Security Vulnerability Assessments in Battery Management Systems
AUG 8, 20259 MIN READ
Generate Your Research Report Instantly with AI Agent
PatSnap Eureka helps you evaluate technical feasibility & market potential.
BMS Security Background
Battery Management Systems (BMS) have become an integral component of modern energy storage solutions, particularly in electric vehicles and renewable energy systems. As these systems become more sophisticated and interconnected, the importance of security in BMS has grown exponentially. The background of BMS security is rooted in the convergence of energy management and cybersecurity, driven by the increasing digitalization of power systems and the growing threat landscape in the cyber domain.
The evolution of BMS security can be traced back to the early 2000s when the first generation of electric vehicles began to emerge. Initially, security considerations were primarily focused on physical access control and basic data encryption. However, as BMS became more complex and started integrating with broader vehicle systems and external networks, the attack surface expanded significantly.
The automotive industry's shift towards connected and autonomous vehicles has further amplified the importance of BMS security. Modern electric vehicles rely heavily on their battery systems not just for propulsion, but also for critical functions such as power distribution, thermal management, and even vehicle-to-grid (V2G) interactions. This increased reliance on BMS has made it a prime target for potential cyber attacks.
In parallel, the renewable energy sector has seen a similar trajectory in BMS security concerns. As large-scale energy storage systems become more prevalent in grid stabilization and load balancing, the security of these systems has become a matter of national energy security. Attacks on BMS in this context could potentially disrupt power supply to entire regions, making it a critical infrastructure protection issue.
The threat landscape for BMS has evolved from simple theft and tampering to sophisticated cyber attacks. Potential threats now include remote exploitation of vulnerabilities to manipulate battery performance, data theft of sensitive battery usage patterns, and even the possibility of coordinated attacks on multiple BMS to cause widespread disruption.
Regulatory bodies and industry standards organizations have responded to these growing concerns by developing frameworks and guidelines specifically addressing BMS security. For instance, the ISO/SAE 21434 standard for automotive cybersecurity and the IEC 62443 series for industrial control systems security now include provisions relevant to BMS.
As we move forward, the background of BMS security continues to evolve, influenced by emerging technologies such as artificial intelligence, blockchain, and 5G connectivity. These technologies offer new opportunities for enhancing BMS security but also introduce new vulnerabilities that must be addressed. The ongoing challenge lies in balancing the need for increased functionality and connectivity with robust security measures to protect these critical systems.
The evolution of BMS security can be traced back to the early 2000s when the first generation of electric vehicles began to emerge. Initially, security considerations were primarily focused on physical access control and basic data encryption. However, as BMS became more complex and started integrating with broader vehicle systems and external networks, the attack surface expanded significantly.
The automotive industry's shift towards connected and autonomous vehicles has further amplified the importance of BMS security. Modern electric vehicles rely heavily on their battery systems not just for propulsion, but also for critical functions such as power distribution, thermal management, and even vehicle-to-grid (V2G) interactions. This increased reliance on BMS has made it a prime target for potential cyber attacks.
In parallel, the renewable energy sector has seen a similar trajectory in BMS security concerns. As large-scale energy storage systems become more prevalent in grid stabilization and load balancing, the security of these systems has become a matter of national energy security. Attacks on BMS in this context could potentially disrupt power supply to entire regions, making it a critical infrastructure protection issue.
The threat landscape for BMS has evolved from simple theft and tampering to sophisticated cyber attacks. Potential threats now include remote exploitation of vulnerabilities to manipulate battery performance, data theft of sensitive battery usage patterns, and even the possibility of coordinated attacks on multiple BMS to cause widespread disruption.
Regulatory bodies and industry standards organizations have responded to these growing concerns by developing frameworks and guidelines specifically addressing BMS security. For instance, the ISO/SAE 21434 standard for automotive cybersecurity and the IEC 62443 series for industrial control systems security now include provisions relevant to BMS.
