How to Optimize ARM for Higher Data Integrity
MAR 25, 20269 MIN READ
Generate Your Research Report Instantly with AI Agent
PatSnap Eureka helps you evaluate technical feasibility & market potential.
ARM Data Integrity Enhancement Background and Objectives
ARM processors have evolved from simple embedded controllers to sophisticated computing platforms powering everything from smartphones to data centers. As ARM-based systems increasingly handle sensitive data and critical operations, the imperative for robust data integrity mechanisms has become paramount. The proliferation of ARM processors in cloud computing, autonomous vehicles, financial systems, and IoT devices has elevated data integrity from a desirable feature to an essential requirement.
The historical development of ARM architecture reveals a gradual but accelerating focus on reliability features. Early ARM designs prioritized power efficiency and performance, with basic error detection capabilities. However, as ARM processors began penetrating mission-critical applications, the need for comprehensive data integrity solutions became evident. The introduction of features like ECC memory support, hardware-assisted virtualization with security extensions, and advanced debugging capabilities marked significant milestones in this evolution.
Current market demands reflect an unprecedented emphasis on data reliability across diverse sectors. Financial institutions require ARM-based systems to maintain transactional integrity under extreme loads. Automotive manufacturers depend on ARM processors for safety-critical functions where data corruption could have catastrophic consequences. Healthcare systems processing patient data demand unwavering reliability to ensure both regulatory compliance and patient safety.
The primary technical objectives for ARM data integrity enhancement encompass multiple dimensions. Hardware-level objectives include implementing robust error correction codes, developing advanced memory protection units, and integrating real-time error monitoring capabilities. Software-level goals focus on creating efficient integrity checking algorithms, establishing secure boot processes, and developing comprehensive fault tolerance mechanisms.
Performance optimization remains a critical objective, as data integrity enhancements must not compromise ARM's fundamental advantages in power efficiency and computational speed. The challenge lies in implementing sophisticated integrity mechanisms while maintaining the lean, efficient architecture that defines ARM processors. This requires innovative approaches to parallel processing, intelligent caching strategies, and adaptive error correction techniques.
Future objectives extend beyond traditional error detection and correction to encompass predictive integrity management. Advanced machine learning algorithms integrated into ARM systems could anticipate potential data corruption scenarios, enabling proactive mitigation strategies. Additionally, the integration of quantum-resistant cryptographic methods and blockchain-based integrity verification represents emerging frontiers in ARM data integrity enhancement.
The historical development of ARM architecture reveals a gradual but accelerating focus on reliability features. Early ARM designs prioritized power efficiency and performance, with basic error detection capabilities. However, as ARM processors began penetrating mission-critical applications, the need for comprehensive data integrity solutions became evident. The introduction of features like ECC memory support, hardware-assisted virtualization with security extensions, and advanced debugging capabilities marked significant milestones in this evolution.
Current market demands reflect an unprecedented emphasis on data reliability across diverse sectors. Financial institutions require ARM-based systems to maintain transactional integrity under extreme loads. Automotive manufacturers depend on ARM processors for safety-critical functions where data corruption could have catastrophic consequences. Healthcare systems processing patient data demand unwavering reliability to ensure both regulatory compliance and patient safety.
The primary technical objectives for ARM data integrity enhancement encompass multiple dimensions. Hardware-level objectives include implementing robust error correction codes, developing advanced memory protection units, and integrating real-time error monitoring capabilities. Software-level goals focus on creating efficient integrity checking algorithms, establishing secure boot processes, and developing comprehensive fault tolerance mechanisms.
Performance optimization remains a critical objective, as data integrity enhancements must not compromise ARM's fundamental advantages in power efficiency and computational speed. The challenge lies in implementing sophisticated integrity mechanisms while maintaining the lean, efficient architecture that defines ARM processors. This requires innovative approaches to parallel processing, intelligent caching strategies, and adaptive error correction techniques.
