MAP Security: Protecting Proprietary Experimental Flows And Models
AUG 29, 202510 MIN READ
Generate Your Research Report Instantly with AI Agent
PatSnap Eureka helps you evaluate technical feasibility & market potential.
MAP Security Background and Objectives
The evolution of Machine Learning Access Points (MAP) has revolutionized how organizations deploy and utilize machine learning models across various domains. However, this advancement has introduced significant security concerns regarding the protection of proprietary experimental flows and models. As machine learning becomes increasingly integral to business operations, the security of these assets has emerged as a critical priority for organizations investing heavily in AI research and development.
MAP Security encompasses the protection mechanisms designed to safeguard valuable intellectual property embedded within machine learning workflows, experimental configurations, and model architectures. The historical development of this field has been driven by the growing recognition that machine learning assets represent substantial competitive advantages that require robust protection against unauthorized access, theft, or replication.
The primary objective of MAP Security is to establish comprehensive protection frameworks that preserve the confidentiality, integrity, and controlled accessibility of proprietary machine learning assets. This includes securing the experimental flows—the sequences of operations, parameter settings, and methodological approaches that lead to successful model development—as well as the resulting models themselves, which embody valuable intellectual property and competitive insights.
Recent industry trends indicate a significant increase in targeted attacks against machine learning infrastructure, with adversaries employing sophisticated techniques to extract proprietary algorithms, training methodologies, and model parameters. These security breaches can result in substantial financial losses, erosion of competitive advantage, and compromise of sensitive information processed by these models.
The technical evolution of MAP Security has progressed from basic access control mechanisms to sophisticated multi-layered protection strategies incorporating encryption, secure enclaves, federated learning approaches, and differential privacy techniques. This evolution reflects the increasing complexity of threats and the growing value of machine learning assets in the digital economy.
Current technological objectives in MAP Security focus on developing solutions that balance robust protection with operational efficiency, ensuring that security measures do not significantly impede the agility and innovation that characterize successful machine learning operations. This includes creating security frameworks that can adapt to the rapid pace of machine learning development while maintaining effective protection against evolving threat vectors.
The global landscape of MAP Security development shows varying approaches across different regions, with significant advancements emerging from research institutions and technology companies in North America, Europe, and Asia. These regional variations reflect different regulatory environments, market priorities, and technological capabilities that influence security implementation strategies.
MAP Security encompasses the protection mechanisms designed to safeguard valuable intellectual property embedded within machine learning workflows, experimental configurations, and model architectures. The historical development of this field has been driven by the growing recognition that machine learning assets represent substantial competitive advantages that require robust protection against unauthorized access, theft, or replication.
The primary objective of MAP Security is to establish comprehensive protection frameworks that preserve the confidentiality, integrity, and controlled accessibility of proprietary machine learning assets. This includes securing the experimental flows—the sequences of operations, parameter settings, and methodological approaches that lead to successful model development—as well as the resulting models themselves, which embody valuable intellectual property and competitive insights.
Recent industry trends indicate a significant increase in targeted attacks against machine learning infrastructure, with adversaries employing sophisticated techniques to extract proprietary algorithms, training methodologies, and model parameters. These security breaches can result in substantial financial losses, erosion of competitive advantage, and compromise of sensitive information processed by these models.
The technical evolution of MAP Security has progressed from basic access control mechanisms to sophisticated multi-layered protection strategies incorporating encryption, secure enclaves, federated learning approaches, and differential privacy techniques. This evolution reflects the increasing complexity of threats and the growing value of machine learning assets in the digital economy.
Current technological objectives in MAP Security focus on developing solutions that balance robust protection with operational efficiency, ensuring that security measures do not significantly impede the agility and innovation that characterize successful machine learning operations. This includes creating security frameworks that can adapt to the rapid pace of machine learning development while maintaining effective protection against evolving threat vectors.
The global landscape of MAP Security development shows varying approaches across different regions, with significant advancements emerging from research institutions and technology companies in North America, Europe, and Asia. These regional variations reflect different regulatory environments, market priorities, and technological capabilities that influence security implementation strategies.
Market Demand Analysis for Secure MAP Solutions
The market for secure Machine-Assisted Programming (MAP) solutions is experiencing rapid growth, driven by the increasing value of proprietary experimental flows and AI models in the technology sector. As organizations invest heavily in developing unique MAP workflows and custom models, the need to protect these intellectual assets has become paramount. Current market analysis indicates that the global market for AI security solutions is expanding at a compound annual growth rate of over 20%, with MAP security representing a significant segment of this growth.
Industry surveys reveal that over 75% of technology companies now consider their experimental MAP flows and models as critical intellectual property assets. This perception has intensified as the competitive advantage gained from advanced AI systems becomes more pronounced. The financial implications are substantial, with leading technology firms reporting that security breaches involving proprietary AI assets could potentially result in losses exceeding hundreds of millions of dollars through competitive disadvantage and market share erosion.
