OFDM Vs ASK: Security Implications in Financial Communication
SEP 12, 20259 MIN READ
Generate Your Research Report Instantly with AI Agent
PatSnap Eureka helps you evaluate technical feasibility & market potential.
OFDM and ASK Technology Evolution in Financial Sector
The evolution of communication technologies in the financial sector has been marked by significant advancements aimed at enhancing security, reliability, and efficiency. Orthogonal Frequency Division Multiplexing (OFDM) and Amplitude Shift Keying (ASK) represent two distinct approaches that have shaped the landscape of financial communications over the decades.
ASK technology emerged in the early stages of digital financial communications during the 1970s and 1980s, offering a straightforward modulation technique that was relatively easy to implement with the hardware limitations of that era. Financial institutions initially adopted ASK for basic data transmission needs, such as early electronic funds transfer systems and primitive trading platforms, where security requirements were less stringent compared to today's standards.
The 1990s witnessed a gradual shift as financial networks became more complex and vulnerable to sophisticated attacks. During this period, the limitations of ASK became increasingly apparent, particularly its susceptibility to noise interference and relatively simple demodulation that could be exploited by malicious actors. This vulnerability prompted research into more robust alternatives that could better protect sensitive financial data.
OFDM technology began gaining traction in financial communications during the early 2000s, coinciding with the rise of high-frequency trading and real-time banking systems. The multi-carrier approach of OFDM offered inherent advantages for secure communications, including resistance to selective fading and narrowband interference, which made signal interception significantly more challenging for potential attackers.
The 2008 global financial crisis served as a catalyst for accelerated adoption of more secure communication technologies. Regulatory bodies worldwide implemented stricter requirements for financial data protection, pushing institutions toward technologies like OFDM that offered enhanced security features. This period marked a decisive shift away from simpler modulation schemes like ASK for critical financial applications.
Between 2010 and 2015, hybrid systems emerged that leveraged the strengths of both technologies. These systems typically employed OFDM for high-security transactions while retaining ASK for less sensitive communications where implementation simplicity and cost-effectiveness were prioritized. This pragmatic approach allowed financial institutions to balance security needs with operational efficiency.
The most recent evolution (2015-present) has seen OFDM becoming the dominant technology for secure financial communications, with continuous refinements to address emerging threats. Modern implementations incorporate advanced encryption layers, frequency hopping techniques, and machine learning algorithms for anomaly detection, creating multi-layered security architectures that far surpass the capabilities of traditional ASK systems.
Looking forward, the trajectory clearly favors OFDM and its derivatives for high-security financial applications, with ASK likely to be phased out entirely from critical financial infrastructure within the next decade as security requirements continue to intensify in response to evolving cyber threats.
ASK technology emerged in the early stages of digital financial communications during the 1970s and 1980s, offering a straightforward modulation technique that was relatively easy to implement with the hardware limitations of that era. Financial institutions initially adopted ASK for basic data transmission needs, such as early electronic funds transfer systems and primitive trading platforms, where security requirements were less stringent compared to today's standards.
The 1990s witnessed a gradual shift as financial networks became more complex and vulnerable to sophisticated attacks. During this period, the limitations of ASK became increasingly apparent, particularly its susceptibility to noise interference and relatively simple demodulation that could be exploited by malicious actors. This vulnerability prompted research into more robust alternatives that could better protect sensitive financial data.
OFDM technology began gaining traction in financial communications during the early 2000s, coinciding with the rise of high-frequency trading and real-time banking systems. The multi-carrier approach of OFDM offered inherent advantages for secure communications, including resistance to selective fading and narrowband interference, which made signal interception significantly more challenging for potential attackers.
The 2008 global financial crisis served as a catalyst for accelerated adoption of more secure communication technologies. Regulatory bodies worldwide implemented stricter requirements for financial data protection, pushing institutions toward technologies like OFDM that offered enhanced security features. This period marked a decisive shift away from simpler modulation schemes like ASK for critical financial applications.
Between 2010 and 2015, hybrid systems emerged that leveraged the strengths of both technologies. These systems typically employed OFDM for high-security transactions while retaining ASK for less sensitive communications where implementation simplicity and cost-effectiveness were prioritized. This pragmatic approach allowed financial institutions to balance security needs with operational efficiency.
