Secure Authentication Methods for Fixed Satellite Networks
MAR 18, 20269 MIN READ
Generate Your Research Report Instantly with AI Agent
Patsnap Eureka helps you evaluate technical feasibility & market potential.
Satellite Authentication Background and Security Goals
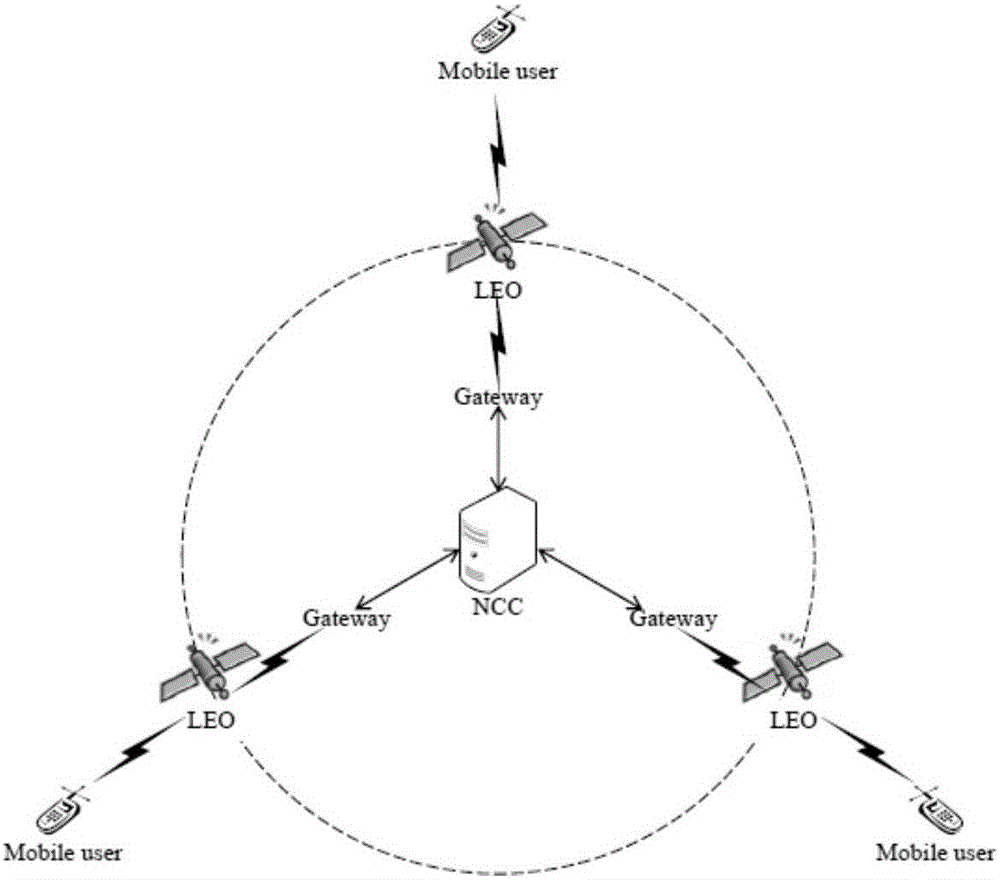
Fixed satellite networks have evolved from simple communication relays to complex, multi-layered systems supporting critical infrastructure across telecommunications, broadcasting, navigation, and defense sectors. The proliferation of satellite-based services has fundamentally transformed global connectivity, enabling seamless communication across vast geographical distances and supporting mission-critical applications ranging from financial transactions to emergency response systems.
The historical development of satellite authentication has progressed through distinct phases, beginning with basic physical security measures in early satellite systems to sophisticated cryptographic protocols in modern networks. Initial satellite communications relied primarily on signal encryption and frequency management, with limited consideration for comprehensive authentication frameworks. As satellite networks became increasingly integrated with terrestrial internet infrastructure, the attack surface expanded significantly, necessitating robust authentication mechanisms.
