How to Streamline Configuration in Distributed Control Systems
APR 28, 20269 MIN READ
Generate Your Research Report Instantly with AI Agent
PatSnap Eureka helps you evaluate technical feasibility & market potential.
Distributed Control Systems Configuration Evolution and Objectives
Distributed Control Systems (DCS) have undergone significant transformation since their inception in the 1970s, evolving from centralized architectures to sophisticated distributed networks that manage complex industrial processes. The early DCS implementations featured proprietary hardware and software solutions with limited interoperability, requiring extensive manual configuration processes that were both time-consuming and error-prone.
The evolution of DCS configuration has been marked by several key technological shifts. Initially, configuration involved hardwired connections and basic programming interfaces that required specialized expertise. The introduction of graphical user interfaces in the 1980s simplified configuration tasks, while the adoption of standardized communication protocols like Foundation Fieldbus and HART in the 1990s enhanced system integration capabilities.
Modern DCS configuration has embraced object-oriented programming paradigms and model-based engineering approaches. The integration of Industrial Internet of Things (IoT) technologies and cloud computing has further revolutionized configuration methodologies, enabling remote configuration management and real-time system optimization. Contemporary systems leverage artificial intelligence and machine learning algorithms to automate routine configuration tasks and predict optimal parameter settings.
The primary objective of streamlining DCS configuration centers on reducing engineering time and minimizing human errors during system setup and maintenance. Organizations seek to achieve faster project delivery cycles while maintaining high reliability standards and ensuring seamless integration with existing infrastructure. Cost reduction remains a critical driver, as traditional configuration approaches often require extensive engineering resources and specialized training.
Enhanced system flexibility represents another fundamental objective, enabling rapid adaptation to changing process requirements and market demands. Modern DCS configuration aims to support plug-and-play device integration, automatic device recognition, and self-configuring network topologies. These capabilities reduce dependency on specialized personnel and accelerate system commissioning phases.
Standardization and interoperability objectives focus on eliminating vendor lock-in scenarios and promoting open architecture designs. The industry increasingly demands configuration tools that support multiple vendor platforms and enable seamless data exchange between different system components. This evolution toward standardized configuration frameworks facilitates easier system upgrades and reduces long-term maintenance costs.
Future configuration objectives emphasize predictive maintenance capabilities and autonomous system optimization. Advanced DCS configurations will incorporate digital twin technologies and simulation-based validation tools, enabling virtual commissioning and reducing physical testing requirements. These technological advancements promise to transform DCS configuration from reactive maintenance approaches to proactive, intelligence-driven system management paradigms.
The evolution of DCS configuration has been marked by several key technological shifts. Initially, configuration involved hardwired connections and basic programming interfaces that required specialized expertise. The introduction of graphical user interfaces in the 1980s simplified configuration tasks, while the adoption of standardized communication protocols like Foundation Fieldbus and HART in the 1990s enhanced system integration capabilities.
Modern DCS configuration has embraced object-oriented programming paradigms and model-based engineering approaches. The integration of Industrial Internet of Things (IoT) technologies and cloud computing has further revolutionized configuration methodologies, enabling remote configuration management and real-time system optimization. Contemporary systems leverage artificial intelligence and machine learning algorithms to automate routine configuration tasks and predict optimal parameter settings.
The primary objective of streamlining DCS configuration centers on reducing engineering time and minimizing human errors during system setup and maintenance. Organizations seek to achieve faster project delivery cycles while maintaining high reliability standards and ensuring seamless integration with existing infrastructure. Cost reduction remains a critical driver, as traditional configuration approaches often require extensive engineering resources and specialized training.
Enhanced system flexibility represents another fundamental objective, enabling rapid adaptation to changing process requirements and market demands. Modern DCS configuration aims to support plug-and-play device integration, automatic device recognition, and self-configuring network topologies. These capabilities reduce dependency on specialized personnel and accelerate system commissioning phases.
Standardization and interoperability objectives focus on eliminating vendor lock-in scenarios and promoting open architecture designs. The industry increasingly demands configuration tools that support multiple vendor platforms and enable seamless data exchange between different system components. This evolution toward standardized configuration frameworks facilitates easier system upgrades and reduces long-term maintenance costs.
Future configuration objectives emphasize predictive maintenance capabilities and autonomous system optimization. Advanced DCS configurations will incorporate digital twin technologies and simulation-based validation tools, enabling virtual commissioning and reducing physical testing requirements. These technological advancements promise to transform DCS configuration from reactive maintenance approaches to proactive, intelligence-driven system management paradigms.
