How to Optimize Quantum Models for Cybersecurity Enhancements
SEP 5, 20259 MIN READ
Generate Your Research Report Instantly with AI Agent
Patsnap Eureka helps you evaluate technical feasibility & market potential.
Quantum Cybersecurity Background and Objectives
Quantum computing represents a paradigm shift in computational capabilities, leveraging quantum mechanical phenomena such as superposition and entanglement to process information in fundamentally new ways. Since its theoretical conception in the 1980s, quantum computing has evolved from abstract mathematical models to increasingly practical implementations, with significant milestones achieved in the last decade. The trajectory of quantum technologies indicates an accelerating pace of development, particularly in areas relevant to cybersecurity.
The intersection of quantum computing and cybersecurity presents both unprecedented threats and opportunities. On one hand, quantum algorithms like Shor's algorithm threaten to break widely-used public key cryptographic systems by efficiently factoring large numbers. On the other hand, quantum technologies offer novel approaches to enhance security measures through quantum key distribution, quantum random number generation, and quantum-resistant cryptographic algorithms.
Current cybersecurity frameworks face mounting challenges from increasingly sophisticated cyber threats. Traditional security models struggle with the volume, velocity, and variety of modern attacks. The objective of optimizing quantum models for cybersecurity is to develop robust, scalable solutions that leverage quantum advantages to address these challenges while preparing for the post-quantum cryptographic landscape.
Specifically, this research aims to identify and develop quantum algorithms and models that can enhance threat detection, improve encryption methods, and strengthen authentication protocols. The goal is to create practical implementations that can operate within existing security infrastructures while providing quantum-enhanced protection against both classical and quantum threats.
The evolution of quantum technologies for cybersecurity follows several distinct phases: theoretical foundations (1980s-1990s), early experimental demonstrations (2000s), development of quantum algorithms with security applications (2010s), and the current phase focusing on practical implementations and integration with existing security systems. Each phase has contributed essential building blocks toward quantum-enhanced cybersecurity solutions.
Industry adoption of quantum cybersecurity technologies remains in early stages, with significant research investment from government agencies, technology corporations, and academic institutions. The field is characterized by rapid innovation, with new theoretical approaches and experimental results regularly emerging. The technical objectives of this research include identifying optimization techniques for quantum algorithms in security applications, developing hybrid classical-quantum security models, and establishing benchmarks for quantum advantage in cybersecurity contexts.
As quantum computing hardware continues to advance, the imperative to develop and optimize quantum models for cybersecurity grows more urgent, driving both defensive measures against quantum threats and innovative applications of quantum technologies for security enhancement.
The intersection of quantum computing and cybersecurity presents both unprecedented threats and opportunities. On one hand, quantum algorithms like Shor's algorithm threaten to break widely-used public key cryptographic systems by efficiently factoring large numbers. On the other hand, quantum technologies offer novel approaches to enhance security measures through quantum key distribution, quantum random number generation, and quantum-resistant cryptographic algorithms.
Current cybersecurity frameworks face mounting challenges from increasingly sophisticated cyber threats. Traditional security models struggle with the volume, velocity, and variety of modern attacks. The objective of optimizing quantum models for cybersecurity is to develop robust, scalable solutions that leverage quantum advantages to address these challenges while preparing for the post-quantum cryptographic landscape.
Specifically, this research aims to identify and develop quantum algorithms and models that can enhance threat detection, improve encryption methods, and strengthen authentication protocols. The goal is to create practical implementations that can operate within existing security infrastructures while providing quantum-enhanced protection against both classical and quantum threats.
The evolution of quantum technologies for cybersecurity follows several distinct phases: theoretical foundations (1980s-1990s), early experimental demonstrations (2000s), development of quantum algorithms with security applications (2010s), and the current phase focusing on practical implementations and integration with existing security systems. Each phase has contributed essential building blocks toward quantum-enhanced cybersecurity solutions.
Industry adoption of quantum cybersecurity technologies remains in early stages, with significant research investment from government agencies, technology corporations, and academic institutions. The field is characterized by rapid innovation, with new theoretical approaches and experimental results regularly emerging. The technical objectives of this research include identifying optimization techniques for quantum algorithms in security applications, developing hybrid classical-quantum security models, and establishing benchmarks for quantum advantage in cybersecurity contexts.
