Improving Brain-Computer Interface Data Encryption for Security
MAR 5, 202610 MIN READ
Generate Your Research Report Instantly with AI Agent
Patsnap Eureka helps you evaluate technical feasibility & market potential.
BCI Data Encryption Background and Security Goals
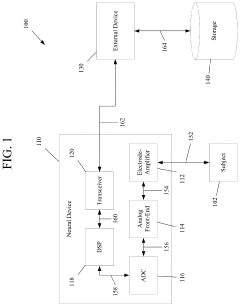
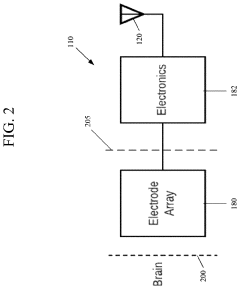
Brain-Computer Interfaces represent a revolutionary convergence of neuroscience, computer science, and biomedical engineering that enables direct communication pathways between the brain and external devices. These systems capture neural signals through various acquisition methods including invasive electrodes, semi-invasive electrocorticography arrays, and non-invasive electroencephalography sensors. The fundamental principle involves translating neural activity patterns into digital commands that can control prosthetic devices, computer cursors, or communication systems.
The evolution of BCI technology has progressed from early experimental demonstrations in the 1970s to sophisticated clinical applications today. Initial research focused primarily on signal acquisition and basic pattern recognition, with limited consideration for data security. However, as BCI systems have advanced toward commercial deployment and widespread clinical adoption, the security implications have become increasingly critical.
Modern BCI systems generate vast amounts of highly sensitive neurological data that contains intimate information about user intentions, cognitive states, and potentially even memories or emotions. This neural data represents perhaps the most personal form of biometric information, as it directly reflects brain activity patterns unique to each individual. The sensitivity of this data far exceeds traditional biometric markers like fingerprints or facial recognition patterns.
Current security challenges in BCI systems stem from multiple vulnerabilities across the data pipeline. Neural signals are typically transmitted wirelessly from implanted or wearable devices to external processing units, creating potential interception points. The computational processing of these signals often occurs on standard computing platforms that may lack specialized security hardening. Additionally, the real-time nature of BCI applications creates tension between security measures and system responsiveness requirements.
The primary security goals for BCI data encryption encompass several critical objectives. Data confidentiality must ensure that neural information remains protected from unauthorized access during transmission, processing, and storage phases. Signal integrity verification is essential to prevent malicious manipulation of neural commands that could result in unintended device actions. User authentication mechanisms must reliably verify the identity of the BCI operator while preventing spoofing attacks.
Privacy preservation represents another fundamental goal, requiring protection against inference attacks that might extract sensitive cognitive information from encrypted neural data patterns. The system must also maintain availability and real-time performance characteristics essential for safe BCI operation, particularly in medical applications where delays could have serious consequences.
Regulatory compliance adds additional complexity, as BCI systems must meet stringent medical device security standards while adhering to data protection regulations. The encryption framework must therefore balance robust security measures with the unique operational requirements and constraints inherent in brain-computer interface applications.
The evolution of BCI technology has progressed from early experimental demonstrations in the 1970s to sophisticated clinical applications today. Initial research focused primarily on signal acquisition and basic pattern recognition, with limited consideration for data security. However, as BCI systems have advanced toward commercial deployment and widespread clinical adoption, the security implications have become increasingly critical.
Modern BCI systems generate vast amounts of highly sensitive neurological data that contains intimate information about user intentions, cognitive states, and potentially even memories or emotions. This neural data represents perhaps the most personal form of biometric information, as it directly reflects brain activity patterns unique to each individual. The sensitivity of this data far exceeds traditional biometric markers like fingerprints or facial recognition patterns.
Current security challenges in BCI systems stem from multiple vulnerabilities across the data pipeline. Neural signals are typically transmitted wirelessly from implanted or wearable devices to external processing units, creating potential interception points. The computational processing of these signals often occurs on standard computing platforms that may lack specialized security hardening. Additionally, the real-time nature of BCI applications creates tension between security measures and system responsiveness requirements.