Future objectives extend beyond traditional error detection and correction to encompass predictive integrity management. Advanced machine learning algorithms integrated into ARM systems could anticipate potential data corruption scenarios, enabling proactive mitigation strategies. Additionally, the integration of quantum-resistant cryptographic methods and blockchain-based integrity verification represents emerging frontiers in ARM data integrity enhancement.
Market Demand for High-Integrity ARM Computing Solutions
The demand for high-integrity ARM computing solutions is experiencing unprecedented growth across multiple critical sectors, driven by the increasing digitization of safety-critical systems and the proliferation of edge computing applications. Industries such as automotive, aerospace, medical devices, industrial automation, and telecommunications are actively seeking ARM-based processors that can deliver enhanced data integrity while maintaining the architecture's inherent advantages of power efficiency and cost-effectiveness.
In the automotive sector, the transition toward autonomous vehicles and advanced driver assistance systems has created substantial demand for ARM processors capable of handling safety-critical computations with zero tolerance for data corruption. Modern vehicles require real-time processing of sensor data, navigation information, and control signals, where even minor data integrity failures could result in catastrophic consequences. This has prompted automotive manufacturers to prioritize ARM solutions with built-in error detection and correction capabilities.
The aerospace and defense industries represent another significant market segment demanding high-integrity ARM computing solutions. Satellite systems, avionics, and military applications require processors that can operate reliably in harsh environments while maintaining data accuracy under extreme conditions including radiation exposure and temperature variations. These applications often mandate compliance with stringent safety standards such as DO-178C and DO-254, driving the need for ARM processors with enhanced fault tolerance mechanisms.
Medical device manufacturers are increasingly adopting ARM-based systems for critical healthcare applications including patient monitoring, diagnostic equipment, and implantable devices. The regulatory requirements in healthcare, particularly FDA approval processes, necessitate ARM solutions with robust data integrity features to ensure patient safety and device reliability throughout extended operational periods.
Industrial automation and Internet of Things deployments are generating substantial demand for ARM processors that can maintain data integrity in distributed computing environments. Manufacturing systems, smart grid infrastructure, and process control applications require ARM-based solutions capable of detecting and correcting data errors in real-time while operating continuously in challenging industrial environments.
The telecommunications sector's evolution toward 5G networks and edge computing infrastructure has created additional market opportunities for high-integrity ARM solutions. Network equipment manufacturers require processors that can handle massive data throughput while ensuring signal integrity and preventing data corruption that could compromise network reliability and security.
Market growth is further accelerated by regulatory compliance requirements across industries, with safety standards becoming increasingly stringent and comprehensive. Organizations are recognizing that investing in high-integrity ARM computing solutions represents a proactive approach to risk mitigation and regulatory adherence, ultimately reducing long-term operational costs and liability exposure.
In the automotive sector, the transition toward autonomous vehicles and advanced driver assistance systems has created substantial demand for ARM processors capable of handling safety-critical computations with zero tolerance for data corruption. Modern vehicles require real-time processing of sensor data, navigation information, and control signals, where even minor data integrity failures could result in catastrophic consequences. This has prompted automotive manufacturers to prioritize ARM solutions with built-in error detection and correction capabilities.
The aerospace and defense industries represent another significant market segment demanding high-integrity ARM computing solutions. Satellite systems, avionics, and military applications require processors that can operate reliably in harsh environments while maintaining data accuracy under extreme conditions including radiation exposure and temperature variations. These applications often mandate compliance with stringent safety standards such as DO-178C and DO-254, driving the need for ARM processors with enhanced fault tolerance mechanisms.
Medical device manufacturers are increasingly adopting ARM-based systems for critical healthcare applications including patient monitoring, diagnostic equipment, and implantable devices. The regulatory requirements in healthcare, particularly FDA approval processes, necessitate ARM solutions with robust data integrity features to ensure patient safety and device reliability throughout extended operational periods.
Industrial automation and Internet of Things deployments are generating substantial demand for ARM processors that can maintain data integrity in distributed computing environments. Manufacturing systems, smart grid infrastructure, and process control applications require ARM-based solutions capable of detecting and correcting data errors in real-time while operating continuously in challenging industrial environments.