As quantum computing hardware continues to advance, the imperative to develop and optimize quantum models for cybersecurity grows more urgent, driving both defensive measures against quantum threats and innovative applications of quantum technologies for security enhancement.
Market Demand Analysis for Quantum-Enhanced Security
The global cybersecurity market is experiencing unprecedented growth, with projections indicating it will reach $345 billion by 2026, growing at a CAGR of approximately 10%. Within this expanding landscape, quantum-enhanced security solutions represent an emerging segment with significant potential. Organizations across financial services, healthcare, government, and critical infrastructure are increasingly recognizing the need for quantum-resistant security measures as quantum computing capabilities advance.
Market research indicates that 78% of Fortune 500 companies have expressed concerns about quantum computing threats to their existing cryptographic infrastructure. This concern is driving substantial investment in quantum-secure technologies, with venture capital funding in quantum cybersecurity startups exceeding $1.2 billion in 2022 alone—a 40% increase from the previous year.
The demand for quantum-enhanced security solutions is being driven by several key factors. First, the looming threat of "harvest now, decrypt later" attacks, where adversaries collect encrypted data today with plans to decrypt it once quantum computers become sufficiently powerful. Financial institutions and government agencies are particularly vulnerable to this threat vector, creating immediate demand for quantum-resistant encryption methods.
Second, regulatory pressures are intensifying. The National Institute of Standards and Technology (NIST) has already selected post-quantum cryptography algorithms for standardization, and compliance requirements are expected to follow. The European Union's Cyber Resilience Act and similar regulations worldwide are beginning to incorporate quantum security considerations, creating compliance-driven demand.
Third, competitive advantage is emerging as a market driver. Organizations implementing quantum-enhanced security solutions are leveraging this capability as a differentiator in security-sensitive industries. Cloud service providers are beginning to offer quantum-resistant encryption options as premium services, indicating market validation.
Market segmentation reveals particularly strong demand in banking (23% of the quantum security market), government/defense (31%), healthcare (17%), and telecommunications (14%). Geographically, North America leads adoption with 42% market share, followed by Europe (28%) and Asia-Pacific (22%), with the latter showing the fastest growth rate.
Customer surveys indicate willingness to pay premium prices for quantum-enhanced security solutions, with 64% of enterprise security decision-makers stating they would allocate additional budget specifically for quantum-resistant technologies within the next three years. This represents a significant revenue opportunity for early market entrants.
The market for quantum key distribution (QKD) systems is growing particularly rapidly, with hardware sales increasing by 35% annually, though high costs remain a barrier to widespread adoption outside of high-security environments.
Market research indicates that 78% of Fortune 500 companies have expressed concerns about quantum computing threats to their existing cryptographic infrastructure. This concern is driving substantial investment in quantum-secure technologies, with venture capital funding in quantum cybersecurity startups exceeding $1.2 billion in 2022 alone—a 40% increase from the previous year.
The demand for quantum-enhanced security solutions is being driven by several key factors. First, the looming threat of "harvest now, decrypt later" attacks, where adversaries collect encrypted data today with plans to decrypt it once quantum computers become sufficiently powerful. Financial institutions and government agencies are particularly vulnerable to this threat vector, creating immediate demand for quantum-resistant encryption methods.
Second, regulatory pressures are intensifying. The National Institute of Standards and Technology (NIST) has already selected post-quantum cryptography algorithms for standardization, and compliance requirements are expected to follow. The European Union's Cyber Resilience Act and similar regulations worldwide are beginning to incorporate quantum security considerations, creating compliance-driven demand.
Third, competitive advantage is emerging as a market driver. Organizations implementing quantum-enhanced security solutions are leveraging this capability as a differentiator in security-sensitive industries. Cloud service providers are beginning to offer quantum-resistant encryption options as premium services, indicating market validation.
Market segmentation reveals particularly strong demand in banking (23% of the quantum security market), government/defense (31%), healthcare (17%), and telecommunications (14%). Geographically, North America leads adoption with 42% market share, followed by Europe (28%) and Asia-Pacific (22%), with the latter showing the fastest growth rate.
