In-Memory Computing Accelerators For Real-Time Fraud Detection
SEP 12, 20259 MIN READ
Generate Your Research Report Instantly with AI Agent
PatSnap Eureka helps you evaluate technical feasibility & market potential.
IMC Technology Background and Objectives
In-Memory Computing (IMC) represents a paradigm shift in computing architecture that addresses the fundamental bottleneck in traditional von Neumann architectures: the separation between processing and memory units. This separation creates significant data transfer delays, commonly referred to as the "memory wall." The evolution of IMC technology can be traced back to the early 2000s, with significant acceleration in development over the past decade due to increasing demands for real-time data processing in various domains.
The financial sector, particularly fraud detection systems, has emerged as a critical application area for IMC technologies. Traditional fraud detection methods often struggle with the dual challenges of processing massive transaction volumes while maintaining strict latency requirements. As financial fraud becomes increasingly sophisticated, detection systems must analyze complex patterns across vast datasets within milliseconds to prevent fraudulent transactions before completion.
IMC accelerators specifically designed for fraud detection aim to overcome these challenges by performing computations directly within memory, dramatically reducing data movement and enabling real-time analysis. The technology evolution trend shows a clear progression from software-based optimizations toward specialized hardware solutions that integrate memory and processing capabilities.
Current IMC technologies for fraud detection leverage various architectural approaches, including resistive random-access memory (RRAM), phase-change memory (PCM), and magnetoresistive random-access memory (MRAM). These non-volatile memory technologies not only store data but can also perform certain computational tasks directly within the memory array, enabling massively parallel processing of transaction data.
The primary technical objectives for IMC accelerators in fraud detection include achieving sub-millisecond response times for complex fraud detection algorithms, reducing power consumption compared to GPU or FPGA-based solutions, and maintaining adaptability to evolving fraud patterns. Additionally, these systems must maintain compatibility with existing financial infrastructure while meeting stringent security and compliance requirements.
Recent advancements in IMC technology have demonstrated promising results, with some implementations showing 10-100x performance improvements and significant energy efficiency gains compared to conventional computing architectures. The technology roadmap suggests continued improvements in integration density, computational capabilities, and algorithm complexity support.
As financial institutions face increasing pressure to prevent fraud while maintaining seamless customer experiences, IMC accelerators represent a critical technological advancement that could fundamentally transform real-time fraud detection capabilities. The convergence of machine learning algorithms with IMC hardware further enhances the potential for detecting subtle fraud patterns that might otherwise go unnoticed in conventional systems.
The financial sector, particularly fraud detection systems, has emerged as a critical application area for IMC technologies. Traditional fraud detection methods often struggle with the dual challenges of processing massive transaction volumes while maintaining strict latency requirements. As financial fraud becomes increasingly sophisticated, detection systems must analyze complex patterns across vast datasets within milliseconds to prevent fraudulent transactions before completion.
IMC accelerators specifically designed for fraud detection aim to overcome these challenges by performing computations directly within memory, dramatically reducing data movement and enabling real-time analysis. The technology evolution trend shows a clear progression from software-based optimizations toward specialized hardware solutions that integrate memory and processing capabilities.
Current IMC technologies for fraud detection leverage various architectural approaches, including resistive random-access memory (RRAM), phase-change memory (PCM), and magnetoresistive random-access memory (MRAM). These non-volatile memory technologies not only store data but can also perform certain computational tasks directly within the memory array, enabling massively parallel processing of transaction data.
The primary technical objectives for IMC accelerators in fraud detection include achieving sub-millisecond response times for complex fraud detection algorithms, reducing power consumption compared to GPU or FPGA-based solutions, and maintaining adaptability to evolving fraud patterns. Additionally, these systems must maintain compatibility with existing financial infrastructure while meeting stringent security and compliance requirements.
Recent advancements in IMC technology have demonstrated promising results, with some implementations showing 10-100x performance improvements and significant energy efficiency gains compared to conventional computing architectures. The technology roadmap suggests continued improvements in integration density, computational capabilities, and algorithm complexity support.