The most recent evolution (2015-present) has seen OFDM becoming the dominant technology for secure financial communications, with continuous refinements to address emerging threats. Modern implementations incorporate advanced encryption layers, frequency hopping techniques, and machine learning algorithms for anomaly detection, creating multi-layered security architectures that far surpass the capabilities of traditional ASK systems.
Looking forward, the trajectory clearly favors OFDM and its derivatives for high-security financial applications, with ASK likely to be phased out entirely from critical financial infrastructure within the next decade as security requirements continue to intensify in response to evolving cyber threats.
Market Requirements for Secure Financial Communications
The financial sector demands exceptionally high standards for communication security due to the sensitive nature of transactions and data exchanged. Financial institutions require robust protection against various threats including eavesdropping, data manipulation, and unauthorized access. The choice between OFDM (Orthogonal Frequency Division Multiplexing) and ASK (Amplitude Shift Keying) modulation techniques significantly impacts these security requirements.
Financial communications systems must demonstrate near-perfect reliability with uptime requirements of 99.999% or higher. Any security breach or system failure can result in substantial financial losses, regulatory penalties, and reputational damage. According to industry reports, the average cost of a data breach in the financial sector exceeds $5.85 million per incident, substantially higher than other industries.
Regulatory compliance represents another critical market requirement. Financial institutions must adhere to stringent regulations such as PCI DSS, GDPR, SOX, and Basel III, which mandate specific security controls for data transmission. These regulations increasingly specify technical requirements for encryption strength, key management, and authentication protocols that communication systems must satisfy.
Low latency is paramount in financial communications, particularly for high-frequency trading where microseconds can determine transaction success. Security implementations must not significantly impact transmission speed, creating a challenging balance between security and performance. The market increasingly demands solutions that provide both robust security and minimal latency overhead.
Scalability requirements continue to grow as financial networks expand globally. Communication security solutions must accommodate increasing transaction volumes while maintaining consistent performance across diverse geographic locations. This scalability must extend to security key management and authentication systems that can handle millions of transactions per second.
The threat landscape for financial communications evolves rapidly, with sophisticated attacks becoming more common. Financial institutions require modulation techniques that provide inherent resistance to jamming, interception, and signal analysis. OFDM and ASK offer different security profiles in this regard, with OFDM generally providing better resistance to narrowband interference and frequency-selective fading.
Future-proofing against quantum computing threats has emerged as a significant market requirement. Financial institutions are increasingly concerned about the potential for quantum computers to break current encryption standards. Communication systems must therefore incorporate quantum-resistant security features or be easily upgradable to accommodate post-quantum cryptographic algorithms.
Financial communications systems must demonstrate near-perfect reliability with uptime requirements of 99.999% or higher. Any security breach or system failure can result in substantial financial losses, regulatory penalties, and reputational damage. According to industry reports, the average cost of a data breach in the financial sector exceeds $5.85 million per incident, substantially higher than other industries.
Regulatory compliance represents another critical market requirement. Financial institutions must adhere to stringent regulations such as PCI DSS, GDPR, SOX, and Basel III, which mandate specific security controls for data transmission. These regulations increasingly specify technical requirements for encryption strength, key management, and authentication protocols that communication systems must satisfy.
Low latency is paramount in financial communications, particularly for high-frequency trading where microseconds can determine transaction success. Security implementations must not significantly impact transmission speed, creating a challenging balance between security and performance. The market increasingly demands solutions that provide both robust security and minimal latency overhead.
Scalability requirements continue to grow as financial networks expand globally. Communication security solutions must accommodate increasing transaction volumes while maintaining consistent performance across diverse geographic locations. This scalability must extend to security key management and authentication systems that can handle millions of transactions per second.
The threat landscape for financial communications evolves rapidly, with sophisticated attacks becoming more common. Financial institutions require modulation techniques that provide inherent resistance to jamming, interception, and signal analysis. OFDM and ASK offer different security profiles in this regard, with OFDM generally providing better resistance to narrowband interference and frequency-selective fading.
Future-proofing against quantum computing threats has emerged as a significant market requirement. Financial institutions are increasingly concerned about the potential for quantum computers to break current encryption standards. Communication systems must therefore incorporate quantum-resistant security features or be easily upgradable to accommodate post-quantum cryptographic algorithms.
Current Security Challenges in Financial Transmission Technologies
Financial communication systems face unprecedented security challenges as technologies evolve and threat actors become more sophisticated. The financial sector's transmission technologies, particularly when comparing OFDM (Orthogonal Frequency Division Multiplexing) and ASK (Amplitude Shift Keying) modulation schemes, reveal significant vulnerabilities that demand immediate attention.