The primary security goals for BCI data encryption encompass several critical objectives. Data confidentiality must ensure that neural information remains protected from unauthorized access during transmission, processing, and storage phases. Signal integrity verification is essential to prevent malicious manipulation of neural commands that could result in unintended device actions. User authentication mechanisms must reliably verify the identity of the BCI operator while preventing spoofing attacks.
Privacy preservation represents another fundamental goal, requiring protection against inference attacks that might extract sensitive cognitive information from encrypted neural data patterns. The system must also maintain availability and real-time performance characteristics essential for safe BCI operation, particularly in medical applications where delays could have serious consequences.
Regulatory compliance adds additional complexity, as BCI systems must meet stringent medical device security standards while adhering to data protection regulations. The encryption framework must therefore balance robust security measures with the unique operational requirements and constraints inherent in brain-computer interface applications.
Market Demand for Secure Brain-Computer Interfaces
The global brain-computer interface market is experiencing unprecedented growth driven by increasing awareness of neurological disorders and the expanding applications of BCI technology across healthcare, gaming, and assistive technologies. However, the integration of robust security measures has emerged as a critical market differentiator, with healthcare institutions and research organizations prioritizing data protection capabilities when selecting BCI solutions.
Healthcare sectors represent the largest demand segment for secure BCI systems, particularly in neural rehabilitation, epilepsy monitoring, and cognitive assessment applications. Medical institutions require compliance with stringent data protection regulations including HIPAA, GDPR, and emerging neurorights legislation. The sensitivity of neural data, which can potentially reveal cognitive states, emotional responses, and neurological conditions, has elevated security requirements beyond traditional medical device standards.
Military and defense applications constitute another significant demand driver, where secure neural interfaces are sought for pilot training, cognitive load assessment, and enhanced human-machine interaction systems. These applications demand encryption standards that meet classified information handling requirements, creating a specialized market segment with premium pricing tolerance for advanced security features.
The consumer electronics sector shows growing interest in secure BCI solutions, particularly for gaming, virtual reality, and wellness applications. Consumer privacy concerns regarding neural data collection have intensified following high-profile data breaches in other technology sectors, leading to increased demand for transparent encryption protocols and user-controlled data management features.
Research institutions and academic organizations represent a substantial market segment requiring secure BCI systems for neuroscience studies and clinical trials. These entities need solutions that balance data security with research collaboration requirements, driving demand for selective encryption schemes and secure multi-party computation capabilities.
Emerging markets in Asia-Pacific and Europe demonstrate accelerating adoption rates, with regulatory frameworks increasingly mandating encryption standards for neural interface devices. The convergence of aging populations, rising healthcare costs, and technological advancement creates sustained demand growth for secure BCI solutions across these regions.
Market barriers include the complexity of implementing encryption without compromising real-time performance requirements and the lack of standardized security protocols specific to neural data. These challenges create opportunities for innovative encryption solutions that address BCI-specific security needs while maintaining system responsiveness and clinical efficacy.
Healthcare sectors represent the largest demand segment for secure BCI systems, particularly in neural rehabilitation, epilepsy monitoring, and cognitive assessment applications. Medical institutions require compliance with stringent data protection regulations including HIPAA, GDPR, and emerging neurorights legislation. The sensitivity of neural data, which can potentially reveal cognitive states, emotional responses, and neurological conditions, has elevated security requirements beyond traditional medical device standards.
Military and defense applications constitute another significant demand driver, where secure neural interfaces are sought for pilot training, cognitive load assessment, and enhanced human-machine interaction systems. These applications demand encryption standards that meet classified information handling requirements, creating a specialized market segment with premium pricing tolerance for advanced security features.
The consumer electronics sector shows growing interest in secure BCI solutions, particularly for gaming, virtual reality, and wellness applications. Consumer privacy concerns regarding neural data collection have intensified following high-profile data breaches in other technology sectors, leading to increased demand for transparent encryption protocols and user-controlled data management features.