As financial institutions face increasing pressure to prevent fraud while maintaining seamless customer experiences, IMC accelerators represent a critical technological advancement that could fundamentally transform real-time fraud detection capabilities. The convergence of machine learning algorithms with IMC hardware further enhances the potential for detecting subtle fraud patterns that might otherwise go unnoticed in conventional systems.
Fraud Detection Market Demand Analysis
The global fraud detection market is experiencing unprecedented growth, driven by the increasing sophistication of fraudulent activities across financial services, e-commerce, and telecommunications sectors. According to recent market research, the fraud detection and prevention market is projected to reach $65.8 billion by 2026, growing at a compound annual growth rate (CAGR) of 22.5% from 2021. This substantial growth reflects the critical need for advanced technological solutions capable of identifying and preventing fraudulent transactions in real-time.
Financial institutions face particularly acute challenges, with fraud losses estimated at $28.65 billion globally in 2021. Credit card fraud alone accounts for approximately 38.6% of all financial fraud cases, highlighting the urgent need for real-time detection capabilities. Traditional rule-based systems are increasingly inadequate against evolving fraud techniques, creating significant market demand for accelerated computing solutions that can process vast amounts of transaction data instantaneously.
E-commerce platforms represent another major market segment driving demand for in-memory computing accelerators. With global e-commerce sales exceeding $4.9 trillion in 2021 and projected to reach $7.4 trillion by 2025, merchants face growing exposure to payment fraud, account takeovers, and identity theft. The ability to analyze transaction patterns in milliseconds rather than seconds can significantly reduce false positives while improving detection rates.
Insurance companies are also emerging as key adopters of real-time fraud detection technologies. The insurance industry loses approximately $80 billion annually to fraudulent claims in the United States alone. In-memory computing accelerators enable insurers to analyze claims data against historical patterns instantaneously, potentially reducing investigation times by up to 70% and improving fraud identification accuracy by 35%.
Market research indicates that 78% of financial institutions consider real-time fraud detection capabilities as "critical" or "very important" to their operations, with 63% planning to increase investments in this area over the next three years. The primary market drivers include the growing volume of digital transactions, increasing regulatory pressure for fraud prevention, and the rising costs associated with fraud incidents.
Geographically, North America currently dominates the fraud detection market with approximately 42% market share, followed by Europe (28%) and Asia-Pacific (21%). However, the Asia-Pacific region is expected to witness the highest growth rate in the coming years due to rapid digitalization of financial services and increasing online retail penetration in countries like China, India, and Indonesia.
Financial institutions face particularly acute challenges, with fraud losses estimated at $28.65 billion globally in 2021. Credit card fraud alone accounts for approximately 38.6% of all financial fraud cases, highlighting the urgent need for real-time detection capabilities. Traditional rule-based systems are increasingly inadequate against evolving fraud techniques, creating significant market demand for accelerated computing solutions that can process vast amounts of transaction data instantaneously.
E-commerce platforms represent another major market segment driving demand for in-memory computing accelerators. With global e-commerce sales exceeding $4.9 trillion in 2021 and projected to reach $7.4 trillion by 2025, merchants face growing exposure to payment fraud, account takeovers, and identity theft. The ability to analyze transaction patterns in milliseconds rather than seconds can significantly reduce false positives while improving detection rates.
Insurance companies are also emerging as key adopters of real-time fraud detection technologies. The insurance industry loses approximately $80 billion annually to fraudulent claims in the United States alone. In-memory computing accelerators enable insurers to analyze claims data against historical patterns instantaneously, potentially reducing investigation times by up to 70% and improving fraud identification accuracy by 35%.
Market research indicates that 78% of financial institutions consider real-time fraud detection capabilities as "critical" or "very important" to their operations, with 63% planning to increase investments in this area over the next three years. The primary market drivers include the growing volume of digital transactions, increasing regulatory pressure for fraud prevention, and the rising costs associated with fraud incidents.
Geographically, North America currently dominates the fraud detection market with approximately 42% market share, followed by Europe (28%) and Asia-Pacific (21%). However, the Asia-Pacific region is expected to witness the highest growth rate in the coming years due to rapid digitalization of financial services and increasing online retail penetration in countries like China, India, and Indonesia.