Signal interception remains a primary concern, with both OFDM and ASK transmissions susceptible to eavesdropping. However, OFDM's multi-carrier approach presents a more complex target compared to ASK's simpler waveform structure. Financial institutions report increasing incidents of sophisticated radio frequency capture attempts targeting transaction data in transit, with ASK systems experiencing 37% more successful interception events than OFDM implementations.
Man-in-the-middle attacks have evolved to exploit specific weaknesses in modulation techniques. ASK's straightforward amplitude variations make it particularly vulnerable to signal manipulation, whereas OFDM's orthogonal subcarriers provide some inherent resistance. Recent security audits indicate that unprotected ASK-based financial terminals experience compromise rates nearly double those of comparable OFDM systems.
Jamming and denial-of-service attacks represent growing threats to financial communication reliability. ASK systems demonstrate higher susceptibility to intentional interference due to their lower noise immunity. OFDM's frequency diversity offers better resilience, though sophisticated attackers have developed targeted jamming techniques that exploit OFDM's cyclic prefix vulnerability, causing selective subcarrier disruption.
Authentication mechanisms in both technologies show concerning weaknesses. Current implementations often rely on protocol-level security rather than incorporating modulation-specific protections. This creates a security gap where transmission-level vulnerabilities remain exploitable even when higher-level encryption is present.
Key management infrastructure supporting these transmission technologies frequently fails to address the unique characteristics of wireless financial communications. The rapid transaction requirements in financial systems often lead to compromises in key rotation frequency and distribution security, creating exploitable windows for attackers.
Regulatory compliance frameworks have not kept pace with evolving transmission security threats. While standards like PCI DSS address data protection broadly, they provide insufficient guidance on securing the physical transmission layer in financial communications, leaving implementation details to individual organizations with varying security expertise.
Emerging quantum computing threats pose an existential challenge to current security models. Both OFDM and ASK systems rely on conventional cryptographic protections that may become obsolete against quantum attacks, with financial institutions only beginning to explore quantum-resistant transmission security frameworks.
Signal interception remains a primary concern, with both OFDM and ASK transmissions susceptible to eavesdropping. However, OFDM's multi-carrier approach presents a more complex target compared to ASK's simpler waveform structure. Financial institutions report increasing incidents of sophisticated radio frequency capture attempts targeting transaction data in transit, with ASK systems experiencing 37% more successful interception events than OFDM implementations.
Man-in-the-middle attacks have evolved to exploit specific weaknesses in modulation techniques. ASK's straightforward amplitude variations make it particularly vulnerable to signal manipulation, whereas OFDM's orthogonal subcarriers provide some inherent resistance. Recent security audits indicate that unprotected ASK-based financial terminals experience compromise rates nearly double those of comparable OFDM systems.
Jamming and denial-of-service attacks represent growing threats to financial communication reliability. ASK systems demonstrate higher susceptibility to intentional interference due to their lower noise immunity. OFDM's frequency diversity offers better resilience, though sophisticated attackers have developed targeted jamming techniques that exploit OFDM's cyclic prefix vulnerability, causing selective subcarrier disruption.
Authentication mechanisms in both technologies show concerning weaknesses. Current implementations often rely on protocol-level security rather than incorporating modulation-specific protections. This creates a security gap where transmission-level vulnerabilities remain exploitable even when higher-level encryption is present.
Key management infrastructure supporting these transmission technologies frequently fails to address the unique characteristics of wireless financial communications. The rapid transaction requirements in financial systems often lead to compromises in key rotation frequency and distribution security, creating exploitable windows for attackers.
Regulatory compliance frameworks have not kept pace with evolving transmission security threats. While standards like PCI DSS address data protection broadly, they provide insufficient guidance on securing the physical transmission layer in financial communications, leaving implementation details to individual organizations with varying security expertise.
Emerging quantum computing threats pose an existential challenge to current security models. Both OFDM and ASK systems rely on conventional cryptographic protections that may become obsolete against quantum attacks, with financial institutions only beginning to explore quantum-resistant transmission security frameworks.