Research institutions and academic organizations represent a substantial market segment requiring secure BCI systems for neuroscience studies and clinical trials. These entities need solutions that balance data security with research collaboration requirements, driving demand for selective encryption schemes and secure multi-party computation capabilities.
Emerging markets in Asia-Pacific and Europe demonstrate accelerating adoption rates, with regulatory frameworks increasingly mandating encryption standards for neural interface devices. The convergence of aging populations, rising healthcare costs, and technological advancement creates sustained demand growth for secure BCI solutions across these regions.
Market barriers include the complexity of implementing encryption without compromising real-time performance requirements and the lack of standardized security protocols specific to neural data. These challenges create opportunities for innovative encryption solutions that address BCI-specific security needs while maintaining system responsiveness and clinical efficacy.
Current BCI Security Vulnerabilities and Encryption Gaps
Brain-computer interfaces face significant security vulnerabilities that stem from their unique position as direct neural data acquisition and transmission systems. The primary security gaps exist at multiple layers of the BCI architecture, creating numerous attack vectors that traditional cybersecurity measures inadequately address.
Signal acquisition vulnerabilities represent the most fundamental security concern in BCI systems. Neural signals captured by electrodes or implanted sensors are transmitted in raw or minimally processed formats, often lacking encryption during the initial capture phase. This creates opportunities for eavesdropping attacks where malicious actors can intercept neural data before any security measures are applied. The analog-to-digital conversion process further compounds these vulnerabilities, as the digitization stage frequently occurs without cryptographic protection.
Data transmission pathways in current BCI implementations exhibit critical encryption gaps. Many existing systems rely on standard wireless protocols such as Bluetooth or WiFi for neural data transmission, which employ encryption methods not specifically designed for the unique characteristics of neural signals. These generic encryption approaches fail to account for the high-frequency, continuous nature of brain data streams, resulting in potential timing attacks and pattern analysis vulnerabilities that could expose sensitive neural information.
Storage and processing vulnerabilities emerge from inadequate encryption of neural databases and real-time processing systems. Current BCI platforms often store raw neural data in unencrypted formats or use weak encryption standards that are insufficient for protecting highly sensitive biometric information. The computational requirements for real-time neural signal processing have led many developers to prioritize performance over security, creating systems where encryption is either bypassed or implemented with compromised algorithms.
Authentication and access control represent another critical vulnerability area in BCI security architecture. Unlike traditional computing systems, BCIs must continuously verify the authenticity of neural signals while distinguishing between legitimate user commands and potential spoofing attempts. Current systems lack robust mechanisms to detect neural signal injection attacks or differentiate between authentic brain activity and artificially generated neural patterns.
The integration of machine learning algorithms in BCI systems introduces additional security gaps through model-based vulnerabilities. Neural decoding algorithms can be compromised through adversarial attacks that manipulate the interpretation of brain signals, potentially causing the system to execute unintended commands. These AI-specific vulnerabilities require specialized encryption approaches that protect both the neural data and the machine learning models processing this information.
Existing encryption standards prove inadequate for BCI applications due to the unique temporal and spatial characteristics of neural data. Traditional encryption methods introduce latency that can disrupt real-time BCI functionality, while the high-dimensional nature of neural signals requires encryption approaches that preserve essential signal characteristics while maintaining security. Current implementations often sacrifice security for performance, creating systems vulnerable to sophisticated attacks targeting neural data patterns and user behavioral biometrics.
Signal acquisition vulnerabilities represent the most fundamental security concern in BCI systems. Neural signals captured by electrodes or implanted sensors are transmitted in raw or minimally processed formats, often lacking encryption during the initial capture phase. This creates opportunities for eavesdropping attacks where malicious actors can intercept neural data before any security measures are applied. The analog-to-digital conversion process further compounds these vulnerabilities, as the digitization stage frequently occurs without cryptographic protection.
