Box capable of protecting content integrity based on RFID (Radio Frequency Identification)
A technology of RFID tags and integrity, applied in the direction of cooperative devices, record carriers used by machines, instruments, etc., can solve the problem of manufacturing counterfeit products
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
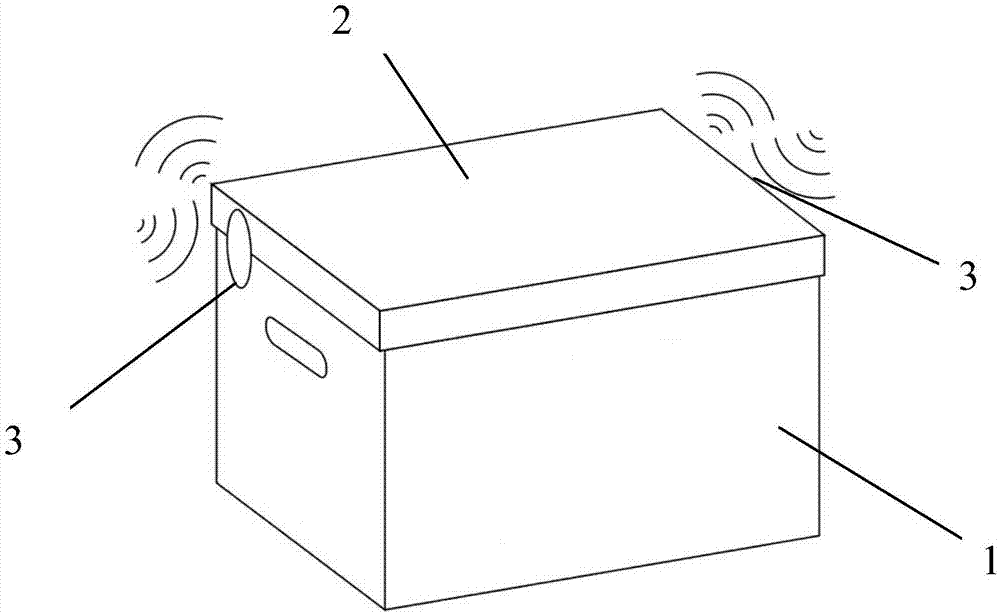
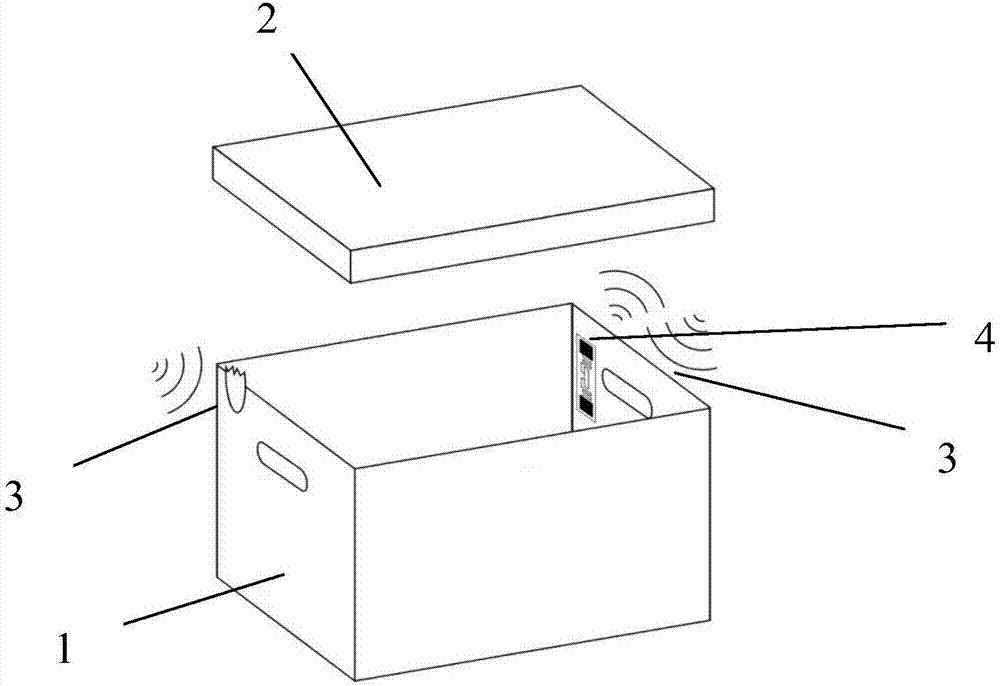
[0023] In this embodiment, the box body 1 and the cover 2 are separated, such as figure 1 , figure 2 and Figure 5 As shown, two fragile RFID tags 3 ( figure 1 and figure 2 In , one of the two fragile RFID tags 3 cannot be seen due to the viewing angle, but its position is marked in the figure). An RFID tag 4 is arranged inside the box body 1, and the RFID tag 4 is an identity tag of the goods.