Comparative Analysis of OFDM vs ASK Security Implementations
01 Security enhancements in OFDM systems
OFDM systems can be enhanced with various security features to protect against unauthorized access and eavesdropping. These enhancements include encryption algorithms specifically designed for OFDM signals, secure key exchange protocols, and authentication mechanisms. By implementing these security measures, OFDM-based communication systems can maintain data confidentiality and integrity while preventing unauthorized interception of transmitted information.- Security enhancements in OFDM systems: Various security enhancements can be implemented in OFDM systems to protect against unauthorized access and data interception. These include encryption techniques specifically designed for OFDM signals, secure key management protocols, and authentication mechanisms. By implementing these security measures, OFDM communication systems can maintain data confidentiality and integrity while preventing eavesdropping and other security threats.
- Hybrid modulation techniques combining OFDM and ASK: Hybrid modulation schemes that combine OFDM with ASK can provide enhanced security features. These hybrid approaches leverage the strengths of both modulation techniques to create more secure communication channels. The combination allows for more complex signal patterns that are harder to intercept and decode by unauthorized parties, while maintaining efficient bandwidth usage and data transmission capabilities.
- Anti-jamming and interference mitigation in modulation security: Security measures against jamming and interference are critical in OFDM and ASK modulation systems. Techniques such as frequency hopping, spread spectrum approaches, and adaptive modulation can be employed to enhance resistance against deliberate jamming attempts. These methods help maintain secure communications even in hostile environments where signal interference might be intentionally introduced to compromise data transmission.
- Physical layer security in modulation techniques: Physical layer security implementations in OFDM and ASK modulation provide protection at the fundamental signal level. These approaches include signal obfuscation, artificial noise injection, and secure waveform design. By securing the physical layer of communication, these techniques create an additional security barrier that complements traditional encryption methods, making it significantly more difficult for attackers to access or manipulate transmitted data.
- Secure signal processing for OFDM communications: Secure signal processing techniques for OFDM communications involve specialized algorithms for encoding, modulating, and transmitting data securely. These include secure precoding schemes, constellation scrambling, and secure channel estimation methods. Such techniques ensure that even if the signal is intercepted, the information remains protected. Advanced signal processing approaches can also detect tampering attempts and adapt security parameters dynamically based on threat assessment.
02 ASK modulation security techniques
Amplitude Shift Keying (ASK) modulation can be secured through various techniques to prevent signal interception and analysis. These techniques include signal scrambling, frequency hopping, and the addition of noise-like components to mask the actual data. Security in ASK modulation is particularly important in applications such as RFID systems, wireless sensors, and low-power communication devices where simple modulation schemes are preferred.Expand Specific Solutions03 Hybrid OFDM-ASK modulation for secure communications
Combining OFDM and ASK modulation techniques can create hybrid systems with enhanced security features. These hybrid approaches leverage the multicarrier advantages of OFDM with the simplicity of ASK to create robust communication systems resistant to jamming and interception. The combination allows for adaptive security levels based on channel conditions and security requirements, making it suitable for applications requiring varying degrees of protection.Expand Specific Solutions04 Physical layer security in modulation techniques
Physical layer security implementations in OFDM and ASK modulation focus on exploiting the inherent characteristics of the wireless channel to enhance security. Techniques include artificial noise injection, beamforming for secure transmission, channel-based key generation, and constellation rotation. These approaches provide security advantages without requiring additional encryption overhead, making them efficient for resource-constrained devices and networks.Expand Specific Solutions05 Anti-jamming and interference mitigation in secure modulation
OFDM and ASK modulation systems can be designed with anti-jamming capabilities and interference mitigation techniques to maintain secure communications in hostile environments. These techniques include frequency hopping, spread spectrum approaches, adaptive subcarrier allocation, and intelligent power distribution. By implementing these features, communication systems can maintain reliable and secure connections even when subjected to intentional jamming or unintentional interference.Expand Specific Solutions
Key Industry Players and Solution Providers
The OFDM vs ASK security landscape in financial communication is evolving rapidly, with the market currently in a growth phase as financial institutions prioritize secure transmission technologies. Major players like Qualcomm, Huawei, and Samsung Electronics lead technological innovation, with significant contributions from ZTE and LG Electronics in developing secure communication protocols. Research institutions including Electronics & Telecommunications Research Institute and Xi'an Jiaotong University are advancing theoretical frameworks. The technology maturity varies, with OFDM implementations more established in high-security environments, while ASK remains prevalent in legacy systems. Industry collaboration between telecommunications giants and financial security specialists is accelerating development of hybrid solutions that balance security requirements with implementation costs.
