Optimize Data Encryption in Fixed Satellite Communications
MAR 18, 202610 MIN READ
Generate Your Research Report Instantly with AI Agent
Patsnap Eureka helps you evaluate technical feasibility & market potential.
Satellite Encryption Background and Security Objectives
Fixed satellite communications have evolved from simple relay systems to complex networks carrying critical data for government, military, commercial, and civilian applications. The inherent vulnerability of satellite links stems from their broadcast nature, where signals traverse vast distances through open space, making them susceptible to interception, jamming, and unauthorized access. Unlike terrestrial networks with physical security barriers, satellite communications operate in an inherently exposed environment where electromagnetic signals can be captured by any receiver within the coverage footprint.
The historical development of satellite encryption began in the 1960s with basic scrambling techniques for military communications. Early systems employed simple frequency hopping and analog encryption methods that provided minimal security against sophisticated adversaries. The transition to digital satellite communications in the 1980s marked a significant milestone, enabling the implementation of more robust cryptographic algorithms and key management systems.
Modern satellite networks face unprecedented security challenges due to increasing data volumes, diverse user requirements, and evolving threat landscapes. The proliferation of small satellites, mega-constellations, and commercial space activities has expanded the attack surface while introducing new vulnerabilities. State-sponsored cyber warfare, commercial espionage, and terrorist activities have elevated the importance of satellite communication security to national security levels.
Current encryption objectives in fixed satellite communications encompass multiple dimensions of security requirements. Confidentiality remains the primary goal, ensuring that sensitive information transmitted via satellite links remains protected from unauthorized disclosure. This includes protecting government communications, financial transactions, corporate data, and personal information from interception by hostile entities or unauthorized third parties.
Integrity assurance represents another critical objective, guaranteeing that transmitted data remains unaltered during transmission. Satellite links are vulnerable to signal manipulation, injection attacks, and data corruption, making integrity verification essential for mission-critical applications. Authentication mechanisms must verify the identity of communicating parties and ensure that only authorized users can access satellite resources.
The unique characteristics of satellite communications impose specific constraints on encryption implementation. High latency, limited bandwidth, power restrictions, and radiation-hardened hardware requirements necessitate specialized cryptographic solutions. Traditional encryption methods designed for terrestrial networks often prove inadequate for satellite environments, requiring optimization for space-based applications.
Emerging objectives include quantum-resistant encryption capabilities to address future threats from quantum computing technologies. As quantum computers advance toward practical implementation, current cryptographic algorithms face potential obsolescence, necessitating the development and deployment of post-quantum cryptographic solutions in satellite systems.
Real-time key management across global satellite networks presents ongoing challenges, requiring secure key distribution, rotation, and revocation mechanisms that operate effectively across multiple ground stations, satellites, and user terminals while maintaining operational continuity and security assurance.
The historical development of satellite encryption began in the 1960s with basic scrambling techniques for military communications. Early systems employed simple frequency hopping and analog encryption methods that provided minimal security against sophisticated adversaries. The transition to digital satellite communications in the 1980s marked a significant milestone, enabling the implementation of more robust cryptographic algorithms and key management systems.
Modern satellite networks face unprecedented security challenges due to increasing data volumes, diverse user requirements, and evolving threat landscapes. The proliferation of small satellites, mega-constellations, and commercial space activities has expanded the attack surface while introducing new vulnerabilities. State-sponsored cyber warfare, commercial espionage, and terrorist activities have elevated the importance of satellite communication security to national security levels.
Current encryption objectives in fixed satellite communications encompass multiple dimensions of security requirements. Confidentiality remains the primary goal, ensuring that sensitive information transmitted via satellite links remains protected from unauthorized disclosure. This includes protecting government communications, financial transactions, corporate data, and personal information from interception by hostile entities or unauthorized third parties.
