Identify authorization method between storage card and terminal equipment at off-line state
A technology of identity authentication and terminal equipment, applied in the field of identity authentication
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
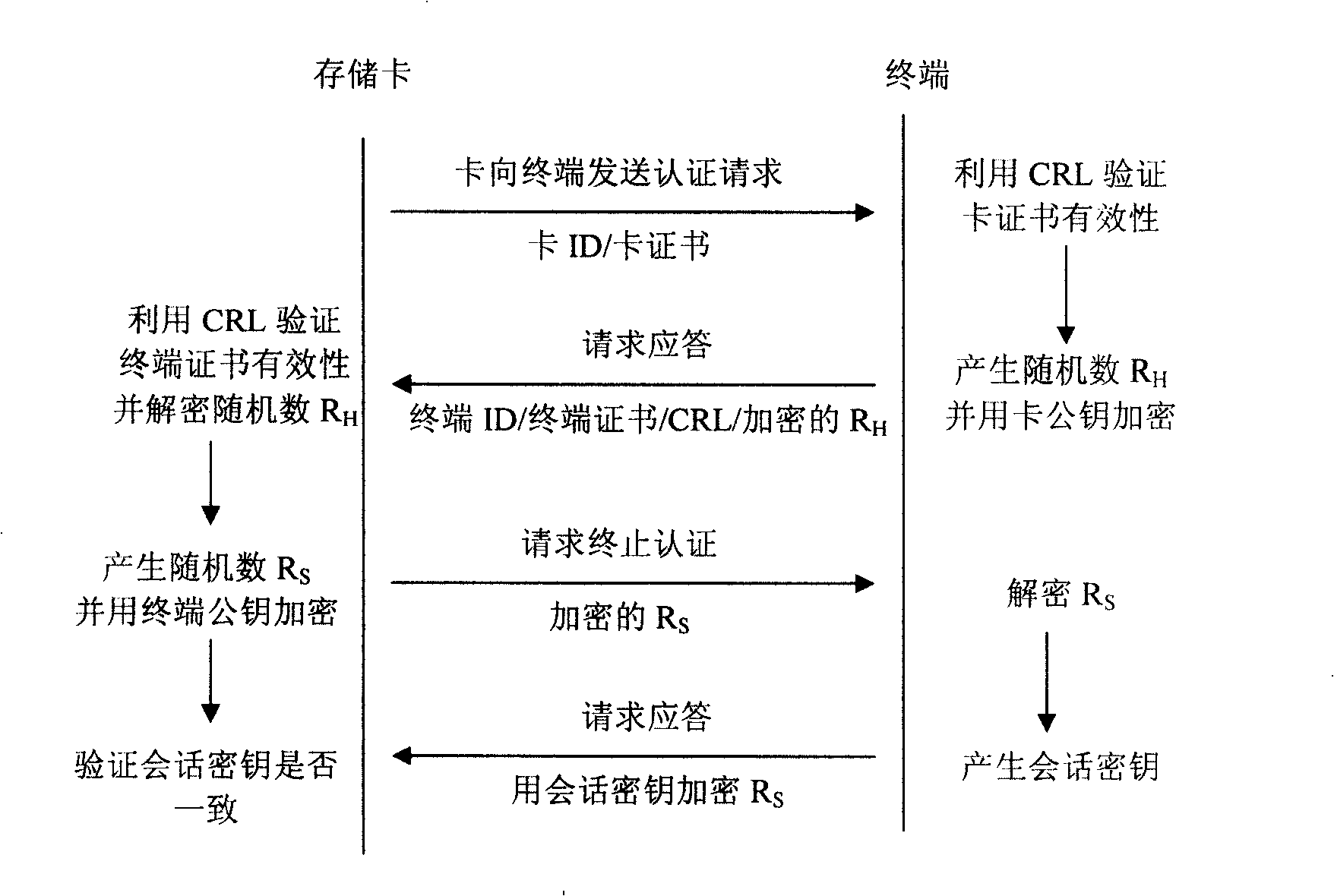
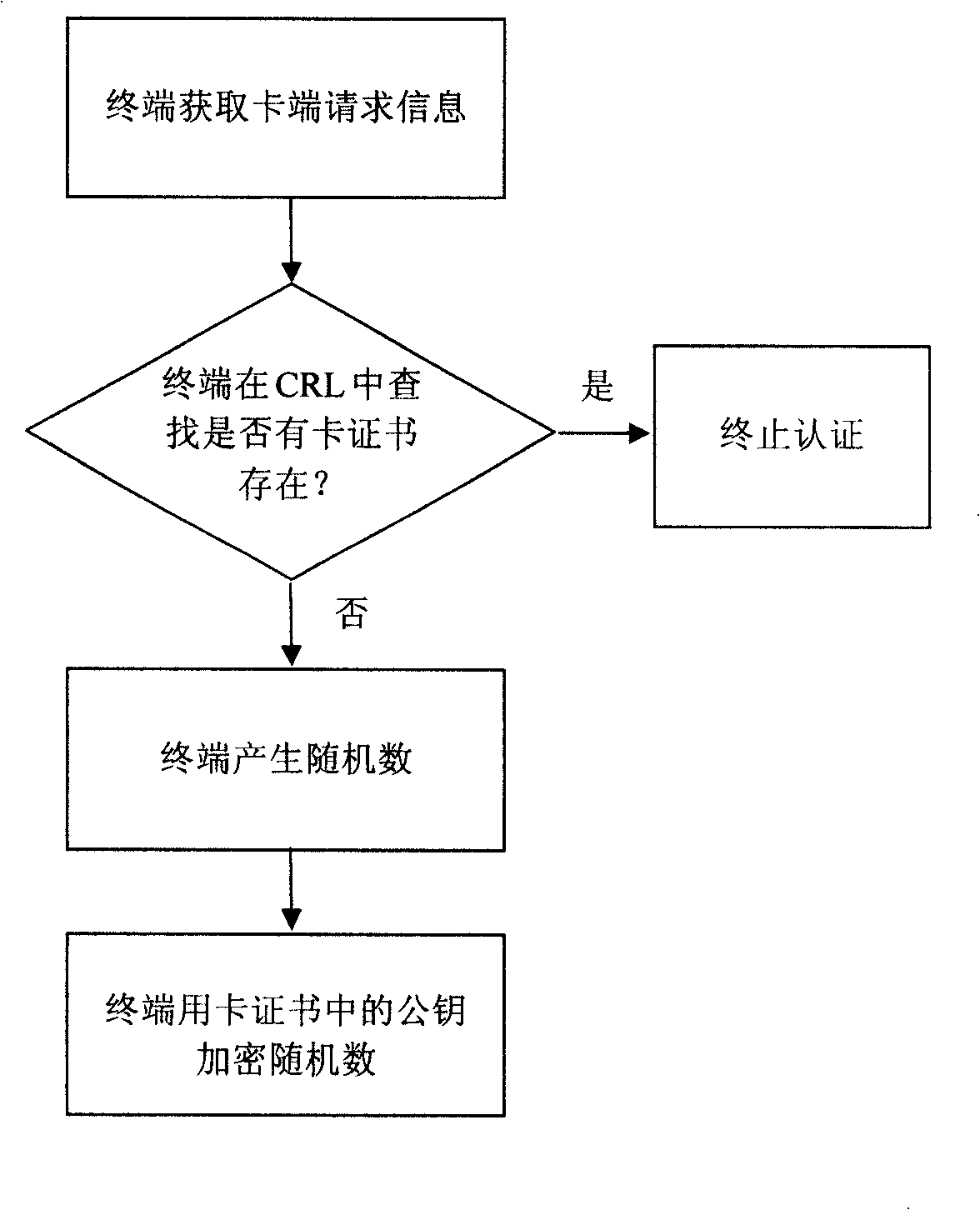
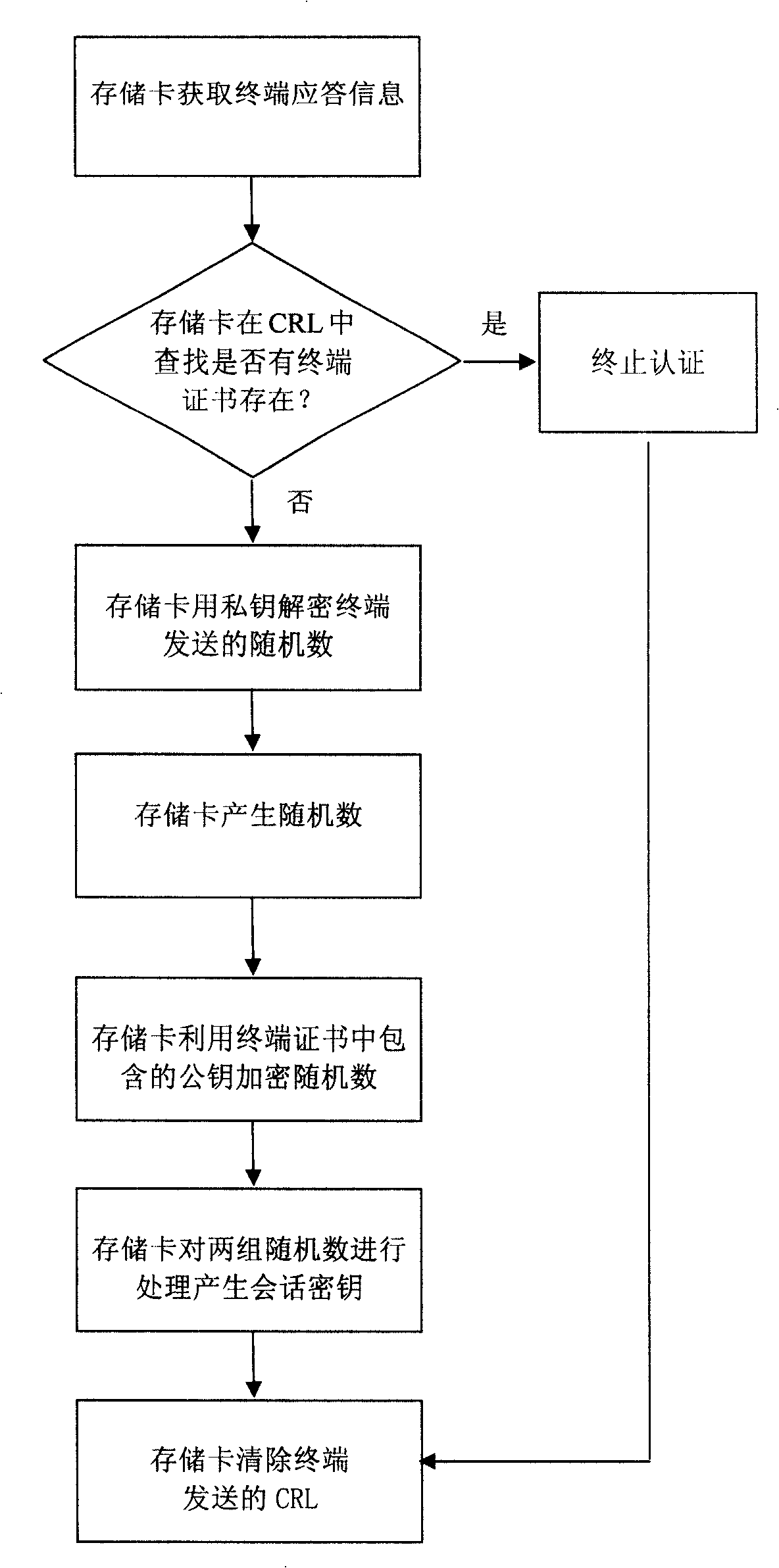
Method used
Image
Examples
Embodiment Construction
[0029] In order to better understand the essence of the present invention, several concepts related to the present invention are briefly introduced before describing the specific implementation process of the present invention in detail.
[0030] Public cryptographic algorithm: also known as asymmetric cryptographic algorithm. There are two different keys used for encryption and decryption, one of which is made public and called the public key; the other is kept strictly secret and called the private key. Both the public key and the private key can be used for data encryption and decryption, and the public key can be placed in a digital certificate and published in the form of a certificate. Public cryptographic algorithms are mainly used for key distribution and digital signatures.
[0031] Symmetric cryptographic algorithm: The same key is used for data encryption and decryption.
[0032] PKI system: It is a collection of hardware, software, personnel and application progr...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More