Cyberspace threat knowledge extraction method and device
A network space and knowledge extraction technology, applied in character and pattern recognition, special data processing applications, instruments, etc., can solve problems that cannot be applied well
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0048] In order to make the purpose, technical solution and advantages of the present application clearer, the present application will be further described in detail below in conjunction with the accompanying drawings and embodiments. It should be understood that the specific embodiments described here are only used to explain the present application, and are not intended to limit the present application.
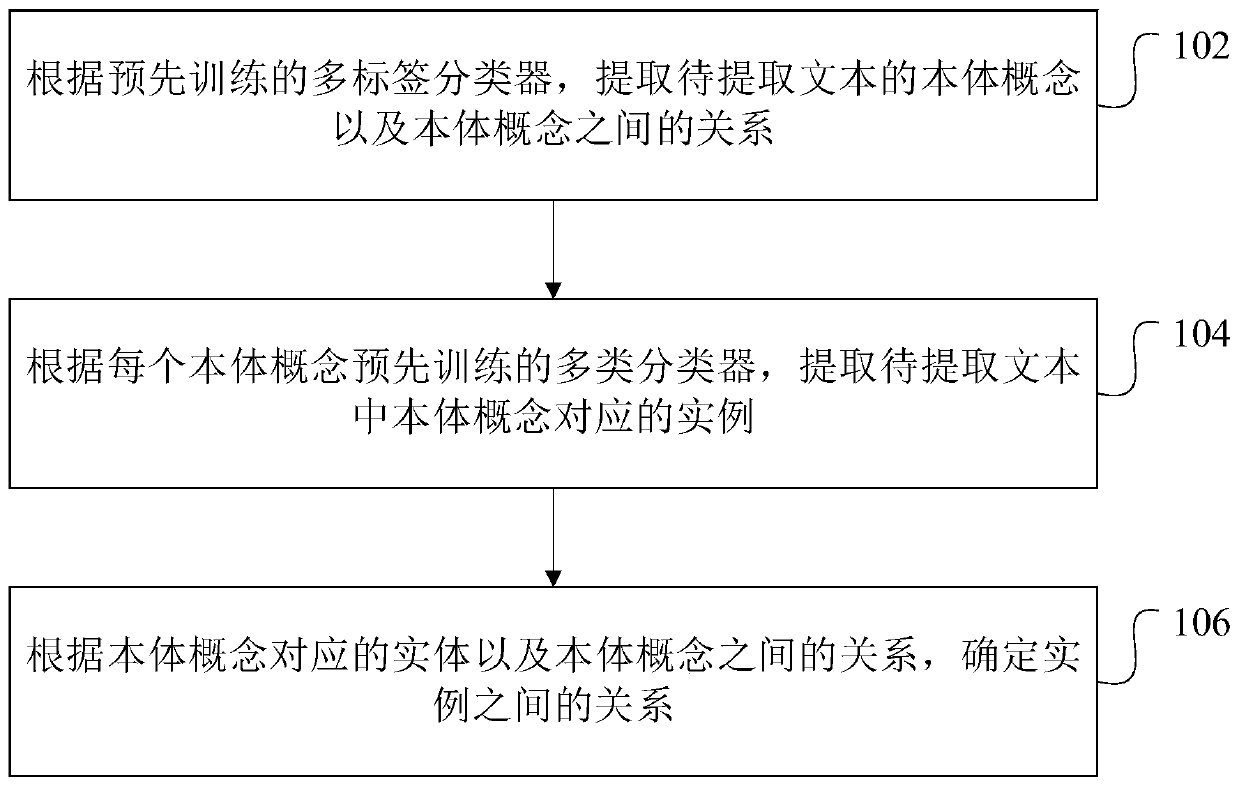
[0049] In one embodiment, such as figure 1 As shown, a cyberspace threat knowledge extraction method is provided, including the following steps:
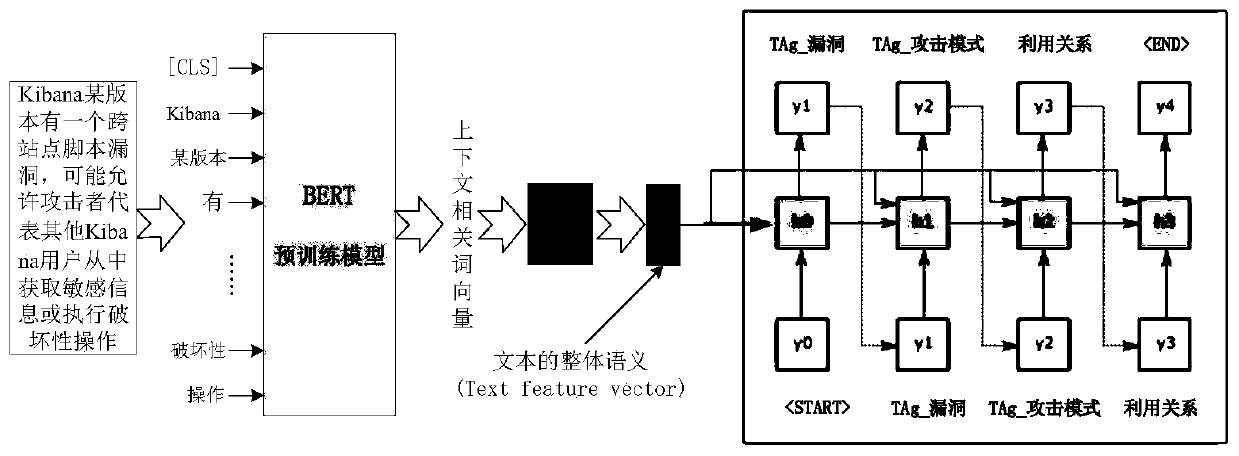
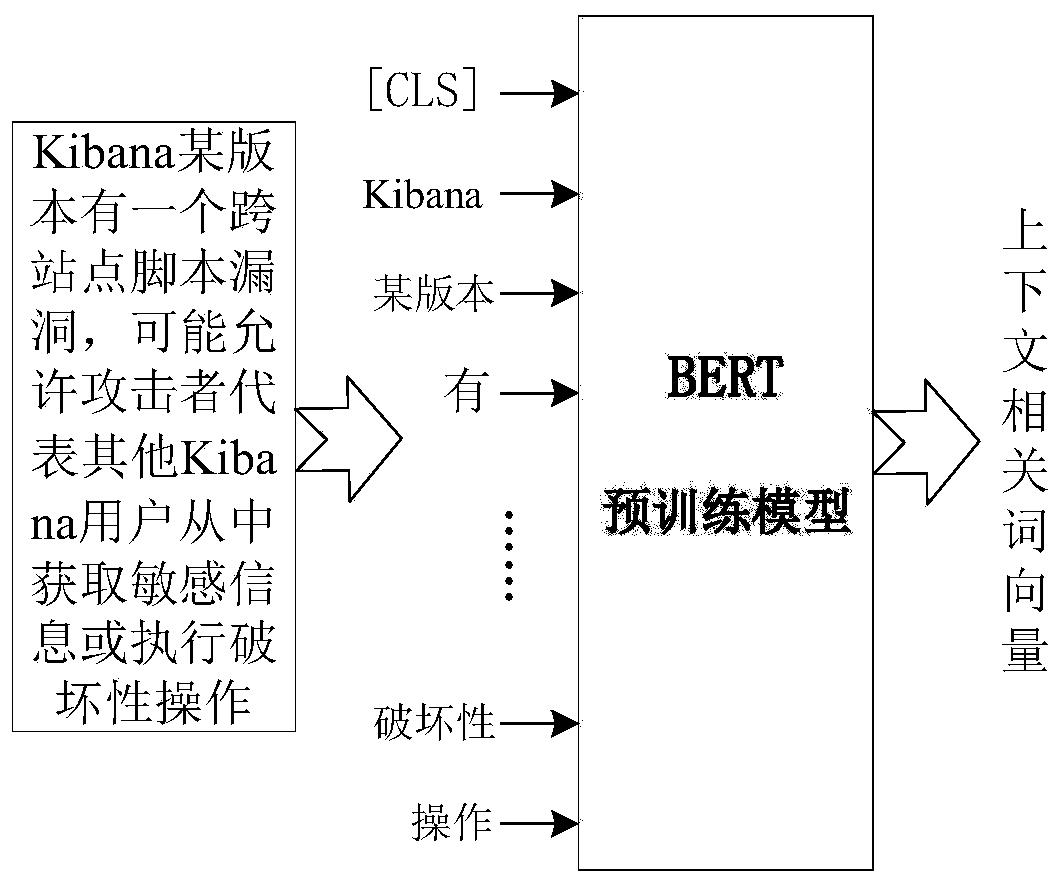
[0050] Step 102, according to the pre-trained multi-label classifier, extract the ontology concept of the text to be extracted and the relationship between the ontology concepts.
[0051] A multi-label classifier is a model for semantic classification based on labels, such as the existing RNN model, CNN model, etc.
[0052] Ontology is the concept on the upper layer of the map. Generally speaking, ontology has no practical mea...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More