The telecommunications sector's evolution toward 5G networks and edge computing infrastructure has created additional market opportunities for high-integrity ARM solutions. Network equipment manufacturers require processors that can handle massive data throughput while ensuring signal integrity and preventing data corruption that could compromise network reliability and security.
Market growth is further accelerated by regulatory compliance requirements across industries, with safety standards becoming increasingly stringent and comprehensive. Organizations are recognizing that investing in high-integrity ARM computing solutions represents a proactive approach to risk mitigation and regulatory adherence, ultimately reducing long-term operational costs and liability exposure.
Current ARM Data Integrity Challenges and Limitations
ARM processors face significant data integrity challenges that stem from their widespread deployment across diverse computing environments, from mobile devices to enterprise servers. The fundamental challenge lies in balancing performance optimization with robust error detection and correction mechanisms, as ARM's energy-efficient design philosophy often conflicts with the overhead required for comprehensive data protection.
Memory subsystem vulnerabilities represent a critical area of concern. ARM processors frequently operate in environments where soft errors from cosmic radiation, electromagnetic interference, and voltage fluctuations can corrupt data stored in caches, registers, and main memory. Unlike traditional server processors that incorporate extensive Error Correcting Code (ECC) mechanisms, many ARM implementations prioritize power efficiency over error resilience, leaving systems vulnerable to single-event upsets and multi-bit errors.
Cache coherency issues pose another substantial challenge, particularly in multi-core ARM configurations. The complexity of maintaining data consistency across multiple processing cores while ensuring high-speed operation creates opportunities for data corruption. ARM's cache architecture, while optimized for performance, can experience race conditions and coherency protocol failures that compromise data integrity during high-throughput operations.
The heterogeneous nature of ARM ecosystems introduces additional complexity. Different ARM core designs, varying memory controllers, and diverse system-on-chip implementations create inconsistent data protection capabilities across the platform landscape. This fragmentation makes it difficult to implement uniform data integrity solutions that work effectively across all ARM variants.
Power management features, while essential for ARM's energy efficiency, create unique data integrity risks. Dynamic voltage and frequency scaling, power gating, and sleep modes can introduce timing variations and voltage instabilities that increase the likelihood of data corruption. The transition between different power states represents particularly vulnerable periods where data integrity mechanisms may be temporarily compromised.
Limited hardware-based security features in many ARM implementations further exacerbate data integrity challenges. While newer ARM architectures include TrustZone and other security extensions, legacy systems and cost-optimized implementations often lack comprehensive hardware-level data protection mechanisms, forcing reliance on software-based solutions that introduce performance penalties and potential security gaps.
Memory subsystem vulnerabilities represent a critical area of concern. ARM processors frequently operate in environments where soft errors from cosmic radiation, electromagnetic interference, and voltage fluctuations can corrupt data stored in caches, registers, and main memory. Unlike traditional server processors that incorporate extensive Error Correcting Code (ECC) mechanisms, many ARM implementations prioritize power efficiency over error resilience, leaving systems vulnerable to single-event upsets and multi-bit errors.
Cache coherency issues pose another substantial challenge, particularly in multi-core ARM configurations. The complexity of maintaining data consistency across multiple processing cores while ensuring high-speed operation creates opportunities for data corruption. ARM's cache architecture, while optimized for performance, can experience race conditions and coherency protocol failures that compromise data integrity during high-throughput operations.
The heterogeneous nature of ARM ecosystems introduces additional complexity. Different ARM core designs, varying memory controllers, and diverse system-on-chip implementations create inconsistent data protection capabilities across the platform landscape. This fragmentation makes it difficult to implement uniform data integrity solutions that work effectively across all ARM variants.
Power management features, while essential for ARM's energy efficiency, create unique data integrity risks. Dynamic voltage and frequency scaling, power gating, and sleep modes can introduce timing variations and voltage instabilities that increase the likelihood of data corruption. The transition between different power states represents particularly vulnerable periods where data integrity mechanisms may be temporarily compromised.