Market Demand for Streamlined DCS Configuration Solutions
The global distributed control systems market is experiencing unprecedented growth driven by increasing industrial automation demands and the need for enhanced operational efficiency. Manufacturing industries, particularly in process sectors such as oil and gas, chemicals, pharmaceuticals, and power generation, are actively seeking solutions to reduce configuration complexity and accelerate system deployment timelines.
Traditional DCS configuration processes often require specialized expertise and extensive manual programming, creating significant bottlenecks in project implementation. Organizations face mounting pressure to reduce engineering costs while maintaining system reliability and performance standards. This challenge has intensified as industrial facilities become more complex and interconnected, requiring sophisticated control strategies that can adapt to dynamic operational requirements.
The emergence of Industry 4.0 initiatives has further amplified demand for streamlined configuration solutions. Companies are pursuing digital transformation strategies that emphasize rapid deployment, reduced commissioning time, and improved system maintainability. The ability to quickly reconfigure control systems in response to changing production requirements has become a critical competitive advantage in today's fast-paced industrial environment.
Market research indicates strong adoption interest in automated configuration tools, template-based engineering approaches, and model-driven development methodologies. End users consistently prioritize solutions that can reduce engineering hours, minimize human error risks, and enable faster time-to-market for new production lines or facility expansions.
The COVID-19 pandemic has accelerated remote work adoption, creating additional demand for configuration solutions that support distributed engineering teams and remote commissioning capabilities. Organizations now require tools that enable collaborative configuration development while maintaining security and version control standards.
Small and medium-sized enterprises represent an emerging market segment, as they seek cost-effective alternatives to traditional custom engineering approaches. These organizations often lack specialized DCS expertise and require intuitive configuration tools that can be operated by general automation personnel rather than dedicated control system specialists.
Traditional DCS configuration processes often require specialized expertise and extensive manual programming, creating significant bottlenecks in project implementation. Organizations face mounting pressure to reduce engineering costs while maintaining system reliability and performance standards. This challenge has intensified as industrial facilities become more complex and interconnected, requiring sophisticated control strategies that can adapt to dynamic operational requirements.
The emergence of Industry 4.0 initiatives has further amplified demand for streamlined configuration solutions. Companies are pursuing digital transformation strategies that emphasize rapid deployment, reduced commissioning time, and improved system maintainability. The ability to quickly reconfigure control systems in response to changing production requirements has become a critical competitive advantage in today's fast-paced industrial environment.
Market research indicates strong adoption interest in automated configuration tools, template-based engineering approaches, and model-driven development methodologies. End users consistently prioritize solutions that can reduce engineering hours, minimize human error risks, and enable faster time-to-market for new production lines or facility expansions.
The COVID-19 pandemic has accelerated remote work adoption, creating additional demand for configuration solutions that support distributed engineering teams and remote commissioning capabilities. Organizations now require tools that enable collaborative configuration development while maintaining security and version control standards.
Small and medium-sized enterprises represent an emerging market segment, as they seek cost-effective alternatives to traditional custom engineering approaches. These organizations often lack specialized DCS expertise and require intuitive configuration tools that can be operated by general automation personnel rather than dedicated control system specialists.
Current DCS Configuration Challenges and Complexity Issues
Distributed Control Systems face significant configuration complexity that stems from their inherently distributed architecture and multi-layered operational requirements. Traditional DCS configurations involve managing thousands of control loops, input/output points, and communication protocols across geographically dispersed field devices, controllers, and operator stations. This complexity is compounded by the need to maintain consistency across multiple engineering workstations while ensuring real-time performance and safety compliance.
The heterogeneous nature of modern industrial environments presents substantial configuration challenges. DCS implementations must accommodate diverse field devices from multiple vendors, each with unique communication protocols, data formats, and configuration parameters. Legacy systems integration further complicates this landscape, as engineers must bridge decades-old proprietary protocols with modern industrial Ethernet standards while maintaining operational continuity.
Configuration management becomes increasingly problematic as system scale expands. Large-scale DCS deployments can involve hundreds of thousands of tags, complex interlocking sequences, and intricate alarm management hierarchies. Manual configuration processes are prone to human error, version control issues, and inconsistent implementation practices across different engineering teams. The lack of standardized configuration templates and reusable components often results in duplicated effort and increased project timelines.
Version control and change management represent critical pain points in current DCS configuration workflows. Multiple engineers working simultaneously on different system aspects often encounter conflicts when merging configuration changes. The absence of robust configuration versioning tools leads to difficulties in tracking modifications, rolling back problematic changes, and maintaining audit trails for regulatory compliance requirements.
