detection methods
Machine learning algorithms can be employed to detect network anomalies by training models on normal network behavior patterns. These methods utilize supervised, unsupervised, or semi-supervised learning techniques to identify deviations from expected patterns. Deep learning approaches, including neural networks and autoencoders, can automatically extract features from network traffic data to improve detection accuracy. The models can adapt to evolving network conditions and reduce false positive rates through continuous learning and refinement.- Machine learning-based anomaly detection methods: Machine learning algorithms can be employed to detect network anomalies by training models on normal network behavior patterns. These methods utilize supervised, unsupervised, or semi-supervised learning techniques to identify deviations from expected patterns. Deep learning approaches, including neural networks and autoencoders, can automatically extract features from network traffic data to improve detection accuracy. The models can adapt to evolving network conditions and reduce false positive rates through continuous learning and refinement.
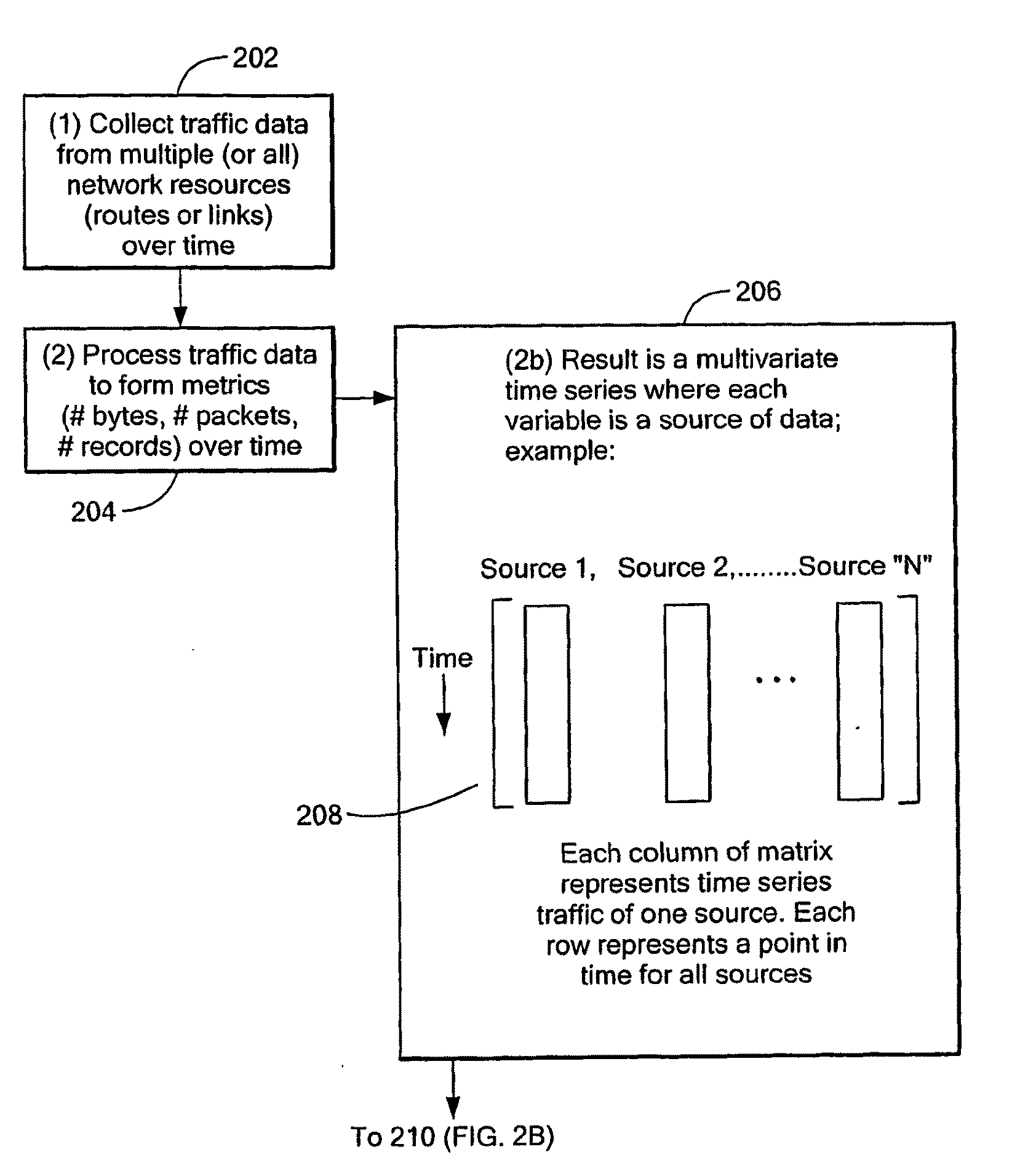
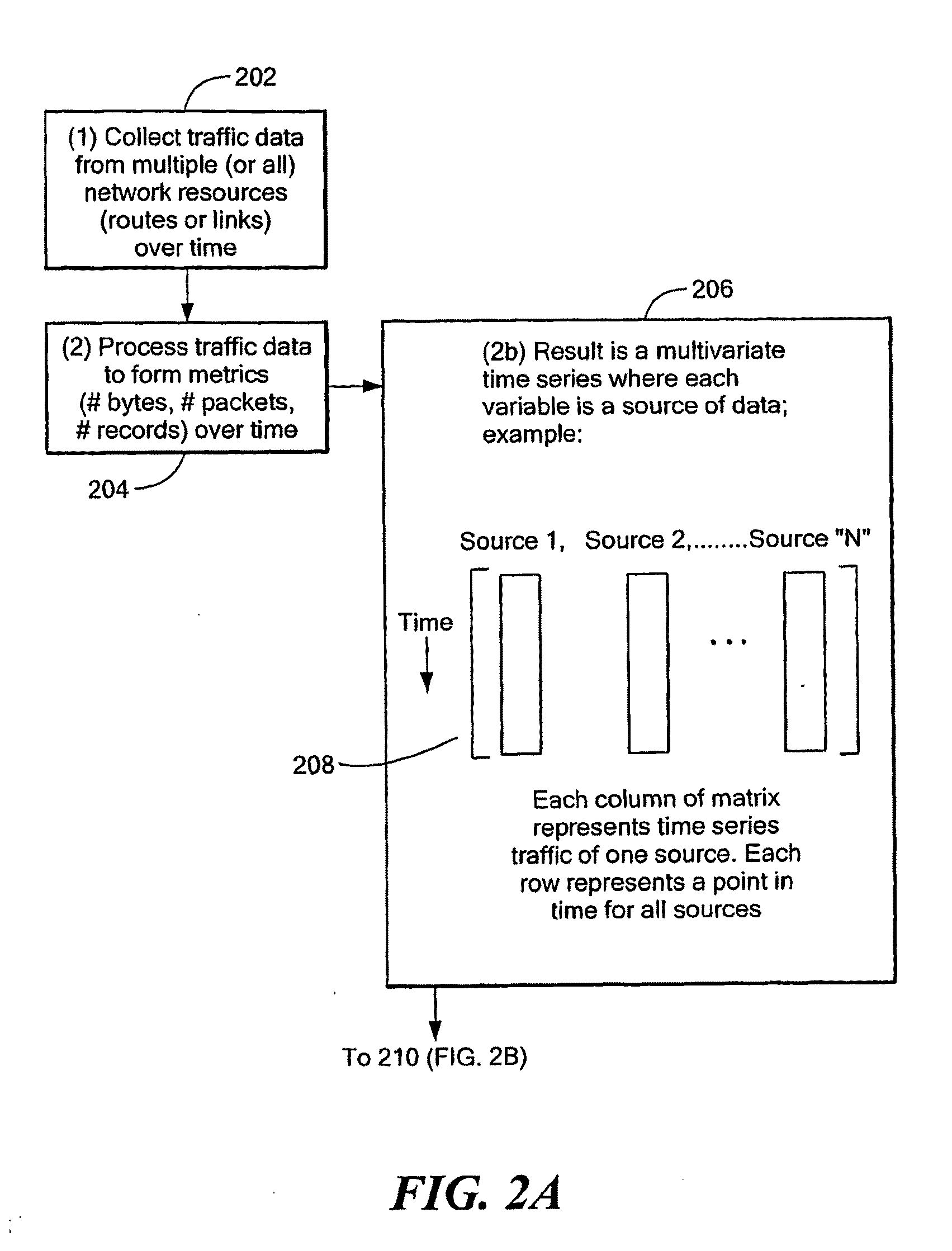
- Statistical analysis and threshold-based detection: Statistical methods analyze network traffic characteristics such as packet rates, bandwidth usage, and connection patterns to establish baseline behaviors. Anomalies are detected when observed metrics deviate significantly from established thresholds or statistical norms. These approaches may incorporate time-series analysis, probability distributions, and correlation techniques to identify unusual patterns. Adaptive thresholding mechanisms can be implemented to account for legitimate variations in network behavior and minimize false alarms.