Current State and Challenges of IMC Accelerators
In-Memory Computing (IMC) accelerators have emerged as a promising solution for real-time fraud detection, addressing the limitations of traditional computing architectures. Currently, IMC technology exists in various implementation forms, including resistive RAM (ReRAM), phase-change memory (PCM), and magnetic RAM (MRAM) based accelerators. These technologies enable computation directly within memory units, significantly reducing the data movement bottleneck that plagues conventional von Neumann architectures.
The global landscape of IMC development shows concentration in North America, Europe, and East Asia, with major research institutions and technology companies driving innovation. Companies like IBM, Intel, and Samsung have made substantial investments in IMC research, while startups such as Mythic and Syntiant are developing specialized IMC solutions for specific applications including fraud detection systems.
Despite promising advancements, IMC accelerators face several critical challenges. Power consumption remains a significant concern, particularly for large-scale deployment in data centers handling massive transaction volumes. Current IMC implementations struggle to balance computational efficiency with energy requirements, limiting their practical application in 24/7 fraud detection systems.
Scalability presents another major hurdle. While laboratory demonstrations have shown impressive results, scaling these technologies to handle the volume and velocity of real-world financial transaction data remains problematic. Most current IMC accelerators can process only limited data sets efficiently, whereas fraud detection systems must analyze millions of transactions simultaneously.
Accuracy and reliability issues also persist. The analog nature of many IMC computations introduces variability that can affect detection precision. This is particularly problematic for fraud detection, where false positives can disrupt legitimate transactions and false negatives can result in significant financial losses.
Integration with existing infrastructure represents a substantial challenge. Financial institutions have invested heavily in conventional computing systems, and the transition to IMC-based solutions requires significant architectural changes and software adaptations. The lack of standardized programming models and development tools for IMC further complicates adoption.
Memory endurance and device degradation remain technical obstacles. Many IMC technologies suffer from limited write endurance, which is problematic for the continuous update requirements of fraud detection models. Device-to-device variability and temporal drift in memory cell characteristics can compromise long-term reliability.
Finally, there exists a significant knowledge gap between theoretical IMC capabilities and practical implementation expertise. The interdisciplinary nature of IMC, spanning device physics, circuit design, architecture, and algorithm development, creates barriers to rapid advancement and deployment in real-world fraud detection systems.
The global landscape of IMC development shows concentration in North America, Europe, and East Asia, with major research institutions and technology companies driving innovation. Companies like IBM, Intel, and Samsung have made substantial investments in IMC research, while startups such as Mythic and Syntiant are developing specialized IMC solutions for specific applications including fraud detection systems.
Despite promising advancements, IMC accelerators face several critical challenges. Power consumption remains a significant concern, particularly for large-scale deployment in data centers handling massive transaction volumes. Current IMC implementations struggle to balance computational efficiency with energy requirements, limiting their practical application in 24/7 fraud detection systems.
Scalability presents another major hurdle. While laboratory demonstrations have shown impressive results, scaling these technologies to handle the volume and velocity of real-world financial transaction data remains problematic. Most current IMC accelerators can process only limited data sets efficiently, whereas fraud detection systems must analyze millions of transactions simultaneously.
Accuracy and reliability issues also persist. The analog nature of many IMC computations introduces variability that can affect detection precision. This is particularly problematic for fraud detection, where false positives can disrupt legitimate transactions and false negatives can result in significant financial losses.
Integration with existing infrastructure represents a substantial challenge. Financial institutions have invested heavily in conventional computing systems, and the transition to IMC-based solutions requires significant architectural changes and software adaptations. The lack of standardized programming models and development tools for IMC further complicates adoption.
Memory endurance and device degradation remain technical obstacles. Many IMC technologies suffer from limited write endurance, which is problematic for the continuous update requirements of fraud detection models. Device-to-device variability and temporal drift in memory cell characteristics can compromise long-term reliability.
Finally, there exists a significant knowledge gap between theoretical IMC capabilities and practical implementation expertise. The interdisciplinary nature of IMC, spanning device physics, circuit design, architecture, and algorithm development, creates barriers to rapid advancement and deployment in real-world fraud detection systems.