Data transmission pathways in current BCI implementations exhibit critical encryption gaps. Many existing systems rely on standard wireless protocols such as Bluetooth or WiFi for neural data transmission, which employ encryption methods not specifically designed for the unique characteristics of neural signals. These generic encryption approaches fail to account for the high-frequency, continuous nature of brain data streams, resulting in potential timing attacks and pattern analysis vulnerabilities that could expose sensitive neural information.
Storage and processing vulnerabilities emerge from inadequate encryption of neural databases and real-time processing systems. Current BCI platforms often store raw neural data in unencrypted formats or use weak encryption standards that are insufficient for protecting highly sensitive biometric information. The computational requirements for real-time neural signal processing have led many developers to prioritize performance over security, creating systems where encryption is either bypassed or implemented with compromised algorithms.
Authentication and access control represent another critical vulnerability area in BCI security architecture. Unlike traditional computing systems, BCIs must continuously verify the authenticity of neural signals while distinguishing between legitimate user commands and potential spoofing attempts. Current systems lack robust mechanisms to detect neural signal injection attacks or differentiate between authentic brain activity and artificially generated neural patterns.
The integration of machine learning algorithms in BCI systems introduces additional security gaps through model-based vulnerabilities. Neural decoding algorithms can be compromised through adversarial attacks that manipulate the interpretation of brain signals, potentially causing the system to execute unintended commands. These AI-specific vulnerabilities require specialized encryption approaches that protect both the neural data and the machine learning models processing this information.
Existing encryption standards prove inadequate for BCI applications due to the unique temporal and spatial characteristics of neural data. Traditional encryption methods introduce latency that can disrupt real-time BCI functionality, while the high-dimensional nature of neural signals requires encryption approaches that preserve essential signal characteristics while maintaining security. Current implementations often sacrifice security for performance, creating systems vulnerable to sophisticated attacks targeting neural data patterns and user behavioral biometrics.
Existing BCI Data Encryption Solutions
01 Encryption algorithms for brain signal data protection
Various encryption algorithms can be applied to secure brain-computer interface data during transmission and storage. These methods include symmetric and asymmetric encryption techniques that protect neural signal data from unauthorized access. Advanced cryptographic protocols ensure the confidentiality and integrity of brain activity information collected by BCI devices.- Encryption algorithms for brain-computer interface data protection: Various encryption algorithms can be applied to secure brain-computer interface data transmission and storage. These methods include symmetric and asymmetric encryption techniques that protect neural signal data from unauthorized access. Advanced cryptographic protocols ensure data integrity and confidentiality during the entire data lifecycle from acquisition to processing.
- Authentication and access control mechanisms for BCI systems: Authentication systems can be implemented to verify user identity and control access to brain-computer interface devices and data. These mechanisms include biometric verification, multi-factor authentication, and secure key management protocols. Access control frameworks ensure that only authorized personnel can interact with sensitive neural data and system configurations.
- Secure data transmission protocols for neural signals: Specialized communication protocols can be designed to securely transmit brain signal data between interface devices and processing systems. These protocols incorporate encryption layers, secure channels, and data integrity verification methods. The transmission security ensures protection against interception, tampering, and unauthorized monitoring of neural information during transfer.
- Privacy-preserving data processing and storage techniques: Privacy protection methods can be integrated into brain-computer interface systems to safeguard user neural data during processing and storage. These techniques include data anonymization, secure enclaves, and distributed storage solutions. Privacy-preserving algorithms allow for data analysis while maintaining confidentiality and preventing unauthorized data reconstruction or identification.
- Blockchain and distributed security frameworks for BCI data: Distributed ledger technologies and blockchain-based security frameworks can be employed to enhance the security and traceability of brain-computer interface data. These systems provide immutable audit trails, decentralized access control, and tamper-proof data records. The distributed architecture ensures resilience against single points of failure and enhances overall system security through consensus mechanisms.