The demand for secure MAP solutions spans multiple sectors. In the software development industry, companies are seeking robust protection mechanisms for their code generation models and experimental programming workflows. The healthcare sector shows growing interest in securing medical research MAP applications that involve sensitive patient data and proprietary diagnostic algorithms. Financial institutions are increasingly investing in secure MAP infrastructure to protect their algorithmic trading models and financial analysis systems.
Market research indicates that enterprise customers are willing to pay premium prices for MAP security solutions that offer comprehensive protection without significantly impacting system performance or developer productivity. The most sought-after features include granular access controls, encryption of model parameters, secure execution environments, and tamper-evident logging systems. Additionally, there is rising demand for solutions that can protect MAP assets across distributed computing environments and cloud platforms.
Regulatory developments are further driving market growth. Recent legislation in major markets has established stricter requirements for protecting intellectual property in AI systems, with penalties for non-compliance becoming more severe. This regulatory landscape has created urgency among organizations to implement robust MAP security measures, particularly in regulated industries such as finance, healthcare, and defense.
Geographically, North America currently leads the market for secure MAP solutions, followed by Europe and the Asia-Pacific region. However, the fastest growth is being observed in emerging technology hubs in Southeast Asia and the Middle East, where rapid AI adoption is creating new demand for security solutions. This global expansion presents significant opportunities for vendors who can address region-specific regulatory requirements and security concerns.
Industry surveys reveal that over 75% of technology companies now consider their experimental MAP flows and models as critical intellectual property assets. This perception has intensified as the competitive advantage gained from advanced AI systems becomes more pronounced. The financial implications are substantial, with leading technology firms reporting that security breaches involving proprietary AI assets could potentially result in losses exceeding hundreds of millions of dollars through competitive disadvantage and market share erosion.
The demand for secure MAP solutions spans multiple sectors. In the software development industry, companies are seeking robust protection mechanisms for their code generation models and experimental programming workflows. The healthcare sector shows growing interest in securing medical research MAP applications that involve sensitive patient data and proprietary diagnostic algorithms. Financial institutions are increasingly investing in secure MAP infrastructure to protect their algorithmic trading models and financial analysis systems.
Market research indicates that enterprise customers are willing to pay premium prices for MAP security solutions that offer comprehensive protection without significantly impacting system performance or developer productivity. The most sought-after features include granular access controls, encryption of model parameters, secure execution environments, and tamper-evident logging systems. Additionally, there is rising demand for solutions that can protect MAP assets across distributed computing environments and cloud platforms.
Regulatory developments are further driving market growth. Recent legislation in major markets has established stricter requirements for protecting intellectual property in AI systems, with penalties for non-compliance becoming more severe. This regulatory landscape has created urgency among organizations to implement robust MAP security measures, particularly in regulated industries such as finance, healthcare, and defense.
Geographically, North America currently leads the market for secure MAP solutions, followed by Europe and the Asia-Pacific region. However, the fastest growth is being observed in emerging technology hubs in Southeast Asia and the Middle East, where rapid AI adoption is creating new demand for security solutions. This global expansion presents significant opportunities for vendors who can address region-specific regulatory requirements and security concerns.
Current MAP Security Challenges and Limitations
Despite significant advancements in Model-Based Accelerated Processing (MAP) technologies, current security mechanisms face substantial challenges in protecting proprietary experimental flows and models. The primary limitation stems from the inherent tension between collaboration requirements and intellectual property protection. Organizations must share certain model components with partners or vendors while simultaneously safeguarding their competitive advantages, creating a complex security boundary that is difficult to maintain.
Traditional encryption methods prove inadequate when applied to MAP environments due to the dynamic nature of model execution. While data-at-rest encryption provides reasonable protection for stored models, securing models during execution presents a more formidable challenge. The computational overhead of continuous encryption/decryption operations significantly impacts the performance benefits that MAP technologies aim to deliver, creating an undesirable trade-off between security and efficiency.
Access control mechanisms currently employed in MAP environments typically lack granularity. They operate on an all-or-nothing principle, where users either have complete access to models or none at all. This approach fails to accommodate the nuanced requirements of collaborative development scenarios where different stakeholders require varying levels of visibility into specific model components without necessarily accessing the entire proprietary workflow.
Model extraction attacks represent another critical vulnerability. Sophisticated adversaries can potentially reconstruct proprietary models through careful observation of inputs and outputs, even without direct access to the model architecture. Current defensive measures against such inference attacks remain largely theoretical or provide only partial protection at significant performance costs.
The distributed nature of modern MAP implementations introduces additional security complications. As models are deployed across multiple environments—from edge devices to cloud platforms—maintaining consistent security policies becomes increasingly difficult. Each transition point represents a potential vulnerability where proprietary information might be compromised.