Current IMC Solutions for Fraud Detection
01 In-Memory Computing Architecture for Real-Time Processing
In-memory computing architectures enable real-time data processing by eliminating the bottleneck between memory and processing units. These architectures integrate computation directly within memory arrays, significantly reducing data movement and enabling parallel processing. This approach allows for faster execution of complex algorithms and real-time analytics by keeping data in memory rather than constantly moving it between storage and processing units.- In-Memory Computing Architecture for Real-Time Processing: In-memory computing architectures enable real-time data processing by eliminating the bottleneck between memory and processing units. These architectures integrate computation directly within memory arrays, significantly reducing data movement and latency. This approach allows for parallel processing of large datasets, making it particularly effective for real-time applications that require immediate responses to incoming data streams.
- Hardware Accelerators for In-Memory Computing: Specialized hardware accelerators enhance in-memory computing capabilities for real-time applications. These accelerators include custom ASICs, FPGAs, and neuromorphic chips designed to perform specific computational tasks directly within memory. By optimizing hardware for particular workloads, these accelerators achieve higher throughput and energy efficiency compared to general-purpose processors, enabling real-time processing of complex data streams.
- Distributed In-Memory Computing for Real-Time Systems: Distributed in-memory computing systems leverage multiple nodes with in-memory processing capabilities to handle real-time workloads. These systems distribute data and computation across a network of in-memory computing nodes, enabling horizontal scalability and fault tolerance. This approach is particularly valuable for real-time applications that process large volumes of data across multiple sources, such as IoT networks, financial trading systems, and telecommunications.
- Energy-Efficient In-Memory Computing for Real-Time Applications: Energy-efficient in-memory computing techniques enable real-time processing while minimizing power consumption. These approaches include low-power memory cell designs, dynamic voltage scaling, and selective activation of memory arrays. By reducing energy requirements, these techniques extend the operational lifetime of battery-powered devices and decrease cooling needs for data centers, making real-time in-memory computing more sustainable for continuous operation.
- Software Frameworks for In-Memory Real-Time Computing: Software frameworks optimize the utilization of in-memory computing accelerators for real-time applications. These frameworks provide programming models, runtime systems, and libraries that abstract hardware complexities and enable efficient development of real-time applications. They include features such as task scheduling, memory management, and synchronization mechanisms specifically designed for in-memory computing environments, allowing developers to leverage hardware capabilities without detailed knowledge of the underlying architecture.
02 Hardware Accelerators for In-Memory Computing
Specialized hardware accelerators designed specifically for in-memory computing applications can significantly improve real-time processing capabilities. These accelerators include custom ASICs, FPGAs, and other dedicated hardware that optimize memory-centric operations. By implementing computational functions directly in hardware, these accelerators achieve higher throughput and lower latency compared to general-purpose processors, making them ideal for time-sensitive applications.Expand Specific Solutions03 Distributed In-Memory Computing Systems
Distributed in-memory computing systems leverage multiple nodes with in-memory capabilities to process large-scale data in real-time. These systems distribute data and processing across a network of computing nodes, each utilizing in-memory techniques to accelerate operations. This approach enables horizontal scalability while maintaining the performance benefits of in-memory processing, making it suitable for real-time applications that require processing massive datasets.Expand Specific Solutions04 Energy-Efficient In-Memory Computing Techniques
Energy-efficient techniques for in-memory computing focus on reducing power consumption while maintaining real-time processing capabilities. These approaches include optimized memory cell designs, power-aware scheduling algorithms, and dynamic voltage scaling. By minimizing energy usage without sacrificing performance, these techniques enable sustainable deployment of in-memory computing accelerators in various environments, including edge devices with limited power resources.Expand Specific Solutions05 Software Frameworks for In-Memory Computing Acceleration
Software frameworks designed for in-memory computing provide programming models, libraries, and runtime systems that optimize application execution on in-memory hardware. These frameworks abstract hardware complexities, enable efficient resource utilization, and provide tools for developing real-time applications. They include specialized compilers that generate optimized code for in-memory architectures, as well as APIs that allow developers to leverage in-memory computing capabilities without detailed hardware knowledge.Expand Specific Solutions
Key Players in IMC Accelerator Industry
In-Memory Computing Accelerators for real-time fraud detection are emerging as critical technologies in the financial security landscape. The market is in a growth phase, with an estimated value exceeding $5 billion and projected annual growth of 15-20%. Major financial institutions like Mastercard, JP Morgan Chase, and PayPal are driving adoption, while technology providers such as IBM, SAP, and ZTE are developing specialized hardware-software solutions. The technology maturity varies across implementations, with established players like Featurespace and NuData Security (a Mastercard company) offering mature solutions, while newer entrants like Trustmi Networks are introducing innovative approaches. Chinese companies including Zhejiang Bangsun and Tencent are rapidly advancing in this space, particularly in high-performance in-memory processing capabilities for large-scale transaction monitoring.