02 Authentication mechanisms for BCI system access control
Authentication systems can be implemented to verify user identity before granting access to brain-computer interface systems. These mechanisms may include biometric verification, multi-factor authentication, and secure credential management. Such approaches prevent unauthorized users from accessing sensitive neural data or controlling BCI devices.Expand Specific Solutions03 Secure communication protocols for neural data transmission
Specialized communication protocols can be designed to ensure secure transmission of brain signal data between BCI devices and processing systems. These protocols incorporate encryption layers, secure handshaking procedures, and data integrity verification methods. The implementation of such protocols protects against interception and tampering during data transfer.Expand Specific Solutions04 Privacy-preserving data processing techniques
Privacy-preserving methods can be employed to process brain-computer interface data while maintaining user confidentiality. These techniques include homomorphic encryption, differential privacy, and secure multi-party computation that allow data analysis without exposing raw neural information. Such approaches enable legitimate data utilization while protecting sensitive brain activity patterns.Expand Specific Solutions05 Key management systems for BCI security infrastructure
Comprehensive key management frameworks can be established to handle cryptographic keys used in brain-computer interface security systems. These systems manage key generation, distribution, storage, rotation, and revocation processes. Proper key management ensures long-term security of encrypted neural data and maintains the integrity of the entire BCI security infrastructure.Expand Specific Solutions
Key Players in BCI Security and Encryption Industry
The brain-computer interface data encryption sector represents an emerging market at the intersection of neurotechnology and cybersecurity, currently in early development stages with significant growth potential driven by increasing BCI adoption across medical and consumer applications. The competitive landscape features diverse players ranging from established semiconductor giants like Intel Corp., AMD, and ARM Limited providing foundational computing infrastructure, to specialized BCI companies such as Precision Neuroscience Corp. and HI LLC developing dedicated neural interface technologies. Technology maturity varies considerably, with traditional tech companies like Microsoft Technology Licensing LLC and IBM leveraging existing encryption expertise, while healthcare-focused entities including Koninklijke Philips NV and Genentech Inc. contribute medical device security knowledge. The fragmented ecosystem also includes telecommunications providers like Huawei Technologies and research institutions such as Southeast University, indicating broad industry recognition of BCI security importance despite nascent commercial deployment.
ARM LIMITED
Technical Solution: ARM's BCI encryption solution focuses on their TrustZone technology and CryptoCell security IP, providing hardware-based security foundations for BCI devices. Their approach implements ARM's Platform Security Architecture (PSA) specifically tailored for medical IoT devices, ensuring secure boot, secure storage, and cryptographic services for BCI systems. The company's solution features low-power cryptographic accelerators optimized for battery-powered implantable BCI devices, supporting AES, RSA, and elliptic curve cryptography with minimal energy consumption. ARM's security framework includes secure firmware update mechanisms and tamper-resistant key storage, critical for long-term implanted BCI devices where physical security is paramount.
Strengths: Low-power consumption ideal for implantable devices, comprehensive hardware security architecture, wide ecosystem adoption. Weaknesses: Limited to ARM-based platforms, requires specialized development expertise, dependency on partner implementations.
Microsoft Technology Licensing LLC
Technical Solution: Microsoft's BCI encryption approach centers on their Azure Confidential Computing platform, providing hardware-based trusted execution environments for neural data processing. Their solution integrates Microsoft's SEAL (Simple Encrypted Arithmetic Library) homomorphic encryption library, enabling secure computation on encrypted BCI data in cloud environments. The platform utilizes Intel SGX and AMD SEV technologies to create secure enclaves where BCI algorithms can process encrypted neural signals. Microsoft's approach includes federated learning capabilities that allow multiple BCI systems to collaboratively train models while keeping individual neural data encrypted and localized, addressing both security and privacy concerns in clinical BCI deployments.
Strengths: Cloud-native security architecture, proven enterprise-grade encryption, extensive developer ecosystem. Weaknesses: Cloud dependency for full functionality, subscription-based cost model, potential vendor lock-in concerns.
