HTTPS data flow audit method and system for carrier backbone network
A backbone network and operator technology, applied in the direction of transmission systems, electrical components, etc., can solve the problems of the middle section of the backbone network link, affecting the data transmission speed of the backbone network, and the impact of network users.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
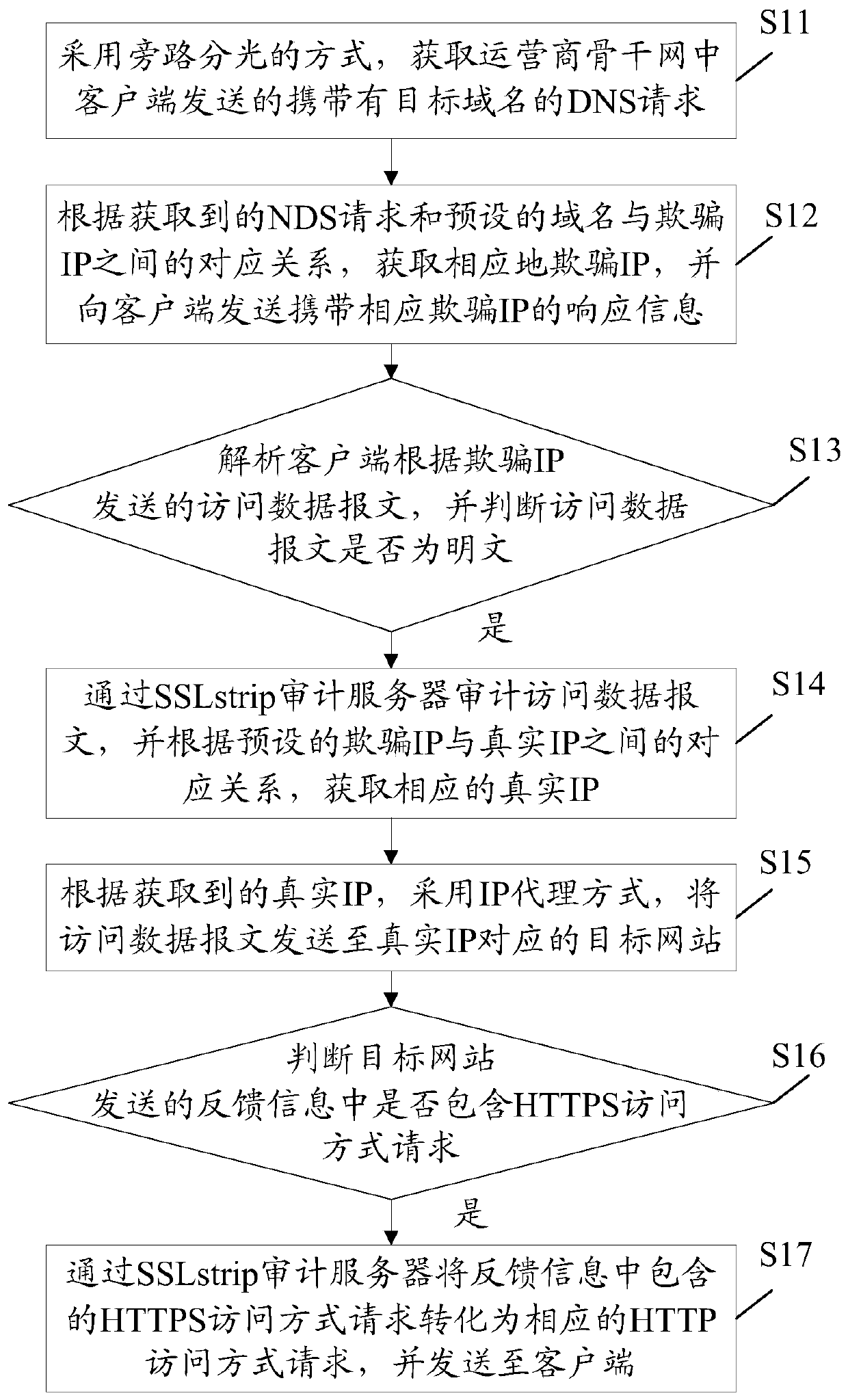
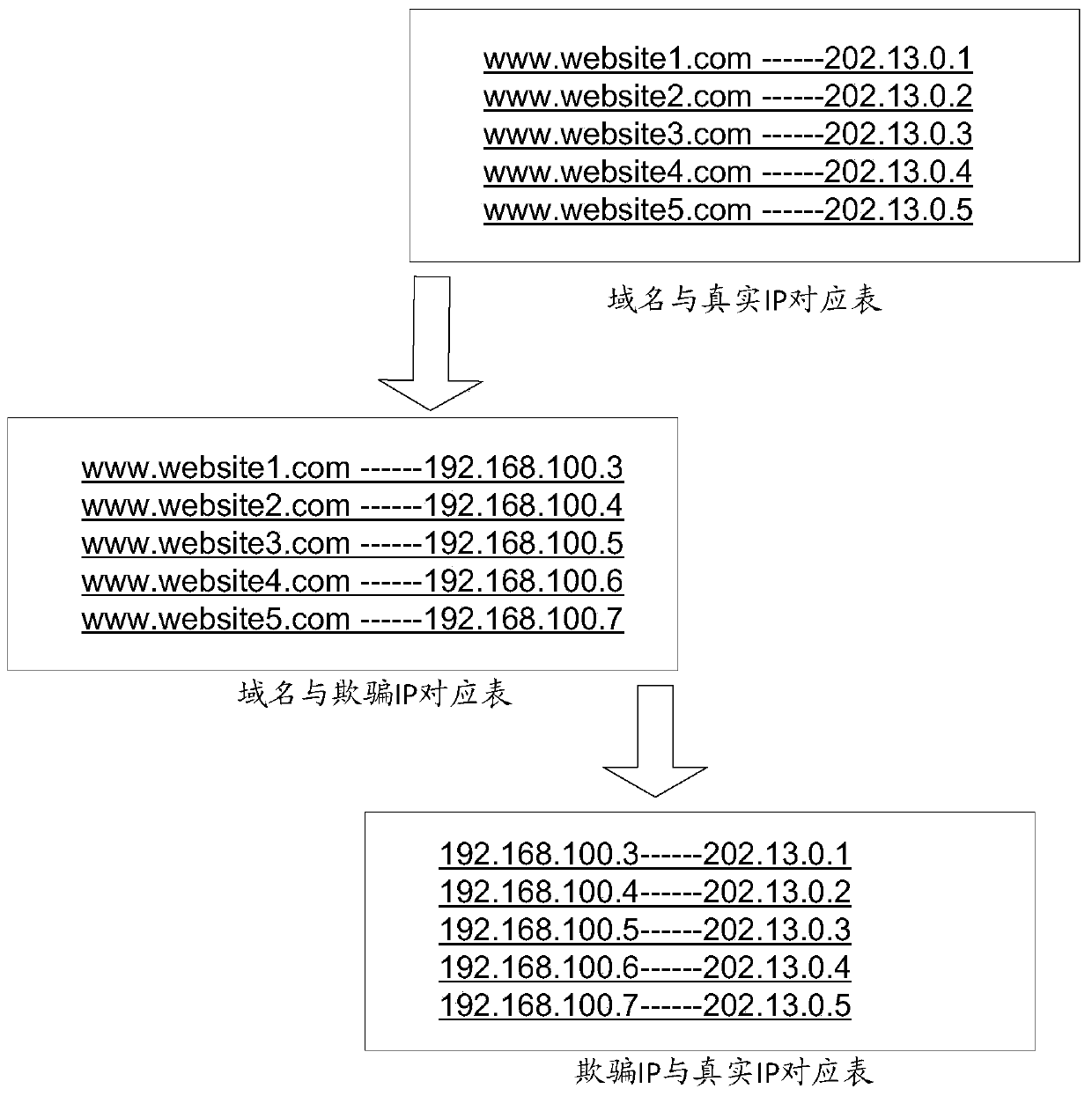
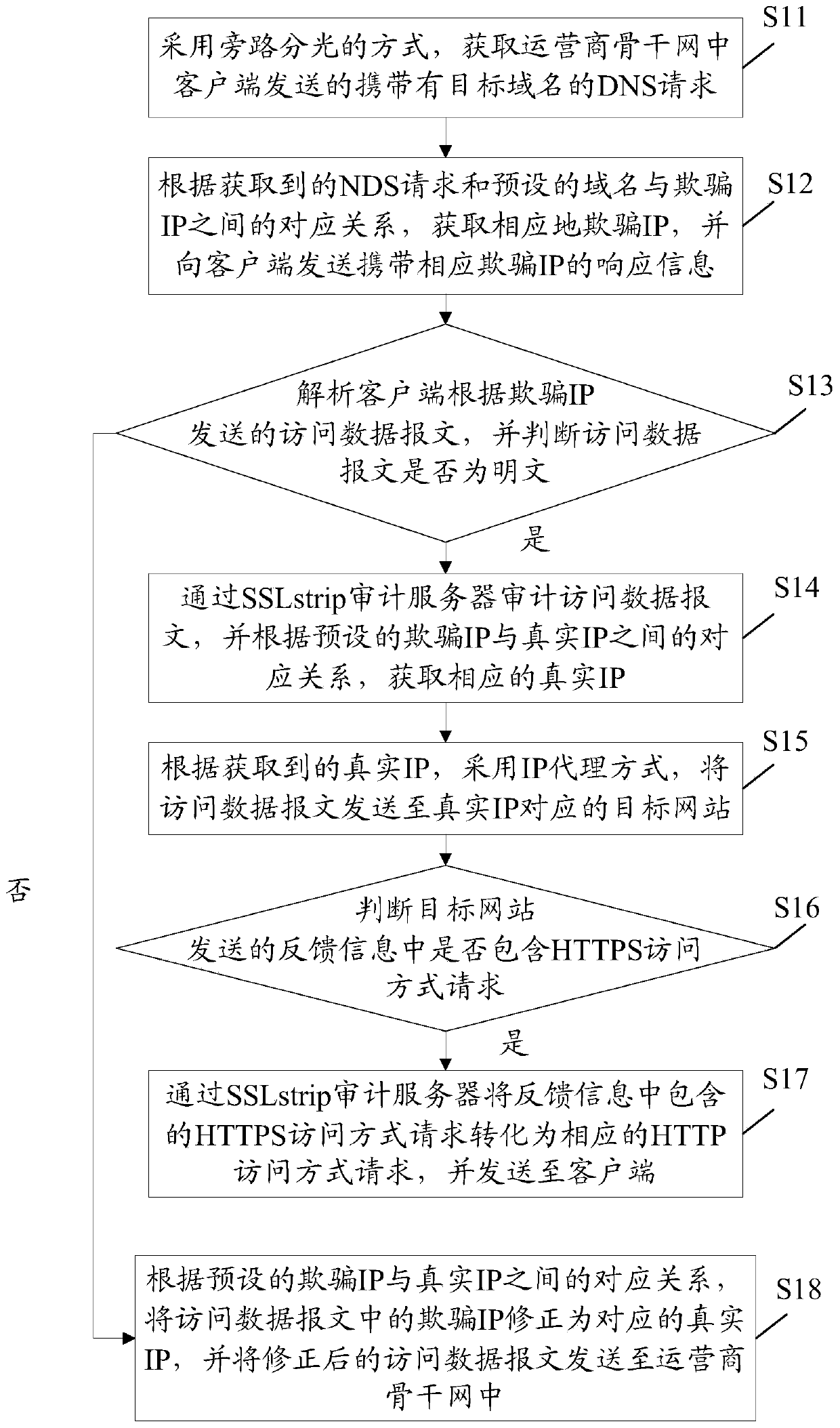
[0042] The embodiment of the present invention provides a kind of HTTPS data stream auditing method for operator's backbone network, is applicable to the HTTPS data stream auditing of operator's large-traffic backbone network (network traffic is above 1Gbps), see figure 1 , the method can include:
[0043] In step S11, the DNS request carrying the target domain name sent by the client in the operator's backbone network is obtained by means of bypass optical splitting.
[0044] In this embodiment, the backbone network is a high-speed network used to connect multiple regions or regions. The traffic of the backbone network of the operator is generally large. When performing a network security audit for this type of network, if the audit Equipment, will seriously affect the transmission speed of the backbone network, and even cause the backbone network link to be interrupted. Therefore, in order to avoid intrusion of audit equipment in the backbone network, the bypass splitting m...
Embodiment 2
[0065] The embodiment of the present invention provides a kind of HTTPS data flow auditing system oriented to the backbone network of the operator, which adopts the method described in the first embodiment, see Figure 4 , the system can include:
[0066] The DNS spoofing server 100 is connected to a client accessing the carrier's backbone network, and is used to obtain a DNS request carrying a target domain name sent by a client in the carrier's backbone network by bypassing optical splitting.
[0067] In this embodiment, the backbone network is a high-speed network used to connect multiple regions or regions (for example, in Figure 4 In the middle, it is a connection link between two different routers), the traffic of the backbone network of the operator is generally large, when performing network security audit for this type of network, if the audit device is connected in the middle of the backbone network, it will seriously Affect the transmission speed of the backbone n...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com