A Java code obfuscation method based on control flow complexity
A technology for code obfuscation and control flow, applied in the field of computer security, can solve the problems of insufficient utilization of loop structures, additions, software piracy, etc., and achieve the effect of realizing the method of complicating control flow and overcoming insufficient utilization.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0051] The present invention will be further described below in conjunction with the accompanying drawings. The following examples are only used to illustrate the technical solution of the present invention more clearly, but not to limit the protection scope of the present invention.
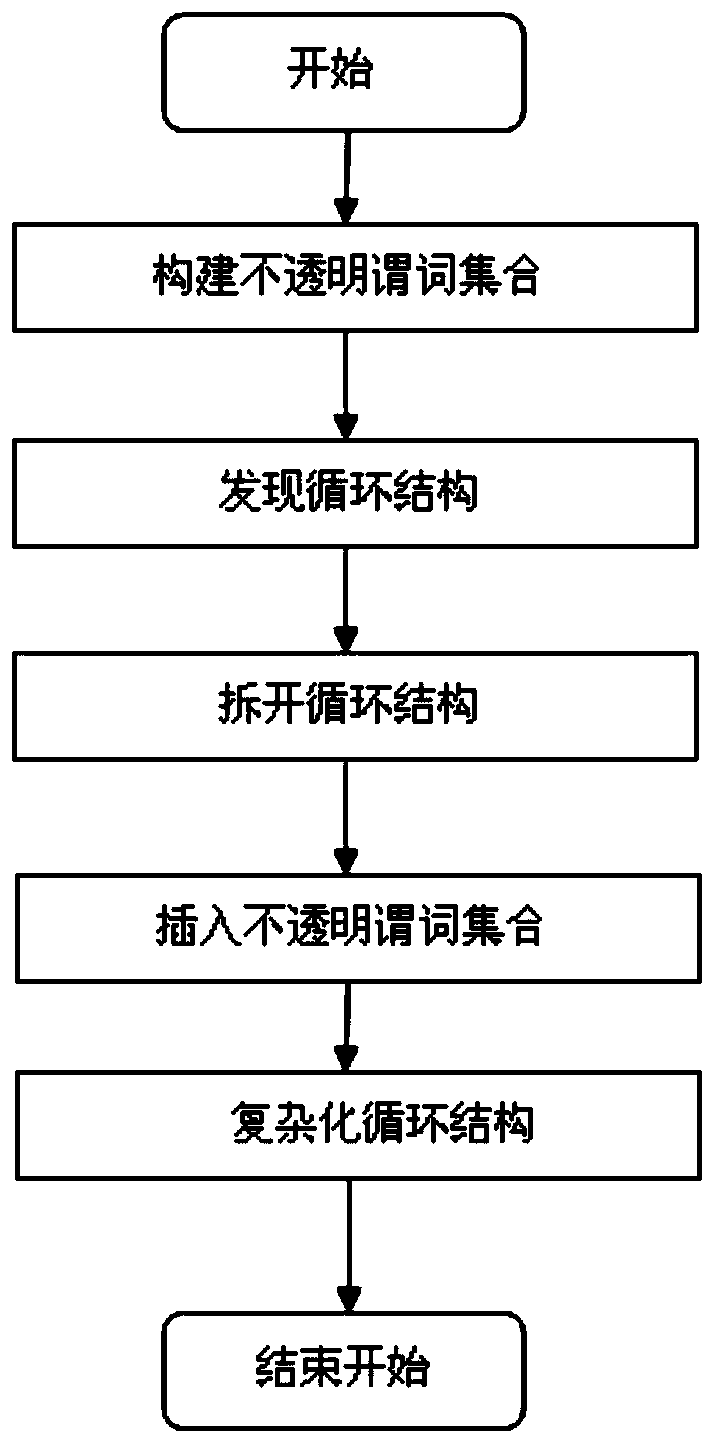
[0052] like figure 1 As shown, a Java code obfuscation method based on control flow complexity includes the following steps:
[0053] Step 1, construct the set of opaque predicates.
[0054] Using the comparison of references in Java to construct opaque predicate sets, the opaque predicate sets include constructing the set T of predicates that are always true and the set F of predicates that are always false.
[0055] Step 2, find the loop structure.