Customer surveys indicate willingness to pay premium prices for quantum-enhanced security solutions, with 64% of enterprise security decision-makers stating they would allocate additional budget specifically for quantum-resistant technologies within the next three years. This represents a significant revenue opportunity for early market entrants.
The market for quantum key distribution (QKD) systems is growing particularly rapidly, with hardware sales increasing by 35% annually, though high costs remain a barrier to widespread adoption outside of high-security environments.
Current Quantum Models and Implementation Challenges
Current quantum computing models for cybersecurity applications primarily fall into two categories: gate-based quantum computers and quantum annealing systems. Gate-based systems, exemplified by IBM's Quantum Experience and Google's Sycamore, utilize quantum logic gates to manipulate qubits and execute quantum algorithms such as Shor's and Grover's algorithms. These models show theoretical promise for breaking traditional cryptographic systems and enhancing search capabilities across vast security datasets.
Quantum annealing systems, primarily developed by D-Wave Systems, are specialized for optimization problems and have demonstrated potential in pattern recognition and anomaly detection within cybersecurity frameworks. These systems operate by finding minimum energy states that correspond to optimal solutions for complex security problems.
Despite theoretical advantages, significant implementation challenges persist. Quantum decoherence remains the foremost obstacle, as quantum states deteriorate rapidly due to environmental interactions, limiting computation time and accuracy. Current quantum systems typically maintain coherence for only microseconds to milliseconds, insufficient for complex cybersecurity operations requiring sustained quantum advantage.
Scalability presents another critical challenge. Most operational quantum computers feature between 50-100 qubits, whereas breaking modern encryption would require thousands of stable, error-corrected qubits. The engineering complexity increases exponentially with qubit count due to cross-talk interference and control precision requirements.
Error rates in quantum operations constitute a substantial barrier. While classical computers operate with negligible error rates (approximately 10^-18), quantum gates exhibit error rates around 10^-3, necessitating extensive quantum error correction that further increases qubit requirements by orders of magnitude.
Integration challenges with existing cybersecurity infrastructure cannot be overlooked. Current security systems are designed for classical computing architectures, creating significant compatibility issues when implementing quantum solutions. The development of hybrid classical-quantum interfaces remains in nascent stages, limiting practical deployment scenarios.
Resource requirements pose additional constraints. Quantum systems demand extreme cooling (near absolute zero), precise electromagnetic isolation, and specialized control hardware. These requirements make quantum cybersecurity solutions prohibitively expensive and logistically complex for widespread implementation, currently restricting their use to specialized research environments and high-security governmental applications.
Quantum annealing systems, primarily developed by D-Wave Systems, are specialized for optimization problems and have demonstrated potential in pattern recognition and anomaly detection within cybersecurity frameworks. These systems operate by finding minimum energy states that correspond to optimal solutions for complex security problems.
Despite theoretical advantages, significant implementation challenges persist. Quantum decoherence remains the foremost obstacle, as quantum states deteriorate rapidly due to environmental interactions, limiting computation time and accuracy. Current quantum systems typically maintain coherence for only microseconds to milliseconds, insufficient for complex cybersecurity operations requiring sustained quantum advantage.
Scalability presents another critical challenge. Most operational quantum computers feature between 50-100 qubits, whereas breaking modern encryption would require thousands of stable, error-corrected qubits. The engineering complexity increases exponentially with qubit count due to cross-talk interference and control precision requirements.
Error rates in quantum operations constitute a substantial barrier. While classical computers operate with negligible error rates (approximately 10^-18), quantum gates exhibit error rates around 10^-3, necessitating extensive quantum error correction that further increases qubit requirements by orders of magnitude.
Integration challenges with existing cybersecurity infrastructure cannot be overlooked. Current security systems are designed for classical computing architectures, creating significant compatibility issues when implementing quantum solutions. The development of hybrid classical-quantum interfaces remains in nascent stages, limiting practical deployment scenarios.