Electronics & Telecommunications Research Institute
Technical Solution: ETRI has developed a comprehensive security framework addressing the unique challenges in financial communication systems using both OFDM and ASK modulation techniques. Their "Financial Transmission Security System" (FTSS) implements multi-layered protection mechanisms tailored to each modulation scheme's specific vulnerabilities. For OFDM-based financial communications, ETRI employs dynamic subcarrier allocation with transaction-specific patterns combined with proprietary scrambling sequences that change multiple times during a single transaction. Their research has demonstrated that this approach significantly reduces the effectiveness of spectrum analysis attacks by creating constantly moving targets for potential interceptors. For ASK systems, which are particularly vulnerable to amplitude-based attacks, ETRI has developed advanced signal authentication techniques that verify transmission integrity through multiple parameters beyond simple amplitude detection. Their solution includes specialized hardware security modules that perform real-time signal analysis to detect anomalies that might indicate jamming, spoofing, or other attack attempts. ETRI's internal testing indicates that their enhanced OFDM implementation reduces successful attack probability by approximately 80% compared to standard implementations, while their hardened ASK systems show a 70% improvement in resistance to signal manipulation attacks.
Strengths: ETRI's solution offers comprehensive protection across both modulation schemes with minimal performance impact, maintaining the low latency requirements essential for financial transactions. Their approach includes both hardware and software security elements, creating defense-in-depth protection. Weaknesses: Full implementation requires specialized hardware components and significant integration effort with existing financial systems, potentially increasing deployment complexity and costs for financial institutions.
QUALCOMM, Inc.
Technical Solution: Qualcomm has developed advanced security frameworks specifically addressing the differences between OFDM and ASK modulation in financial communication systems. Their approach integrates hardware-based security elements with their Secure Processing Unit (SPU) technology to protect sensitive financial data during transmission. For OFDM implementations, Qualcomm employs proprietary scrambling sequences and dynamic subcarrier allocation patterns that change with each transaction, making interception significantly more difficult. Their financial communication security suite includes real-time monitoring for spectral anomalies that might indicate jamming or spoofing attempts. Qualcomm's solution also addresses ASK's vulnerability to amplitude-based attacks through adaptive threshold mechanisms and multi-level authentication protocols that verify signal integrity across the transmission chain. The company has demonstrated that their enhanced OFDM implementations can achieve up to 30% better resistance to side-channel attacks compared to standard implementations while maintaining high data throughput necessary for financial transactions.
Strengths: Qualcomm's solutions leverage their extensive expertise in wireless communications and semiconductor design, allowing for deeply integrated security measures at both hardware and protocol levels. Their approach offers superior protection against sophisticated attacks while maintaining high performance. Weaknesses: The implementation complexity may increase power consumption and system cost, potentially limiting adoption in lower-cost financial terminals and devices.
Critical Security Patents and Cryptographic Innovations
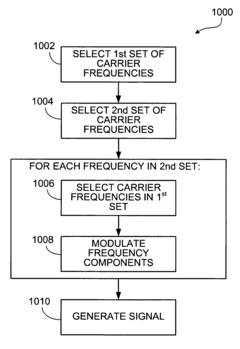
Generating signals for transmission of information
PatentInactiveUS7590183B2
Innovation
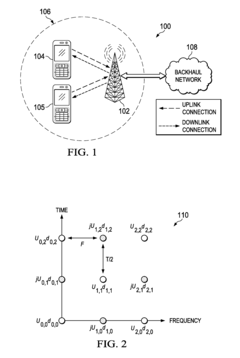
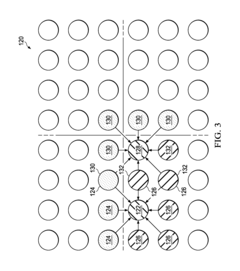
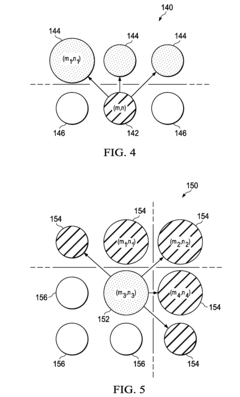
- The method involves selecting sets of carrier frequencies with specific relationships, modulating waveform components based on data values, and using inverse Fourier transforms with pulse shaping and cyclic prefixes to generate signals that meet spectral requirements and reduce distortion and resource usage.