Integrity assurance represents another critical objective, guaranteeing that transmitted data remains unaltered during transmission. Satellite links are vulnerable to signal manipulation, injection attacks, and data corruption, making integrity verification essential for mission-critical applications. Authentication mechanisms must verify the identity of communicating parties and ensure that only authorized users can access satellite resources.
The unique characteristics of satellite communications impose specific constraints on encryption implementation. High latency, limited bandwidth, power restrictions, and radiation-hardened hardware requirements necessitate specialized cryptographic solutions. Traditional encryption methods designed for terrestrial networks often prove inadequate for satellite environments, requiring optimization for space-based applications.
Emerging objectives include quantum-resistant encryption capabilities to address future threats from quantum computing technologies. As quantum computers advance toward practical implementation, current cryptographic algorithms face potential obsolescence, necessitating the development and deployment of post-quantum cryptographic solutions in satellite systems.
Real-time key management across global satellite networks presents ongoing challenges, requiring secure key distribution, rotation, and revocation mechanisms that operate effectively across multiple ground stations, satellites, and user terminals while maintaining operational continuity and security assurance.
Market Demand for Secure Satellite Communication Systems
The global satellite communication market is experiencing unprecedented growth driven by increasing demand for secure data transmission across multiple sectors. Government agencies, military organizations, and defense contractors represent the primary demand drivers for enhanced encryption capabilities in fixed satellite communications. These entities require robust security measures to protect classified information, strategic communications, and sensitive operational data from potential cyber threats and unauthorized interception.
Commercial enterprises are emerging as significant contributors to market demand, particularly in sectors handling sensitive data such as financial services, healthcare, and energy infrastructure. Banks and financial institutions rely on satellite communications for secure transaction processing and data backup services, especially in remote locations where terrestrial networks are unreliable. The healthcare sector increasingly depends on satellite-enabled telemedicine and remote patient monitoring systems, necessitating HIPAA-compliant encryption standards.
The proliferation of Internet of Things devices and remote sensing applications has created substantial demand for secure satellite data transmission. Oil and gas companies, mining operations, and agricultural enterprises operating in remote locations require encrypted satellite communications to protect proprietary data and maintain operational security. These industries face growing cybersecurity threats and regulatory compliance requirements that mandate advanced encryption protocols.
Critical infrastructure protection represents another major demand segment, encompassing power grids, water treatment facilities, and transportation networks that rely on satellite communications for monitoring and control systems. Recent cyberattacks on infrastructure have heightened awareness of vulnerabilities in satellite communication links, driving investment in advanced encryption technologies.
The maritime and aviation industries contribute significantly to market demand, requiring secure satellite communications for navigation, weather monitoring, and passenger services. International regulations and safety standards mandate encrypted communications for critical flight and vessel operations, creating consistent demand for optimized encryption solutions.
Emerging markets in developing regions present substantial growth opportunities as these areas increasingly adopt satellite communications for connectivity. Government initiatives to bridge digital divides and provide secure communications infrastructure in underserved regions are expanding the addressable market for encrypted satellite communication systems.
The demand landscape is further influenced by evolving regulatory frameworks and compliance requirements across different jurisdictions. Organizations must implement encryption standards that meet various national and international security protocols, driving the need for flexible and robust encryption optimization solutions in fixed satellite communication systems.
Commercial enterprises are emerging as significant contributors to market demand, particularly in sectors handling sensitive data such as financial services, healthcare, and energy infrastructure. Banks and financial institutions rely on satellite communications for secure transaction processing and data backup services, especially in remote locations where terrestrial networks are unreliable. The healthcare sector increasingly depends on satellite-enabled telemedicine and remote patient monitoring systems, necessitating HIPAA-compliant encryption standards.
The proliferation of Internet of Things devices and remote sensing applications has created substantial demand for secure satellite data transmission. Oil and gas companies, mining operations, and agricultural enterprises operating in remote locations require encrypted satellite communications to protect proprietary data and maintain operational security. These industries face growing cybersecurity threats and regulatory compliance requirements that mandate advanced encryption protocols.