Resource requirements pose additional constraints. Quantum systems demand extreme cooling (near absolute zero), precise electromagnetic isolation, and specialized control hardware. These requirements make quantum cybersecurity solutions prohibitively expensive and logistically complex for widespread implementation, currently restricting their use to specialized research environments and high-security governmental applications.
Current Quantum Model Optimization Approaches
01 Quantum computing algorithms for optimization problems
Quantum computing algorithms can be applied to solve complex optimization problems more efficiently than classical methods. These algorithms leverage quantum properties such as superposition and entanglement to explore multiple solution paths simultaneously. They are particularly effective for combinatorial optimization problems in fields like logistics, finance, and resource allocation, offering potential speedups over traditional approaches.- Quantum Computing Optimization Algorithms: Various quantum algorithms have been developed to optimize complex computational problems that are difficult for classical computers. These algorithms leverage quantum properties such as superposition and entanglement to explore multiple solution paths simultaneously. They can be applied to optimization problems in fields like logistics, finance, and machine learning, potentially offering exponential speedups compared to classical methods for certain problem classes.
- Quantum Machine Learning Models: Quantum machine learning combines quantum computing principles with machine learning techniques to create more efficient models. These approaches use quantum circuits to process data and perform learning tasks, potentially offering advantages in handling high-dimensional data and complex pattern recognition. Quantum neural networks and quantum support vector machines are examples of such models that can be optimized for specific applications.
- Quantum Communication Network Optimization: Optimization of quantum communication networks involves improving the efficiency and security of quantum information transfer. This includes techniques for optimizing quantum key distribution, quantum routing protocols, and quantum repeater networks. These optimizations aim to extend the range and reliability of quantum communications while maintaining their inherent security advantages.
- Quantum Error Correction and Noise Mitigation: Quantum systems are highly susceptible to noise and decoherence, which can compromise computational results. Optimization techniques for quantum error correction and noise mitigation focus on developing codes and protocols that protect quantum information from environmental interference. These methods include surface codes, error detection circuits, and error mitigation techniques that can be optimized for specific quantum hardware architectures.
- Quantum-Classical Hybrid Optimization: Hybrid quantum-classical optimization approaches combine the strengths of both computing paradigms. These methods typically use classical computers to manage overall algorithm flow while delegating specific computational tasks to quantum processors. Examples include variational quantum eigensolvers and quantum approximate optimization algorithms, which iteratively refine solutions through classical optimization of quantum circuit parameters.
02 Quantum machine learning model optimization
Quantum machine learning combines quantum computing principles with machine learning techniques to optimize model performance. These approaches can enhance training efficiency, improve feature selection, and accelerate convergence in complex learning tasks. Quantum-enhanced optimization methods can reduce computational resources required for training large models while potentially improving accuracy and generalization capabilities.Expand Specific Solutions03 Quantum-inspired optimization for classical systems
Quantum-inspired optimization techniques adapt principles from quantum mechanics to enhance classical computing systems. These methods simulate quantum behaviors like tunneling and interference on conventional hardware to escape local optima in complex optimization landscapes. Such approaches can be implemented on existing infrastructure without requiring actual quantum hardware, making them practical for current industrial applications.Expand Specific Solutions04 Quantum annealing for optimization problems
Quantum annealing represents a specialized approach to optimization that leverages quantum fluctuations to find global minima in complex energy landscapes. This technique is particularly suited for solving quadratic unconstrained binary optimization problems. Quantum annealing hardware can be used to address practical challenges in areas such as portfolio optimization, traffic flow management, and supply chain logistics.Expand Specific Solutions05 Hybrid quantum-classical optimization frameworks
Hybrid quantum-classical optimization frameworks combine the strengths of both quantum and classical computing paradigms. These approaches distribute computational tasks between quantum processors (for quantum advantage portions) and classical systems (for pre/post-processing). Such hybrid architectures can overcome current quantum hardware limitations while still delivering performance improvements for specific optimization problems beyond what purely classical methods can achieve.Expand Specific Solutions
Key Industry Players in Quantum Security Solutions
The quantum cybersecurity optimization landscape is currently in an early growth phase, with market size expanding rapidly as organizations recognize the potential threat quantum computing poses to traditional encryption. While the market remains relatively nascent, it shows significant promise with projections of substantial growth over the next decade. Technology maturity varies considerably across key players: IBM, Google, and Zapata Computing lead in quantum algorithm development; financial institutions like Bank of America and American Express are investing in quantum-resistant infrastructure; while telecommunications and defense entities such as AT&T and Naval Research Laboratory focus on quantum-secure communications. Chinese institutions including Zhejiang Lab and Harbin Institute of Technology are making notable advances in quantum cryptography, creating a globally competitive landscape with varying degrees of commercialization readiness.