- Behavioral profiling and pattern recognition: Network entities such as users, devices, and applications can be profiled based on their typical behavior patterns. Anomaly detection systems compare real-time activities against these established profiles to identify suspicious deviations. Pattern recognition techniques analyze sequences of events, communication patterns, and access behaviors to detect anomalies. This approach enables the identification of insider threats, compromised accounts, and abnormal application behaviors that may indicate security incidents.
- Hybrid and ensemble detection approaches: Combining multiple detection techniques can enhance overall accuracy by leveraging the strengths of different methods. Ensemble approaches integrate outputs from various detection algorithms to make more robust decisions about anomalies. Hybrid systems may combine signature-based detection with behavioral analysis or integrate multiple machine learning models. Voting mechanisms, weighted scoring, and consensus algorithms can be used to aggregate results from different detection components and reduce both false positives and false negatives.
- Real-time monitoring and adaptive detection systems: Real-time network monitoring systems continuously analyze traffic flows and system events to detect anomalies as they occur. Adaptive detection mechanisms automatically adjust their parameters and models based on feedback and changing network conditions. Stream processing techniques enable the analysis of high-volume network data with minimal latency. These systems incorporate feedback loops that allow them to learn from detection outcomes and improve accuracy over time through dynamic model updates and parameter tuning.
02 Statistical analysis and threshold-based detection
Statistical methods analyze network traffic characteristics such as packet rates, bandwidth usage, and connection patterns to establish baseline behaviors. Anomalies are detected when observed metrics deviate significantly from established thresholds or statistical norms. These approaches may incorporate time-series analysis, probability distributions, and correlation techniques to identify unusual patterns. Adaptive thresholding mechanisms can dynamically adjust detection parameters based on network conditions to maintain high accuracy.Expand Specific Solutions03 Behavioral analysis and profiling techniques
Network anomaly detection can be enhanced through behavioral profiling of users, devices, and applications. These techniques establish normal behavior patterns for network entities and flag deviations that may indicate security threats or operational issues. Profiling methods may track access patterns, communication relationships, and resource utilization over time. Context-aware analysis incorporates multiple behavioral dimensions to reduce false alarms and improve detection precision.Expand Specific Solutions04 Hybrid and ensemble detection approaches
Combining multiple detection techniques can significantly improve overall accuracy in identifying network anomalies. Hybrid systems integrate different methodologies such as signature-based detection, anomaly-based detection, and heuristic analysis to leverage their complementary strengths. Ensemble methods aggregate outputs from multiple detection models through voting, weighted averaging, or meta-learning to achieve more robust and reliable results. These approaches can handle diverse attack types and reduce both false positives and false negatives.Expand Specific Solutions05 Real-time processing and optimization techniques
Achieving high detection accuracy requires efficient real-time processing of network data streams. Optimization techniques include feature selection to reduce dimensionality, incremental learning for continuous model updates, and distributed processing architectures for scalability. Stream processing frameworks enable low-latency analysis of high-volume network traffic. Performance optimization balances computational efficiency with detection accuracy through algorithmic improvements and hardware acceleration.Expand Specific Solutions
Key Players in Network Security and Control Systems
The network anomaly detection through adaptive network control field represents a rapidly evolving sector driven by increasing cybersecurity threats and network complexity. The market demonstrates significant growth potential as organizations prioritize proactive threat detection capabilities. Technology maturity varies considerably across different player categories. Established telecommunications giants like Huawei, Ericsson, and NEC possess advanced infrastructure capabilities, while specialized security firms such as Securonix and NetFlow Logic offer cutting-edge anomaly detection algorithms. Traditional IT companies including Red Hat and Extreme Networks contribute foundational networking technologies. Research institutions like Beijing University of Posts & Telecommunications and Electronics & Telecommunications Research Institute drive innovation in adaptive control mechanisms. The competitive landscape shows convergence between network infrastructure providers and cybersecurity specialists, indicating market consolidation trends toward comprehensive security-integrated networking solutions.
Huawei Technologies Co., Ltd.
Technical Solution: Huawei has developed an intelligent network anomaly detection system that leverages AI-driven adaptive control mechanisms. Their solution integrates machine learning algorithms with Software-Defined Networking (SDN) controllers to enable real-time network monitoring and automatic response to anomalies. The system employs deep learning models to analyze network traffic patterns and identify deviations from normal behavior. When anomalies are detected, the adaptive control system automatically adjusts network parameters, reroutes traffic, or isolates affected network segments to maintain optimal performance. Huawei's approach combines behavioral analysis with predictive modeling to proactively identify potential security threats and network performance issues before they impact service quality.