Critical infrastructure protection represents another major demand segment, encompassing power grids, water treatment facilities, and transportation networks that rely on satellite communications for monitoring and control systems. Recent cyberattacks on infrastructure have heightened awareness of vulnerabilities in satellite communication links, driving investment in advanced encryption technologies.
The maritime and aviation industries contribute significantly to market demand, requiring secure satellite communications for navigation, weather monitoring, and passenger services. International regulations and safety standards mandate encrypted communications for critical flight and vessel operations, creating consistent demand for optimized encryption solutions.
Emerging markets in developing regions present substantial growth opportunities as these areas increasingly adopt satellite communications for connectivity. Government initiatives to bridge digital divides and provide secure communications infrastructure in underserved regions are expanding the addressable market for encrypted satellite communication systems.
The demand landscape is further influenced by evolving regulatory frameworks and compliance requirements across different jurisdictions. Organizations must implement encryption standards that meet various national and international security protocols, driving the need for flexible and robust encryption optimization solutions in fixed satellite communication systems.
Current Encryption Challenges in Fixed Satellite Networks
Fixed satellite communication networks face unprecedented encryption challenges as data transmission volumes surge and cyber threats become increasingly sophisticated. Traditional encryption methods, originally designed for terrestrial networks, struggle to address the unique characteristics of satellite environments, including extended signal propagation delays, limited bandwidth resources, and vulnerability to interception across vast coverage areas.
The most significant challenge stems from the inherent latency in geostationary satellite communications, where round-trip times can exceed 500 milliseconds. This delay severely impacts real-time key exchange protocols and authentication mechanisms, creating windows of vulnerability during handshake processes. Conventional encryption algorithms like RSA and AES, while robust in terrestrial applications, experience performance degradation when adapted to satellite network constraints.
Bandwidth limitations present another critical obstacle. Satellite transponders operate with finite spectrum allocations, making encryption overhead a costly burden. Current encryption implementations can consume 15-25% of available bandwidth through protocol headers, key management traffic, and redundant security layers. This overhead becomes particularly problematic for commercial satellite operators managing multiple concurrent data streams across different security domains.
Power consumption constraints on satellite platforms further complicate encryption deployment. Onboard processing units must balance computational complexity with energy efficiency, as excessive power draw can compromise mission longevity. Advanced encryption algorithms requiring intensive mathematical operations strain these limited resources, forcing operators to choose between security strength and operational sustainability.
The distributed nature of satellite networks creates key management complexities absent in centralized terrestrial systems. Coordinating encryption keys across multiple ground stations, satellite nodes, and user terminals requires sophisticated distribution mechanisms that remain vulnerable to timing attacks and synchronization failures. Legacy key management infrastructures lack the flexibility to handle dynamic satellite constellation changes and beam handovers.
Quantum computing threats pose an emerging challenge to current cryptographic foundations. While practical quantum computers capable of breaking RSA encryption remain years away, satellite systems with 15-20 year operational lifespans must consider post-quantum cryptographic migration strategies. The transition complexity is amplified by the difficulty of updating satellite-based encryption hardware once deployed.
Regulatory compliance adds another layer of complexity, as satellite operators must navigate varying encryption standards across different countries and regions. International data transmission requirements often conflict with national security restrictions, creating operational challenges for global satellite service providers managing cross-border communications while maintaining regulatory compliance across multiple jurisdictions.
The most significant challenge stems from the inherent latency in geostationary satellite communications, where round-trip times can exceed 500 milliseconds. This delay severely impacts real-time key exchange protocols and authentication mechanisms, creating windows of vulnerability during handshake processes. Conventional encryption algorithms like RSA and AES, while robust in terrestrial applications, experience performance degradation when adapted to satellite network constraints.
Bandwidth limitations present another critical obstacle. Satellite transponders operate with finite spectrum allocations, making encryption overhead a costly burden. Current encryption implementations can consume 15-25% of available bandwidth through protocol headers, key management traffic, and redundant security layers. This overhead becomes particularly problematic for commercial satellite operators managing multiple concurrent data streams across different security domains.