Mastercard International, Inc.
Technical Solution: Mastercard has pioneered an advanced in-memory computing platform called "Decision Intelligence" specifically optimized for real-time fraud detection across their global payment network. Their architecture employs specialized memory-centric processing units that can analyze transaction patterns at the point of authorization without transferring data to external processing systems. Mastercard's solution utilizes a distributed in-memory grid that maintains a constantly updated profile of cardholder behavior patterns across multiple dimensions. The system employs proprietary algorithms that leverage resistive RAM (ReRAM) technology to perform complex pattern matching operations directly within memory arrays. This approach enables the simultaneous evaluation of hundreds of risk factors for each transaction in milliseconds. Mastercard's platform incorporates a hierarchical memory structure with different tiers optimized for specific types of fraud detection operations, from simple rule checking to complex behavioral analysis. Their system can process over 160 million transactions per hour while maintaining sub-10ms response times for fraud decisions.
Strengths: Mastercard's solution offers exceptional scalability to handle global transaction volumes with consistent performance and extremely low latency. Their distributed architecture provides built-in redundancy and fault tolerance. Weaknesses: The proprietary nature of their technology creates vendor lock-in, and the system requires significant customization when deployed in different regional markets with varying fraud patterns and regulatory requirements.
International Business Machines Corp.
Technical Solution: IBM has developed a comprehensive in-memory computing architecture specifically designed for real-time fraud detection. Their solution integrates Phase Change Memory (PCM) technology with specialized hardware accelerators to perform complex fraud detection algorithms directly within memory units. IBM's approach utilizes a hybrid architecture that combines traditional von Neumann computing with in-memory processing capabilities, allowing for parallel processing of large transaction datasets. The system employs resistive processing units (RPUs) that can perform matrix operations directly in memory, eliminating the data movement bottleneck typical in conventional systems. IBM's solution includes specialized neural network accelerators that can process thousands of transactions simultaneously while applying machine learning models to detect anomalous patterns indicative of fraud. Their architecture supports both supervised and unsupervised learning models that continuously adapt to new fraud patterns without requiring system downtime for model updates.
Strengths: IBM's solution significantly reduces latency by eliminating data movement between memory and processing units, enabling true real-time fraud detection even during peak transaction periods. Their hybrid architecture provides flexibility to handle both rule-based and AI-based fraud detection algorithms. Weaknesses: The specialized hardware requirements may result in higher initial implementation costs compared to software-only solutions, and integration with legacy banking systems can be complex.
Core IMC Patents and Technical Literature
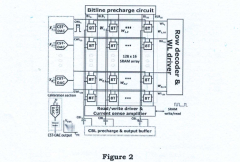
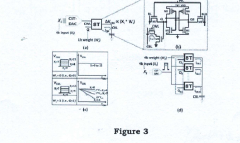
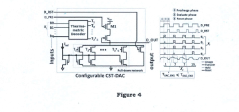
An in-memory computation (IMC)-based hardware accelerator system using a configurable digital-to-analog converter (DAC) and method capable of performing multi-bit multiply-and-accumulate (MAC) operations
PatentPendingIN202311065832A
Innovation
- The proposed solution involves a combined PAM and thermometric IMC system using a configurable current steering thermometric DAC (CST-DAC) array to generate PAM signals with various dynamic ranges and non-linear gaps, along with post-silicon calibration to mitigate process-variation issues and improve signal margin, enabling 4b x 4b MAC operations with high speed and accuracy.