Limited hardware-based security features in many ARM implementations further exacerbate data integrity challenges. While newer ARM architectures include TrustZone and other security extensions, legacy systems and cost-optimized implementations often lack comprehensive hardware-level data protection mechanisms, forcing reliance on software-based solutions that introduce performance penalties and potential security gaps.
Existing ARM Data Integrity Protection Solutions
01 Error detection and correction mechanisms in ARM processors
Implementation of error detection and correction codes (ECC) to ensure data integrity in ARM-based systems. These mechanisms detect and correct single-bit errors and detect multi-bit errors in memory and data transmission paths. Parity checking and cyclic redundancy check (CRC) techniques are employed to verify data accuracy during storage and transfer operations.- Error detection and correction mechanisms in ARM processors: Implementation of error detection and correction codes (ECC) to ensure data integrity in ARM-based systems. These mechanisms detect and correct single-bit errors and detect multi-bit errors in memory and data transmission paths. Parity checking and cyclic redundancy check (CRC) techniques are employed to validate data accuracy during processing and storage operations.
- Memory protection and access control in ARM architecture: Techniques for protecting memory regions and controlling access permissions in ARM processors to maintain data integrity. Memory management units (MMU) and memory protection units (MPU) are utilized to prevent unauthorized access and data corruption. These mechanisms enforce privilege levels and access rights to ensure that only authorized processes can read or modify specific memory regions.
- Secure boot and trusted execution environment: Implementation of secure boot processes and trusted execution environments (TEE) in ARM systems to ensure data integrity from system startup. These technologies verify the authenticity and integrity of firmware and software before execution. Cryptographic signatures and hash verification are used to detect tampering and ensure that only trusted code is executed on the processor.
- Data encryption and cryptographic operations: Integration of hardware-accelerated cryptographic engines in ARM processors to protect data integrity through encryption. These implementations provide efficient encryption and decryption operations for data at rest and in transit. Advanced encryption standards and cryptographic protocols are supported to ensure confidentiality and integrity of sensitive information processed by ARM-based devices.
- Bus integrity and transaction monitoring: Mechanisms for monitoring and validating data transactions on ARM system buses to maintain data integrity. Bus integrity checkers and transaction monitors detect anomalies and errors during data transfers between processor cores, memory, and peripherals. Protocol compliance verification and real-time error detection ensure that data corruption is identified and handled appropriately during system operation.
02 Memory protection and access control in ARM architecture
Techniques for protecting memory regions and controlling access permissions in ARM processors to maintain data integrity. Memory management units (MMU) and memory protection units (MPU) are utilized to define access rights and prevent unauthorized modifications. These mechanisms ensure that only authorized processes can read, write, or execute specific memory regions, preventing data corruption.Expand Specific Solutions03 Secure boot and trusted execution environment
Implementation of secure boot processes and trusted execution environments (TEE) in ARM systems to ensure data integrity from system startup. These technologies verify the authenticity and integrity of firmware and software before execution. Cryptographic signatures and hash verification are used to detect any unauthorized modifications to the boot chain and runtime environment.Expand Specific Solutions04 Data integrity verification through cryptographic methods
Application of cryptographic techniques including digital signatures, message authentication codes (MAC), and hash functions to verify data integrity in ARM-based systems. These methods ensure that data has not been tampered with during storage or transmission. Hardware-accelerated cryptographic engines in ARM processors provide efficient computation of integrity checks.Expand Specific Solutions05 Bus and interconnect integrity monitoring
Monitoring and verification mechanisms for data integrity on system buses and interconnects in ARM architectures. These include protocol-level checks, transaction monitoring, and integrity tags that accompany data transfers. Real-time detection of transmission errors and corruption on communication channels between processors, memory, and peripherals ensures system reliability.Expand Specific Solutions
Key Players in ARM-based High-Reliability Computing
The ARM data integrity optimization landscape represents a rapidly evolving sector driven by increasing demand for secure, reliable computing across edge, cloud, and embedded systems. The market demonstrates significant growth potential as ARM-based architectures expand beyond mobile into data centers and high-performance computing. Technology maturity varies considerably among key players: established semiconductor leaders like ARM Limited, Texas Instruments, and Micron Technology possess advanced hardware-level integrity solutions, while companies such as Beijing Shudun specialize in ARM-powered secure storage systems. Chinese technology firms including Alibaba Cloud, Hygon Information Technology, and various research institutions are developing localized ARM optimization solutions. The competitive landscape shows a mix of hardware manufacturers, cloud service providers, and specialized security companies, indicating the technology is transitioning from early adoption to mainstream implementation, with particular emphasis on cryptographic enhancements and fault-tolerant architectures.