Power consumption constraints on satellite platforms further complicate encryption deployment. Onboard processing units must balance computational complexity with energy efficiency, as excessive power draw can compromise mission longevity. Advanced encryption algorithms requiring intensive mathematical operations strain these limited resources, forcing operators to choose between security strength and operational sustainability.
The distributed nature of satellite networks creates key management complexities absent in centralized terrestrial systems. Coordinating encryption keys across multiple ground stations, satellite nodes, and user terminals requires sophisticated distribution mechanisms that remain vulnerable to timing attacks and synchronization failures. Legacy key management infrastructures lack the flexibility to handle dynamic satellite constellation changes and beam handovers.
Quantum computing threats pose an emerging challenge to current cryptographic foundations. While practical quantum computers capable of breaking RSA encryption remain years away, satellite systems with 15-20 year operational lifespans must consider post-quantum cryptographic migration strategies. The transition complexity is amplified by the difficulty of updating satellite-based encryption hardware once deployed.
Regulatory compliance adds another layer of complexity, as satellite operators must navigate varying encryption standards across different countries and regions. International data transmission requirements often conflict with national security restrictions, creating operational challenges for global satellite service providers managing cross-border communications while maintaining regulatory compliance across multiple jurisdictions.
Existing Encryption Solutions for Satellite Communications
01 Symmetric key encryption methods
Symmetric key encryption utilizes the same key for both encryption and decryption processes. This approach offers high-speed data processing and is particularly suitable for encrypting large volumes of data. Common algorithms include AES, DES, and their variants. The method requires secure key distribution and management to maintain data confidentiality. Implementation can be optimized for various hardware and software platforms to achieve efficient encryption performance.- Symmetric key encryption methods: Symmetric key encryption utilizes the same key for both encryption and decryption processes. This approach offers high-speed data processing and is particularly efficient for encrypting large volumes of data. Common algorithms include AES, DES, and their variants. The main challenge lies in secure key distribution and management between parties.
- Public key infrastructure and asymmetric encryption: Asymmetric encryption employs a pair of keys - a public key for encryption and a private key for decryption. This method enables secure communication without prior key exchange and supports digital signatures for authentication. The technology is fundamental for secure online transactions and certificate-based authentication systems.
- Hybrid encryption systems combining multiple encryption techniques: Hybrid encryption systems combine the advantages of both symmetric and asymmetric encryption methods. These systems typically use asymmetric encryption for secure key exchange and symmetric encryption for actual data encryption, optimizing both security and performance. This approach is widely adopted in secure communication protocols and data protection frameworks.
- Key management and secure key storage solutions: Effective key management systems provide secure generation, distribution, storage, and destruction of cryptographic keys throughout their lifecycle. These solutions include hardware security modules, key escrow systems, and secure key derivation functions. Proper key management is critical for maintaining the overall security of encrypted systems.
- End-to-end encryption for secure data transmission: End-to-end encryption ensures that data remains encrypted during transmission from sender to recipient, preventing intermediate parties from accessing the plaintext. This technology is essential for protecting sensitive communications in messaging applications, email systems, and cloud storage services. Implementation includes secure channel establishment and authentication mechanisms.