Core Innovations in Neural Data Cryptography
Secure interfaces for neural devices
PatentPendingUS20240137348A1
Innovation
- Implementing a neural device system with end-to-end encryption protocols across communications interfaces, using advanced encryption standards such as AES, RSA, and ciphers, to secure data transfer between neural devices and external devices, including wired and wireless connections, ensuring the integrity of brain data handling and processing.
Sensation transmission system, sensation transmission method, and sensation transmission program
PatentWO2024062972A1
Innovation
- A sensory transmission system that employs a transmitting device to encrypt brain activity information using key information and a delivery device to distribute quantum entangled key information for secure decryption, ensuring the privacy of personal data during transmission.
Privacy Regulations for Neural Data Protection
The regulatory landscape for neural data protection is rapidly evolving as brain-computer interfaces transition from experimental technologies to commercial applications. Current privacy frameworks, including the European Union's General Data Protection Regulation (GDPR) and California's Consumer Privacy Act (CCPA), provide foundational principles but lack specific provisions addressing the unique characteristics of neural data. These regulations classify neural information as sensitive personal data, requiring explicit consent and enhanced security measures, yet they fall short of addressing the continuous, high-resolution nature of brain signal collection.
Emerging legislative initiatives specifically target neurotechnology privacy concerns. The Chilean government pioneered neurological rights legislation in 2021, establishing constitutional protections for mental privacy and cognitive liberty. Similar proposals have emerged in Spain, France, and several U.S. states, creating a patchwork of regulatory approaches that companies must navigate. These frameworks typically emphasize data minimization principles, requiring that neural data collection be limited to specific, legitimate purposes with clear temporal boundaries.
International standardization efforts are gaining momentum through organizations like the International Organization for Standardization (ISO) and the Institute of Electrical and Electronics Engineers (IEEE). The IEEE 2857 standard for privacy engineering in neural interface systems provides technical guidelines for implementing privacy-by-design principles in BCI architectures. These standards emphasize the importance of encryption not merely as a security measure but as a fundamental privacy protection mechanism.
Regulatory compliance presents significant technical challenges for BCI encryption systems. Traditional anonymization techniques prove inadequate for neural data due to the inherent uniqueness of individual brain patterns, necessitating advanced cryptographic approaches that preserve data utility while ensuring privacy. Regulations increasingly require real-time consent mechanisms, audit trails, and the ability to selectively delete specific neural data segments without compromising system integrity.
The regulatory trajectory indicates stricter requirements for cross-border neural data transfers, mandatory impact assessments for neurotechnology deployments, and enhanced user control mechanisms. Companies developing BCI encryption solutions must anticipate these evolving requirements, designing systems that can adapt to varying jurisdictional demands while maintaining robust security standards. This regulatory evolution directly influences encryption architecture decisions, pushing toward more sophisticated, privacy-preserving cryptographic implementations.
Emerging legislative initiatives specifically target neurotechnology privacy concerns. The Chilean government pioneered neurological rights legislation in 2021, establishing constitutional protections for mental privacy and cognitive liberty. Similar proposals have emerged in Spain, France, and several U.S. states, creating a patchwork of regulatory approaches that companies must navigate. These frameworks typically emphasize data minimization principles, requiring that neural data collection be limited to specific, legitimate purposes with clear temporal boundaries.
International standardization efforts are gaining momentum through organizations like the International Organization for Standardization (ISO) and the Institute of Electrical and Electronics Engineers (IEEE). The IEEE 2857 standard for privacy engineering in neural interface systems provides technical guidelines for implementing privacy-by-design principles in BCI architectures. These standards emphasize the importance of encryption not merely as a security measure but as a fundamental privacy protection mechanism.
Regulatory compliance presents significant technical challenges for BCI encryption systems. Traditional anonymization techniques prove inadequate for neural data due to the inherent uniqueness of individual brain patterns, necessitating advanced cryptographic approaches that preserve data utility while ensuring privacy. Regulations increasingly require real-time consent mechanisms, audit trails, and the ability to selectively delete specific neural data segments without compromising system integrity.