Method and apparatus for real-time fraud machine learning model execution module
PatentActiveUS20200364718A1
Innovation
- Implementing a real-time fraud machine learning module (RTFMLM) with a distributed parallel architecture using proprietary machine learning algorithms, open-source software, and commodity hardware, allowing for simultaneous execution of multiple machine learning models across various data sources and frequent updates without manual recoding.
Performance Benchmarking Methodology
To establish a robust evaluation framework for In-Memory Computing (IMC) accelerators in fraud detection applications, a comprehensive performance benchmarking methodology must be implemented. This methodology should incorporate both standardized metrics and domain-specific indicators that reflect real-world fraud detection scenarios.
The benchmarking process begins with the definition of representative workloads that simulate actual fraud detection patterns. These workloads should include various transaction types, different fraud patterns, and varying data volumes to test the accelerators under diverse conditions. Synthetic datasets must be complemented with anonymized real-world data to ensure practical relevance while maintaining privacy compliance.
Key performance metrics for IMC accelerators in fraud detection applications include throughput (transactions processed per second), latency (focusing particularly on tail latency at the 99th percentile), energy efficiency (performance per watt), and detection accuracy (false positive and false negative rates). These metrics should be measured across different transaction volumes to assess scalability characteristics.
The testing environment must be carefully controlled to ensure reproducibility of results. This includes standardizing hardware configurations, operating system parameters, and network conditions. For comparative analysis, benchmarks should be run against baseline implementations using traditional computing architectures, such as CPU-only and GPU-accelerated solutions.
Memory-specific metrics are particularly important for IMC accelerators, including memory bandwidth utilization, memory access patterns, and cache hit/miss ratios. These metrics provide insights into how effectively the in-memory architecture is leveraged for fraud detection algorithms.
Real-time performance evaluation requires specialized methodologies that capture time-sensitive aspects of fraud detection. This includes measuring the system's ability to maintain consistent performance under sustained high loads and its resilience to sudden traffic spikes, which are common during shopping seasons or promotional events.
The benchmarking methodology should also incorporate adversarial testing, where the system is challenged with evolving fraud patterns to assess adaptability. This simulates the real-world scenario where fraudsters continuously modify their techniques to evade detection systems.
Finally, the methodology must include a standardized reporting format that facilitates clear comparison between different IMC accelerator implementations, ensuring that stakeholders can make informed decisions based on objective performance data relevant to fraud detection applications.
The benchmarking process begins with the definition of representative workloads that simulate actual fraud detection patterns. These workloads should include various transaction types, different fraud patterns, and varying data volumes to test the accelerators under diverse conditions. Synthetic datasets must be complemented with anonymized real-world data to ensure practical relevance while maintaining privacy compliance.
Key performance metrics for IMC accelerators in fraud detection applications include throughput (transactions processed per second), latency (focusing particularly on tail latency at the 99th percentile), energy efficiency (performance per watt), and detection accuracy (false positive and false negative rates). These metrics should be measured across different transaction volumes to assess scalability characteristics.
The testing environment must be carefully controlled to ensure reproducibility of results. This includes standardizing hardware configurations, operating system parameters, and network conditions. For comparative analysis, benchmarks should be run against baseline implementations using traditional computing architectures, such as CPU-only and GPU-accelerated solutions.
Memory-specific metrics are particularly important for IMC accelerators, including memory bandwidth utilization, memory access patterns, and cache hit/miss ratios. These metrics provide insights into how effectively the in-memory architecture is leveraged for fraud detection algorithms.
Real-time performance evaluation requires specialized methodologies that capture time-sensitive aspects of fraud detection. This includes measuring the system's ability to maintain consistent performance under sustained high loads and its resilience to sudden traffic spikes, which are common during shopping seasons or promotional events.
The benchmarking methodology should also incorporate adversarial testing, where the system is challenged with evolving fraud patterns to assess adaptability. This simulates the real-world scenario where fraudsters continuously modify their techniques to evade detection systems.
Finally, the methodology must include a standardized reporting format that facilitates clear comparison between different IMC accelerator implementations, ensuring that stakeholders can make informed decisions based on objective performance data relevant to fraud detection applications.