Audit and traceability capabilities in current MAP security frameworks are notably underdeveloped. Organizations struggle to maintain comprehensive logs of model access and usage, complicating both compliance efforts and forensic analysis following suspected security breaches. This limitation makes it difficult to detect unauthorized access or model misappropriation until significant damage has already occurred.
Lastly, the rapid evolution of MAP technologies themselves outpaces security solution development. As new model architectures and acceleration techniques emerge, security mechanisms designed for previous generations become obsolete. This creates a persistent gap between cutting-edge MAP capabilities and the security measures needed to protect them, leaving organizations in a continuous cycle of security catch-up.
Traditional encryption methods prove inadequate when applied to MAP environments due to the dynamic nature of model execution. While data-at-rest encryption provides reasonable protection for stored models, securing models during execution presents a more formidable challenge. The computational overhead of continuous encryption/decryption operations significantly impacts the performance benefits that MAP technologies aim to deliver, creating an undesirable trade-off between security and efficiency.
Access control mechanisms currently employed in MAP environments typically lack granularity. They operate on an all-or-nothing principle, where users either have complete access to models or none at all. This approach fails to accommodate the nuanced requirements of collaborative development scenarios where different stakeholders require varying levels of visibility into specific model components without necessarily accessing the entire proprietary workflow.
Model extraction attacks represent another critical vulnerability. Sophisticated adversaries can potentially reconstruct proprietary models through careful observation of inputs and outputs, even without direct access to the model architecture. Current defensive measures against such inference attacks remain largely theoretical or provide only partial protection at significant performance costs.
The distributed nature of modern MAP implementations introduces additional security complications. As models are deployed across multiple environments—from edge devices to cloud platforms—maintaining consistent security policies becomes increasingly difficult. Each transition point represents a potential vulnerability where proprietary information might be compromised.
Audit and traceability capabilities in current MAP security frameworks are notably underdeveloped. Organizations struggle to maintain comprehensive logs of model access and usage, complicating both compliance efforts and forensic analysis following suspected security breaches. This limitation makes it difficult to detect unauthorized access or model misappropriation until significant damage has already occurred.
Lastly, the rapid evolution of MAP technologies themselves outpaces security solution development. As new model architectures and acceleration techniques emerge, security mechanisms designed for previous generations become obsolete. This creates a persistent gap between cutting-edge MAP capabilities and the security measures needed to protect them, leaving organizations in a continuous cycle of security catch-up.
Existing MAP Protection Mechanisms
01 Authentication and access control mechanisms
Various authentication methods and access control mechanisms are implemented to protect MAP (Mobile Application Part) security. These include multi-factor authentication, biometric verification, and token-based access systems. These mechanisms ensure that only authorized users can access sensitive information and services, preventing unauthorized access and potential security breaches in mobile network communications.- Authentication and Access Control Systems: Security systems that implement authentication mechanisms and access control protocols to protect MAP (Mobile Application Part) communications. These systems verify user identities, manage permissions, and control access to sensitive network resources. They often include multi-factor authentication, biometric verification, and role-based access controls to ensure that only authorized users can access protected MAP services and data.
- Encryption and Secure Communication Protocols: Implementation of encryption technologies and secure communication protocols to protect MAP data during transmission. These solutions encrypt sensitive information using advanced algorithms, establish secure channels for data exchange, and implement key management systems. They help prevent unauthorized interception, eavesdropping, and man-in-the-middle attacks on MAP communications.
- Intrusion Detection and Prevention Systems: Security systems designed to monitor, detect, and prevent unauthorized access or attacks on MAP infrastructure. These systems analyze network traffic patterns, identify suspicious activities, and automatically respond to potential security threats. They include real-time monitoring capabilities, anomaly detection algorithms, and automated response mechanisms to protect MAP services from various cyber threats.
- Mobile Network Security Frameworks: Comprehensive security frameworks specifically designed for mobile networks that incorporate MAP protection. These frameworks provide end-to-end security solutions for mobile communication systems, including protection for signaling protocols, subscriber data, and network infrastructure. They integrate various security mechanisms such as firewalls, security gateways, and protocol filters to safeguard MAP interfaces and transactions.
- Security Monitoring and Management Systems: Systems for continuous monitoring, management, and auditing of MAP security. These solutions provide visibility into security events, generate alerts for potential breaches, and maintain comprehensive logs for compliance and forensic purposes. They include security dashboards, reporting tools, and analytics capabilities to help organizations maintain and verify the security posture of their MAP implementations.