Contemporary satellite networks face unprecedented security challenges due to their inherent architectural vulnerabilities. The broadcast nature of satellite communications creates opportunities for eavesdropping, signal interception, and unauthorized access attempts. Unlike terrestrial networks with physical access controls, satellite signals traverse open space, making them susceptible to various attack vectors including jamming, spoofing, and man-in-the-middle attacks.
The unique operational environment of satellite networks introduces specific authentication requirements that differ substantially from terrestrial systems. High latency inherent in geostationary satellite communications, typically ranging from 250 to 600 milliseconds, significantly impacts real-time authentication protocols. Additionally, the limited computational resources available on satellite platforms constrain the complexity of authentication algorithms that can be implemented effectively.
Modern satellite authentication systems must address multiple security objectives simultaneously. Primary goals include ensuring the integrity of command and control communications, preventing unauthorized access to satellite resources, and maintaining service availability despite potential cyber attacks. Authentication mechanisms must verify the legitimacy of ground stations, satellite operators, and end-users while protecting against sophisticated adversaries with substantial resources.
The integration of satellite networks with 5G and future 6G terrestrial networks has elevated security requirements, demanding seamless authentication across heterogeneous network environments. This convergence necessitates authentication protocols that can operate effectively across different network architectures while maintaining consistent security levels and user experience standards throughout the integrated communication ecosystem.
The historical development of satellite authentication has progressed through distinct phases, beginning with basic physical security measures in early satellite systems to sophisticated cryptographic protocols in modern networks. Initial satellite communications relied primarily on signal encryption and frequency management, with limited consideration for comprehensive authentication frameworks. As satellite networks became increasingly integrated with terrestrial internet infrastructure, the attack surface expanded significantly, necessitating robust authentication mechanisms.
Contemporary satellite networks face unprecedented security challenges due to their inherent architectural vulnerabilities. The broadcast nature of satellite communications creates opportunities for eavesdropping, signal interception, and unauthorized access attempts. Unlike terrestrial networks with physical access controls, satellite signals traverse open space, making them susceptible to various attack vectors including jamming, spoofing, and man-in-the-middle attacks.
The unique operational environment of satellite networks introduces specific authentication requirements that differ substantially from terrestrial systems. High latency inherent in geostationary satellite communications, typically ranging from 250 to 600 milliseconds, significantly impacts real-time authentication protocols. Additionally, the limited computational resources available on satellite platforms constrain the complexity of authentication algorithms that can be implemented effectively.
Modern satellite authentication systems must address multiple security objectives simultaneously. Primary goals include ensuring the integrity of command and control communications, preventing unauthorized access to satellite resources, and maintaining service availability despite potential cyber attacks. Authentication mechanisms must verify the legitimacy of ground stations, satellite operators, and end-users while protecting against sophisticated adversaries with substantial resources.
The integration of satellite networks with 5G and future 6G terrestrial networks has elevated security requirements, demanding seamless authentication across heterogeneous network environments. This convergence necessitates authentication protocols that can operate effectively across different network architectures while maintaining consistent security levels and user experience standards throughout the integrated communication ecosystem.
Market Demand for Secure Satellite Communication
The global satellite communication market is experiencing unprecedented growth driven by increasing demand for secure, reliable connectivity across diverse sectors. Government and defense agencies represent the largest consumer segment, requiring robust authentication mechanisms to protect classified communications, military operations, and national security infrastructure. These organizations demand end-to-end encryption and multi-layered authentication protocols that can withstand sophisticated cyber threats and maintain operational integrity in contested environments.
Commercial enterprises are rapidly expanding their reliance on satellite networks for critical business operations, particularly in remote locations where terrestrial infrastructure is unavailable or unreliable. Industries such as oil and gas, mining, maritime shipping, and aviation require secure authentication methods to protect proprietary data, financial transactions, and operational control systems. The growing adoption of Internet of Things devices in these sectors further amplifies the need for scalable authentication solutions that can handle thousands of simultaneous connections.
Financial services institutions increasingly utilize satellite networks for backup communications, disaster recovery, and operations in underserved regions. These organizations face stringent regulatory requirements for data protection and transaction security, driving demand for authentication systems that comply with international standards such as Common Criteria and FIPS 140-2. The rise of satellite-based payment systems and mobile banking services in developing markets creates additional requirements for lightweight yet robust authentication protocols.