ARM LIMITED
Technical Solution: ARM implements comprehensive data integrity solutions through its TrustZone technology and Pointer Authentication features. TrustZone creates secure and non-secure worlds within the processor, isolating critical operations and sensitive data from potential threats. The architecture includes hardware-based memory protection units (MPU) and memory management units (MMU) that enforce access controls and prevent unauthorized memory access. ARM's Cortex-A series processors incorporate advanced error correction codes (ECC) for cache and memory subsystems, detecting and correcting single-bit errors while flagging multi-bit errors. The company's latest architectures feature enhanced branch prediction security and speculative execution protections to mitigate side-channel attacks that could compromise data integrity.
Strengths: Industry-leading security architecture with hardware-level isolation, comprehensive ecosystem support, and proven track record in mobile and embedded systems. Weaknesses: Higher complexity in implementation, potential performance overhead from security features, and dependency on software stack for full security realization.
Micron Technology, Inc.
Technical Solution: Micron's contribution to ARM data integrity optimization centers on advanced memory technologies and storage solutions that complement ARM processors. The company develops high-reliability memory products with built-in error correction capabilities, including advanced ECC algorithms that can correct multi-bit errors and detect complex error patterns. Micron's approach includes implementing on-die ECC for NAND flash memory and advanced error correction for DRAM products used in ARM-based systems. Their solutions feature real-time error monitoring and predictive analytics to identify potential memory degradation before it affects data integrity. Micron also provides specialized memory architectures optimized for ARM's cache hierarchies and memory access patterns, ensuring optimal performance while maintaining data reliability.
Strengths: Leading memory technology expertise, comprehensive error correction capabilities, and strong integration with ARM ecosystems. Weaknesses: Limited to memory-centric solutions, dependency on ARM processor vendors for full system integration, and potential cost premium for high-reliability memory products.
Core Innovations in ARM Fault-Tolerant Architecture
Data integrity improvement programming techniques
PatentPendingUS20240296879A1
Innovation
- Implementing data integrity improvement programming techniques by identifying and bolstering affected data areas with additional data or adjusting data characteristics like read thresholds and voltage levels, and performing refresh operations using these adjustments to enhance data integrity.
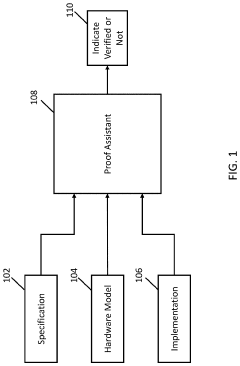
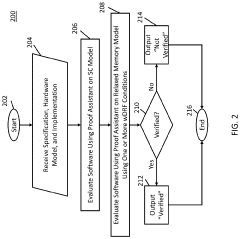
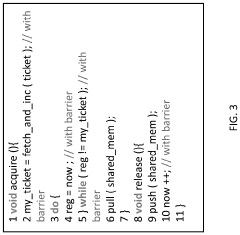
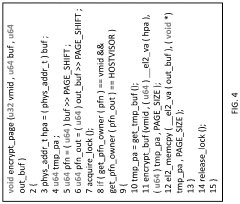
Systems, methods, and media for proving the correctness of software on relaxed memory hardware
PatentActiveUS20220019514A1
Innovation
- The mechanisms involve evaluating software using a sequentially consistent hardware model and a relaxed memory hardware model, with conditions such as data-race-free kernel, no-barrier-misuse, memory-isolation, transactional-page-table, write-once-kernel-mapping, and weak-memory-isolation conditions to determine software correctness, using proof assistants like Coq to verify kernel-level system software.