As we move forward, the background of BMS security continues to evolve, influenced by emerging technologies such as artificial intelligence, blockchain, and 5G connectivity. These technologies offer new opportunities for enhancing BMS security but also introduce new vulnerabilities that must be addressed. The ongoing challenge lies in balancing the need for increased functionality and connectivity with robust security measures to protect these critical systems.
Market Demand Analysis
The market demand for Security Vulnerability Assessments in Battery Management Systems (BMS) has been experiencing significant growth in recent years. This surge is primarily driven by the rapid expansion of the electric vehicle (EV) market and the increasing adoption of large-scale energy storage systems. As these technologies become more prevalent, the need for robust security measures in BMS has become paramount.
The automotive industry, particularly the EV sector, represents a major market for BMS security assessments. With the global EV market projected to grow at a compound annual growth rate (CAGR) of over 20% in the coming years, the demand for secure BMS solutions is expected to rise proportionally. Major automakers and EV manufacturers are increasingly prioritizing cybersecurity in their vehicle designs, recognizing the potential risks associated with compromised battery systems.
In addition to the automotive sector, the energy storage industry is another key driver of demand for BMS security assessments. As renewable energy sources become more prevalent and grid modernization efforts continue, the deployment of large-scale battery storage systems is accelerating. These systems require robust security measures to protect against potential cyber threats that could disrupt power supply or cause safety hazards.
The industrial and consumer electronics sectors also contribute to the growing demand for BMS security assessments. With the proliferation of battery-powered devices and equipment in various industries, ensuring the security and integrity of battery management systems has become crucial for maintaining operational efficiency and safety.
Market trends indicate a shift towards more comprehensive and proactive security measures in BMS. There is an increasing emphasis on continuous monitoring and real-time threat detection capabilities, as well as the integration of advanced encryption and authentication protocols. This trend is driven by the recognition that traditional security measures may be insufficient in the face of evolving cyber threats targeting battery systems.
The regulatory landscape is also shaping market demand for BMS security assessments. Governments and industry bodies worldwide are implementing stricter cybersecurity standards and regulations for battery-powered systems, particularly in critical infrastructure and automotive applications. This regulatory push is compelling manufacturers and operators to invest in robust security assessment and implementation measures for their BMS.
As the market for BMS security assessments continues to evolve, there is a growing demand for specialized expertise and tools. Organizations are seeking comprehensive vulnerability assessment services that can identify potential weaknesses in their BMS architectures and provide actionable recommendations for enhancing security. This has led to the emergence of specialized cybersecurity firms focusing on BMS and related technologies, as well as increased investment in research and development of advanced security assessment methodologies.
The automotive industry, particularly the EV sector, represents a major market for BMS security assessments. With the global EV market projected to grow at a compound annual growth rate (CAGR) of over 20% in the coming years, the demand for secure BMS solutions is expected to rise proportionally. Major automakers and EV manufacturers are increasingly prioritizing cybersecurity in their vehicle designs, recognizing the potential risks associated with compromised battery systems.
In addition to the automotive sector, the energy storage industry is another key driver of demand for BMS security assessments. As renewable energy sources become more prevalent and grid modernization efforts continue, the deployment of large-scale battery storage systems is accelerating. These systems require robust security measures to protect against potential cyber threats that could disrupt power supply or cause safety hazards.
The industrial and consumer electronics sectors also contribute to the growing demand for BMS security assessments. With the proliferation of battery-powered devices and equipment in various industries, ensuring the security and integrity of battery management systems has become crucial for maintaining operational efficiency and safety.
Market trends indicate a shift towards more comprehensive and proactive security measures in BMS. There is an increasing emphasis on continuous monitoring and real-time threat detection capabilities, as well as the integration of advanced encryption and authentication protocols. This trend is driven by the recognition that traditional security measures may be insufficient in the face of evolving cyber threats targeting battery systems.