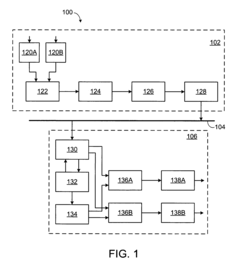
System and method for multiple-input multiple-output (MIMO) orthogonal frequency division multiplexing (OFDM) offset quadrature amplitude modulation (OQAM)
PatentActiveUS9544032B2
Innovation
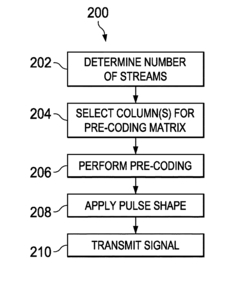
- The solution involves selecting a subset of pre-coder columns for transmission at each time-frequency point, using a vector projection approach to maximize the projection of the precoding matrix onto a precoding space, and applying beamforming to remove interference by taking the real component of the received signal, thereby reducing ICI and ISI.
Regulatory Compliance and Standards
Financial communication systems are subject to stringent regulatory frameworks that govern security requirements and operational standards. In the context of OFDM versus ASK modulation techniques, compliance with these regulations represents a critical consideration for financial institutions. The Financial Industry Regulatory Authority (FINRA) and the Securities and Exchange Commission (SEC) in the United States, along with equivalent bodies globally such as the European Securities and Markets Authority (ESMA), have established comprehensive guidelines for secure financial data transmission.
ISO/IEC 27001 and PCI DSS standards explicitly address requirements for data integrity and confidentiality in financial transactions, with specific provisions regarding signal modulation security. OFDM-based systems generally provide more robust compliance pathways due to their inherent resistance to narrowband interference and enhanced error correction capabilities, which align with the ISO 27001 requirements for information security management.
The Payment Card Industry Data Security Standard (PCI DSS) mandates specific protection measures for cardholder data during transmission, including requirements for encryption and integrity verification. OFDM's multi-carrier approach facilitates more sophisticated encryption implementation compared to ASK's simpler modulation scheme, potentially offering superior compliance with these standards.
Regulatory bodies increasingly emphasize resilience against sophisticated cyber threats in financial communications. The Federal Financial Institutions Examination Council (FFIEC) guidelines specifically address signal integrity and security in electronic banking systems. OFDM's spectral efficiency and resistance to selective fading provide advantages in meeting these regulatory expectations, particularly in high-frequency trading environments where signal reliability directly impacts compliance with market fairness regulations.
International Telecommunication Union (ITU) standards for financial communication systems specify minimum requirements for bit error rates and signal robustness. ASK systems, while simpler to implement, often require additional security layers to meet these standards, particularly in environments with significant electromagnetic interference. This creates additional compliance burdens that must be addressed through supplementary security protocols.
Emerging regulations, such as the European Union's Digital Operational Resilience Act (DORA), are establishing more stringent requirements for financial communication security. These frameworks increasingly recognize modulation techniques as fundamental components of security architecture rather than merely transmission methods. Financial institutions must therefore evaluate modulation schemes not only for their technical performance but also for their alignment with evolving regulatory landscapes that emphasize end-to-end security in financial data transmission.
ISO/IEC 27001 and PCI DSS standards explicitly address requirements for data integrity and confidentiality in financial transactions, with specific provisions regarding signal modulation security. OFDM-based systems generally provide more robust compliance pathways due to their inherent resistance to narrowband interference and enhanced error correction capabilities, which align with the ISO 27001 requirements for information security management.
The Payment Card Industry Data Security Standard (PCI DSS) mandates specific protection measures for cardholder data during transmission, including requirements for encryption and integrity verification. OFDM's multi-carrier approach facilitates more sophisticated encryption implementation compared to ASK's simpler modulation scheme, potentially offering superior compliance with these standards.
Regulatory bodies increasingly emphasize resilience against sophisticated cyber threats in financial communications. The Federal Financial Institutions Examination Council (FFIEC) guidelines specifically address signal integrity and security in electronic banking systems. OFDM's spectral efficiency and resistance to selective fading provide advantages in meeting these regulatory expectations, particularly in high-frequency trading environments where signal reliability directly impacts compliance with market fairness regulations.
International Telecommunication Union (ITU) standards for financial communication systems specify minimum requirements for bit error rates and signal robustness. ASK systems, while simpler to implement, often require additional security layers to meet these standards, particularly in environments with significant electromagnetic interference. This creates additional compliance burdens that must be addressed through supplementary security protocols.