[0024] Figure 5 It is a structural schematic diagram of the fragile RFID tag 3, the fragile RFID tag 3 includes the RFID tag 5 and the tissue paper 6, the RFID tag 5 is wrapped in the tissue paper 6, and the tissue paper 6 is a paper self-adhesive, and then it is pasted on the box The closure of the body 1 and the cover 2. The RFID tag 5 includes a tag memory (the tag memory is used to store unique codes and tag-related information), a tag control circuit and a tag antenna. When the box is opened, the fragile RFID tags 3 arranged on both sides are torn apart, and the tags ins...
Embodiment 2
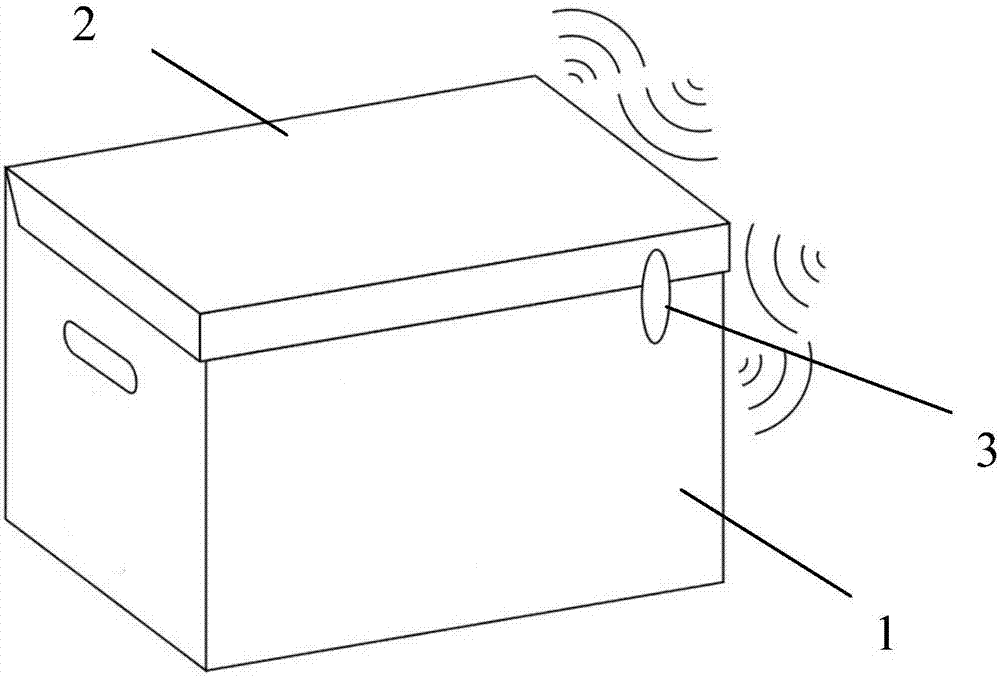
[0026] In this embodiment, the box body and the cover are integrated, such as image 3 , Figure 4 and Figure 5 As shown, a fragile RFID tag 3 is provided at the closure of the box body 1 and the cover 2 . An RFID tag 4 is arranged inside the box body 1, and the RFID tag 4 is an identity tag of the goods.
[0027] Figure 5 It is a structural schematic diagram of the fragile RFID tag 3, the fragile RFID tag 3 includes the RFID tag 5 and the tissue paper 6, the RFID tag 5 is wrapped in the tissue paper 6, and the tissue paper 6 is a paper self-adhesive, and then it is pasted on the box The closure of the body 1 and the cover 2. The RFID tag 5 includes a tag memory (the tag memory is used to store unique codes and tag-related information), a tag control circuit and a tag antenna. When the box is opened, the fragile RFID tag 3 arranged at the closure is torn open, and the tags inside If the antenna is damaged (you can also pre-cut some incisions on the surface of the thin p...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com