The regulatory landscape is also shaping market demand for BMS security assessments. Governments and industry bodies worldwide are implementing stricter cybersecurity standards and regulations for battery-powered systems, particularly in critical infrastructure and automotive applications. This regulatory push is compelling manufacturers and operators to invest in robust security assessment and implementation measures for their BMS.
As the market for BMS security assessments continues to evolve, there is a growing demand for specialized expertise and tools. Organizations are seeking comprehensive vulnerability assessment services that can identify potential weaknesses in their BMS architectures and provide actionable recommendations for enhancing security. This has led to the emergence of specialized cybersecurity firms focusing on BMS and related technologies, as well as increased investment in research and development of advanced security assessment methodologies.
Current Vulnerabilities
Battery Management Systems (BMS) play a crucial role in ensuring the safe and efficient operation of battery-powered devices and systems. However, these systems are not immune to security vulnerabilities, which can have severe consequences if exploited. Current vulnerabilities in BMS can be categorized into several key areas, each presenting unique challenges and potential risks.
One of the primary vulnerabilities lies in the communication protocols used within BMS. Many systems rely on CAN (Controller Area Network) bus or other standard protocols for internal communication. These protocols, while efficient, often lack robust security measures, making them susceptible to man-in-the-middle attacks, data injection, and unauthorized access. Attackers can potentially intercept, modify, or inject false data, leading to incorrect battery management decisions or system malfunctions.
Another significant vulnerability stems from the firmware and software components of BMS. Like any embedded system, BMS are susceptible to software bugs, outdated firmware, and inadequate update mechanisms. These issues can create exploitable weaknesses, allowing attackers to gain unauthorized control over the system, manipulate battery parameters, or even execute malicious code. The complexity of BMS software and the challenges in regularly updating firmware in deployed systems exacerbate this vulnerability.
Physical access to BMS components presents another avenue for potential security breaches. Many BMS lack adequate physical security measures, making them vulnerable to tampering or direct manipulation. This can include unauthorized access to diagnostic ports, sensor tampering, or even physical modification of BMS hardware. Such vulnerabilities can lead to data theft, system compromise, or deliberate sabotage of battery performance and safety features.
The increasing connectivity of BMS, particularly in electric vehicles and smart grid applications, introduces new vulnerabilities related to network security. As these systems become more integrated with external networks and cloud services, they become potential targets for remote attacks. Inadequate network security measures, such as weak authentication protocols or insufficient encryption, can expose BMS to a wide range of cyber threats, including data breaches, remote system manipulation, and denial-of-service attacks.
Sensor vulnerabilities represent another critical area of concern in current BMS designs. The accuracy and integrity of sensor data are crucial for proper battery management. However, sensors can be susceptible to various forms of interference, manipulation, or failure. This can include electromagnetic interference, environmental factors, or deliberate tampering. Inaccurate or compromised sensor data can lead to incorrect battery state estimation, potentially resulting in overcharging, over-discharging, or thermal runaway scenarios.
Lastly, the lack of comprehensive security testing and validation processes in BMS development and deployment contributes to overall system vulnerability. Many BMS are not subjected to rigorous security assessments, penetration testing, or ongoing security monitoring. This gap in security practices can leave unknown vulnerabilities undetected and unaddressed, increasing the risk of successful attacks or system compromises.
One of the primary vulnerabilities lies in the communication protocols used within BMS. Many systems rely on CAN (Controller Area Network) bus or other standard protocols for internal communication. These protocols, while efficient, often lack robust security measures, making them susceptible to man-in-the-middle attacks, data injection, and unauthorized access. Attackers can potentially intercept, modify, or inject false data, leading to incorrect battery management decisions or system malfunctions.
Another significant vulnerability stems from the firmware and software components of BMS. Like any embedded system, BMS are susceptible to software bugs, outdated firmware, and inadequate update mechanisms. These issues can create exploitable weaknesses, allowing attackers to gain unauthorized control over the system, manipulate battery parameters, or even execute malicious code. The complexity of BMS software and the challenges in regularly updating firmware in deployed systems exacerbate this vulnerability.