02 Encryption and secure data transmission
Encryption technologies are employed to secure data transmission in MAP protocols. This includes end-to-end encryption, secure key management systems, and cryptographic algorithms that protect sensitive information during transmission. These encryption methods ensure that data exchanged between mobile network entities remains confidential and cannot be intercepted or compromised by malicious actors.Expand Specific Solutions03 Intrusion detection and prevention systems
Advanced intrusion detection and prevention systems are implemented to monitor MAP networks for suspicious activities and potential security threats. These systems use real-time monitoring, anomaly detection algorithms, and behavioral analysis to identify and mitigate security breaches before they can cause significant damage to the network infrastructure or compromise user data.Expand Specific Solutions04 Hardware-based security solutions
Hardware-based security solutions provide robust protection for MAP systems through physical security measures. These include secure elements, trusted platform modules, hardware security modules, and tamper-resistant devices that protect cryptographic keys and sensitive operations. These hardware solutions offer stronger security guarantees compared to software-only approaches by providing a secure execution environment isolated from potential software vulnerabilities.Expand Specific Solutions05 Security protocols and compliance frameworks
Standardized security protocols and compliance frameworks are established to ensure consistent security practices across MAP implementations. These include industry-specific security standards, regulatory compliance requirements, and best practices for secure development and operation. By adhering to these protocols and frameworks, organizations can ensure that their MAP security protection measures meet established security benchmarks and legal requirements.Expand Specific Solutions
Key Players in MAP Security Industry
The MAP security landscape for protecting proprietary experimental flows and models is evolving rapidly, currently in a growth phase with increasing market adoption. The market is expanding as organizations recognize the critical importance of safeguarding intellectual property in machine learning and algorithmic processes. From a technical maturity perspective, industry leaders like Huawei, Intel, Samsung, and Alibaba have developed sophisticated security frameworks, while companies such as Baidu and Tencent are advancing innovative authentication mechanisms. Financial institutions including ICBC are implementing robust MAP security protocols for their proprietary systems. The competitive landscape features both established technology giants and specialized security firms like Shenzhen Kaiyuan Internet Security Technology, creating a diverse ecosystem of solutions ranging from hardware-based protection to cloud-native security implementations.
Huawei Technologies Co., Ltd.
Technical Solution: Huawei has developed a comprehensive MAP (Model, Algorithm, and Parameter) Security framework that employs multi-layered protection mechanisms. Their solution integrates hardware-based security elements with software protection techniques to safeguard proprietary experimental flows and AI models. The framework implements Trusted Execution Environments (TEE) that isolate sensitive computations from the main operating system, preventing unauthorized access. Additionally, Huawei employs model encryption, watermarking, and obfuscation techniques to protect intellectual property during both storage and inference stages. Their approach includes differential privacy methods that add calculated noise to training data and model outputs, preventing reverse engineering while maintaining model utility. For secure collaborative development, Huawei has implemented federated learning protocols that enable multiple parties to train models without sharing raw data.
Strengths: Comprehensive end-to-end protection covering the entire AI lifecycle; strong hardware-software integration leveraging their chip capabilities; mature implementation across their product ecosystem. Weaknesses: Potential performance overhead from encryption operations; some protection mechanisms may be specific to Huawei hardware, limiting broader applicability.
Samsung Electronics Co., Ltd.
Technical Solution: Samsung has created a comprehensive MAP security solution centered around their Knox security platform. Their approach integrates hardware-based security elements with software protection layers to safeguard AI models and experimental workflows. Samsung's solution implements secure enclaves within their devices where sensitive AI operations can be performed in isolation from the main operating system. For model protection, they employ encryption techniques that keep models secured both at rest and during computation. Their framework includes runtime integrity verification that continuously monitors for tampering attempts during model execution. Samsung has also developed specialized hardware acceleration for encrypted model inference, minimizing the performance impact of security measures. Their solution incorporates secure key management systems that control access to protected models based on device authentication and user authorization levels.
Strengths: Tight integration with Samsung's hardware ecosystem providing end-to-end protection; strong mobile-focused security features; efficient implementation with minimal performance impact. Weaknesses: Most comprehensive protection limited to Samsung's own device ecosystem; potential compatibility challenges with third-party development environments.
