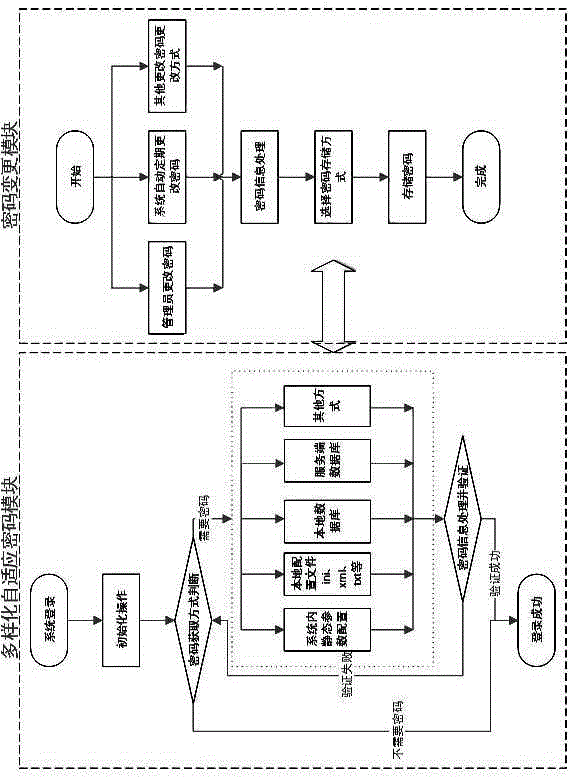
Diversified adaptive password changing control module
A cryptographic module and change control technology, applied to key distribution, can solve problems such as implementation difficulties
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0009] The content of the present invention is described in more detail below:
[0010] Diversified adaptive cryptographic module implementation methods:
[0011] 1) System startup;
[0012] 2) Realize the preprocessing operation and load the configuration information (config.xml, config.ini, etc.);
[0013] 3) Determine whether the system needs password verification. If no password verification is required, just log in directly. If password verification is required, you need to obtain and analyze the password storage configuration information;
[0014] 4) Refer to the password storage configuration information to obtain the password information to be verified;
[0015] 5) Process, decrypt, format transform and other operations on the obtained password information;
[0016] 6) Verify the password. If the verification passes, the system login is successful. If the verification fails, you need to obtain the next password information to be verified according to the configurat...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com