Physical access to BMS components presents another avenue for potential security breaches. Many BMS lack adequate physical security measures, making them vulnerable to tampering or direct manipulation. This can include unauthorized access to diagnostic ports, sensor tampering, or even physical modification of BMS hardware. Such vulnerabilities can lead to data theft, system compromise, or deliberate sabotage of battery performance and safety features.
The increasing connectivity of BMS, particularly in electric vehicles and smart grid applications, introduces new vulnerabilities related to network security. As these systems become more integrated with external networks and cloud services, they become potential targets for remote attacks. Inadequate network security measures, such as weak authentication protocols or insufficient encryption, can expose BMS to a wide range of cyber threats, including data breaches, remote system manipulation, and denial-of-service attacks.
Sensor vulnerabilities represent another critical area of concern in current BMS designs. The accuracy and integrity of sensor data are crucial for proper battery management. However, sensors can be susceptible to various forms of interference, manipulation, or failure. This can include electromagnetic interference, environmental factors, or deliberate tampering. Inaccurate or compromised sensor data can lead to incorrect battery state estimation, potentially resulting in overcharging, over-discharging, or thermal runaway scenarios.
Lastly, the lack of comprehensive security testing and validation processes in BMS development and deployment contributes to overall system vulnerability. Many BMS are not subjected to rigorous security assessments, penetration testing, or ongoing security monitoring. This gap in security practices can leave unknown vulnerabilities undetected and unaddressed, increasing the risk of successful attacks or system compromises.
Existing Security Solutions
01 Network security measures for Battery Management Systems
Implementing robust network security measures is crucial for protecting Battery Management Systems (BMS) from potential vulnerabilities. This includes firewalls, intrusion detection systems, and secure communication protocols to prevent unauthorized access and data breaches. Encryption and authentication mechanisms are also employed to ensure the integrity and confidentiality of BMS data transmission.- Network security measures for Battery Management Systems: Implementing robust network security measures is crucial for protecting Battery Management Systems (BMS) from potential vulnerabilities. This includes firewalls, intrusion detection systems, and secure communication protocols to prevent unauthorized access and data breaches. Encryption techniques and secure authentication mechanisms are also employed to safeguard sensitive information within the BMS network.
- Secure firmware updates and patch management: Ensuring the security of firmware updates and implementing effective patch management strategies are essential for mitigating vulnerabilities in Battery Management Systems. This involves secure distribution channels for updates, digital signature verification, and rollback protection to prevent unauthorized modifications. Regular security assessments and timely application of patches help address known vulnerabilities and maintain system integrity.
- Access control and user authentication: Implementing strong access control mechanisms and user authentication protocols is crucial for protecting Battery Management Systems from unauthorized access. This includes multi-factor authentication, role-based access control, and secure password policies. Regular audits of user privileges and access logs help detect and prevent potential security breaches.
- Secure data storage and encryption: Protecting sensitive data stored within Battery Management Systems is vital for maintaining security. This involves implementing robust encryption algorithms for data at rest and in transit, secure key management practices, and data backup strategies. Secure storage solutions and data isolation techniques help prevent unauthorized access and data leakage.
- Continuous monitoring and threat detection: Implementing continuous monitoring and threat detection mechanisms is essential for identifying and responding to potential security threats in Battery Management Systems. This includes real-time monitoring of system activities, anomaly detection algorithms, and security information and event management (SIEM) solutions. Regular security audits and penetration testing help identify vulnerabilities and improve overall system security.