The emergence of mega-constellations and low Earth orbit satellite networks has transformed market dynamics, creating new opportunities for secure communication services. These networks enable global broadband coverage but introduce unique security challenges due to their distributed architecture and frequent handoffs between satellites. Service providers require authentication methods that can maintain security while supporting seamless connectivity across multiple satellites and ground stations.
Critical infrastructure sectors including power grids, water systems, and transportation networks increasingly depend on satellite communications for monitoring and control systems. Recent cyber attacks on infrastructure have heightened awareness of security vulnerabilities, driving demand for authentication solutions that can prevent unauthorized access and ensure system integrity. These applications require authentication methods that operate reliably in harsh environments while maintaining low latency for real-time control applications.
The growing threat landscape, including state-sponsored cyber attacks and sophisticated hacking groups, has elevated security requirements across all market segments. Organizations seek authentication solutions that incorporate quantum-resistant cryptography, biometric verification, and behavioral analysis to stay ahead of evolving threats. This trend is particularly pronounced in sectors handling sensitive data or critical operations where security breaches could have catastrophic consequences.
Commercial enterprises are rapidly expanding their reliance on satellite networks for critical business operations, particularly in remote locations where terrestrial infrastructure is unavailable or unreliable. Industries such as oil and gas, mining, maritime shipping, and aviation require secure authentication methods to protect proprietary data, financial transactions, and operational control systems. The growing adoption of Internet of Things devices in these sectors further amplifies the need for scalable authentication solutions that can handle thousands of simultaneous connections.
Financial services institutions increasingly utilize satellite networks for backup communications, disaster recovery, and operations in underserved regions. These organizations face stringent regulatory requirements for data protection and transaction security, driving demand for authentication systems that comply with international standards such as Common Criteria and FIPS 140-2. The rise of satellite-based payment systems and mobile banking services in developing markets creates additional requirements for lightweight yet robust authentication protocols.
The emergence of mega-constellations and low Earth orbit satellite networks has transformed market dynamics, creating new opportunities for secure communication services. These networks enable global broadband coverage but introduce unique security challenges due to their distributed architecture and frequent handoffs between satellites. Service providers require authentication methods that can maintain security while supporting seamless connectivity across multiple satellites and ground stations.
Critical infrastructure sectors including power grids, water systems, and transportation networks increasingly depend on satellite communications for monitoring and control systems. Recent cyber attacks on infrastructure have heightened awareness of security vulnerabilities, driving demand for authentication solutions that can prevent unauthorized access and ensure system integrity. These applications require authentication methods that operate reliably in harsh environments while maintaining low latency for real-time control applications.
The growing threat landscape, including state-sponsored cyber attacks and sophisticated hacking groups, has elevated security requirements across all market segments. Organizations seek authentication solutions that incorporate quantum-resistant cryptography, biometric verification, and behavioral analysis to stay ahead of evolving threats. This trend is particularly pronounced in sectors handling sensitive data or critical operations where security breaches could have catastrophic consequences.
Current State and Vulnerabilities of Satellite Authentication
Fixed satellite networks currently employ a variety of authentication mechanisms, ranging from traditional cryptographic protocols to more advanced quantum-resistant solutions. The predominant authentication frameworks include Public Key Infrastructure (PKI) systems, symmetric key management protocols, and hybrid authentication schemes that combine multiple verification layers. Most operational satellite systems rely on ground-based certificate authorities and pre-shared key distributions, which have served adequately for closed network environments but face increasing challenges as satellite networks expand and interconnect.
The authentication landscape in satellite communications is characterized by significant heterogeneity across different operators and mission types. Commercial satellite operators typically implement proprietary authentication protocols optimized for their specific network architectures, while military and government systems employ more stringent security frameworks with enhanced encryption standards. This fragmentation creates interoperability challenges and potential security gaps when different satellite systems need to communicate or share resources.