Documentation and knowledge transfer challenges further exacerbate configuration complexity. DCS configurations often rely heavily on tribal knowledge and undocumented design decisions, making system maintenance and future modifications increasingly difficult. The steep learning curve associated with proprietary configuration tools creates bottlenecks in project execution and limits the available pool of qualified engineering resources.
Validation and testing of complex DCS configurations present additional operational challenges. Comprehensive testing requires sophisticated simulation environments that accurately replicate field conditions, yet many organizations lack adequate testing infrastructure. This limitation often results in configuration errors being discovered during commissioning phases, leading to costly project delays and potential safety risks.
The heterogeneous nature of modern industrial environments presents substantial configuration challenges. DCS implementations must accommodate diverse field devices from multiple vendors, each with unique communication protocols, data formats, and configuration parameters. Legacy systems integration further complicates this landscape, as engineers must bridge decades-old proprietary protocols with modern industrial Ethernet standards while maintaining operational continuity.
Configuration management becomes increasingly problematic as system scale expands. Large-scale DCS deployments can involve hundreds of thousands of tags, complex interlocking sequences, and intricate alarm management hierarchies. Manual configuration processes are prone to human error, version control issues, and inconsistent implementation practices across different engineering teams. The lack of standardized configuration templates and reusable components often results in duplicated effort and increased project timelines.
Version control and change management represent critical pain points in current DCS configuration workflows. Multiple engineers working simultaneously on different system aspects often encounter conflicts when merging configuration changes. The absence of robust configuration versioning tools leads to difficulties in tracking modifications, rolling back problematic changes, and maintaining audit trails for regulatory compliance requirements.
Documentation and knowledge transfer challenges further exacerbate configuration complexity. DCS configurations often rely heavily on tribal knowledge and undocumented design decisions, making system maintenance and future modifications increasingly difficult. The steep learning curve associated with proprietary configuration tools creates bottlenecks in project execution and limits the available pool of qualified engineering resources.
Validation and testing of complex DCS configurations present additional operational challenges. Comprehensive testing requires sophisticated simulation environments that accurately replicate field conditions, yet many organizations lack adequate testing infrastructure. This limitation often results in configuration errors being discovered during commissioning phases, leading to costly project delays and potential safety risks.
Existing DCS Configuration Streamlining Solutions
01 Network architecture and communication protocols for distributed control systems
This category focuses on the fundamental network infrastructure and communication protocols that enable distributed control systems to operate effectively. It includes methods for establishing reliable communication channels between distributed nodes, implementing various network topologies, and ensuring data integrity across the system. The approaches cover both wired and wireless communication methods, protocol standardization, and network redundancy mechanisms to maintain system reliability.- Network architecture and communication protocols for distributed control systems: Distributed control systems require robust network architectures and communication protocols to enable seamless data exchange between distributed nodes. These systems implement various communication standards and protocols to ensure reliable connectivity, real-time data transmission, and fault-tolerant operation across multiple control units and field devices.
- Configuration management and system integration: Configuration management involves the systematic setup and integration of distributed control system components, including hardware configuration, software parameterization, and system commissioning. This encompasses the coordination of multiple subsystems, device mapping, and the establishment of control hierarchies to ensure proper system functionality and performance optimization.
- Real-time monitoring and data acquisition systems: Real-time monitoring capabilities are essential for distributed control systems to collect, process, and analyze data from various sensors and control points. These systems implement advanced data acquisition techniques, signal processing algorithms, and monitoring interfaces to provide operators with comprehensive system visibility and enable timely decision-making.
- Security and access control mechanisms: Security frameworks for distributed control systems include authentication protocols, encryption methods, and access control mechanisms to protect against cyber threats and unauthorized access. These security measures ensure system integrity, data confidentiality, and operational safety while maintaining compliance with industrial security standards and regulations.
- Fault tolerance and redundancy strategies: Fault tolerance mechanisms ensure continuous operation of distributed control systems through redundancy strategies, backup systems, and automatic failover capabilities. These approaches include redundant hardware configurations, distributed processing architectures, and recovery protocols that maintain system availability and reliability even during component failures or network disruptions.