02 Secure firmware and software updates for BMS
Ensuring the security of firmware and software updates is essential for maintaining the integrity of Battery Management Systems. This involves implementing secure update mechanisms, digital signatures, and version control to prevent unauthorized modifications or malicious code injection. Regular security audits and vulnerability assessments are conducted to identify and address potential weaknesses in the update process.Expand Specific Solutions03 Access control and authentication for BMS
Implementing strong access control and authentication mechanisms is crucial for protecting Battery Management Systems from unauthorized access. This includes multi-factor authentication, role-based access control, and secure user management systems. Regular monitoring and logging of access attempts help detect and prevent potential security breaches.Expand Specific Solutions04 Secure data storage and encryption for BMS
Protecting sensitive data stored within Battery Management Systems is essential for maintaining security. This involves implementing robust encryption algorithms for data at rest and in transit, secure key management practices, and regular data backups. Secure storage solutions and access controls are also employed to prevent unauthorized data access or manipulation.Expand Specific Solutions05 Threat detection and incident response for BMS
Implementing effective threat detection and incident response mechanisms is crucial for identifying and mitigating security vulnerabilities in Battery Management Systems. This includes real-time monitoring, anomaly detection, and automated alert systems to quickly identify potential security breaches. Incident response plans and procedures are established to ensure timely and effective responses to security incidents.Expand Specific Solutions
Key Industry Players
The security vulnerability assessment landscape in Battery Management Systems (BMS) is evolving rapidly, reflecting the industry's growth stage and increasing market size. As electric vehicles and energy storage systems gain traction, the BMS market is expanding, with a projected CAGR of 19.9% from 2021 to 2026. The technology maturity varies among key players, with companies like LG Energy Solution, Samsung SDI, and CATL leading in innovation. Established automotive giants such as Bosch and Hyundai are also making significant strides. Emerging players like Green Cubes Technology and Paired Power are introducing novel solutions, while research institutions like ITRI and government labs contribute to advancing security measures in BMS.
LG Energy Solution Ltd.
Technical Solution: LG Energy Solution has developed a comprehensive security vulnerability assessment framework for battery management systems (BMS). Their approach integrates multi-layered security measures, including hardware-based security modules and advanced encryption algorithms. The company employs machine learning techniques to detect anomalies and potential cyber threats in real-time[1]. They have also implemented a secure over-the-air (OTA) update system to address vulnerabilities promptly[2]. LG's BMS incorporates a dedicated security chip that provides secure boot, runtime integrity checking, and secure key storage[3].
Strengths: Robust multi-layered security approach, real-time threat detection, and secure OTA updates. Weaknesses: Potential increased cost due to dedicated hardware security modules, and the need for regular updates to keep pace with evolving threats.
Robert Bosch GmbH
Technical Solution: Bosch has developed an innovative approach to security vulnerability assessments in BMS, focusing on a holistic security concept. Their solution incorporates intrusion detection systems (IDS) specifically designed for automotive networks[4]. Bosch's BMS security framework includes secure communication protocols, authentication mechanisms, and cryptographic key management. They have also implemented a hardware security module (HSM) that provides a root of trust for critical security operations[5]. Bosch's vulnerability assessment process includes regular penetration testing and security audits to identify and address potential weaknesses in the BMS[6].
Strengths: Comprehensive security approach tailored for automotive applications, integration of HSM for enhanced security. Weaknesses: Potential complexity in implementation and integration with existing systems, possible performance overhead due to extensive security measures.
Core Security Innovations
Energy storage system and communication method therefor
PatentPendingEP4507247A1
Innovation
- The energy storage system employs a method where an upper-level controller generates authentication key information and a first authentication key using battery cell information from a battery management system (BMS), and the BMS generates a second authentication key using the same information. The authenticity of control commands is determined by comparing the first and second authentication keys, ensuring secure communication while efficiently using computing resources.
Battery security systems and methods
PatentPendingUS20250094551A1
Innovation
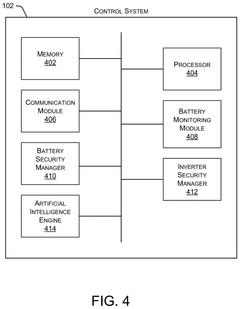
- A battery security system that employs a battery management system (BMS) to manage a security key or token, verifying ownership and preventing operation if stolen, using a control system to communicate with the BMS and remotely deactivate batteries if necessary.