Strengths: Comprehensive AI integration with strong R&D capabilities and extensive telecom infrastructure experience. Weaknesses: Limited market access in some regions due to geopolitical concerns and regulatory restrictions.
Telefonaktiebolaget LM Ericsson
Technical Solution: Ericsson has developed network anomaly detection solutions integrated into their Network Intelligence platform, utilizing machine learning for adaptive network management. Their approach combines real-time analytics with automated network optimization to detect and respond to anomalies in mobile and fixed networks. The system employs predictive analytics to identify potential network issues before they affect service quality, and uses adaptive algorithms to automatically adjust network parameters such as load balancing, resource allocation, and traffic routing. Ericsson's solution is particularly focused on 5G networks, where it can dynamically manage network slices and optimize performance based on detected anomalies and changing traffic patterns.
Strengths: Deep telecommunications expertise with strong 5G network management capabilities and proven scalability. Weaknesses: Solutions are primarily telecom-focused and may require significant customization for enterprise networks.
Core Innovations in Adaptive Network Control Patents
Adaptive filtering based network anomaly detection
PatentWO2017016492A1
Innovation
- Introduces adaptive filtering for predicting future values of network quality indicators, enabling proactive anomaly detection rather than reactive detection.
- Performs frequency-domain analysis of residues between predicted and measured values, allowing detection of anomalies in specific frequency bands rather than time-domain only.
- Combines residue analysis with measured values for anomaly detection, providing a dual-validation mechanism that reduces false positives.
Method and Apparatus for Whole-Network Anomaly Diagnosis and Method to Detect and Classify Network Anomalies Using Traffic Feature Distributions
PatentActiveUS20100071061A1
Innovation
- The technique analyzes the distributional properties of multiple network traffic features across the entire network, using statistical and mathematical methods for classification and localization of anomalies, allowing for the detection and classification of novel anomalies without human intervention, and providing a general solution for a wide range of anomalous events.
Cybersecurity Regulations and Compliance Requirements
The implementation of network anomaly detection through adaptive network control operates within a complex regulatory landscape that varies significantly across jurisdictions. In the United States, organizations must comply with sector-specific regulations such as NIST Cybersecurity Framework, FISMA for federal agencies, and industry standards like PCI DSS for payment processing. The European Union's NIS2 Directive establishes comprehensive cybersecurity requirements for critical infrastructure operators, mandating incident reporting and risk management measures that directly impact anomaly detection system deployment.
Financial institutions face particularly stringent requirements under regulations like SOX, Basel III, and regional banking supervisory guidelines. These frameworks require continuous monitoring capabilities and automated threat detection systems, making adaptive network control solutions essential for compliance. Healthcare organizations must navigate HIPAA requirements in the US and GDPR provisions in Europe, which demand robust data protection measures and breach notification protocols that anomaly detection systems must support.
Cross-border data transfer regulations significantly influence the architecture of adaptive network control systems. GDPR's data localization requirements and emerging data sovereignty laws in countries like China and Russia necessitate geographically distributed anomaly detection capabilities. Organizations must ensure their systems can operate within these constraints while maintaining effective threat detection across global networks.
Compliance reporting requirements create additional technical specifications for anomaly detection systems. Regulations typically mandate detailed logging, audit trails, and incident documentation capabilities. Systems must generate compliance-ready reports that demonstrate adherence to security controls and provide evidence of continuous monitoring activities. The integration of automated compliance reporting features has become a critical requirement for enterprise-grade solutions.
Emerging regulations around artificial intelligence and automated decision-making, such as the EU's proposed AI Act, introduce new compliance considerations for machine learning-based anomaly detection systems. These regulations may require explainability features, bias testing, and human oversight mechanisms that influence system design and deployment strategies.
Financial institutions face particularly stringent requirements under regulations like SOX, Basel III, and regional banking supervisory guidelines. These frameworks require continuous monitoring capabilities and automated threat detection systems, making adaptive network control solutions essential for compliance. Healthcare organizations must navigate HIPAA requirements in the US and GDPR provisions in Europe, which demand robust data protection measures and breach notification protocols that anomaly detection systems must support.
Cross-border data transfer regulations significantly influence the architecture of adaptive network control systems. GDPR's data localization requirements and emerging data sovereignty laws in countries like China and Russia necessitate geographically distributed anomaly detection capabilities. Organizations must ensure their systems can operate within these constraints while maintaining effective threat detection across global networks.