Current satellite authentication systems face several critical vulnerabilities that threaten network security. Signal interception remains a primary concern, as satellite communications traverse vast distances through open space, making them susceptible to eavesdropping and man-in-the-middle attacks. The high latency inherent in satellite communications complicates real-time authentication processes, creating windows of opportunity for malicious actors to exploit timing-based vulnerabilities.
Ground segment security represents another significant weakness in the authentication chain. Many satellite networks rely heavily on terrestrial infrastructure for key management and certificate validation, creating single points of failure that can compromise entire network segments. The distributed nature of ground stations across multiple geographic locations further complicates security management and increases the attack surface.
Emerging threats include sophisticated spoofing attacks that exploit GPS and timing synchronization vulnerabilities, potentially allowing unauthorized entities to masquerade as legitimate network participants. Advanced persistent threats targeting satellite control systems have demonstrated the ability to compromise authentication mechanisms through supply chain infiltration and insider threats.
The integration of commercial off-the-shelf components in satellite systems introduces additional vulnerabilities, as these components may not be designed to withstand the unique security challenges of space-based operations. Legacy systems operating with outdated authentication protocols present particular risks, as they often lack the computational resources necessary to implement modern security measures while remaining vulnerable to increasingly sophisticated attack vectors.
The authentication landscape in satellite communications is characterized by significant heterogeneity across different operators and mission types. Commercial satellite operators typically implement proprietary authentication protocols optimized for their specific network architectures, while military and government systems employ more stringent security frameworks with enhanced encryption standards. This fragmentation creates interoperability challenges and potential security gaps when different satellite systems need to communicate or share resources.
Current satellite authentication systems face several critical vulnerabilities that threaten network security. Signal interception remains a primary concern, as satellite communications traverse vast distances through open space, making them susceptible to eavesdropping and man-in-the-middle attacks. The high latency inherent in satellite communications complicates real-time authentication processes, creating windows of opportunity for malicious actors to exploit timing-based vulnerabilities.
Ground segment security represents another significant weakness in the authentication chain. Many satellite networks rely heavily on terrestrial infrastructure for key management and certificate validation, creating single points of failure that can compromise entire network segments. The distributed nature of ground stations across multiple geographic locations further complicates security management and increases the attack surface.
Emerging threats include sophisticated spoofing attacks that exploit GPS and timing synchronization vulnerabilities, potentially allowing unauthorized entities to masquerade as legitimate network participants. Advanced persistent threats targeting satellite control systems have demonstrated the ability to compromise authentication mechanisms through supply chain infiltration and insider threats.
The integration of commercial off-the-shelf components in satellite systems introduces additional vulnerabilities, as these components may not be designed to withstand the unique security challenges of space-based operations. Legacy systems operating with outdated authentication protocols present particular risks, as they often lack the computational resources necessary to implement modern security measures while remaining vulnerable to increasingly sophisticated attack vectors.
Existing Authentication Solutions for Fixed Satellite Networks
01 Multi-factor authentication systems
Authentication security can be enhanced through multi-factor authentication approaches that combine multiple verification methods. These systems typically require users to provide two or more authentication factors from different categories, such as knowledge-based factors, possession-based factors, or biometric factors. By implementing multiple layers of verification, the security of authentication processes is significantly strengthened, reducing the risk of unauthorized access even if one authentication factor is compromised.- Multi-factor authentication systems: Authentication security can be enhanced through multi-factor authentication methods that combine multiple verification elements such as passwords, biometric data, tokens, or one-time codes. These systems require users to provide two or more authentication factors from different categories to verify their identity, significantly reducing the risk of unauthorized access. The implementation of multi-factor authentication provides layered security by ensuring that even if one factor is compromised, additional factors still protect the system.
- Biometric authentication methods: Biometric authentication utilizes unique physical or behavioral characteristics of individuals for identity verification. These methods include fingerprint recognition, facial recognition, iris scanning, voice recognition, and other biological traits that are difficult to replicate or steal. Biometric authentication provides a high level of security as these characteristics are inherently tied to the individual and cannot be easily transferred or forgotten like traditional passwords.