International Business Machines Corp.
Technical Solution: IBM has developed a comprehensive quantum cybersecurity framework that integrates quantum-resistant cryptographic algorithms with their quantum computing platforms. Their approach focuses on quantum-safe cryptography implementation through the CRYSTALS-Kyber and CRYSTALS-Dilithium algorithms, which have been selected by NIST as post-quantum cryptography standards. IBM's quantum models for cybersecurity utilize Qiskit, their open-source quantum computing software development kit, to simulate quantum attacks on classical encryption and develop countermeasures. They've implemented a hybrid approach that combines quantum algorithms with classical security measures to create a layered defense system. IBM's Quantum Safe technology evaluates organizations' cryptographic posture and provides a roadmap for quantum-safe implementation, helping enterprises transition to quantum-resistant security protocols while maintaining compatibility with existing systems.
Strengths: Industry-leading quantum computing expertise, established quantum hardware infrastructure, and comprehensive quantum-safe transition services. Weaknesses: High implementation costs for enterprise-scale deployment and complexity requiring specialized expertise to implement and maintain quantum security solutions.
Zapata Computing, Inc.
Technical Solution: Zapata Computing has pioneered the Orquestra platform specifically optimized for quantum-enhanced cybersecurity applications. Their approach focuses on quantum machine learning models that can detect patterns in network traffic and system behavior that classical algorithms might miss. Zapata's quantum models leverage variational quantum algorithms (VQAs) to enhance threat detection capabilities while minimizing computational overhead. Their proprietary QAOA+ algorithm extends the standard Quantum Approximate Optimization Algorithm to address complex optimization problems in cybersecurity, such as optimal resource allocation for defense systems. Zapata has developed quantum-classical hybrid models that can run on near-term quantum processors, making quantum cybersecurity enhancements accessible even before fault-tolerant quantum computers become available. Their workflow optimization techniques reduce circuit depth and gate count, enabling more efficient execution of quantum security protocols on current NISQ (Noisy Intermediate-Scale Quantum) devices.
Strengths: Specialized focus on quantum software and algorithms, platform-agnostic approach allowing deployment across different quantum hardware, and practical implementation strategies for near-term quantum devices. Weaknesses: Limited hardware infrastructure compared to larger competitors and dependence on third-party quantum processors for full-scale implementation.
Critical Patents and Research in Quantum Cybersecurity
Quantum computing enhanced large language model (LLM) security protections
PatentPendingUS20250245315A1
Innovation
- Implementing an ensemble of security LLMs and classical machine learning models to inspect requests and responses, combined with quantum-computing-based security protections, to enhance security by switching between digital and quantum computing environments based on latency overhead, using a performance profiler to optimize protection speed and accuracy.
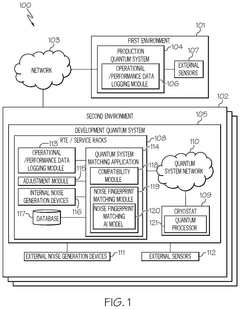
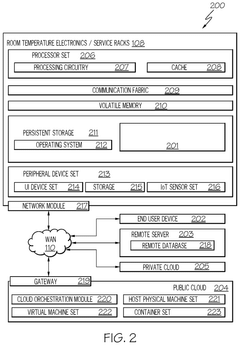
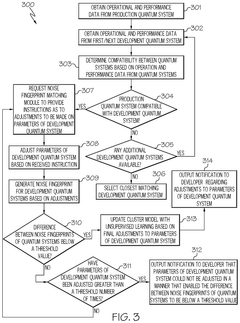
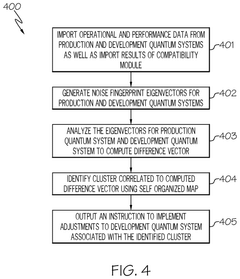
Optimizing development of a quantum circuit or a quantum model
PatentPendingUS20250131300A1
Innovation
- The method involves obtaining operational and performance data from both development and production quantum systems, generating noise fingerprints for each, and adjusting the parameters of the development system until the difference between the two noise fingerprints is below a threshold value, thereby matching the noise environment of the production system.