02 Real-time data processing and synchronization mechanisms
This encompasses techniques for processing and synchronizing data in real-time across distributed control nodes. It includes algorithms for time synchronization, data buffering, and ensuring consistent system states across all distributed components. The methods address latency management, data prioritization, and maintaining temporal coherence in distributed environments where multiple control units must coordinate their actions based on shared information.Expand Specific Solutions03 Fault tolerance and redundancy management
This category covers strategies for implementing fault-tolerant distributed control systems that can continue operating despite component failures. It includes redundancy schemes, automatic failover mechanisms, and error detection and recovery protocols. The approaches ensure system reliability through backup systems, distributed backup strategies, and graceful degradation methods that maintain critical functionality even when parts of the system fail.Expand Specific Solutions04 Configuration management and system deployment
This focuses on methods for configuring, deploying, and managing distributed control systems across multiple nodes and locations. It includes automated configuration tools, version control for distributed systems, and dynamic reconfiguration capabilities. The techniques address system scalability, configuration consistency across nodes, and methods for updating system parameters without disrupting ongoing operations.Expand Specific Solutions05 Security and access control in distributed environments
This category addresses security measures and access control mechanisms specifically designed for distributed control systems. It includes authentication protocols, encryption methods for distributed communications, and authorization frameworks that work across multiple system nodes. The approaches cover protection against cyber threats, secure key management, and ensuring data confidentiality and integrity in distributed control environments.Expand Specific Solutions
Key Players in DCS and Configuration Management Industry
The distributed control systems configuration market is experiencing significant growth driven by increasing industrial automation demands and digital transformation initiatives. The industry is in a mature expansion phase, with established players like Siemens AG, ABB Ltd., and Rockwell Automation Technologies dominating through comprehensive automation portfolios. Technology giants IBM and Microsoft Technology Licensing LLC are advancing cloud-based configuration solutions, while specialized firms like Sedai Inc. focus on autonomous management platforms. Chinese companies including Huawei Technologies, HollySys Automation, and Guodian Nanjing Automation are rapidly developing competitive solutions, particularly in process automation. The technology maturity varies significantly - traditional hardware-centric approaches from Siemens and ABB are well-established, while AI-driven configuration tools from newer entrants like Sedai represent emerging capabilities. Market consolidation continues as companies seek integrated solutions spanning hardware, software, and services to streamline complex distributed system configurations.
Siemens AG
Technical Solution: Siemens implements a comprehensive distributed control system configuration approach through their SIMATIC PCS 7 and TIA Portal platforms. Their solution features centralized engineering with distributed execution, utilizing standardized function blocks and libraries to streamline configuration processes. The TIA Portal provides unified engineering environment that enables seamless integration of hardware and software components across distributed nodes. Their approach incorporates automated configuration validation, version control, and change management capabilities. The system supports hierarchical configuration structures with inheritance mechanisms, allowing engineers to define templates at higher levels that automatically propagate to lower-level components. This significantly reduces configuration time and ensures consistency across distributed control points while maintaining flexibility for local adaptations.
Strengths: Industry-leading integration capabilities, comprehensive toolset, strong standardization. Weaknesses: High complexity for smaller systems, significant learning curve, expensive licensing costs.
ABB Ltd.
Technical Solution: ABB's distributed control system configuration strategy centers on their System 800xA platform, which employs object-oriented engineering principles and aspect objects for streamlined configuration management. Their solution utilizes a single database architecture that maintains consistency across all distributed nodes while enabling local configuration autonomy. The platform features intelligent configuration wizards, pre-configured application libraries, and automated commissioning tools that significantly reduce engineering time. ABB's approach includes dynamic configuration capabilities allowing real-time modifications without system shutdown. Their Control Builder software provides graphical configuration interfaces with drag-and-drop functionality, template-based engineering, and automatic code generation. The system supports federated architecture enabling seamless integration of legacy systems while maintaining modern configuration standards and practices.
Strengths: Excellent scalability, robust object-oriented design, strong legacy integration. Weaknesses: Complex initial setup, requires specialized training, limited third-party integration options.
Core Innovations in Automated DCS Configuration Technologies
Distributed Control System for Industrial Processes, A Method Therein, Computer Program and Computer Program Product
PatentPendingUS20240160177A1
Innovation
- A distributed control system where each runtime service manages its own configuration data with unique identifiers, avoiding central storage and unnecessary address translations by using a concatenation of Global Unique Identifiers and OPC UA node paths for configuration items, allowing services to operate independently and maintain loose coupling.