- Token-based authentication and cryptographic methods: Token-based authentication systems use cryptographic tokens or digital certificates to verify user identity. These tokens can be hardware devices, software applications, or cryptographic keys that generate time-sensitive codes or digital signatures. The authentication process involves cryptographic algorithms that ensure secure communication between the user and the system, protecting against interception and replay attacks. This method provides strong security through encryption and can be combined with other authentication factors.
- Adaptive and risk-based authentication: Adaptive authentication systems analyze contextual information and user behavior patterns to assess risk levels and adjust authentication requirements accordingly. These systems consider factors such as device information, location, time of access, and historical behavior patterns to determine the appropriate level of authentication needed. When suspicious activity or high-risk scenarios are detected, additional verification steps are triggered to ensure security while maintaining user convenience in low-risk situations.
- Secure credential storage and transmission: Security of authentication methods relies heavily on the secure storage and transmission of credentials and authentication data. This includes encryption of stored passwords, secure hashing algorithms, protected communication channels, and secure key management systems. These techniques prevent unauthorized access to sensitive authentication information and protect against various attack vectors such as credential theft, man-in-the-middle attacks, and database breaches. Implementation of secure protocols and encryption standards ensures that authentication data remains confidential throughout its lifecycle.
02 Biometric authentication methods
Biometric authentication utilizes unique physical or behavioral characteristics of individuals to verify identity. These methods can include fingerprint recognition, facial recognition, iris scanning, or voice recognition. Biometric authentication provides a high level of security as these characteristics are difficult to replicate or steal. The integration of biometric data into authentication systems offers a more secure and user-friendly alternative to traditional password-based methods.Expand Specific Solutions03 Token-based authentication protocols
Token-based authentication involves the generation and validation of security tokens to verify user identity. These tokens can be hardware devices, software applications, or cryptographic keys that generate time-sensitive codes. The authentication process validates these tokens against stored credentials, providing secure access without repeatedly transmitting sensitive information. This approach enhances security by limiting the exposure of authentication credentials and enabling session management.Expand Specific Solutions04 Cryptographic key management for authentication
Secure authentication relies on robust cryptographic key management systems that handle the generation, distribution, storage, and rotation of encryption keys. These systems employ advanced encryption algorithms to protect authentication data during transmission and storage. Proper key management ensures that authentication credentials remain secure throughout their lifecycle, preventing unauthorized access through key compromise. The implementation of secure key exchange protocols and regular key rotation further strengthens the overall authentication security framework.Expand Specific Solutions05 Adaptive authentication and risk-based access control
Adaptive authentication systems dynamically adjust security requirements based on contextual factors and risk assessment. These systems analyze various parameters such as user behavior patterns, device characteristics, location data, and access patterns to determine the appropriate level of authentication required. By implementing risk-based access control, the authentication process can require additional verification steps when suspicious activities are detected, while providing streamlined access for low-risk scenarios. This approach balances security with user experience.Expand Specific Solutions
Key Players in Satellite Security and Authentication Industry
The secure authentication methods for fixed satellite networks represent an emerging yet critical technology sector driven by increasing satellite constellation deployments and cybersecurity concerns. The market is experiencing rapid growth as satellite communications expand beyond traditional applications into commercial broadband, IoT, and autonomous systems. Technology maturity varies significantly across players, with established telecommunications giants like China Telecom, China Mobile, and Huawei leading infrastructure development, while aerospace leaders Boeing and defense specialists Thales DIS contribute advanced security protocols. Research institutions including Xidian University and ETRI are advancing cryptographic innovations, while network security specialists like Palo Alto Networks bring cybersecurity expertise. The competitive landscape shows convergence between satellite operators, telecommunications providers, and security vendors, indicating the technology's transition from experimental to deployment-ready solutions for next-generation satellite networks.
Thales DIS France SA
Technical Solution: Thales develops comprehensive satellite authentication solutions utilizing advanced cryptographic protocols including quantum-resistant algorithms and hardware security modules (HSMs). Their approach integrates multi-layered security architecture with PKI-based certificate management systems specifically designed for satellite communications. The solution incorporates real-time key management protocols that can handle the dynamic nature of satellite networks, including handover scenarios and orbital mechanics considerations. Their authentication framework supports both ground-to-satellite and inter-satellite authentication mechanisms with end-to-end encryption capabilities.