Compliance reporting requirements create additional technical specifications for anomaly detection systems. Regulations typically mandate detailed logging, audit trails, and incident documentation capabilities. Systems must generate compliance-ready reports that demonstrate adherence to security controls and provide evidence of continuous monitoring activities. The integration of automated compliance reporting features has become a critical requirement for enterprise-grade solutions.
Emerging regulations around artificial intelligence and automated decision-making, such as the EU's proposed AI Act, introduce new compliance considerations for machine learning-based anomaly detection systems. These regulations may require explainability features, bias testing, and human oversight mechanisms that influence system design and deployment strategies.
Privacy Protection in Network Monitoring Systems
Privacy protection in network monitoring systems represents a critical challenge when implementing adaptive network anomaly detection solutions. The fundamental tension lies between the need for comprehensive network visibility to detect sophisticated threats and the imperative to safeguard sensitive user data and organizational information from unauthorized access or misuse.
Traditional network monitoring approaches often require deep packet inspection and extensive data collection, creating significant privacy vulnerabilities. When implementing adaptive network control for anomaly detection, organizations must navigate complex regulatory frameworks including GDPR, CCPA, and sector-specific compliance requirements. These regulations mandate strict data minimization principles, requiring that only necessary data be collected and processed for legitimate security purposes.
Modern privacy-preserving techniques offer promising solutions for network anomaly detection systems. Differential privacy mechanisms can add calibrated noise to network traffic statistics while maintaining the statistical properties necessary for accurate anomaly detection. Homomorphic encryption enables computation on encrypted network data, allowing anomaly detection algorithms to operate without exposing sensitive traffic content. Federated learning approaches permit collaborative threat detection across multiple network domains without sharing raw traffic data.
Data anonymization and pseudonymization techniques play crucial roles in protecting individual privacy while enabling effective anomaly detection. Advanced anonymization methods such as k-anonymity, l-diversity, and t-closeness can be applied to network flow records and connection metadata. However, these techniques must be carefully balanced against detection accuracy, as over-anonymization can obscure the subtle patterns that indicate network anomalies.
Zero-knowledge proof systems and secure multi-party computation protocols enable privacy-preserving collaboration between organizations for threat intelligence sharing. These cryptographic approaches allow network operators to jointly detect distributed attacks and coordinated threats without revealing proprietary network information or sensitive operational data.
Implementation challenges include computational overhead from privacy-preserving mechanisms, potential reduction in detection accuracy due to data obfuscation, and the complexity of managing cryptographic keys and protocols. Organizations must also establish clear data governance frameworks that define retention policies, access controls, and audit mechanisms for privacy-protected monitoring systems.
Traditional network monitoring approaches often require deep packet inspection and extensive data collection, creating significant privacy vulnerabilities. When implementing adaptive network control for anomaly detection, organizations must navigate complex regulatory frameworks including GDPR, CCPA, and sector-specific compliance requirements. These regulations mandate strict data minimization principles, requiring that only necessary data be collected and processed for legitimate security purposes.
Modern privacy-preserving techniques offer promising solutions for network anomaly detection systems. Differential privacy mechanisms can add calibrated noise to network traffic statistics while maintaining the statistical properties necessary for accurate anomaly detection. Homomorphic encryption enables computation on encrypted network data, allowing anomaly detection algorithms to operate without exposing sensitive traffic content. Federated learning approaches permit collaborative threat detection across multiple network domains without sharing raw traffic data.
Data anonymization and pseudonymization techniques play crucial roles in protecting individual privacy while enabling effective anomaly detection. Advanced anonymization methods such as k-anonymity, l-diversity, and t-closeness can be applied to network flow records and connection metadata. However, these techniques must be carefully balanced against detection accuracy, as over-anonymization can obscure the subtle patterns that indicate network anomalies.
Zero-knowledge proof systems and secure multi-party computation protocols enable privacy-preserving collaboration between organizations for threat intelligence sharing. These cryptographic approaches allow network operators to jointly detect distributed attacks and coordinated threats without revealing proprietary network information or sensitive operational data.
Implementation challenges include computational overhead from privacy-preserving mechanisms, potential reduction in detection accuracy due to data obfuscation, and the complexity of managing cryptographic keys and protocols. Organizations must also establish clear data governance frameworks that define retention policies, access controls, and audit mechanisms for privacy-protected monitoring systems.
Unlock deeper insights with PatSnap Eureka Quick Research — get a full tech report to explore trends and direct your research. Try now!
Generate Your Research Report Instantly with AI Agent
Supercharge your innovation with PatSnap Eureka AI Agent Platform!