Malicious code detection method based on sdn network
A malicious code detection and malicious code technology, applied in the field of computer network security, can solve problems such as large computational consumption of malicious code
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
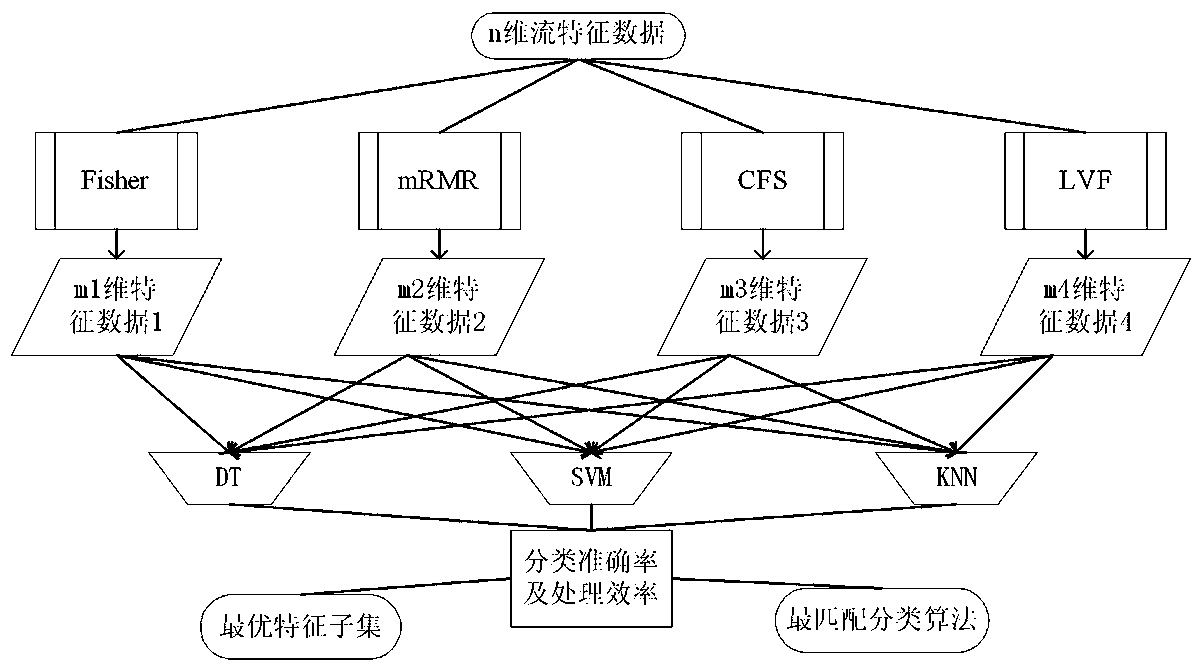
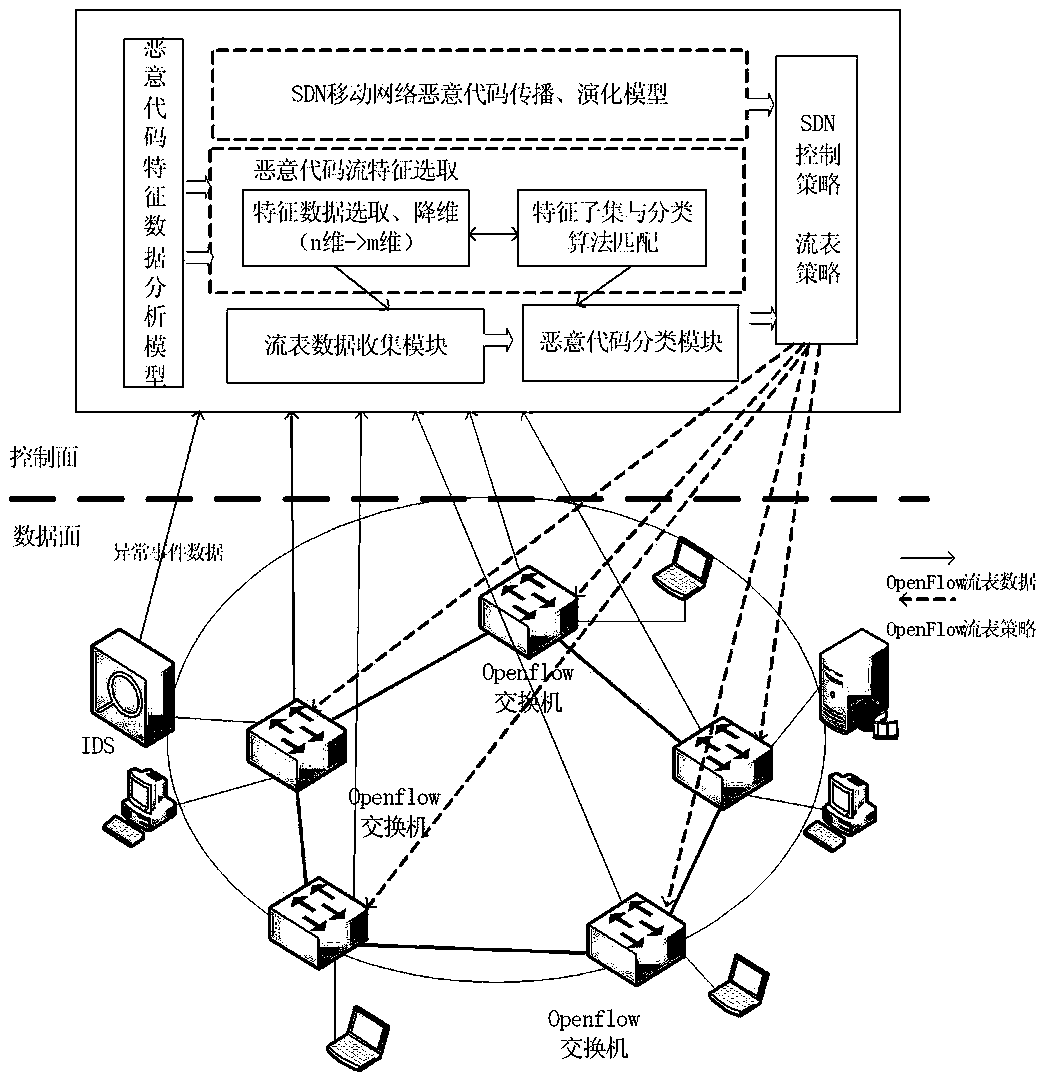
[0019] The road map of the invention is as figure 1 Shown.
[0020] In actual detection, the flow table data collection module periodically sends a flow table request to the OpenFlow switch, and the flow table information returned by the switch is transmitted to the flow table collection node through an encrypted channel. The flow feature extraction module receives the flow table data collected by the flow table collection module according to the result of the feature analysis, and extracts related m flow features to form m-tuples. Each m-tuple uses the ID of the switch that collected the data as Identification, which can monitor which SDN switch has found a certain type of malicious event. The classifier module is responsible for classifying the collected m-tuples to distinguish which type of abnormal flow or normal flow is the flow during the period.
[0021] (1) OpenFlow flow table feature selection and importance ranking
[0022] The OpenFlow flow table uses flow forwarding to ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More