Core Security Innovations for Proprietary MAP Assets
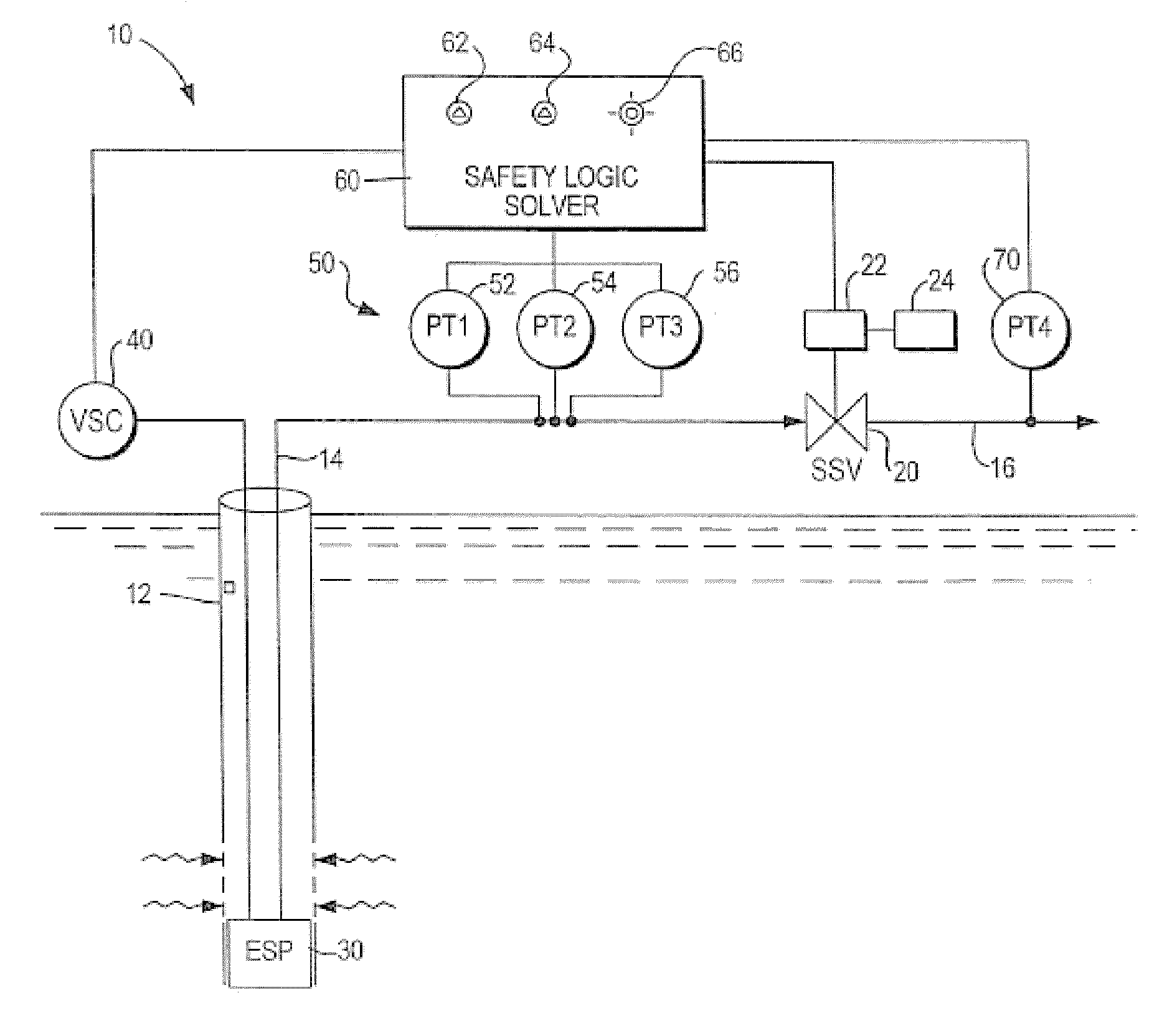
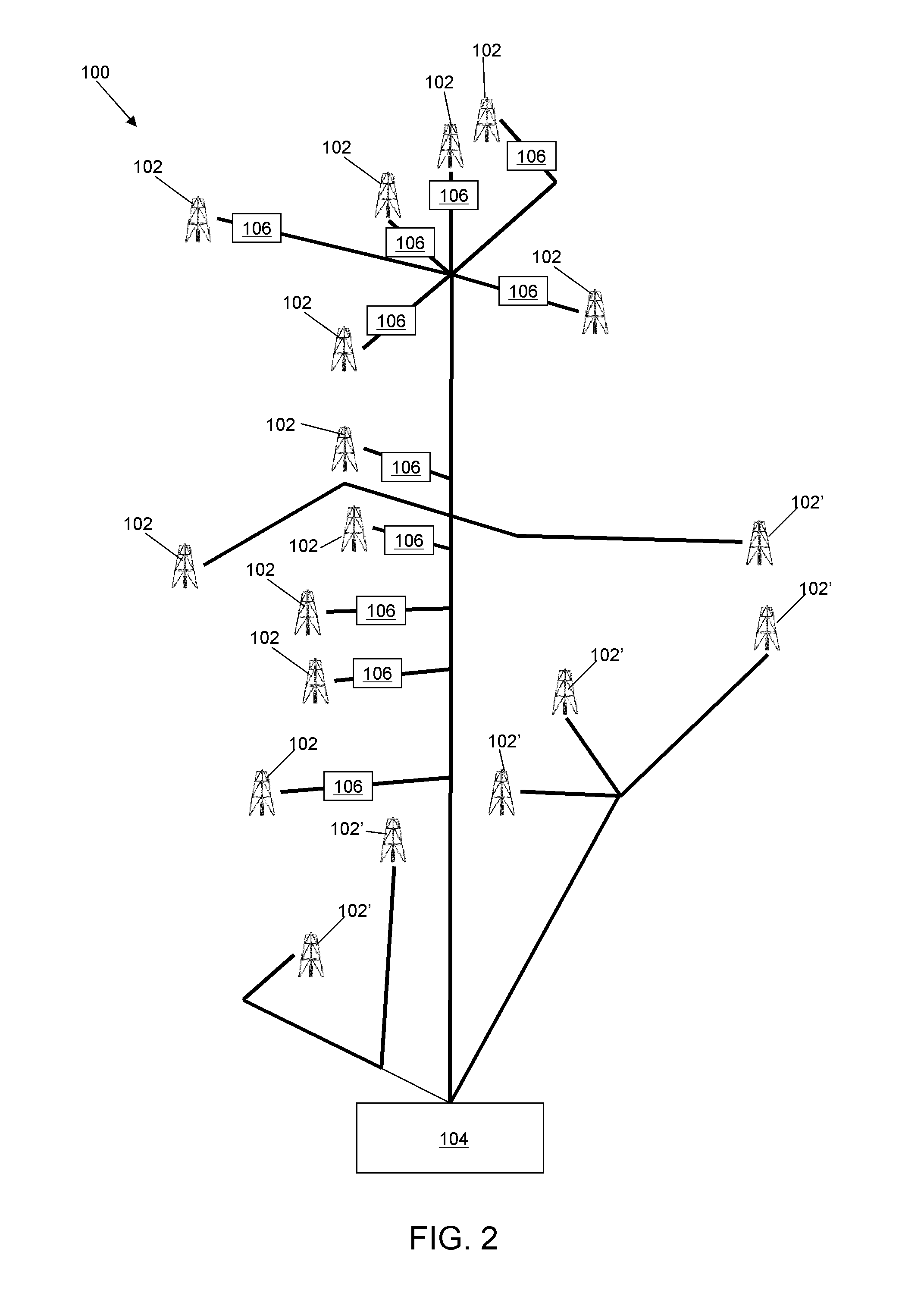
Wellhead flowline protection and testing system with esp speed controller and emergency isolation valve
PatentInactiveEP2217984A1
Innovation
- A wellhead flowline protection system utilizing an ESP variable speed controller and a surface emergency isolation valve (SSV) for fully automated testing and diagnostics, ensuring safe pressure limits are maintained during testing without interrupting production, using redundant sensors and diverse final elements to protect lower-rated flowline piping from overpressure.
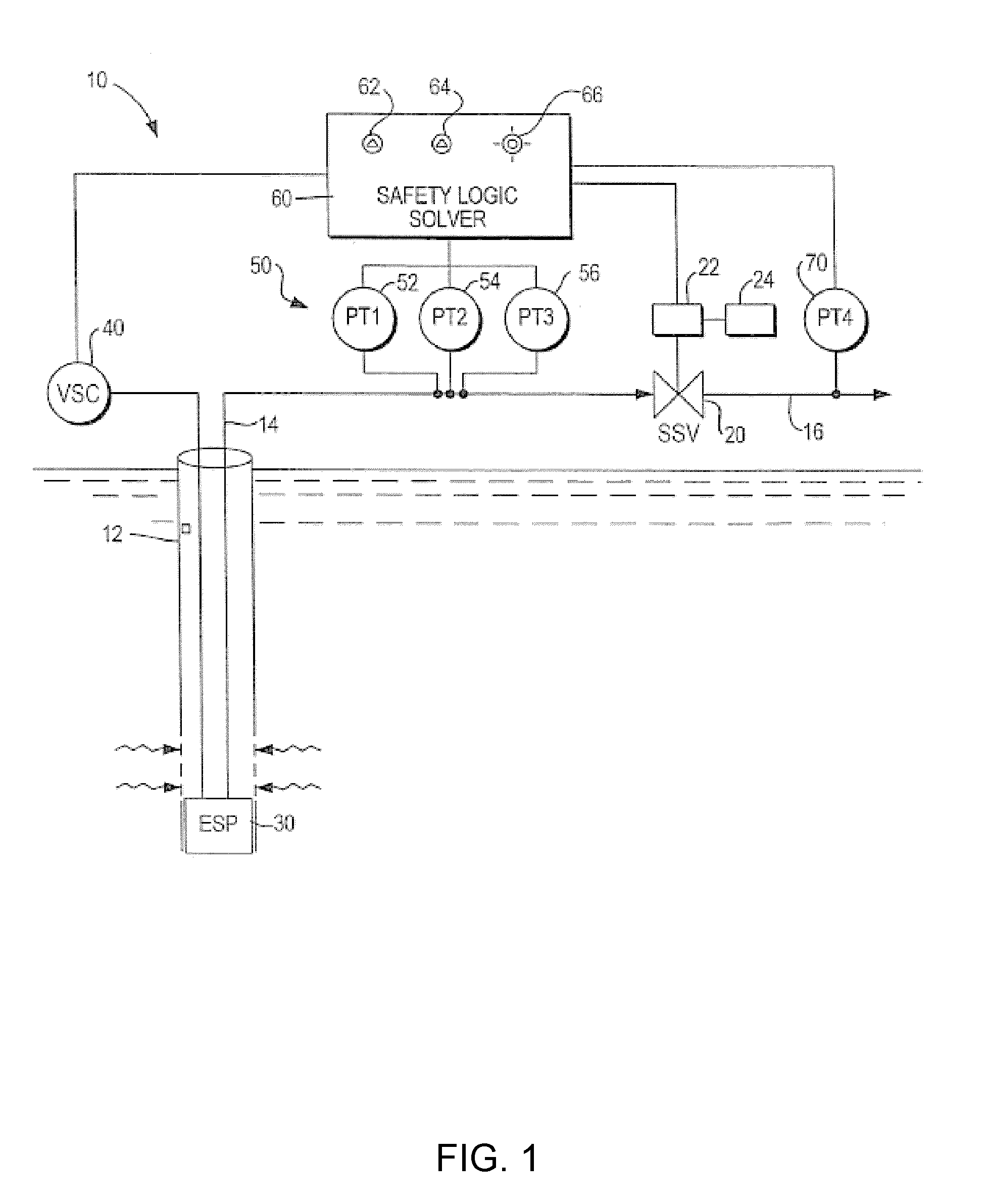
Clustered wellhead trunkline protection and testing system with esp speed controller and emergency isolation valve
PatentInactiveUS20110061861A1
Innovation
- An automated system using a safety logic solver, pressure sensors, and a variable speed drive controller for ESPs, along with an emergency isolation valve, enables continuous monitoring and online testing of wellhead flowlines without interrupting production, allowing for incremental speed adjustments and emergency shutdowns to manage pressure safely.
Regulatory Compliance for MAP Security
Regulatory compliance for MAP security has become increasingly complex as organizations navigate a multifaceted landscape of international and regional data protection regulations. The protection of Machine-Assisted Programming (MAP) systems, which often contain proprietary experimental workflows and valuable AI models, must align with frameworks such as GDPR in Europe, CCPA in California, and industry-specific regulations like HIPAA for healthcare applications. These regulations impose strict requirements on data handling, security measures, and breach notification protocols that directly impact MAP security implementations.