Strengths: Proven aerospace security expertise and quantum-resistant cryptography. Weaknesses: High implementation complexity and cost for smaller satellite operators.
Huawei Technologies Co., Ltd.
Technical Solution: Huawei's satellite authentication solution leverages their 5G security framework adapted for Non-Terrestrial Networks (NTN). The system employs enhanced Authentication and Key Agreement (AKA) protocols with satellite-specific modifications to handle propagation delays and Doppler effects. Their approach includes distributed authentication servers positioned strategically to minimize latency, combined with blockchain-based identity verification for enhanced security. The solution supports seamless integration with terrestrial networks while maintaining consistent security policies across hybrid satellite-terrestrial infrastructures.
Strengths: Strong integration with 5G standards and comprehensive network infrastructure experience. Weaknesses: Potential geopolitical restrictions and limited adoption in certain markets.
Core Innovations in Satellite Authentication Protocols
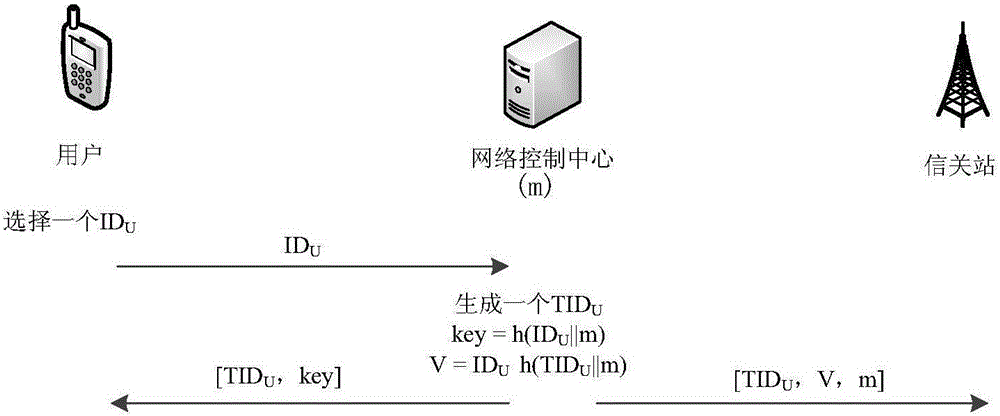
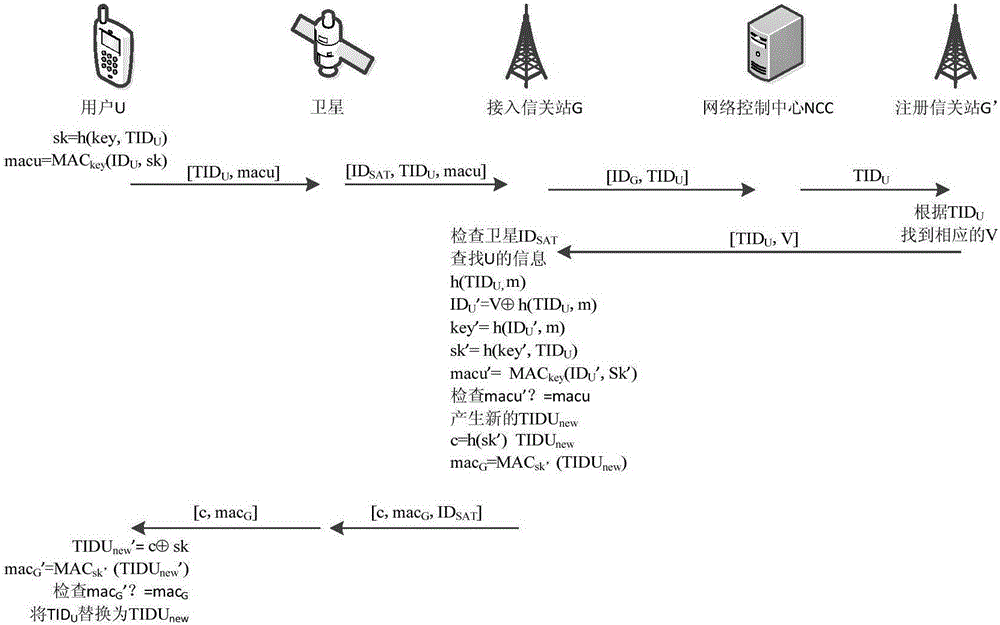
Gateway station-based satellite network anonymous authentication method
PatentActiveCN105827304A
Innovation
- Adopt the anonymous authentication method of satellite network based on the gateway station, transfer the authorization authentication function to the gateway station, and use the message authentication code (MAC) during the authentication process to achieve anonymous user authentication and satellite user security authentication, achieving two-way authentication purpose.