02 Public key cryptography systems
Public key cryptography employs a pair of mathematically related keys, where one key encrypts data and the other decrypts it. This asymmetric approach eliminates the need for secure key exchange between parties. The system enables secure communication over insecure channels and supports digital signatures for authentication. RSA and elliptic curve cryptography are widely implemented algorithms in this category. The method is particularly useful for key exchange and establishing secure communication sessions.Expand Specific Solutions03 Key management and distribution systems
Effective key management systems provide secure generation, storage, distribution, and rotation of cryptographic keys throughout their lifecycle. These systems implement protocols for key establishment between multiple parties and ensure keys are protected from unauthorized access. Hierarchical key structures and key derivation functions enable scalable security architectures. The systems may include hardware security modules and secure key storage mechanisms. Automated key rotation and revocation procedures enhance overall security posture.Expand Specific Solutions04 Data encryption in storage and transmission
Encryption techniques for data at rest and in transit protect information from unauthorized access during storage and communication. These methods implement end-to-end encryption protocols that secure data across various network layers and storage media. The approach includes file-level, disk-level, and database encryption mechanisms. Stream ciphers and block ciphers are applied based on specific use cases and performance requirements. Integration with existing infrastructure ensures transparent encryption without significant performance degradation.Expand Specific Solutions05 Authentication and access control in encryption systems
Authentication mechanisms verify the identity of users and devices before granting access to encrypted data. Multi-factor authentication and biometric verification enhance security beyond traditional password-based systems. Access control policies define granular permissions for encrypted resources based on user roles and attributes. Token-based authentication and certificate-based systems provide scalable identity management. Integration of authentication with encryption ensures that only authorized parties can decrypt and access sensitive information.Expand Specific Solutions
Key Players in Satellite Encryption and Security Industry
The data encryption optimization in fixed satellite communications sector represents a rapidly evolving market driven by increasing cybersecurity demands and satellite constellation deployments. The industry is experiencing significant growth with substantial investments from telecommunications giants like China Mobile, China Telecom, and Huawei Technologies, alongside specialized satellite operators such as China Satellite Communications and China Star Network Application. Technology maturity varies considerably across players, with established telecommunications companies like Huawei and Hughes Network Systems demonstrating advanced encryption capabilities, while emerging companies like AtomBeam Technologies introduce innovative AI-driven data compression solutions. Research institutions including Tsinghua University and National University of Defense Technology contribute foundational research, while specialized security firms like Beijing Shudun Information Technology and Beijing Zhongdun Security Technology focus on cryptographic implementations. The competitive landscape shows a convergence of traditional telecom infrastructure providers, satellite operators, cybersecurity specialists, and academic institutions, indicating the sector's transition from nascent to growth phase with increasing technological sophistication.
China Satellite Communications Co., Ltd.
Technical Solution: China Satellite Communications has implemented a multi-layered encryption framework optimized for their Ka-band and Ku-band satellite networks. Their solution employs elliptic curve cryptography (ECC) combined with advanced stream ciphers, specifically designed to minimize computational overhead while maintaining robust security. The system features real-time key rotation mechanisms that adapt to satellite orbital patterns, ensuring continuous secure communications even during satellite handovers. Their proprietary compression-encryption hybrid algorithm reduces data payload by up to 30% while simultaneously applying encryption, significantly improving bandwidth efficiency in fixed satellite communications scenarios.
Strengths: Excellent bandwidth efficiency, proven satellite network integration, strong domestic market presence. Weaknesses: Limited global standardization, dependency on proprietary algorithms, potential scalability issues for international deployments.
Hughes Network Systems
Technical Solution: Hughes has developed the HughesON encryption suite specifically for satellite broadband and enterprise communications, featuring end-to-end encryption with forward secrecy capabilities. Their solution implements a hybrid approach combining RSA key exchange with AES-GCM for data encryption, optimized for high-throughput satellite (HTS) networks. The system includes intelligent traffic shaping that prioritizes encrypted data flows based on application requirements, supporting up to 10 Gbps throughput with less than 2ms additional latency. Hughes' solution also incorporates machine learning algorithms to detect and prevent potential security threats in real-time, while maintaining compatibility with existing VSAT infrastructure.
Strengths: Proven global deployment experience, excellent performance optimization, strong enterprise focus. Weaknesses: Higher licensing costs, limited customization options, dependency on Hughes hardware ecosystem.