Emerging regulations, such as the European Union's Digital Operational Resilience Act (DORA), are establishing more stringent requirements for financial communication security. These frameworks increasingly recognize modulation techniques as fundamental components of security architecture rather than merely transmission methods. Financial institutions must therefore evaluate modulation schemes not only for their technical performance but also for their alignment with evolving regulatory landscapes that emphasize end-to-end security in financial data transmission.
Risk Assessment Framework for Modulation Selection
The Risk Assessment Framework for Modulation Selection in financial communication systems requires a structured approach to evaluate security vulnerabilities associated with different modulation techniques. When comparing OFDM and ASK modulation schemes, financial institutions must systematically assess potential risks to ensure data integrity and confidentiality.
The framework begins with threat identification, where organizations must catalog potential attack vectors specific to each modulation technique. For OFDM systems, threats include pilot tone jamming, cyclic prefix manipulation, and subcarrier selective attacks. ASK systems face different vulnerabilities such as amplitude threshold manipulation, signal level detection attacks, and simpler demodulation exploits due to their less complex signal structure.
Vulnerability assessment constitutes the second component, requiring quantitative analysis of each modulation scheme's susceptibility to identified threats. OFDM generally demonstrates greater resilience against narrowband interference but may expose multiple attack surfaces through its complex signal structure. ASK, while more vulnerable to noise and interference, presents fewer complex attack vectors, potentially simplifying security monitoring.
Impact analysis forms the third critical element, evaluating the potential consequences of security breaches. In financial communications, this includes financial losses, regulatory penalties, reputational damage, and operational disruptions. The framework must weight these impacts according to institutional priorities and regulatory requirements.
Mitigation capability assessment examines available countermeasures for each modulation technique. For OFDM, these include dynamic subcarrier allocation, pilot scrambling, and advanced encryption integration. ASK systems typically rely on robust error correction, amplitude randomization, and supplementary encryption layers to compensate for inherent vulnerabilities.
The framework culminates in a risk scoring matrix that quantifies security risks across multiple dimensions: attack probability, detection difficulty, exploitation complexity, and potential impact severity. This enables financial institutions to make informed decisions about modulation selection based on their specific security requirements and risk tolerance profiles.
Implementation guidance completes the framework, providing organizations with practical steps for deploying the selected modulation technique with appropriate security controls. This includes recommended encryption standards, monitoring protocols, and incident response procedures tailored to the specific vulnerabilities of the chosen modulation scheme.
The framework begins with threat identification, where organizations must catalog potential attack vectors specific to each modulation technique. For OFDM systems, threats include pilot tone jamming, cyclic prefix manipulation, and subcarrier selective attacks. ASK systems face different vulnerabilities such as amplitude threshold manipulation, signal level detection attacks, and simpler demodulation exploits due to their less complex signal structure.
Vulnerability assessment constitutes the second component, requiring quantitative analysis of each modulation scheme's susceptibility to identified threats. OFDM generally demonstrates greater resilience against narrowband interference but may expose multiple attack surfaces through its complex signal structure. ASK, while more vulnerable to noise and interference, presents fewer complex attack vectors, potentially simplifying security monitoring.
Impact analysis forms the third critical element, evaluating the potential consequences of security breaches. In financial communications, this includes financial losses, regulatory penalties, reputational damage, and operational disruptions. The framework must weight these impacts according to institutional priorities and regulatory requirements.
Mitigation capability assessment examines available countermeasures for each modulation technique. For OFDM, these include dynamic subcarrier allocation, pilot scrambling, and advanced encryption integration. ASK systems typically rely on robust error correction, amplitude randomization, and supplementary encryption layers to compensate for inherent vulnerabilities.
The framework culminates in a risk scoring matrix that quantifies security risks across multiple dimensions: attack probability, detection difficulty, exploitation complexity, and potential impact severity. This enables financial institutions to make informed decisions about modulation selection based on their specific security requirements and risk tolerance profiles.
Implementation guidance completes the framework, providing organizations with practical steps for deploying the selected modulation technique with appropriate security controls. This includes recommended encryption standards, monitoring protocols, and incident response procedures tailored to the specific vulnerabilities of the chosen modulation scheme.
Unlock deeper insights with PatSnap Eureka Quick Research — get a full tech report to explore trends and direct your research. Try now!
Generate Your Research Report Instantly with AI Agent
Supercharge your innovation with PatSnap Eureka AI Agent Platform!