[0056] Discover loop structures from Java code snippets, they should look like this case:
[0057] code show as below:
[0058] B: Cal_A
[0059] If not A go to E;
[0060] C
[0061] Go to B;
[0062] E:
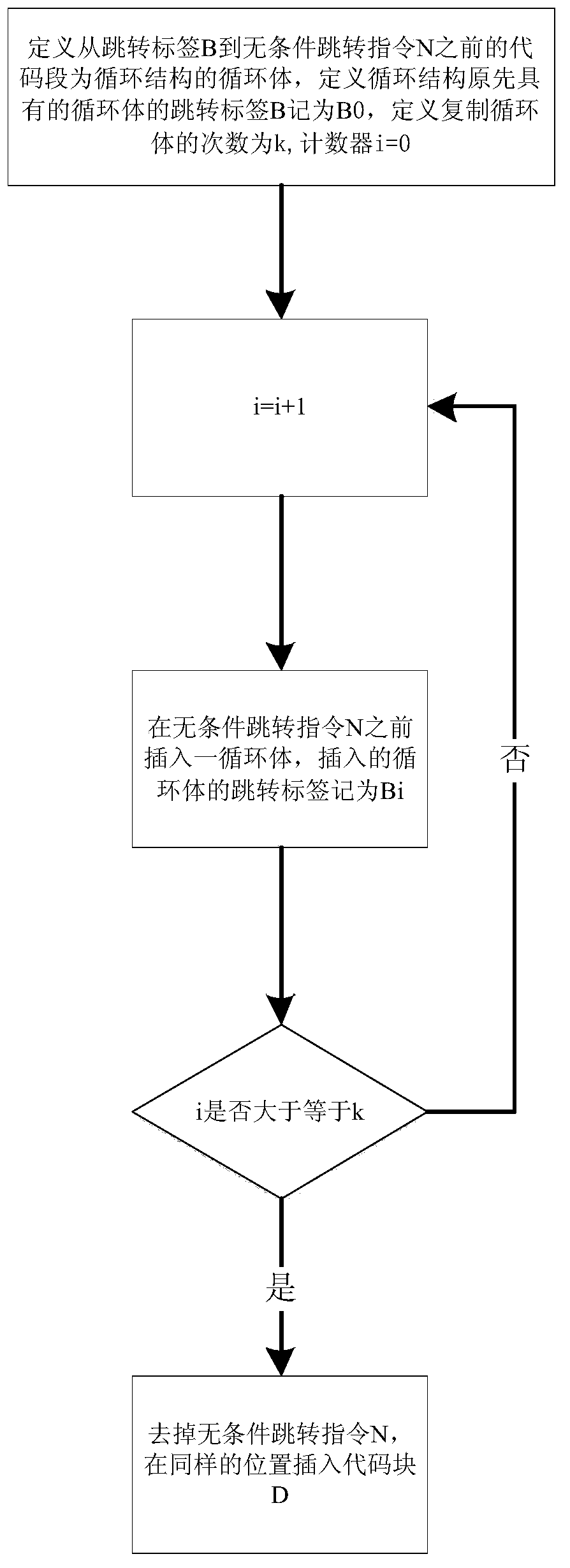
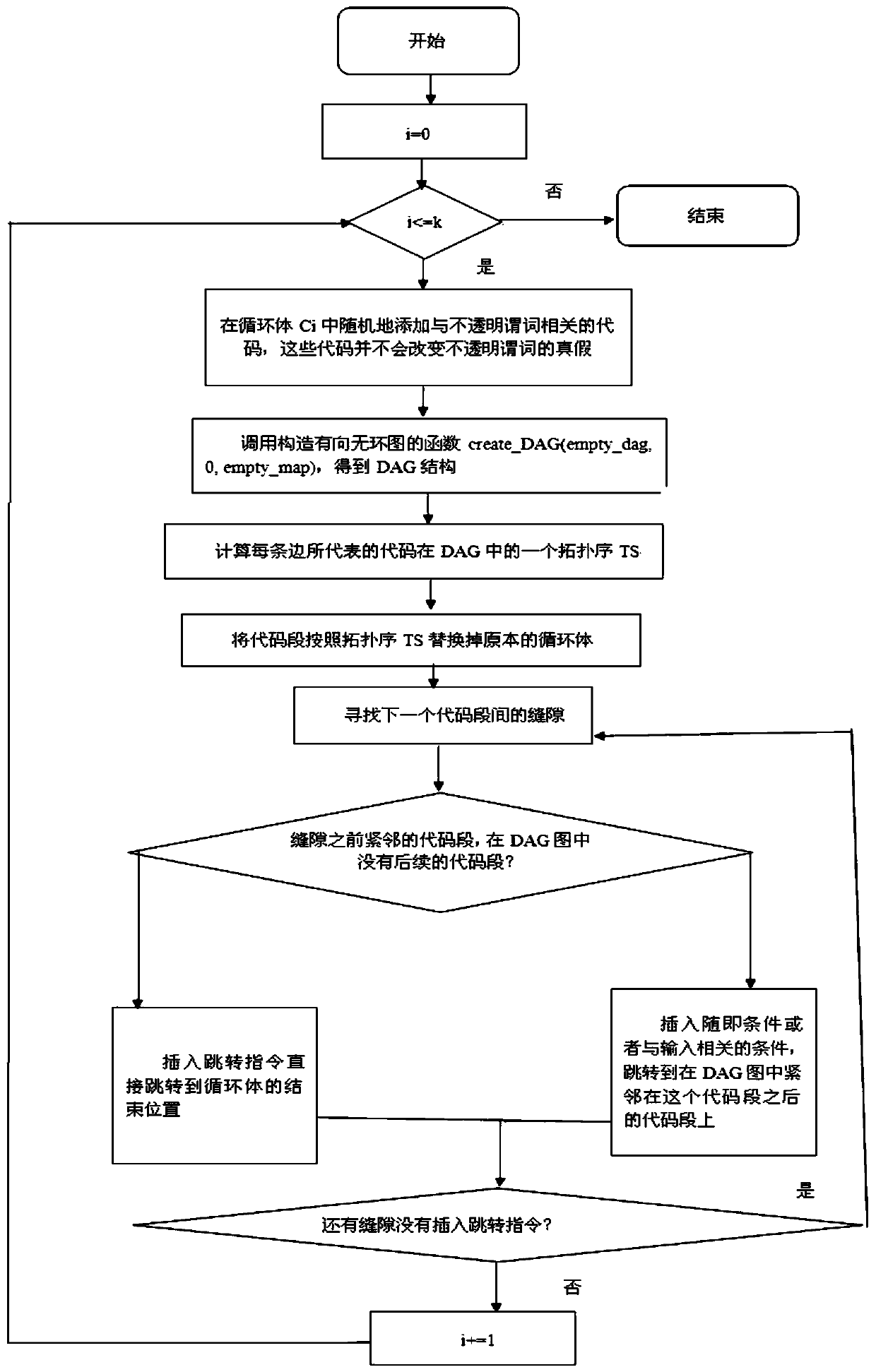
[0063] The specific process is...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More