Organizations developing or deploying MAP technologies must establish comprehensive compliance programs that address the specific regulatory requirements applicable to their operational jurisdictions. This includes conducting regular privacy impact assessments (PIAs) and data protection impact assessments (DPIAs) when implementing new MAP features or experimental workflows. Such assessments help identify potential compliance gaps and security vulnerabilities before they manifest as regulatory violations.
Export control regulations present another critical compliance dimension for MAP security. Many countries classify advanced AI models and machine learning technologies as dual-use items with potential national security implications. The U.S. Export Administration Regulations (EAR) and International Traffic in Arms Regulations (ITAR) may restrict the cross-border transfer of certain MAP technologies, requiring organizations to implement robust controls to prevent unauthorized access or transfer of proprietary models.
Intellectual property protection frameworks also intersect with MAP security compliance requirements. Organizations must ensure their security measures adequately protect trade secrets and patented algorithms embedded within MAP systems while complying with disclosure requirements in certain regulated industries. This balancing act requires sophisticated technical controls and well-documented compliance procedures.
The financial services sector faces particularly stringent requirements when implementing MAP technologies. Regulations such as PCI DSS for payment card data and financial-specific frameworks like SOX impose additional security controls that must be integrated into MAP security architectures. These include strict access controls, encryption requirements, and comprehensive audit trails for all interactions with proprietary models.
Emerging regulations specifically targeting AI and algorithmic systems, such as the EU's proposed AI Act, will introduce new compliance challenges for MAP security. These frameworks may require organizations to demonstrate the explainability, fairness, and robustness of their proprietary models while still maintaining adequate security protections. Preparing for these evolving regulatory requirements demands forward-looking security architectures that can adapt to new compliance obligations without compromising protection for proprietary assets.
Organizations developing or deploying MAP technologies must establish comprehensive compliance programs that address the specific regulatory requirements applicable to their operational jurisdictions. This includes conducting regular privacy impact assessments (PIAs) and data protection impact assessments (DPIAs) when implementing new MAP features or experimental workflows. Such assessments help identify potential compliance gaps and security vulnerabilities before they manifest as regulatory violations.
Export control regulations present another critical compliance dimension for MAP security. Many countries classify advanced AI models and machine learning technologies as dual-use items with potential national security implications. The U.S. Export Administration Regulations (EAR) and International Traffic in Arms Regulations (ITAR) may restrict the cross-border transfer of certain MAP technologies, requiring organizations to implement robust controls to prevent unauthorized access or transfer of proprietary models.