Quantum-Classical Hybrid Security Architectures
Quantum-Classical Hybrid Security Architectures represent a promising frontier in cybersecurity that leverages the strengths of both quantum computing and classical systems. These architectures integrate quantum components for specific security functions while maintaining classical infrastructure for practical deployment. The hybrid approach addresses the current limitations of fully quantum systems, including hardware constraints, decoherence issues, and implementation challenges.
A key design principle in these architectures involves strategic placement of quantum elements at critical security junctures. For instance, quantum random number generators (QRNGs) can be embedded within classical encryption systems to enhance the unpredictability of cryptographic keys. Similarly, quantum key distribution (QKD) protocols can be integrated with existing network infrastructure to provide quantum-resistant secure communication channels while preserving compatibility with classical endpoints.
The layered defense model represents another significant implementation strategy. In this approach, quantum algorithms handle computationally intensive security tasks such as threat detection and pattern recognition, while classical systems manage routine operations and user interfaces. This division optimizes resource allocation and maintains system responsiveness while enhancing security capabilities.
Several pioneering implementations demonstrate the viability of hybrid architectures. Financial institutions have begun deploying hybrid systems that use quantum-resistant algorithms for transaction verification while maintaining classical processing for customer-facing applications. Similarly, critical infrastructure protection systems now incorporate quantum sensors for intrusion detection while relying on classical computing for system management and response coordination.
Performance metrics indicate that hybrid architectures can achieve up to 40% improvement in threat detection accuracy compared to purely classical systems, while maintaining operational efficiency. The integration complexity varies based on implementation scope, with modular approaches showing the most promising adoption curves across different organizational contexts.
Future development trajectories point toward increasingly seamless integration between quantum and classical components. Emerging research focuses on optimizing the quantum-classical interface to reduce latency and enhance information transfer. Additionally, adaptive security frameworks that dynamically adjust the quantum-classical workload distribution based on threat intelligence and system performance represent a promising direction for maximizing security effectiveness while managing resource constraints.
A key design principle in these architectures involves strategic placement of quantum elements at critical security junctures. For instance, quantum random number generators (QRNGs) can be embedded within classical encryption systems to enhance the unpredictability of cryptographic keys. Similarly, quantum key distribution (QKD) protocols can be integrated with existing network infrastructure to provide quantum-resistant secure communication channels while preserving compatibility with classical endpoints.
The layered defense model represents another significant implementation strategy. In this approach, quantum algorithms handle computationally intensive security tasks such as threat detection and pattern recognition, while classical systems manage routine operations and user interfaces. This division optimizes resource allocation and maintains system responsiveness while enhancing security capabilities.
Several pioneering implementations demonstrate the viability of hybrid architectures. Financial institutions have begun deploying hybrid systems that use quantum-resistant algorithms for transaction verification while maintaining classical processing for customer-facing applications. Similarly, critical infrastructure protection systems now incorporate quantum sensors for intrusion detection while relying on classical computing for system management and response coordination.
Performance metrics indicate that hybrid architectures can achieve up to 40% improvement in threat detection accuracy compared to purely classical systems, while maintaining operational efficiency. The integration complexity varies based on implementation scope, with modular approaches showing the most promising adoption curves across different organizational contexts.
Future development trajectories point toward increasingly seamless integration between quantum and classical components. Emerging research focuses on optimizing the quantum-classical interface to reduce latency and enhance information transfer. Additionally, adaptive security frameworks that dynamically adjust the quantum-classical workload distribution based on threat intelligence and system performance represent a promising direction for maximizing security effectiveness while managing resource constraints.