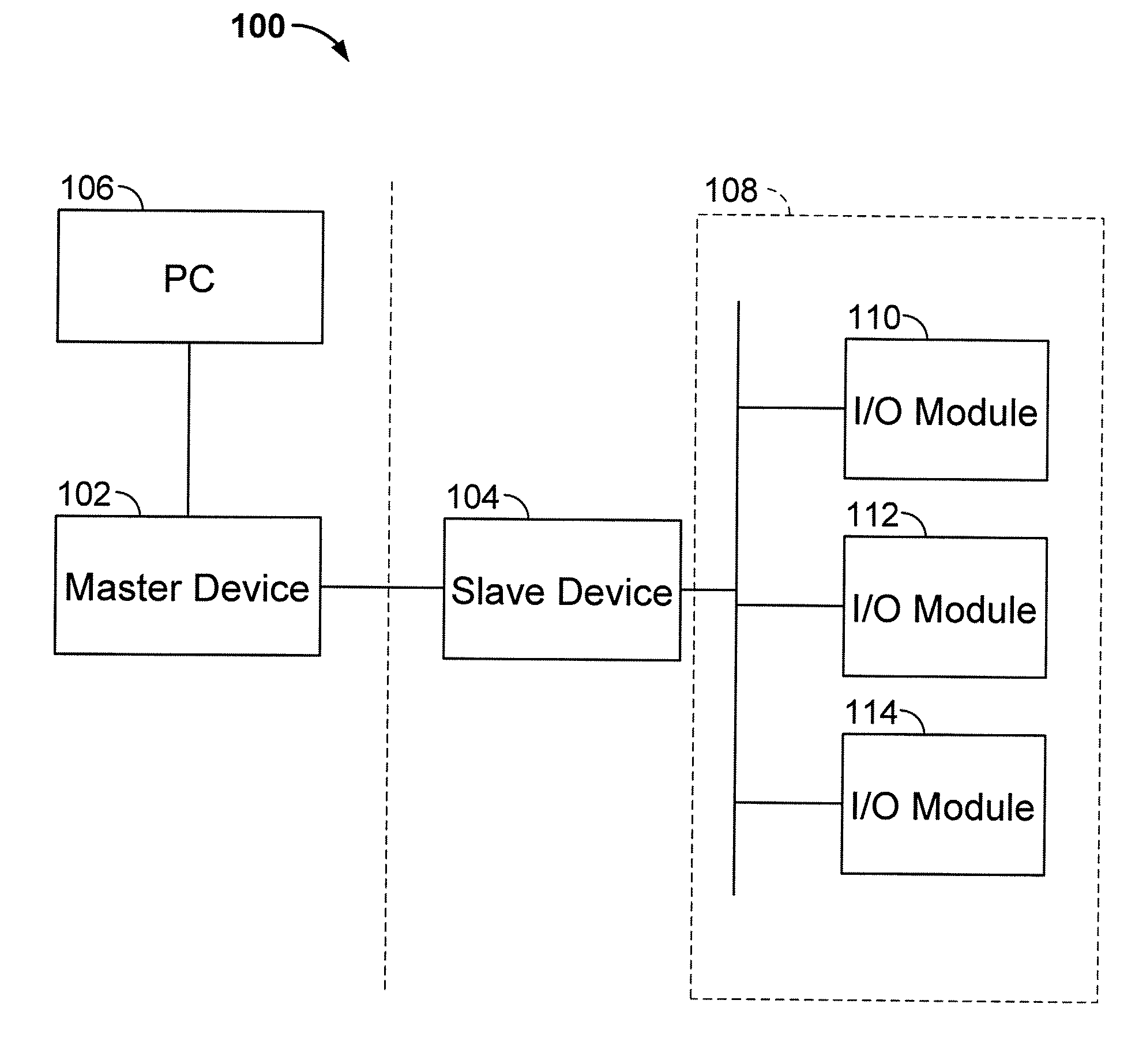
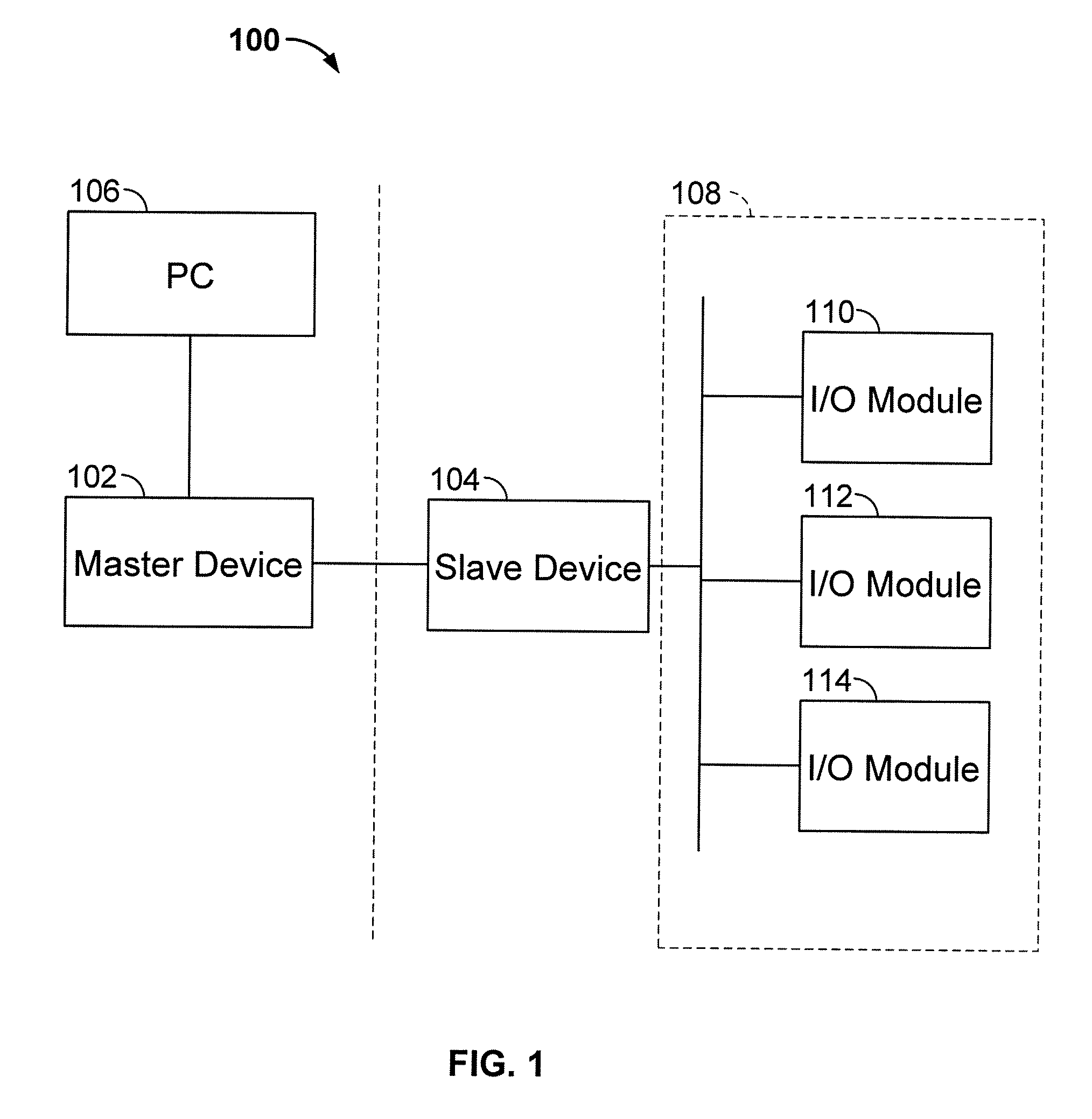
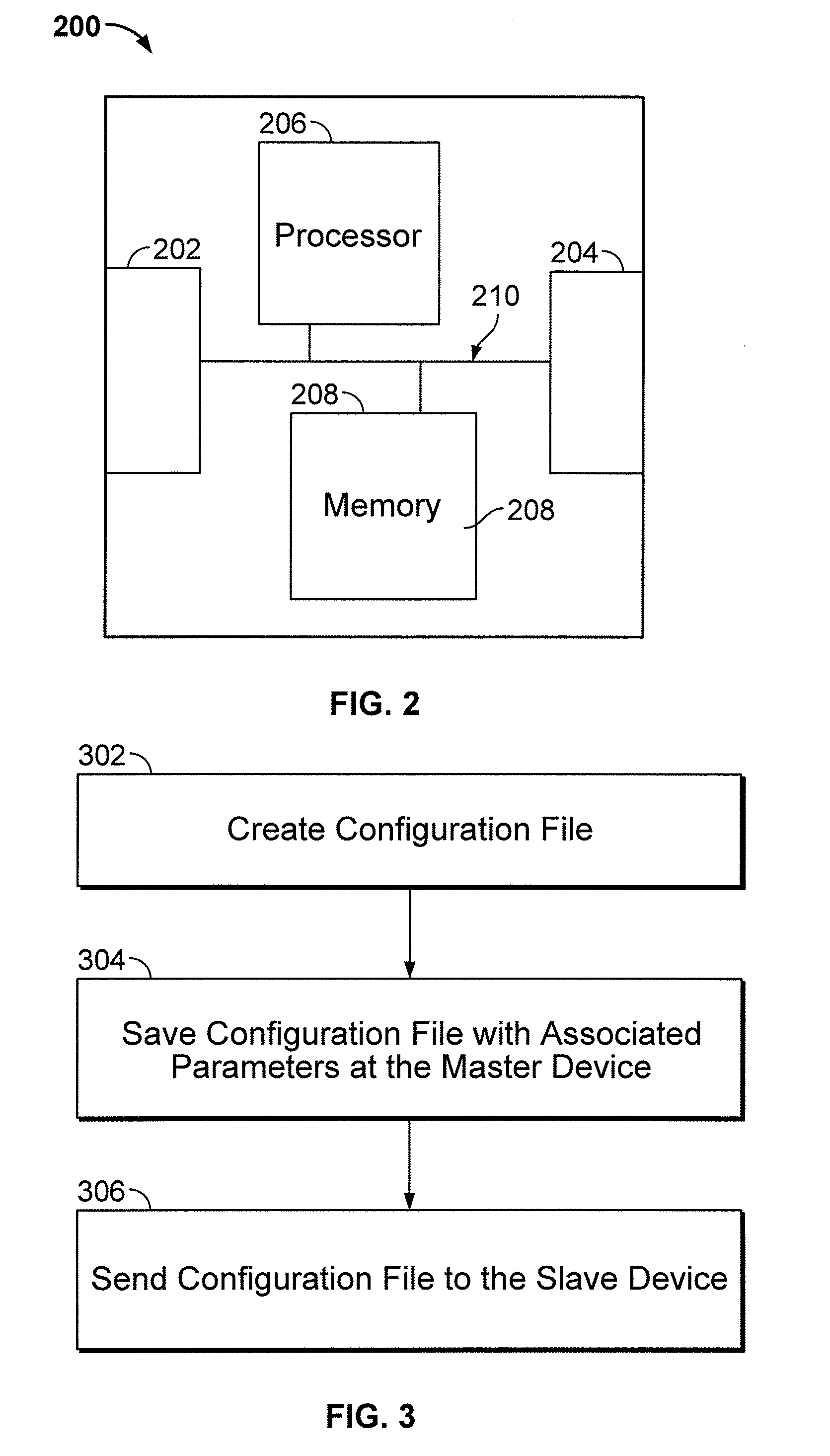
Method and Apparatus for Distributing Configuration Files in a Distributed Control System
PatentActiveUS20090172223A1
Innovation
- A method is implemented to download and apply configuration files to slave devices via the fieldbus protocol, such as CANopen, allowing for remote configuration and automatic updates by comparing file parameters between master and slave devices, ensuring that the slave devices receive the latest configuration files.
Industrial Safety Standards for DCS Configuration
Industrial safety standards play a pivotal role in ensuring the secure and reliable configuration of Distributed Control Systems across various sectors. The International Electrotechnical Commission (IEC) 61511 standard serves as the primary framework for functional safety of safety instrumented systems in the process industry, establishing comprehensive guidelines for DCS configuration practices. This standard emphasizes the importance of systematic configuration management throughout the entire system lifecycle, from initial design to decommissioning.