Regulatory Compliance
Regulatory compliance plays a crucial role in the development and implementation of security vulnerability assessments for Battery Management Systems (BMS). As the automotive industry increasingly adopts electric vehicles, the need for robust security measures in BMS has become paramount. Various regulatory bodies and standards organizations have established guidelines and requirements to ensure the safety and security of these critical systems.
The International Electrotechnical Commission (IEC) has developed several standards relevant to BMS security, including IEC 62619 and IEC 61508. These standards outline safety requirements for lithium-ion batteries and functional safety for electrical/electronic/programmable electronic safety-related systems, respectively. Compliance with these standards is essential for manufacturers to demonstrate the reliability and security of their BMS.
In the United States, the National Highway Traffic Safety Administration (NHTSA) has issued guidelines for cybersecurity in vehicles, which extend to BMS. These guidelines emphasize the importance of risk assessment, security by design, and incident response planning. Manufacturers must conduct thorough vulnerability assessments and implement appropriate security measures to comply with NHTSA recommendations.
The European Union has introduced the UN Regulation No. 155 on Cyber Security and Cyber Security Management System, which applies to vehicles, including their BMS. This regulation mandates that manufacturers implement a Cyber Security Management System (CSMS) and obtain type approval for their vehicles based on cybersecurity considerations. Compliance with this regulation requires comprehensive vulnerability assessments and ongoing security management throughout the vehicle's lifecycle.
The ISO/SAE 21434 standard, jointly developed by the International Organization for Standardization (ISO) and SAE International, provides a framework for cybersecurity engineering in road vehicles. This standard outlines processes for identifying and mitigating cybersecurity risks, including those related to BMS. Adherence to ISO/SAE 21434 is becoming increasingly important for automotive manufacturers and suppliers.
As the regulatory landscape continues to evolve, companies must stay informed about emerging standards and requirements. Regular audits and assessments are necessary to ensure ongoing compliance. Additionally, collaboration with regulatory bodies and participation in industry working groups can help organizations stay ahead of regulatory changes and contribute to the development of future standards.
Failure to comply with regulatory requirements can result in significant consequences, including fines, product recalls, and reputational damage. Therefore, integrating regulatory compliance into the security vulnerability assessment process for BMS is not only a legal necessity but also a critical business imperative.
The International Electrotechnical Commission (IEC) has developed several standards relevant to BMS security, including IEC 62619 and IEC 61508. These standards outline safety requirements for lithium-ion batteries and functional safety for electrical/electronic/programmable electronic safety-related systems, respectively. Compliance with these standards is essential for manufacturers to demonstrate the reliability and security of their BMS.
In the United States, the National Highway Traffic Safety Administration (NHTSA) has issued guidelines for cybersecurity in vehicles, which extend to BMS. These guidelines emphasize the importance of risk assessment, security by design, and incident response planning. Manufacturers must conduct thorough vulnerability assessments and implement appropriate security measures to comply with NHTSA recommendations.
The European Union has introduced the UN Regulation No. 155 on Cyber Security and Cyber Security Management System, which applies to vehicles, including their BMS. This regulation mandates that manufacturers implement a Cyber Security Management System (CSMS) and obtain type approval for their vehicles based on cybersecurity considerations. Compliance with this regulation requires comprehensive vulnerability assessments and ongoing security management throughout the vehicle's lifecycle.
The ISO/SAE 21434 standard, jointly developed by the International Organization for Standardization (ISO) and SAE International, provides a framework for cybersecurity engineering in road vehicles. This standard outlines processes for identifying and mitigating cybersecurity risks, including those related to BMS. Adherence to ISO/SAE 21434 is becoming increasingly important for automotive manufacturers and suppliers.
As the regulatory landscape continues to evolve, companies must stay informed about emerging standards and requirements. Regular audits and assessments are necessary to ensure ongoing compliance. Additionally, collaboration with regulatory bodies and participation in industry working groups can help organizations stay ahead of regulatory changes and contribute to the development of future standards.