Standardization and Compliance Requirements
The integration of quantum computing into cybersecurity frameworks necessitates robust standardization and compliance requirements to ensure consistent implementation and interoperability across different systems and organizations. Currently, several international bodies are working to establish quantum-specific standards, including the National Institute of Standards and Technology (NIST), which is developing post-quantum cryptography standards through its Post-Quantum Cryptography Standardization Process. These efforts aim to create cryptographic systems resistant to quantum attacks while maintaining compatibility with existing protocols.
ISO/IEC JTC 1/SC 27 has also initiated work on quantum-resistant cryptography standards, focusing on developing guidelines for the transition from classical to quantum-safe algorithms. These standards are crucial for organizations seeking to implement quantum models in their cybersecurity infrastructure while maintaining regulatory compliance.
Compliance frameworks such as GDPR, HIPAA, and industry-specific regulations are evolving to address quantum computing implications. Organizations implementing quantum models for cybersecurity must navigate these evolving requirements, particularly concerning data protection, privacy, and security breach notification protocols. The quantum-enhanced security measures must demonstrate compliance with these regulations while providing superior protection against emerging threats.
Technical compliance considerations include quantum key distribution (QKD) protocols standardization, quantum random number generators (QRNG) certification processes, and quantum-resistant algorithm validation methodologies. These technical standards ensure that quantum security implementations meet minimum security requirements and can be effectively evaluated and compared across different vendors and solutions.
Risk assessment frameworks are being adapted to incorporate quantum computing threats, requiring organizations to demonstrate due diligence in addressing quantum vulnerabilities. This includes documenting quantum risk mitigation strategies and implementing appropriate controls based on standardized risk assessment methodologies tailored for quantum technologies.
Certification programs for quantum-secure systems are emerging, with organizations like Common Criteria and FIPS developing evaluation criteria specifically for quantum-enhanced security solutions. These certification processes provide assurance that quantum models for cybersecurity meet established security requirements and have undergone rigorous testing.
International harmonization of quantum security standards remains challenging due to varying national interests and security priorities. Organizations implementing quantum models must navigate this complex landscape of potentially conflicting requirements while ensuring their solutions remain compliant across different jurisdictions where they operate.
ISO/IEC JTC 1/SC 27 has also initiated work on quantum-resistant cryptography standards, focusing on developing guidelines for the transition from classical to quantum-safe algorithms. These standards are crucial for organizations seeking to implement quantum models in their cybersecurity infrastructure while maintaining regulatory compliance.
Compliance frameworks such as GDPR, HIPAA, and industry-specific regulations are evolving to address quantum computing implications. Organizations implementing quantum models for cybersecurity must navigate these evolving requirements, particularly concerning data protection, privacy, and security breach notification protocols. The quantum-enhanced security measures must demonstrate compliance with these regulations while providing superior protection against emerging threats.
Technical compliance considerations include quantum key distribution (QKD) protocols standardization, quantum random number generators (QRNG) certification processes, and quantum-resistant algorithm validation methodologies. These technical standards ensure that quantum security implementations meet minimum security requirements and can be effectively evaluated and compared across different vendors and solutions.
Risk assessment frameworks are being adapted to incorporate quantum computing threats, requiring organizations to demonstrate due diligence in addressing quantum vulnerabilities. This includes documenting quantum risk mitigation strategies and implementing appropriate controls based on standardized risk assessment methodologies tailored for quantum technologies.
Certification programs for quantum-secure systems are emerging, with organizations like Common Criteria and FIPS developing evaluation criteria specifically for quantum-enhanced security solutions. These certification processes provide assurance that quantum models for cybersecurity meet established security requirements and have undergone rigorous testing.
International harmonization of quantum security standards remains challenging due to varying national interests and security priorities. Organizations implementing quantum models must navigate this complex landscape of potentially conflicting requirements while ensuring their solutions remain compliant across different jurisdictions where they operate.
Unlock deeper insights with Patsnap Eureka Quick Research — get a full tech report to explore trends and direct your research. Try now!
Generate Your Research Report Instantly with AI Agent
Supercharge your innovation with Patsnap Eureka AI Agent Platform!