Security and Compliance Considerations
In-memory computing accelerators for real-time fraud detection systems must adhere to stringent security protocols and compliance standards due to the sensitive nature of financial data processing. These systems handle personally identifiable information (PII), transaction details, and proprietary fraud detection algorithms that require robust protection mechanisms. The implementation of hardware-level encryption for data at rest and in transit represents a critical security measure, ensuring that sensitive information remains protected even if physical access to the accelerator is compromised.
Data governance frameworks must be established specifically for in-memory computing environments, addressing the unique challenges of securing volatile memory where fraud detection operations occur. This includes implementing memory isolation techniques that prevent unauthorized access between different processing domains and establishing secure boot processes that verify the integrity of the system before loading fraud detection algorithms.
Regulatory compliance requirements vary significantly across jurisdictions, with frameworks such as PCI DSS, GDPR, CCPA, and SOX imposing specific obligations on financial fraud detection systems. In-memory computing accelerators must be designed with these requirements in mind, incorporating features like comprehensive audit logging capabilities that track all system access and data processing activities. These logs must be tamper-proof and provide sufficient detail for forensic analysis in case of security incidents.
The real-time nature of fraud detection introduces additional security considerations, as the system cannot sacrifice performance for security measures. This necessitates the development of hardware-accelerated security functions that can perform encryption, decryption, and authentication at line speed without introducing latency that would compromise fraud detection effectiveness. Homomorphic encryption techniques show particular promise in this context, allowing fraud detection algorithms to operate on encrypted data without requiring decryption.
Third-party risk management becomes especially important when deploying in-memory computing accelerators, as these systems often integrate with multiple financial platforms and services. Comprehensive vendor security assessments and continuous monitoring protocols must be established to ensure that all components of the fraud detection ecosystem maintain appropriate security standards. This includes regular penetration testing and vulnerability assessments specifically designed for in-memory computing environments.
Privacy-preserving computation techniques represent an emerging approach to balancing security requirements with analytical capabilities. Techniques such as secure multi-party computation and differential privacy can enable fraud detection systems to identify suspicious patterns without exposing individual transaction details, thereby enhancing compliance with privacy regulations while maintaining detection effectiveness.
Data governance frameworks must be established specifically for in-memory computing environments, addressing the unique challenges of securing volatile memory where fraud detection operations occur. This includes implementing memory isolation techniques that prevent unauthorized access between different processing domains and establishing secure boot processes that verify the integrity of the system before loading fraud detection algorithms.
Regulatory compliance requirements vary significantly across jurisdictions, with frameworks such as PCI DSS, GDPR, CCPA, and SOX imposing specific obligations on financial fraud detection systems. In-memory computing accelerators must be designed with these requirements in mind, incorporating features like comprehensive audit logging capabilities that track all system access and data processing activities. These logs must be tamper-proof and provide sufficient detail for forensic analysis in case of security incidents.
The real-time nature of fraud detection introduces additional security considerations, as the system cannot sacrifice performance for security measures. This necessitates the development of hardware-accelerated security functions that can perform encryption, decryption, and authentication at line speed without introducing latency that would compromise fraud detection effectiveness. Homomorphic encryption techniques show particular promise in this context, allowing fraud detection algorithms to operate on encrypted data without requiring decryption.
Third-party risk management becomes especially important when deploying in-memory computing accelerators, as these systems often integrate with multiple financial platforms and services. Comprehensive vendor security assessments and continuous monitoring protocols must be established to ensure that all components of the fraud detection ecosystem maintain appropriate security standards. This includes regular penetration testing and vulnerability assessments specifically designed for in-memory computing environments.
Privacy-preserving computation techniques represent an emerging approach to balancing security requirements with analytical capabilities. Techniques such as secure multi-party computation and differential privacy can enable fraud detection systems to identify suspicious patterns without exposing individual transaction details, thereby enhancing compliance with privacy regulations while maintaining detection effectiveness.
Unlock deeper insights with PatSnap Eureka Quick Research — get a full tech report to explore trends and direct your research. Try now!
Generate Your Research Report Instantly with AI Agent
Supercharge your innovation with PatSnap Eureka AI Agent Platform!