Identity authentication method of satellite in orbit
PatentActiveCN106850674A
Innovation
- Adopt a two-way identity authentication mechanism based on public and private keys, through location verification and identity verification, and use ECC and MD5/DES/AES algorithms for encryption protection, reducing resource usage and improving security strength.
Regulatory Framework for Satellite Communication Security
The regulatory framework for satellite communication security has evolved significantly over the past two decades, driven by increasing concerns about cybersecurity threats and the critical role of satellite networks in global communications infrastructure. International organizations, national governments, and industry bodies have established comprehensive guidelines to ensure secure authentication methods are properly implemented and maintained across fixed satellite networks.
At the international level, the International Telecommunication Union (ITU) has developed fundamental security recommendations through its ITU-T Study Group 17, which addresses telecommunications security, cybersecurity, and privacy. These recommendations provide baseline security requirements for satellite operators, including mandatory authentication protocols and encryption standards. The ITU Radio Regulations also specify technical parameters that indirectly support security implementations by defining frequency coordination and interference mitigation measures.
National regulatory authorities have implemented varying approaches to satellite communication security oversight. The Federal Communications Commission (FCC) in the United States has established specific cybersecurity requirements for satellite operators, mandating risk assessments, incident reporting, and implementation of robust authentication mechanisms. Similarly, the European Telecommunications Standards Institute (ETSI) has developed technical specifications for satellite security, including detailed requirements for user authentication and network access control.
Industry-specific regulations have emerged to address sector-critical applications. The aviation industry operates under International Civil Aviation Organization (ICAO) standards that mandate specific authentication protocols for aeronautical satellite communications. Maritime satellite communications are governed by International Maritime Organization (IMO) regulations, which require certified security measures for safety-critical communications systems.
Compliance frameworks typically require satellite operators to demonstrate adherence to established security standards through regular audits and certifications. These frameworks mandate documentation of authentication procedures, vulnerability assessments, and incident response capabilities. Operators must also maintain detailed logs of authentication events and provide regular security reports to regulatory authorities.
The regulatory landscape continues to evolve as new threats emerge and technology advances. Recent developments include enhanced requirements for quantum-resistant authentication methods and stricter guidelines for supply chain security in satellite network components.
At the international level, the International Telecommunication Union (ITU) has developed fundamental security recommendations through its ITU-T Study Group 17, which addresses telecommunications security, cybersecurity, and privacy. These recommendations provide baseline security requirements for satellite operators, including mandatory authentication protocols and encryption standards. The ITU Radio Regulations also specify technical parameters that indirectly support security implementations by defining frequency coordination and interference mitigation measures.
National regulatory authorities have implemented varying approaches to satellite communication security oversight. The Federal Communications Commission (FCC) in the United States has established specific cybersecurity requirements for satellite operators, mandating risk assessments, incident reporting, and implementation of robust authentication mechanisms. Similarly, the European Telecommunications Standards Institute (ETSI) has developed technical specifications for satellite security, including detailed requirements for user authentication and network access control.
Industry-specific regulations have emerged to address sector-critical applications. The aviation industry operates under International Civil Aviation Organization (ICAO) standards that mandate specific authentication protocols for aeronautical satellite communications. Maritime satellite communications are governed by International Maritime Organization (IMO) regulations, which require certified security measures for safety-critical communications systems.