Failure to comply with regulatory requirements can result in significant consequences, including fines, product recalls, and reputational damage. Therefore, integrating regulatory compliance into the security vulnerability assessment process for BMS is not only a legal necessity but also a critical business imperative.
Risk Mitigation Strategies
Risk mitigation strategies are crucial for addressing security vulnerabilities in Battery Management Systems (BMS). A comprehensive approach involves multiple layers of protection and proactive measures. One key strategy is the implementation of robust encryption protocols for all data transmissions within the BMS. This includes both internal communications between components and external interfaces with other vehicle systems or charging infrastructure. Advanced encryption algorithms, such as AES-256, should be employed to safeguard sensitive information from interception or tampering.
Another critical aspect of risk mitigation is the adoption of secure authentication mechanisms. Multi-factor authentication should be implemented for all access points to the BMS, ensuring that only authorized personnel can modify system parameters or access critical data. This can include a combination of hardware tokens, biometric verification, and secure passwords. Regular audits and updates of access credentials are essential to maintain the integrity of the authentication system.
Continuous monitoring and anomaly detection form another vital component of risk mitigation. Implementing real-time monitoring systems that can detect unusual patterns or behaviors within the BMS can help identify potential security breaches or cyberattacks in their early stages. Machine learning algorithms can be employed to establish baseline operational patterns and flag any deviations that may indicate a security threat.
Segmentation and isolation of critical BMS components can significantly reduce the potential impact of a security breach. By implementing logical or physical separation between different subsystems, the spread of a potential attack can be contained. This approach limits the attacker's ability to move laterally within the system and compromises the entire BMS.
Regular software updates and patch management are essential for addressing known vulnerabilities and improving overall system security. Establishing a robust update mechanism that can securely deliver and install firmware updates to BMS components is crucial. This process should include integrity checks to ensure that only authentic, unaltered updates are applied to the system.
Implementing a comprehensive incident response plan is another critical risk mitigation strategy. This plan should outline clear procedures for detecting, containing, and responding to security incidents. It should include steps for isolating affected components, preserving evidence for forensic analysis, and restoring normal operations. Regular drills and simulations can help ensure that the response team is well-prepared to handle various security scenarios effectively.
Another critical aspect of risk mitigation is the adoption of secure authentication mechanisms. Multi-factor authentication should be implemented for all access points to the BMS, ensuring that only authorized personnel can modify system parameters or access critical data. This can include a combination of hardware tokens, biometric verification, and secure passwords. Regular audits and updates of access credentials are essential to maintain the integrity of the authentication system.
Continuous monitoring and anomaly detection form another vital component of risk mitigation. Implementing real-time monitoring systems that can detect unusual patterns or behaviors within the BMS can help identify potential security breaches or cyberattacks in their early stages. Machine learning algorithms can be employed to establish baseline operational patterns and flag any deviations that may indicate a security threat.
Segmentation and isolation of critical BMS components can significantly reduce the potential impact of a security breach. By implementing logical or physical separation between different subsystems, the spread of a potential attack can be contained. This approach limits the attacker's ability to move laterally within the system and compromises the entire BMS.
Regular software updates and patch management are essential for addressing known vulnerabilities and improving overall system security. Establishing a robust update mechanism that can securely deliver and install firmware updates to BMS components is crucial. This process should include integrity checks to ensure that only authentic, unaltered updates are applied to the system.
Implementing a comprehensive incident response plan is another critical risk mitigation strategy. This plan should outline clear procedures for detecting, containing, and responding to security incidents. It should include steps for isolating affected components, preserving evidence for forensic analysis, and restoring normal operations. Regular drills and simulations can help ensure that the response team is well-prepared to handle various security scenarios effectively.
Unlock deeper insights with PatSnap Eureka Quick Research — get a full tech report to explore trends and direct your research. Try now!
Generate Your Research Report Instantly with AI Agent
Supercharge your innovation with PatSnap Eureka AI Agent Platform!