The ISA-99 series, now incorporated into IEC 62443, addresses cybersecurity concerns specifically related to industrial automation and control systems. These standards mandate strict configuration protocols to prevent unauthorized access and ensure system integrity. Configuration procedures must include robust authentication mechanisms, encrypted communication channels, and comprehensive audit trails to maintain compliance with these security requirements.
Safety Integrity Level (SIL) classifications under IEC 61508 directly impact DCS configuration strategies. Higher SIL ratings demand more stringent configuration validation processes, including redundant system architectures and fail-safe operational modes. Configuration engineers must implement systematic verification procedures to ensure that safety functions operate within specified probability of failure parameters.
The NIST Cybersecurity Framework provides additional guidance for DCS configuration security, emphasizing the need for continuous monitoring and incident response capabilities. Configuration management must incorporate real-time threat detection and automated response mechanisms to address emerging cybersecurity challenges in industrial environments.
Compliance with these standards requires organizations to establish formal configuration change management processes, including impact assessment procedures, testing protocols, and rollback capabilities. Documentation requirements mandate comprehensive configuration baselines, change logs, and validation records to support regulatory audits and safety assessments. These standardized approaches ensure that DCS configurations maintain operational safety while enabling efficient system management and reduced configuration complexity across distributed industrial networks.
The ISA-99 series, now incorporated into IEC 62443, addresses cybersecurity concerns specifically related to industrial automation and control systems. These standards mandate strict configuration protocols to prevent unauthorized access and ensure system integrity. Configuration procedures must include robust authentication mechanisms, encrypted communication channels, and comprehensive audit trails to maintain compliance with these security requirements.
Safety Integrity Level (SIL) classifications under IEC 61508 directly impact DCS configuration strategies. Higher SIL ratings demand more stringent configuration validation processes, including redundant system architectures and fail-safe operational modes. Configuration engineers must implement systematic verification procedures to ensure that safety functions operate within specified probability of failure parameters.