Safety Standards and Certification Requirements for ARM Systems
ARM systems operating in safety-critical environments must comply with rigorous international standards to ensure data integrity and system reliability. The most prominent framework is ISO 26262, which defines functional safety requirements for automotive electronic systems. This standard establishes Safety Integrity Levels (SIL) ranging from A to D, with ASIL-D representing the highest criticality level for systems where failure could result in life-threatening situations.
IEC 61508 serves as the foundational standard for functional safety across industrial sectors, providing comprehensive guidelines for safety lifecycle management. ARM-based systems must demonstrate compliance through systematic hazard analysis, risk assessment, and implementation of appropriate safety measures. The standard mandates specific architectural requirements including hardware fault tolerance, diagnostic coverage, and safe failure fraction calculations.
DO-178C governs software considerations in airborne systems, establishing rigorous verification and validation processes for ARM-based avionics applications. This standard requires extensive documentation, traceability, and testing protocols to achieve certification levels from A through E. ARM processors used in flight-critical systems must undergo comprehensive qualification processes including environmental testing and failure mode analysis.
Medical device applications follow IEC 62304 for software lifecycle processes, complemented by ISO 14971 for risk management. ARM systems in medical devices must demonstrate systematic development processes, including software classification based on potential harm to patients. The standards require comprehensive verification activities, including static analysis, dynamic testing, and clinical evaluation where applicable.
Railway applications adhere to EN 50128 and EN 50129, which specify software and safety-related electronic systems requirements respectively. These standards define Safety Integrity Levels (SIL 1-4) and mandate specific development methodologies, including formal methods for highest criticality applications. ARM-based railway systems must undergo independent safety assessment and continuous monitoring throughout their operational lifecycle.
Nuclear industry applications follow IEC 61513 and IEEE 7-4.3.2, requiring extensive qualification processes for digital instrumentation and control systems. ARM processors must demonstrate resistance to radiation effects, electromagnetic interference, and environmental stresses typical in nuclear facilities.
Certification processes typically involve third-party assessment bodies who evaluate compliance with applicable standards. These assessments include design reviews, testing verification, quality management system audits, and ongoing surveillance activities to maintain certification validity throughout the product lifecycle.
IEC 61508 serves as the foundational standard for functional safety across industrial sectors, providing comprehensive guidelines for safety lifecycle management. ARM-based systems must demonstrate compliance through systematic hazard analysis, risk assessment, and implementation of appropriate safety measures. The standard mandates specific architectural requirements including hardware fault tolerance, diagnostic coverage, and safe failure fraction calculations.
DO-178C governs software considerations in airborne systems, establishing rigorous verification and validation processes for ARM-based avionics applications. This standard requires extensive documentation, traceability, and testing protocols to achieve certification levels from A through E. ARM processors used in flight-critical systems must undergo comprehensive qualification processes including environmental testing and failure mode analysis.
Medical device applications follow IEC 62304 for software lifecycle processes, complemented by ISO 14971 for risk management. ARM systems in medical devices must demonstrate systematic development processes, including software classification based on potential harm to patients. The standards require comprehensive verification activities, including static analysis, dynamic testing, and clinical evaluation where applicable.
Railway applications adhere to EN 50128 and EN 50129, which specify software and safety-related electronic systems requirements respectively. These standards define Safety Integrity Levels (SIL 1-4) and mandate specific development methodologies, including formal methods for highest criticality applications. ARM-based railway systems must undergo independent safety assessment and continuous monitoring throughout their operational lifecycle.