Intellectual property protection frameworks also intersect with MAP security compliance requirements. Organizations must ensure their security measures adequately protect trade secrets and patented algorithms embedded within MAP systems while complying with disclosure requirements in certain regulated industries. This balancing act requires sophisticated technical controls and well-documented compliance procedures.
The financial services sector faces particularly stringent requirements when implementing MAP technologies. Regulations such as PCI DSS for payment card data and financial-specific frameworks like SOX impose additional security controls that must be integrated into MAP security architectures. These include strict access controls, encryption requirements, and comprehensive audit trails for all interactions with proprietary models.
Emerging regulations specifically targeting AI and algorithmic systems, such as the EU's proposed AI Act, will introduce new compliance challenges for MAP security. These frameworks may require organizations to demonstrate the explainability, fairness, and robustness of their proprietary models while still maintaining adequate security protections. Preparing for these evolving regulatory requirements demands forward-looking security architectures that can adapt to new compliance obligations without compromising protection for proprietary assets.
Risk Assessment Framework for MAP Systems
A comprehensive risk assessment framework for MAP (Machine Assisted Programming) systems requires systematic evaluation of vulnerabilities across multiple dimensions. The framework must begin with threat modeling that identifies potential attack vectors specific to proprietary experimental flows and models. These threats include unauthorized access to algorithmic logic, model extraction through inference attacks, and tampering with experimental configurations that could compromise intellectual property.
Risk categorization forms the second component, classifying vulnerabilities according to their impact severity and exploitation probability. Critical risks typically involve complete model extraction or flow manipulation, while moderate risks might include partial information leakage that provides competitors with insights into proprietary methods. The framework should incorporate quantitative metrics for risk evaluation, utilizing standardized scoring systems such as CVSS (Common Vulnerability Scoring System) adapted specifically for MAP environments.
Defensive perimeter analysis constitutes an essential element, examining both technical and procedural safeguards. This includes evaluation of authentication mechanisms, encryption protocols for models in transit and at rest, and access control granularity. The framework should assess whether the principle of least privilege is effectively implemented across the MAP ecosystem, particularly focusing on separation between experimental and production environments.
Temporal considerations must be integrated through continuous monitoring protocols that detect anomalous access patterns or unexpected model behavior that might indicate security breaches. The framework should establish thresholds for automated alerts and define escalation procedures when potential compromises are detected. This dynamic assessment capability ensures that security posture evolves alongside emerging threats.
Compliance verification represents the final component, ensuring that security measures align with relevant industry standards and regulatory requirements. This includes documentation of security controls, regular audit procedures, and validation that proprietary information receives appropriate protection classification. The framework should establish clear responsibilities for security oversight and incident response within organizational structures.
Implementation guidance should accompany the framework, providing practical steps for conducting assessments at different organizational maturity levels. This includes templates for risk documentation, recommended testing methodologies, and integration points with existing security governance processes. The framework must balance comprehensive protection with operational flexibility to avoid impeding legitimate research activities.
Risk categorization forms the second component, classifying vulnerabilities according to their impact severity and exploitation probability. Critical risks typically involve complete model extraction or flow manipulation, while moderate risks might include partial information leakage that provides competitors with insights into proprietary methods. The framework should incorporate quantitative metrics for risk evaluation, utilizing standardized scoring systems such as CVSS (Common Vulnerability Scoring System) adapted specifically for MAP environments.
Defensive perimeter analysis constitutes an essential element, examining both technical and procedural safeguards. This includes evaluation of authentication mechanisms, encryption protocols for models in transit and at rest, and access control granularity. The framework should assess whether the principle of least privilege is effectively implemented across the MAP ecosystem, particularly focusing on separation between experimental and production environments.
Temporal considerations must be integrated through continuous monitoring protocols that detect anomalous access patterns or unexpected model behavior that might indicate security breaches. The framework should establish thresholds for automated alerts and define escalation procedures when potential compromises are detected. This dynamic assessment capability ensures that security posture evolves alongside emerging threats.
Compliance verification represents the final component, ensuring that security measures align with relevant industry standards and regulatory requirements. This includes documentation of security controls, regular audit procedures, and validation that proprietary information receives appropriate protection classification. The framework should establish clear responsibilities for security oversight and incident response within organizational structures.
Implementation guidance should accompany the framework, providing practical steps for conducting assessments at different organizational maturity levels. This includes templates for risk documentation, recommended testing methodologies, and integration points with existing security governance processes. The framework must balance comprehensive protection with operational flexibility to avoid impeding legitimate research activities.
Unlock deeper insights with PatSnap Eureka Quick Research — get a full tech report to explore trends and direct your research. Try now!
Generate Your Research Report Instantly with AI Agent
Supercharge your innovation with PatSnap Eureka AI Agent Platform!