The NIST Cybersecurity Framework provides additional guidance for DCS configuration security, emphasizing the need for continuous monitoring and incident response capabilities. Configuration management must incorporate real-time threat detection and automated response mechanisms to address emerging cybersecurity challenges in industrial environments.
Compliance with these standards requires organizations to establish formal configuration change management processes, including impact assessment procedures, testing protocols, and rollback capabilities. Documentation requirements mandate comprehensive configuration baselines, change logs, and validation records to support regulatory audits and safety assessments. These standardized approaches ensure that DCS configurations maintain operational safety while enabling efficient system management and reduced configuration complexity across distributed industrial networks.
Cybersecurity Considerations in DCS Configuration Management
Cybersecurity has emerged as a critical concern in distributed control systems configuration management, particularly as industrial networks become increasingly interconnected and exposed to external threats. The configuration management process itself presents multiple attack vectors that malicious actors can exploit to compromise system integrity, manipulate operational parameters, or disrupt industrial processes.
Authentication and authorization mechanisms form the foundation of secure DCS configuration management. Multi-factor authentication protocols must be implemented to ensure only authorized personnel can access configuration tools and databases. Role-based access control systems should define granular permissions, limiting configuration privileges based on operational responsibilities and system criticality levels.
Configuration data encryption represents another essential security layer. Both data-at-rest and data-in-transit encryption protocols protect configuration parameters from unauthorized access during storage and transmission across distributed networks. Advanced encryption standards ensure that even if configuration databases are compromised, the extracted information remains unusable without proper decryption keys.
Version control and audit trails provide crucial security oversight capabilities. Comprehensive logging systems must track all configuration changes, including timestamps, user identities, and modification details. Digital signatures and cryptographic hashing verify configuration integrity and detect unauthorized alterations. These mechanisms enable rapid identification of security breaches and facilitate forensic analysis following incidents.
Network segmentation strategies isolate configuration management systems from operational networks and external connections. Dedicated configuration networks with restricted access points minimize exposure to cyber threats while maintaining necessary connectivity for legitimate operations. Firewall configurations and intrusion detection systems monitor network traffic patterns to identify suspicious activities.
Regular security assessments and penetration testing evaluate configuration management vulnerabilities. These evaluations identify potential weaknesses in authentication systems, encryption implementations, and network architectures. Continuous monitoring tools detect anomalous configuration activities and trigger automated response protocols when security thresholds are exceeded.
Backup and recovery procedures ensure configuration data availability during security incidents. Secure, offline backup systems protect against ransomware attacks and data corruption. Recovery protocols enable rapid restoration of known-good configurations while maintaining security controls throughout the restoration process.
Authentication and authorization mechanisms form the foundation of secure DCS configuration management. Multi-factor authentication protocols must be implemented to ensure only authorized personnel can access configuration tools and databases. Role-based access control systems should define granular permissions, limiting configuration privileges based on operational responsibilities and system criticality levels.
Configuration data encryption represents another essential security layer. Both data-at-rest and data-in-transit encryption protocols protect configuration parameters from unauthorized access during storage and transmission across distributed networks. Advanced encryption standards ensure that even if configuration databases are compromised, the extracted information remains unusable without proper decryption keys.
Version control and audit trails provide crucial security oversight capabilities. Comprehensive logging systems must track all configuration changes, including timestamps, user identities, and modification details. Digital signatures and cryptographic hashing verify configuration integrity and detect unauthorized alterations. These mechanisms enable rapid identification of security breaches and facilitate forensic analysis following incidents.
Network segmentation strategies isolate configuration management systems from operational networks and external connections. Dedicated configuration networks with restricted access points minimize exposure to cyber threats while maintaining necessary connectivity for legitimate operations. Firewall configurations and intrusion detection systems monitor network traffic patterns to identify suspicious activities.
Regular security assessments and penetration testing evaluate configuration management vulnerabilities. These evaluations identify potential weaknesses in authentication systems, encryption implementations, and network architectures. Continuous monitoring tools detect anomalous configuration activities and trigger automated response protocols when security thresholds are exceeded.
Backup and recovery procedures ensure configuration data availability during security incidents. Secure, offline backup systems protect against ransomware attacks and data corruption. Recovery protocols enable rapid restoration of known-good configurations while maintaining security controls throughout the restoration process.
Unlock deeper insights with PatSnap Eureka Quick Research — get a full tech report to explore trends and direct your research. Try now!
Generate Your Research Report Instantly with AI Agent
Supercharge your innovation with PatSnap Eureka AI Agent Platform!