Nuclear industry applications follow IEC 61513 and IEEE 7-4.3.2, requiring extensive qualification processes for digital instrumentation and control systems. ARM processors must demonstrate resistance to radiation effects, electromagnetic interference, and environmental stresses typical in nuclear facilities.
Certification processes typically involve third-party assessment bodies who evaluate compliance with applicable standards. These assessments include design reviews, testing verification, quality management system audits, and ongoing surveillance activities to maintain certification validity throughout the product lifecycle.
Hardware-Software Co-design for ARM Data Integrity
Hardware-software co-design represents a paradigm shift in ARM architecture optimization, where data integrity mechanisms are embedded at both hardware and software layers through synchronized development processes. This integrated approach enables comprehensive protection strategies that leverage hardware acceleration while maintaining software flexibility for adaptive security policies.
Modern ARM processors incorporate dedicated hardware security extensions such as Pointer Authentication and Memory Tagging Extensions (MTE) that require coordinated software stack modifications. The co-design methodology ensures that compiler optimizations, runtime libraries, and operating system kernels are developed in tandem with hardware features to maximize data integrity coverage while minimizing performance overhead.
The integration of ARM TrustZone technology with software security frameworks exemplifies effective co-design implementation. Hardware-enforced secure and non-secure world separation works in conjunction with trusted execution environment software to create isolated computation spaces where critical data operations can be performed with enhanced integrity guarantees. This dual-layer protection mechanism requires careful orchestration between hardware privilege levels and software security policies.
Memory protection units and cache coherency mechanisms in ARM architectures benefit significantly from co-designed software that understands underlying hardware behavior. Software components can be optimized to work with specific cache line sizes, memory ordering constraints, and error correction capabilities, resulting in more efficient data integrity checking without compromising system performance.
Cross-layer error detection and correction strategies represent another crucial aspect of hardware-software co-design. Hardware-based error detection mechanisms such as ECC memory controllers and parity checking units can be complemented by software-based redundancy techniques and algorithmic error detection methods. This layered approach provides comprehensive coverage against both transient and permanent faults.
The co-design approach also enables dynamic adaptation of integrity mechanisms based on runtime conditions and threat assessments. Hardware performance counters and security event monitoring capabilities can inform software-based policy engines to adjust protection levels, enabling systems to balance security requirements with performance constraints in real-time operational environments.
Modern ARM processors incorporate dedicated hardware security extensions such as Pointer Authentication and Memory Tagging Extensions (MTE) that require coordinated software stack modifications. The co-design methodology ensures that compiler optimizations, runtime libraries, and operating system kernels are developed in tandem with hardware features to maximize data integrity coverage while minimizing performance overhead.
The integration of ARM TrustZone technology with software security frameworks exemplifies effective co-design implementation. Hardware-enforced secure and non-secure world separation works in conjunction with trusted execution environment software to create isolated computation spaces where critical data operations can be performed with enhanced integrity guarantees. This dual-layer protection mechanism requires careful orchestration between hardware privilege levels and software security policies.
Memory protection units and cache coherency mechanisms in ARM architectures benefit significantly from co-designed software that understands underlying hardware behavior. Software components can be optimized to work with specific cache line sizes, memory ordering constraints, and error correction capabilities, resulting in more efficient data integrity checking without compromising system performance.
Cross-layer error detection and correction strategies represent another crucial aspect of hardware-software co-design. Hardware-based error detection mechanisms such as ECC memory controllers and parity checking units can be complemented by software-based redundancy techniques and algorithmic error detection methods. This layered approach provides comprehensive coverage against both transient and permanent faults.
The co-design approach also enables dynamic adaptation of integrity mechanisms based on runtime conditions and threat assessments. Hardware performance counters and security event monitoring capabilities can inform software-based policy engines to adjust protection levels, enabling systems to balance security requirements with performance constraints in real-time operational environments.
Unlock deeper insights with PatSnap Eureka Quick Research — get a full tech report to explore trends and direct your research. Try now!
Generate Your Research Report Instantly with AI Agent
Supercharge your innovation with PatSnap Eureka AI Agent Platform!