Core Innovations in Satellite Data Protection Technologies
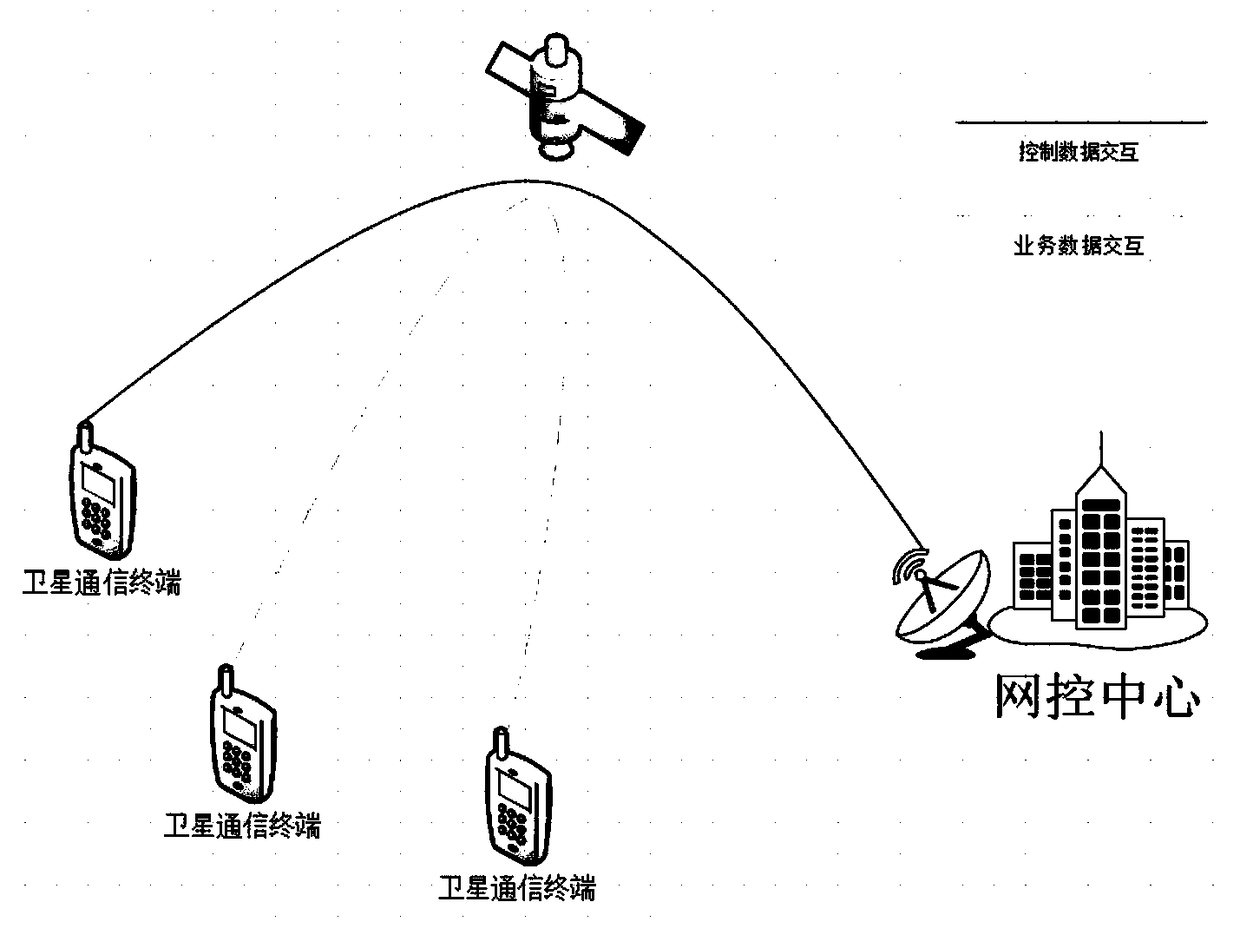
Satellite communication system encryption method based on RSA and AES
PatentActiveCN109462480A
Innovation
- Using encryption methods based on RSA and AES, the network control center broadcasts the RSA public key and generates the AES key to realize encrypted communication between the satellite terminal and the network control center, uses the RSA algorithm to securely transmit the AES key, and uses the AES key Perform data encryption and decryption, reduce hardware requirements, and improve encryption efficiency.