Compliance frameworks typically require satellite operators to demonstrate adherence to established security standards through regular audits and certifications. These frameworks mandate documentation of authentication procedures, vulnerability assessments, and incident response capabilities. Operators must also maintain detailed logs of authentication events and provide regular security reports to regulatory authorities.
The regulatory landscape continues to evolve as new threats emerge and technology advances. Recent developments include enhanced requirements for quantum-resistant authentication methods and stricter guidelines for supply chain security in satellite network components.
Space Debris Impact on Authentication Infrastructure
Space debris poses an increasingly critical threat to the authentication infrastructure of fixed satellite networks, fundamentally challenging the reliability and continuity of secure communication systems. The proliferation of orbital debris, ranging from defunct satellites to microscopic fragments from collisions, creates a hostile environment where authentication hardware and communication pathways face constant risk of physical damage or complete destruction.
The vulnerability of authentication infrastructure to debris impact manifests across multiple system components. Ground-based authentication servers and satellite tracking stations represent primary targets, where even small debris fragments traveling at hypervelocities can cause catastrophic damage to sensitive electronic equipment. The cascading effect of such impacts extends beyond immediate hardware destruction, potentially compromising cryptographic key storage systems and authentication databases that maintain network security protocols.
Satellite-based authentication nodes face particularly acute risks due to their extended exposure in debris-dense orbital regions. The loss of a single authentication satellite can create significant coverage gaps, forcing network operators to implement emergency authentication protocols that may compromise security standards. The cumulative effect of multiple debris impacts across a constellation can lead to systematic authentication failures, rendering entire network segments inaccessible or vulnerable to unauthorized access.
The temporal unpredictability of debris encounters introduces additional complexity to authentication infrastructure planning. Unlike terrestrial systems where physical security can be reasonably assured, satellite networks must account for random collision events that can instantly disable critical authentication components. This uncertainty necessitates robust redundancy mechanisms and rapid recovery protocols to maintain authentication services during and after debris impact events.
Mitigation strategies for debris-related authentication infrastructure damage require comprehensive risk assessment frameworks that integrate orbital debris tracking data with authentication system architecture. Advanced shielding technologies for critical authentication hardware, coupled with distributed authentication protocols that can dynamically reroute around damaged nodes, represent essential defensive measures against debris-induced system failures.
The vulnerability of authentication infrastructure to debris impact manifests across multiple system components. Ground-based authentication servers and satellite tracking stations represent primary targets, where even small debris fragments traveling at hypervelocities can cause catastrophic damage to sensitive electronic equipment. The cascading effect of such impacts extends beyond immediate hardware destruction, potentially compromising cryptographic key storage systems and authentication databases that maintain network security protocols.
Satellite-based authentication nodes face particularly acute risks due to their extended exposure in debris-dense orbital regions. The loss of a single authentication satellite can create significant coverage gaps, forcing network operators to implement emergency authentication protocols that may compromise security standards. The cumulative effect of multiple debris impacts across a constellation can lead to systematic authentication failures, rendering entire network segments inaccessible or vulnerable to unauthorized access.
The temporal unpredictability of debris encounters introduces additional complexity to authentication infrastructure planning. Unlike terrestrial systems where physical security can be reasonably assured, satellite networks must account for random collision events that can instantly disable critical authentication components. This uncertainty necessitates robust redundancy mechanisms and rapid recovery protocols to maintain authentication services during and after debris impact events.
Mitigation strategies for debris-related authentication infrastructure damage require comprehensive risk assessment frameworks that integrate orbital debris tracking data with authentication system architecture. Advanced shielding technologies for critical authentication hardware, coupled with distributed authentication protocols that can dynamically reroute around damaged nodes, represent essential defensive measures against debris-induced system failures.
Unlock deeper insights with Patsnap Eureka Quick Research — get a full tech report to explore trends and direct your research. Try now!
Generate Your Research Report Instantly with AI Agent
Supercharge your innovation with Patsnap Eureka AI Agent Platform!