The regulatory trajectory indicates stricter requirements for cross-border neural data transfers, mandatory impact assessments for neurotechnology deployments, and enhanced user control mechanisms. Companies developing BCI encryption solutions must anticipate these evolving requirements, designing systems that can adapt to varying jurisdictional demands while maintaining robust security standards. This regulatory evolution directly influences encryption architecture decisions, pushing toward more sophisticated, privacy-preserving cryptographic implementations.
Ethical Framework for Brain Data Security
The ethical framework for brain data security in brain-computer interfaces represents a critical foundation for addressing the unprecedented privacy and security challenges posed by neural data collection and processing. This framework must establish comprehensive principles that balance technological advancement with fundamental human rights, particularly focusing on mental privacy, cognitive liberty, and neural autonomy.
Central to this ethical framework is the principle of informed consent, which requires significant adaptation for brain data contexts. Traditional consent models prove inadequate when dealing with neural information that may reveal unconscious thoughts, emotional states, or cognitive patterns that users themselves may not be aware of sharing. The framework must establish protocols for dynamic consent mechanisms that allow users to understand and control what aspects of their neural data are being accessed, processed, and stored.
Mental privacy emerges as a fundamental right requiring explicit protection within the ethical framework. Unlike other forms of personal data, brain signals represent the most intimate form of human information, potentially revealing thoughts, intentions, and mental states. The framework must define clear boundaries around what constitutes acceptable neural data collection and establish strict limitations on inference-making from brain signals that could violate cognitive privacy.
The framework must address the concept of neural non-discrimination, ensuring that brain data cannot be used to create unfair advantages or disadvantages in employment, insurance, education, or social contexts. This includes establishing protections against neural profiling and preventing the use of brain data for purposes beyond the explicitly consented applications.
Data ownership and control represent another crucial component, requiring clear definitions of who owns neural data and how individuals can exercise control over their brain information throughout its lifecycle. The framework must establish rights for data portability, deletion, and correction specific to neural data contexts.
Finally, the ethical framework must incorporate principles of transparency and accountability, requiring organizations to clearly communicate their neural data practices and establish mechanisms for oversight and enforcement of ethical standards in brain-computer interface implementations.
Central to this ethical framework is the principle of informed consent, which requires significant adaptation for brain data contexts. Traditional consent models prove inadequate when dealing with neural information that may reveal unconscious thoughts, emotional states, or cognitive patterns that users themselves may not be aware of sharing. The framework must establish protocols for dynamic consent mechanisms that allow users to understand and control what aspects of their neural data are being accessed, processed, and stored.
Mental privacy emerges as a fundamental right requiring explicit protection within the ethical framework. Unlike other forms of personal data, brain signals represent the most intimate form of human information, potentially revealing thoughts, intentions, and mental states. The framework must define clear boundaries around what constitutes acceptable neural data collection and establish strict limitations on inference-making from brain signals that could violate cognitive privacy.
The framework must address the concept of neural non-discrimination, ensuring that brain data cannot be used to create unfair advantages or disadvantages in employment, insurance, education, or social contexts. This includes establishing protections against neural profiling and preventing the use of brain data for purposes beyond the explicitly consented applications.
Data ownership and control represent another crucial component, requiring clear definitions of who owns neural data and how individuals can exercise control over their brain information throughout its lifecycle. The framework must establish rights for data portability, deletion, and correction specific to neural data contexts.
Finally, the ethical framework must incorporate principles of transparency and accountability, requiring organizations to clearly communicate their neural data practices and establish mechanisms for oversight and enforcement of ethical standards in brain-computer interface implementations.
Unlock deeper insights with Patsnap Eureka Quick Research — get a full tech report to explore trends and direct your research. Try now!
Generate Your Research Report Instantly with AI Agent
Supercharge your innovation with Patsnap Eureka AI Agent Platform!