Encrypted satellite communications
PatentActiveEP4346255A1
Innovation
- A method utilizing a hardware-based cryptoprocessor to establish a secure transport-layer session via satellite, generating cryptographic key pairs, and encrypting payload data using a shared key, while employing protocols like QUIC and TLS 1.3 to ensure secure and efficient communication without significant modifications to existing systems.
Regulatory Framework for Satellite Communication Security
The regulatory framework for satellite communication security represents a complex multi-layered governance structure that spans international, national, and industry-specific jurisdictions. At the international level, the International Telecommunication Union (ITU) serves as the primary coordinating body, establishing fundamental principles for satellite spectrum allocation and orbital slot management while providing baseline security recommendations through its ITU-T Study Groups.
Regional regulatory bodies such as the Federal Communications Commission (FCC) in the United States, the European Communications Committee (ECC) under CEPT, and similar organizations in other jurisdictions have developed comprehensive frameworks specifically addressing encryption requirements for fixed satellite services. These regulations typically mandate minimum encryption standards, key management protocols, and compliance reporting mechanisms for commercial satellite operators.
The regulatory landscape has evolved significantly following high-profile cybersecurity incidents in space-based infrastructure. Recent regulatory updates have introduced stricter requirements for end-to-end encryption in fixed satellite communications, particularly for critical infrastructure applications. The FCC's 2022 Space Innovation rules, for instance, require detailed cybersecurity plans including encryption protocols for all new satellite system applications.
Compliance frameworks now emphasize risk-based approaches to encryption implementation, requiring operators to demonstrate adequate protection levels based on data sensitivity classifications. The European Union's NIS2 Directive extends cybersecurity requirements to satellite communication providers, mandating specific encryption standards and incident reporting procedures.
Industry-specific regulations add additional layers of complexity, particularly in sectors such as maritime communications, aviation, and government services. The International Maritime Organization (IMO) and International Civil Aviation Organization (ICAO) have established sector-specific encryption requirements that satellite communication providers must accommodate.
Cross-border data protection regulations, including GDPR and similar privacy frameworks, create additional encryption obligations for satellite operators handling personal data across international boundaries. These regulations often require specific encryption algorithms, key lengths, and data residency controls that directly impact satellite communication system design and operation.
Regional regulatory bodies such as the Federal Communications Commission (FCC) in the United States, the European Communications Committee (ECC) under CEPT, and similar organizations in other jurisdictions have developed comprehensive frameworks specifically addressing encryption requirements for fixed satellite services. These regulations typically mandate minimum encryption standards, key management protocols, and compliance reporting mechanisms for commercial satellite operators.
The regulatory landscape has evolved significantly following high-profile cybersecurity incidents in space-based infrastructure. Recent regulatory updates have introduced stricter requirements for end-to-end encryption in fixed satellite communications, particularly for critical infrastructure applications. The FCC's 2022 Space Innovation rules, for instance, require detailed cybersecurity plans including encryption protocols for all new satellite system applications.
Compliance frameworks now emphasize risk-based approaches to encryption implementation, requiring operators to demonstrate adequate protection levels based on data sensitivity classifications. The European Union's NIS2 Directive extends cybersecurity requirements to satellite communication providers, mandating specific encryption standards and incident reporting procedures.
Industry-specific regulations add additional layers of complexity, particularly in sectors such as maritime communications, aviation, and government services. The International Maritime Organization (IMO) and International Civil Aviation Organization (ICAO) have established sector-specific encryption requirements that satellite communication providers must accommodate.
Cross-border data protection regulations, including GDPR and similar privacy frameworks, create additional encryption obligations for satellite operators handling personal data across international boundaries. These regulations often require specific encryption algorithms, key lengths, and data residency controls that directly impact satellite communication system design and operation.
Performance Impact Assessment of Encryption on Satellite Links
The implementation of encryption algorithms in fixed satellite communication systems introduces measurable performance overhead that directly affects link efficiency and operational characteristics. Encryption processes consume computational resources at both transmission and reception endpoints, creating latency that ranges from microseconds for hardware-accelerated implementations to several milliseconds for software-based solutions. This processing delay becomes particularly significant in geostationary satellite links where inherent propagation delays already exceed 250 milliseconds for round-trip communications.
Throughput degradation represents another critical performance consideration when deploying encryption in satellite links. Advanced Encryption Standard (AES) implementations typically reduce effective data rates by 5-15% depending on key length and operational mode. Stream ciphers generally exhibit lower throughput impact compared to block ciphers, but the choice often depends on security requirements rather than performance optimization alone. The overhead becomes more pronounced in high-frequency trading applications or real-time control systems where every millisecond affects operational effectiveness.
Power consumption increases substantially when encryption hardware operates continuously in satellite terminals. Field-Programmable Gate Arrays (FPGAs) configured for encryption tasks can consume 20-40% additional power compared to unencrypted transmission modes. This power overhead directly impacts satellite terminal battery life and thermal management requirements, particularly in remote installations where power resources are constrained. The trade-off between security strength and power efficiency becomes crucial in designing sustainable satellite communication architectures.
Memory utilization patterns change significantly with encryption implementation, as cryptographic algorithms require dedicated buffer space for key storage, intermediate calculations, and data queuing. Modern encryption standards demand between 2-8 MB of dedicated memory per active channel, which can strain resource-limited satellite terminals. The memory footprint grows exponentially when supporting multiple simultaneous encrypted channels or implementing quantum-resistant algorithms that require larger key sizes.
Network protocol efficiency suffers measurable degradation when encryption layers are inserted into satellite communication stacks. Header overhead from cryptographic protocols adds 16-64 bytes per packet, reducing payload efficiency in bandwidth-constrained satellite links. The cumulative effect of encryption overhead, combined with satellite-specific protocol adaptations for error correction and flow control, can reduce overall link utilization by 10-25% compared to unencrypted alternatives.
Throughput degradation represents another critical performance consideration when deploying encryption in satellite links. Advanced Encryption Standard (AES) implementations typically reduce effective data rates by 5-15% depending on key length and operational mode. Stream ciphers generally exhibit lower throughput impact compared to block ciphers, but the choice often depends on security requirements rather than performance optimization alone. The overhead becomes more pronounced in high-frequency trading applications or real-time control systems where every millisecond affects operational effectiveness.
Power consumption increases substantially when encryption hardware operates continuously in satellite terminals. Field-Programmable Gate Arrays (FPGAs) configured for encryption tasks can consume 20-40% additional power compared to unencrypted transmission modes. This power overhead directly impacts satellite terminal battery life and thermal management requirements, particularly in remote installations where power resources are constrained. The trade-off between security strength and power efficiency becomes crucial in designing sustainable satellite communication architectures.
Memory utilization patterns change significantly with encryption implementation, as cryptographic algorithms require dedicated buffer space for key storage, intermediate calculations, and data queuing. Modern encryption standards demand between 2-8 MB of dedicated memory per active channel, which can strain resource-limited satellite terminals. The memory footprint grows exponentially when supporting multiple simultaneous encrypted channels or implementing quantum-resistant algorithms that require larger key sizes.
Network protocol efficiency suffers measurable degradation when encryption layers are inserted into satellite communication stacks. Header overhead from cryptographic protocols adds 16-64 bytes per packet, reducing payload efficiency in bandwidth-constrained satellite links. The cumulative effect of encryption overhead, combined with satellite-specific protocol adaptations for error correction and flow control, can reduce overall link utilization by 10-25% compared to unencrypted alternatives.
Unlock deeper insights with Patsnap Eureka Quick Research — get a full tech report to explore trends and direct your research. Try now!
Generate Your Research Report Instantly with AI Agent
Supercharge your innovation with Patsnap Eureka AI Agent Platform!